I have an R7000 currently running TomatoUSB. I have it setup rather uniquely in that the physical port #4 is it's own subnet (172.17.1.) but ports 1-3 and the wifi are on the 192.168.1. range. Is this possible with LEDE?
Sure, a similar setup would be done with VLANs in LEDE. You simply setup the VLANs/IPs, firewall zone and then assign them to the to the proper Switch ports as either Access (untagged VLAN port) or Trunked (tagged VLAN port). I currently do this to create other LANs and guest wireless networks on my device.
See:
https://wiki.openwrt.org/doc/uci/network
and
https://wiki.openwrt.org/doc/networking/network.interfaces
Thank you very much for the reply. I am currently considering going from TomatoUSB to LEDE (haven't pulled the trigger yet).
No problem. I should also mention that your setup seems simple with LEDE (if that helps you make the decision).
Once you install LEDE, your device should have the LuCI web GUI. The device should be setup for a LAN and WAN. You will add another LAN under "Interfaces" and use the next available VLAN ID. From there, you will configure the IP and DHCP of the network and assign/create a new firewall zone.
From there, you will go to the "Switch" tab. You will add this VLAN to the CPU, and add it to what the OpenWRT manual notes as your 4th port (removing the other LAN from the port).
That should be it. Hope all works out.
UI’m not sure I would recommend LEDE on the Netgear R7000. For only one reason: the Broadcom chipset is not supported.
The Broadcom binaries blobs are better supported by dd-wrt. This is a license issue and a problem with the newer kernel used by LEDE. It’s unfortunate that some manufacturers are not more willing to cooperate to make their devices able to run the latest software with all the relevant security patches, like the latest WPA2 patch(es)
Edit: looks there is already a topic on this Netgear R7000 ... what doesn't work with LEDE 17.01.4
OK... step 1 before I try to create the port #4 is to allow my workstation on the primary LAN to ping a device on the guestzone where I will have a server connected and on its own subnet with no access to the primary one.
I have the 192.168.1.1 range setup for my primary LAN and guestzone (Wireless currently) using the 172.17.1.1 range. I used the script on the guestwifi_configuration page. I want to be able to ping and ssh into devices that I put on my guestwifi zone from my primary LAN but am unsure how to do it.
Currently, I cannot ping from the my workstation on 192.168.1.100 to a device on the guest wifi (172.17.1.200). If I ssh into the router, I can obviously ping both zones.
Thanks, always good to check the router's page on the Table of Hardware to ensure it's [fully] supported.
There are two straightforward methods to accomplish this:
-
If they are in different Firewall Zones (and forwarding between them is disabled), you can add Port Forwards for ICMP Echo Request and tcp/22 to guestWLAN from trusted-LAN.
-
Or, you can set this up one-way by allowing forwarding from your trusted-LAN Firewall Zone to the guestWLAN Firewall Zone. This will also allow replies from Established and Related traffic initiated from the trusted-LAN to work without necessity for future configuration of more ports/protocol. NOTE: Only use this method if you're OK with all hosts on trusted-LAN initiating traffic to devices on the guestWIFI.
- From there, depending on the config, you may have to allow, Echo Reply from guestWLAN to trusted-LAN (but this should be Related to the ping sent from trusted-LAN).
I have an interface called "GUEST" (br-guest) I created for the guest wireless. It is setup on it's own IP range and in its own firewall zone. Can I simply go into the "Switch" tab and setup port 4 to use this interface?
I'm not quite clear on the settings need to use for my newly created VLAN 3 or if this is even possible.
EDIT: The wiki mentions that my device (R7800) has an embedded switch ... not sure how/if that matters for my use-case?
# ls -l /sys/class/net/
lrwxrwxrwx 1 root root 0 Oct 19 09:37 br-guest -> ../../devices/virtual/net/br-guest
lrwxrwxrwx 1 root root 0 Oct 19 09:37 br-lan -> ../../devices/virtual/net/br-lan
lrwxrwxrwx 1 root root 0 Dec 31 1969 eth0 -> ../../devices/platform/soc/37200000.ethernet/net/eth0
lrwxrwxrwx 1 root root 0 Dec 31 1969 eth1 -> ../../devices/platform/soc/37400000.ethernet/net/eth1
lrwxrwxrwx 1 root root 0 Dec 31 1969 lo -> ../../devices/virtual/net/lo
lrwxrwxrwx 1 root root 0 Oct 19 09:37 wlan0 -> ../../devices/platform/soc/1b500000.pci/pci0000:00/0000:00:00.0/0000:01:00.0/net/wlan0
lrwxrwxrwx 1 root root 0 Oct 19 09:39 wlan0-1 -> ../../devices/platform/soc/1b500000.pci/pci0000:00/0000:00:00.0/0000:01:00.0/net/wlan0-1
Yes. From your picture, it appears you will do the following to accomplish this:
- First, be certain LAN 4 is labeled in the correct order - SEE TABLE OF HARDWARE
- Use WI-Fi, LAN 2 or 3 to complete this (in case the ports are labeled in reverse)
- Add VLAN 3 to CPU/eth1 as "Untagged"
- Remove VLAN 1 from LAN 4 by changing it to "Off"
- Add VLAN 3 by changing it from "Off" to "Untagged" (verify this in Switch documentation, as my CPU has these tagged by default)
- Hit "Save and Apply"
Port 4 should now be on your new VLAN 3.
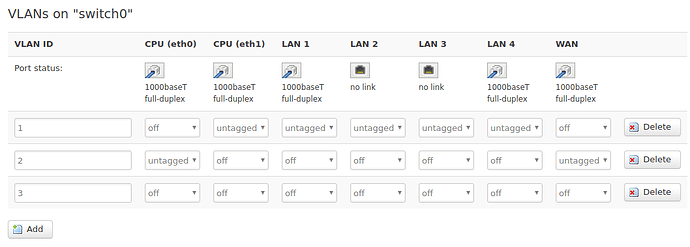
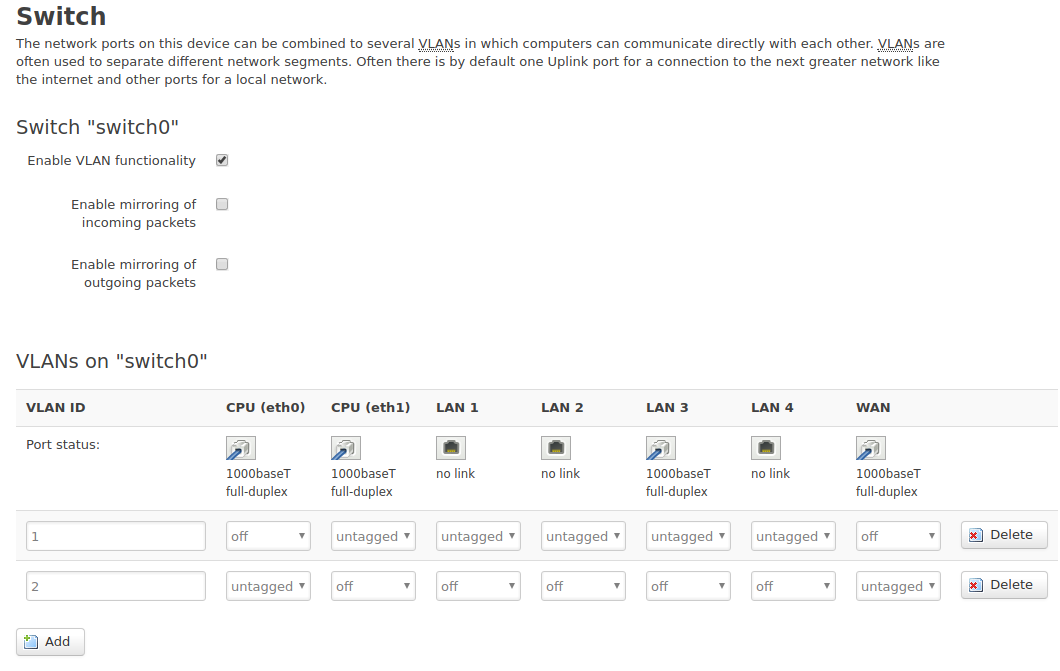
On a fresh installation of LEDE on my R7800, here is the default switch page:
I don't think I got this setup correctly... it's angry about untagged status:
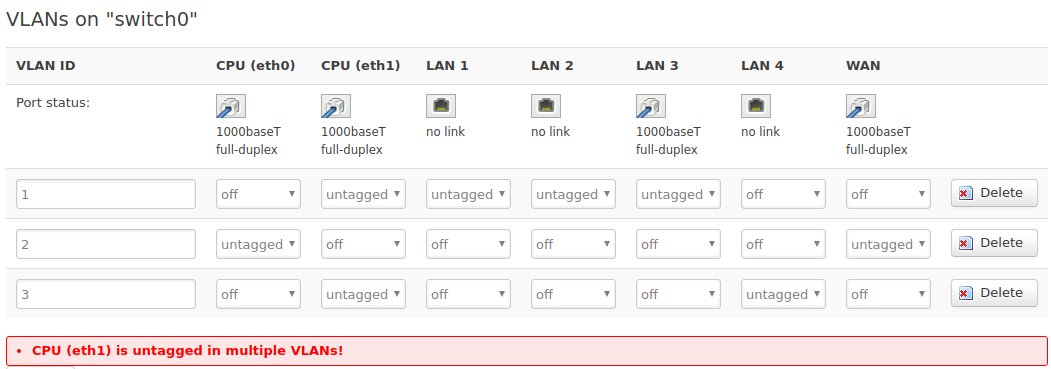
Have you changed the status to "tagged" for all VLANs on cpu/eth1 and tested?
I haven't tried... let's take a step back. I deleted VLAN 3. What would you like me to try changing in VLAN1 and VLAN2?
You wouldn't change anything on VLANs 1 and 2, as they are configured properly. You are working with VLAN 3.
I'm not sure whant you mean by:
You need a VLAN specified in interfaces setup including its IP range, etc. If you deleted that, you'll have to add it again. Regarding the Switch settings, I only mentioned tagging the CPU:
- Add VLAN 3 to CPU/eth1 as “Tagged”
- Change VLAN 1 on CPU/eth1 to “Tagged”
- Remove VLAN 1 from LAN 4 by changing it to “Off”
- Add VLAN 3 to LAN 4 by changing it from “Off” to “Untagged”
- Hit “Save and Apply”
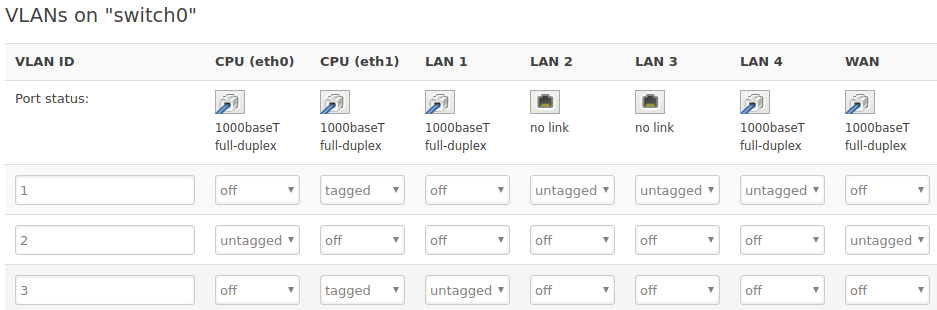
Sorry... I thought you were suggesting something about the default state of mine vs. yours.... I re-added VLAN3 and made the changes you proposed as summarized in the screenshot below. Upon hitting "save and apply," a yellow box came up stating: Interface "lan" device auto-migrated from "eth1" to "eth1.1".
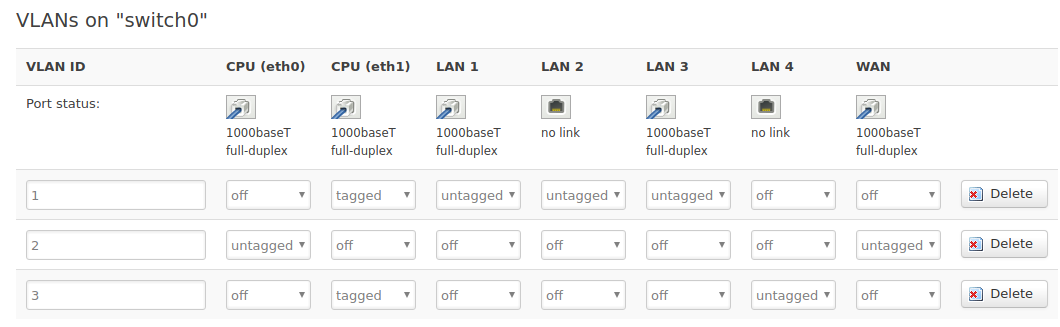
I went into Network>interfaces>GUEST>Edit>Physical Settings and checked "Switch VLAN: "eht1.3" Then booted a machine (dhcp) connected directly to port 4 but it did not receive an IP in the range defined in my guestzone. How do we associate VLAN3 with the guestzone interface?
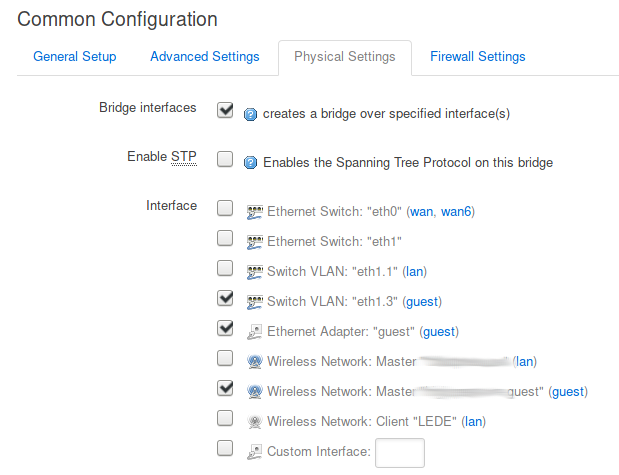
VLAN 3 appears to be properly setup on the Router and Switch...You should be able to test at this point by statically assigning an IP and attempting to reach the router. But let's work on the DHCP for your VLAN 3...
Did you enable DHCP server and specify how many hosts should receive dynamic IPs (size of the DHCP pool)?
- First, you go to INTERFACES > then click on your Guest-LAN
- Under the Common Confguration section, you should see DHCP.
- Be sure to specify the beginning IP to be issued and how many IPs to hand out (e.g. place "2" and a limit of "10" to make a dynamic pool of xxx.xxx.xxx.2 - xxx.xxx.xx.11). The lease time should have a default of 12h.
- Lastly, check the "Dynamic DHCP" button on the advanced tab.
Also, make sure that your router accepts inbound DHCP Request traffic from the Guest Firewall Zone, as the issue could be your DCHP request packets are being dropped or rejected.
I browsed to the hardware page but didn't see anything about mapping. I then did an experiment: I plugging cable into port 1 and watched the icon in Network>Switch. I saw "no link" over 1,2, and 3 and "1000baseT full-duplex" over 4. After walking for cable down the other ports I determined that they are mapped precisely backwards.
Physical 1 --> LAN4
Physical 2 --> LAN3
Physical 3 --> LAN2
Physical 4 --> LAN1
SO... I left the device to be wired-connected to Physical 4 and adjusted Network>Switch as shown below and it did indeed get a correct IP address in the subnet I wanted it to!
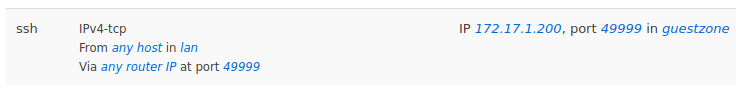
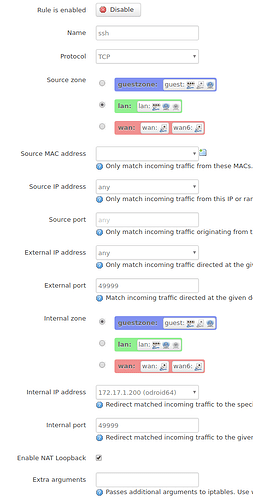
Now have I been trying and failing to create a firewall rule to allow the ssh traffic on port 49999 from any host on LAN to a specific host in the guestzone.
Here is the summary rule that does not work (I get ssh: connect to host odroid64 port 49999: Connection refused when I try):
Here is the long version...
Note - I know odroid64 is accepting ssh on port 49999 because I can ssh into the LEDE router and from there successfully connect via:
ssh -p 49999 user@odroid64
Halting the firewall on the router /etc/init.d/firewall stop allows the connect to work so it has to be something I setup incorrectly. Thanks for your insights and continued patients with me ![]()
EDIT2: This is scary... it seems as through LAN and WAN are also mis-mapped. If I attempt to ssh to my external IP address using the above rule, I actually connect just fine.
ssh -p 49999 myuser@mydomain.com
Last login: Thu Oct 19 18:16:42 2017 from ...
myuser@odroid64 ~ %
- First...does device 172.17.1.200 have port tcp/22 open or port tcp/49999 for SSH?
- You don't connect to the router as no Network Address Translation is needed...both devices are known to the system, it can route it...that brings me to this...
- You appear to have made a Port Forward, instead of a Traffic Rule
- Your Traffic Rule should read: "IPv4-tcp From any host in lan to IP 172.17.1.200 at port 22 in guestzone" (use 49999 only if you configured that SSH server to use that port instead of 22)
Yes, it's listening on both ports.
Yes! I misunderstood your suggestion for a port forwarding setup and in fact I needed a traffic rule. That solved the problem for me:

Thanks again for your help... I would have never figured out the switch settings without it ![]()
If I wanted to make it more generic so I could connect to any number of machines in the guestzone, would I just define the IP in the guestzone as 172.17.1.0/24 or is there a more proper way?
Well...are you testing this from the INTERNET or from inside your LAN???
- If you're testing from the LAN, that's why the rules works when you switch it (meaning, you also need a local firewall rule if they are in 2 difffernt zones)
- You have to test the HTTPS connection from the correct zone (the Internet)
- If both client and server are on the same LAN, use the Public IP address, and make sure you enabled "Enable NAT Loopback"
- Testing between LANs may be a little more complex, you may have to configure NAT re-directs (which place the packet in the other LAN, then routes it) or a port forward, allowing the router to NAT (this is what you configured)
If you want to make it generic, remove 172.17.1.200 and change it to ANY or 172.17.1.0/24
Thanks... I figured it out and edited after you quoted me, but I think I'm good with it now as I typed it.
Thank you very much for all the advise and direction you provided to me.