I appreciate the help.
I was able to get my old certificates working, but I made them back in 2014. I wanted to create new ones with better encryption. I have a spare router and am playing with this until I feel comfortable to put this on our (now) mission critical system.
Like I did back in 2014, I installed openvpn/openssh/easyrsa on a linux machine and went through and created certificates and keys. I run Arch Linux and it is running easyrsa 3 today, so some commands are a bit different. I am certain I am doing something wrong because when I put the newly generated certificates and keys in the same format and put them on the server and try to connect, I cannot.
These are the commands I used to create the certificates and keys:
easyrsa clean-all
easyrsa build-ca nopass
openssl dhparam -out dh2048.pem 2048
easyrsa gen-req server nopass
easyrsa sign-req server server nopass
easyrsa gen-req client_1 nopass
openvpn --genkey --secret ta.key
openssl dhparam -out dh2048.pem 2048
this generates my files that I sftp onto the router:
-rw-r--r-- 1 root root 1204 May 19 20:33 ca.crt
-rw-r--r-- 1 root root 1679 May 19 20:33 ca.key
-rw-r--r-- 1 root root 424 May 19 20:33 dh2048.pem
-rw-r--r-- 1 root root 4608 May 19 20:46 server.crt
-rw-r--r-- 1 root root 1704 May 19 20:33 server.key
-rw-r--r-- 1 root root 636 May 19 20:33 ta.key
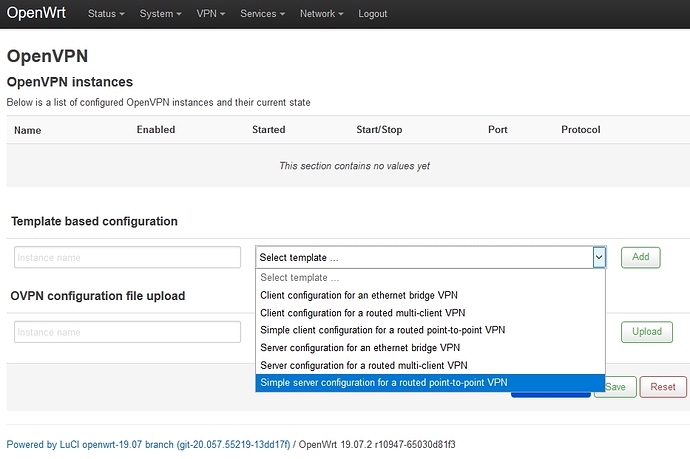
I make sure all the files are linked back up in teh GUI (the pem was 1024 and now it is 2048) and restart the ovpn server. Server comes up no errors and I try to connect and cannot. I get a timeout on the client end.
5/19/2020, 4:28:38 PM OpenVPN core 3.git::f225fcd0 win x86_64 64-bit PT_PROXY built on Mar 19 2020 21:16:20
⏎5/19/2020, 4:28:38 PM Frame=512/2048/512 mssfix-ctrl=1250
⏎5/19/2020, 4:28:38 PM UNUSED OPTIONS
4 [resolv-retry] [infinite]
5 [nobind]
6 [persist-key]
7 [persist-tun]
10 [auth-nocache]
⏎5/19/2020, 4:28:38 PM Contacting 192.168.2.2:1194 via UDP
⏎5/19/2020, 4:28:38 PM Connecting to [192.168.2.2]:1194 (192.168.2.2) via UDPv4
⏎5/19/2020, 4:28:38 PM Tunnel Options:V4,dev-type tun,link-mtu 1541,tun-mtu 1500,proto UDPv4,keydir 1,cipher BF-CBC,auth SHA1,keysize 128,tls-auth,key-method 2,tls-client
⏎5/19/2020, 4:28:38 PM Creds: UsernameEmpty/PasswordEmpty
⏎5/19/2020, 4:28:38 PM Peer Info:
IV_GUI_VER=OCmacOS_3.1.3-713
IV_VER=3.git::f225fcd0
IV_PLAT=win
IV_NCP=2
IV_TCPNL=1
IV_PROTO=2
IV_AUTO_SESS=1
IV_BS64DL=1
⏎5/19/2020, 4:28:38 PM EVENT: RESOLVE ⏎5/19/2020, 4:28:38 PM EVENT: WAIT ⏎5/19/2020, 4:28:38 PM EVENT: CONNECTING ⏎5/19/2020, 4:28:38 PM VERIFY OK : depth=1
cert. version : 3
serial number : 0C:7E:B4:7E:F6:EC:F6:6C:C3:78:FE:C6:2C:84:A1:2C:EB:7E:EE:1D
issuer name : CN=Easy-RSA CA
subject name : CN=Easy-RSA CA
issued on : 2020-05-19 20:18:10
expires on : 2030-05-17 20:18:10
signed using : RSA with SHA-256
RSA key size : 2048 bits
basic constraints : CA=true
key usage : Key Cert Sign, CRL Sign
⏎5/19/2020, 4:28:38 PM VERIFY OK : depth=0
cert. version : 3
serial number : 37:1D:FE:8E:4D:3A:E6:9F:33:41:07:08:01:5E:E5:C6
issuer name : CN=Easy-RSA CA
subject name : CN=server
issued on : 2020-05-19 20:39:44
expires on : 2022-08-22 20:39:44
signed using : RSA with SHA-256
RSA key size : 2048 bits
basic constraints : CA=false
subject alt name : server
key usage : Digital Signature, Key Encipherment
ext key usage : TLS Web Server Authentication
⏎5/19/2020, 4:29:18 PM Session invalidated: KEEPALIVE_TIMEOUT
⏎5/19/2020, 4:29:18 PM Client terminated, restarting in 2000 ms...
⏎5/19/2020, 4:29:20 PM EVENT: RECONNECTING
With my old certificates, I get immediate connection and no errors:
5/19/2020, 4:19:31 PM OpenVPN core 3.git::f225fcd0 win x86_64 64-bit PT_PROXY built on Mar 19 2020 21:16:20
⏎5/19/2020, 4:19:31 PM Frame=512/2048/512 mssfix-ctrl=1250
⏎5/19/2020, 4:19:31 PM UNUSED OPTIONS
4 [resolv-retry] [infinite]
5 [nobind]
6 [persist-key]
7 [persist-tun]
10 [auth-nocache]
⏎5/19/2020, 4:19:31 PM Contacting 192.168.2.2:1194 via UDP
⏎5/19/2020, 4:19:31 PM Connecting to [192.168.2.2]:1194 (192.168.2.2) via UDPv4
⏎5/19/2020, 4:19:31 PM Tunnel Options:V4,dev-type tun,link-mtu 1541,tun-mtu 1500,proto UDPv4,keydir 1,cipher BF-CBC,auth SHA1,keysize 128,tls-auth,key-method 2,tls-client
⏎5/19/2020, 4:19:31 PM Creds: UsernameEmpty/PasswordEmpty
⏎5/19/2020, 4:19:31 PM Peer Info:
IV_GUI_VER=OCmacOS_3.1.3-713
IV_VER=3.git::f225fcd0
IV_PLAT=win
IV_NCP=2
IV_TCPNL=1
IV_PROTO=2
IV_AUTO_SESS=1
IV_BS64DL=1
⏎5/19/2020, 4:19:31 PM EVENT: RESOLVE ⏎5/19/2020, 4:19:31 PM EVENT: WAIT ⏎5/19/2020, 4:19:31 PM EVENT: CONNECTING ⏎5/19/2020, 4:19:31 PM VERIFY OK : depth=0
cert. version : 3
serial number : 01
issuer name : C=US, ST=IL, L=Chicago, O=Griders, OU=changeme, CN=changeme, ??=changeme, emailAddress=grider.4@osu.edu
subject name : C=US, ST=IL, L=Chicago, O=Griders, OU=changeme, CN=changeme, ??=changeme, emailAddress=grider.4@osu.edu
issued on : 2014-04-13 15:19:02
expires on : 2024-04-10 15:19:02
signed using : RSA with SHA1
RSA key size : 1024 bits
basic constraints : CA=false
cert. type : SSL Server
key usage : Digital Signature, Key Encipherment
ext key usage : TLS Web Server Authentication
⏎5/19/2020, 4:19:31 PM SSL Handshake: TLSv1.2/TLS-ECDHE-RSA-WITH-AES-256-GCM-SHA384
⏎5/19/2020, 4:19:31 PM Session is ACTIVE
⏎5/19/2020, 4:19:31 PM Sending PUSH_REQUEST to server...
⏎5/19/2020, 4:19:31 PM EVENT: GET_CONFIG ⏎5/19/2020, 4:19:31 PM OPTIONS:
0 [comp-lzo] [no]
1 [dhcp-option] [DNS] [192.168.2.1]
2 [route] [192.168.66.0] [255.255.255.0]
3 [topology] [net30]
4 [ping] [10]
5 [ping-restart] [120]
6 [ifconfig] [192.168.66.6] [192.168.66.5]
7 [peer-id] [0]
8 [cipher] [AES-256-GCM]
⏎5/19/2020, 4:19:31 PM PROTOCOL OPTIONS:
cipher: AES-256-GCM
digest: SHA1
compress: LZO_STUB
peer ID: 0
⏎5/19/2020, 4:19:31 PM CAPTURED OPTIONS:
Session Name: 192.168.2.2
Layer: OSI_LAYER_3
Remote Address: 192.168.2.2
Tunnel Addresses:
192.168.66.6/30 -> 192.168.66.5 [net30]
Reroute Gateway: IPv4=0 IPv6=0 flags=[ IPv4 ]
Block IPv6: no
Add Routes:
192.168.66.0/24
Exclude Routes:
DNS Servers:
192.168.2.1
Any ideas as to what is going on? The rest of the settings are the same (maybe the problem?) The only one that I think may be related is the Cipher which doesn't change at AES-256-CBC. I do not know what else I would change it to, though.
In the meantime, I'll run the certificate generation recipe on the router and see how it goes.
TIA