The NextDNS client on OpenWRT is problematic. Before discovering AdGuardHome, I have made a ticket on the NextDNS Support and I was recommended to use AdGuardHome and just using NextDNS as my upstream server.
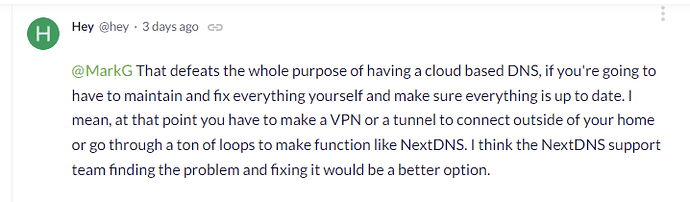
Network Latency Issues - Philippines - Bug Reports - NextDNS Help Center
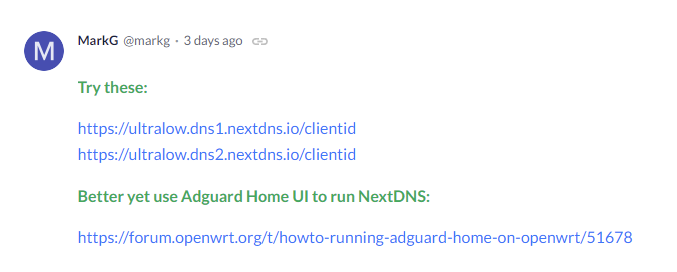
So my current setup:
- All devices that supports NextDNS (Apple devices mainly, will use the NextDNS Profile)
- All devices that do not natively support NextDNS or requires running an app to function goes to AGH.
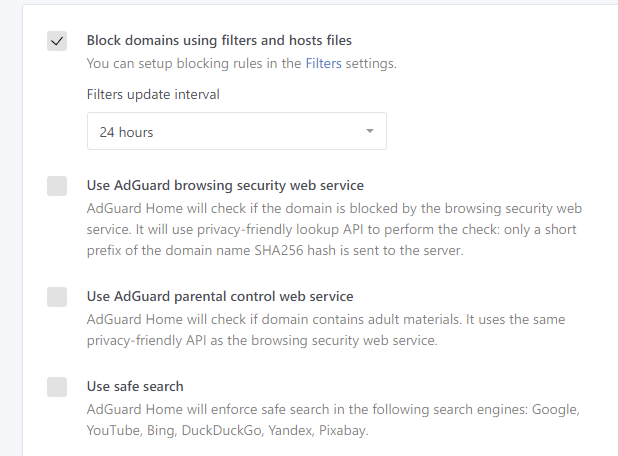
Both NextDNS and AGH use the same list. OISD + 1Hosts (Lite).
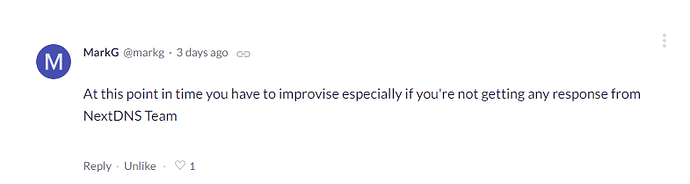
In the end, I would be using NextDNS over AdGuard's browsing security service
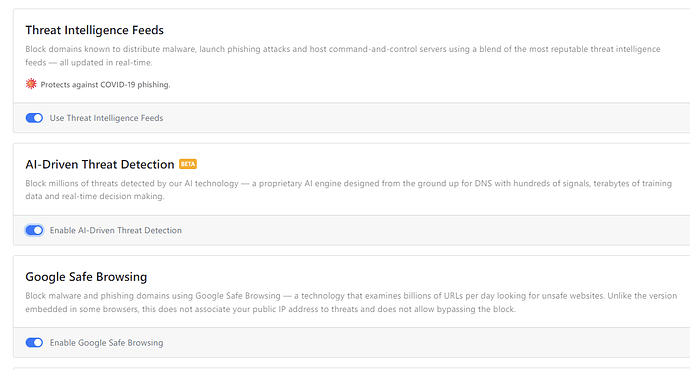
And NextDNS just overtook Google in the DNS Performance Charts.