Pieced this together along with some of my own thoughts and is really good for me but now want to get the opinion of others appreciate any ideas, criticism or feedback
/root/dscp.sh
#!/bin/bash -x
IPT="iptables"
# Latency Sensitive (CS7, CS6, EF, VA, CS5, CS4)
# Streaming Media (AF4x, AF3x, CS3, AF2x, TOS4, CS2, TOS1)
# Best Effort (CS0, AF1x, TOS2, and those not specified)
# Background Traffic (CS1)
$IPT -t mangle -N dscp_mark > /dev/null 2>&1
$IPT -t mangle -F dscp_mark
$IPT -t mangle -A dscp_mark -i wan -j DSCP --set-dscp-class CS0
$IPT -t mangle -A dscp_mark -s 192.168.1.0/24 -j DSCP --set-dscp-class CS0
iptmark(){
$IPT -t mangle -A dscp_mark "$@"
}
## check if POSTROUTING already exits then jumps to our tables if not, add them
$IPT -t mangle -L POSTROUTING -n | grep dscp_mark || $IPT -t mangle -A POSTROUTING -j dscp_mark
sport1="3658"
sport2="9305:9308"
sport3="3074:3079"
dport1="3478:3479"
dport2="9305:9308"
dport3="1117,1247,3074:3079,3893,7130,7463"
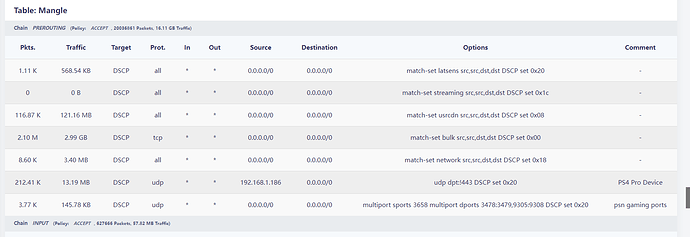
$IPT -t mangle -A PREROUTING -m set --match-set latsens srcip,srcport,dstip,dstport -j DSCP --set-dscp-class CS4 ## set dscp tag for our (latsens) ipset
$IPT -t mangle -A PREROUTING -m set --match-set streaming srcip,srcport,dstip,dstport -j DSCP --set-dscp-class AF32 ## set dscp tag for our (streaming) ipset
$IPT -t mangle -A PREROUTING -m set --match-set usrcdn srcip,srcport,dstip,dstport -j DSCP --set-dscp-class CS1 ## set dscp tag for our (usrcdn) ipset
$IPT -t mangle -A PREROUTING -p tcp -m set --match-set bulk srcip,srcport,dstip,dstport -j DSCP --set-dscp-class CS0 ## set dscp tag for our (bulk) ipset
$IPT -t mangle -A PREROUTING -m set --match-set network srcip,srcport,dstip,dstport -j DSCP --set-dscp-class CS3 ## set dscp tag for our (network) ipset
$IPT -t mangle -A PREROUTING -p udp -s 192.168.1.186 ! --dport 443 -m comment --comment "PS4 Pro Device" -j DSCP --set-dscp-class CS4
$IPT -t mangle -A PREROUTING -p udp -m multiport --sports $sport1 -m multiport --dports $dport1,$dport2 -j DSCP --set-dscp-class CS4 -m comment --comment "psn gaming ports"
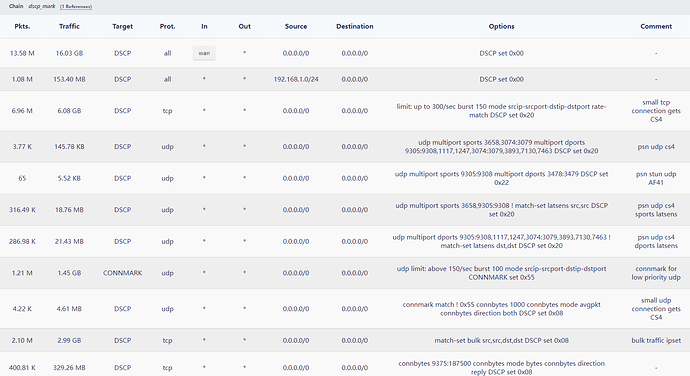
iptmark -p tcp -m hashlimit --hashlimit-name tcp_high_prio --hashlimit-upto 300/second --hashlimit-burst 150 --hashlimit-mode srcip,srcport,dstip,dstport --hashlimit-rate-match --hashlimit-rate-interval 1 -j DSCP --set-dscp-class CS4 -m comment --comment "small tcp connection gets CS4"
iptmark -p udp -m udp -m multiport --sports $sport1,$sport3 -m multiport --dports $dport2,$dport3 -m comment --comment "psn udp cs4" -j DSCP --set-dscp-class CS4
iptmark -p udp -m udp -m multiport --sports $sport2 -m multiport --dports $dport1 -m comment --comment "psn stun udp AF41" -j DSCP --set-dscp-class AF41
iptmark -p udp -m udp -m multiport --sports $sport1,$sport2 -m set ! --match-set latsens srcip,srcport -j DSCP --set-dscp-class CS4 -m comment --comment "psn udp cs4 sports latsens"
iptmark -p udp -m udp -m multiport --dports $dport2,$dport3 -m set ! --match-set latsens dstip,dstport -j DSCP --set-dscp-class CS4 -m comment --comment "psn udp cs4 dports latsens"
iptmark -p udp -m udp -m hashlimit --hashlimit-mode srcip,srcport,dstip,dstport --hashlimit-name udp_low_prio --hashlimit-above 150/second --hashlimit-burst 100 -j CONNMARK --set-mark 0x55 -m comment --comment "connmark for low priority udp"
iptmark -p udp -m connmark ! --mark 0x55 -m connbytes --connbytes 1000: --connbytes-dir both --connbytes-mode avgpkt -j DSCP --set-dscp-class CS1 -m comment --comment "large udp connection gets CS1"
iptmark -p tcp -m set --match-set bulk srcip,srcport,dstip,dstport -j DSCP --set-dscp-class CS1 -m comment --comment "bulk traffic ipset"
iptmark -p tcp -m connbytes --connbytes 9375:187500 --connbytes-dir reply --connbytes-mode bytes -j DSCP --set-dscp-class CS1
iptmark -p tcp -m connbytes --connbytes 187500: --connbytes-dir reply --connbytes-mode bytes -j DSCP --set-dscp-class CS0
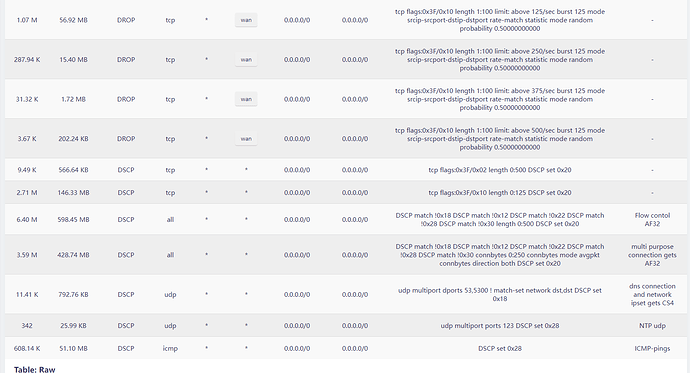
ackrate=125
iptmark -p tcp -m tcp --tcp-flags ALL ACK -o wan -m length --length 1:100 -m hashlimit --hashlimit-mode srcip,srcport,dstip,dstport --hashlimit-name ackfilter1 --hashlimit-above "${ackrate}/second" --hashlimit-burst $ackrate --hashlimit-rate-match --hashlimit-rate-interval 1 -m statistic --mode random --probability .5 -j DROP
iptmark -p tcp -m tcp --tcp-flags ALL ACK -o wan -m length --length 1:100 -m hashlimit --hashlimit-mode srcip,srcport,dstip,dstport --hashlimit-name ackfilter2 --hashlimit-above "$((ackrate*2))/second" --hashlimit-burst $ackrate --hashlimit-rate-match --hashlimit-rate-interval 1 -m statistic --mode random --probability .5 -j DROP
iptmark -p tcp -m tcp --tcp-flags ALL ACK -o wan -m length --length 1:100 -m hashlimit --hashlimit-mode srcip,srcport,dstip,dstport --hashlimit-name ackfilter3 --hashlimit-above "$((ackrate*3))/second" --hashlimit-burst $ackrate --hashlimit-rate-match --hashlimit-rate-interval 1 -m statistic --mode random --probability .5 -j DROP
iptmark -p tcp -m tcp --tcp-flags ALL ACK -o wan -m length --length 1:100 -m hashlimit --hashlimit-mode srcip,srcport,dstip,dstport --hashlimit-name ackfilter4 --hashlimit-above "$((ackrate*4))/second" --hashlimit-burst $ackrate --hashlimit-rate-match --hashlimit-rate-interval 1 -m statistic --mode random --probability .5 -j DROP
iptmark -p tcp -m tcp --tcp-flags ALL SYN -m length --length 0:500 -j DSCP --set-dscp-class CS4
iptmark -p tcp -m tcp --tcp-flags ALL ACK -m length --length 0:125 -j DSCP --set-dscp-class CS4
iptmark -m dscp ! --dscp 24 -m dscp ! --dscp 18 -m dscp ! --dscp 34 -m dscp ! --dscp 40 -m dscp ! --dscp 48 -m length --length 0:500 -j DSCP --set-dscp-class CS4 -m comment --comment "Flow contol AF32"
iptmark -m dscp ! --dscp 24 -m dscp ! --dscp 18 -m dscp ! --dscp 34 -m dscp ! --dscp 40 -m dscp ! --dscp 48 -m connbytes --connbytes 0:250 --connbytes-dir both --connbytes-mode avgpkt -j DSCP --set-dscp-class CS4 -m comment --comment "multi purpose connection gets AF32"
iptmark -p udp -m udp -m multiport --dports 53,5300 -m set ! --match-set network dstip,dstport -j DSCP --set-dscp-class CS3 -m comment --comment "dns connection and network ipset gets CS4"
iptmark -p udp -m udp -m multiport --port 123 -j DSCP --set-dscp-class CS5 -m comment --comment "NTP udp"
iptmark -p icmp -j DSCP --set-dscp-class CS5 -m comment --comment "ICMP-pings"
/etc/dnsmasq.conf... I use this to minimize priority to other connections and also to prioritize gaming cdn servers although I do need to clean this up a bit but is a good example I think
##CS4
ipset=/zcure-blr-ps4-east-us.hardsuitlabs.com/latsens
##CS3
ipset=/*.res.spectrum.com/Fortune-3.lan/network
ipset=/service.playstation.net/ps4.np.playstation.net/34-213-59-198-pushcl.np.communication.playstation.net/*.np.communication.playstation.net/sie.com/*.sie.com/network
ipset=/pspro.lan/network
ipset=/*.rockstargames.com/network
##CS1
ipset=/party.rnps.dl.playstation.net/googletagmanager.com/googleusercontent.com/clients4.google.com/*.googleusercontent.com/google.com/fbcdn.net/*.fbcdn.net/akamaihd.net/*.akamaihd.net/whatsapp.net/*.whatsapp.net/whatsapp.com/*.whatsapp.com/www-cdn.whatsapp.net/googleapis.com/*.googleapis.com/ucy.ac.cy/1e100.net/hwcdn.net/usrcdn
##CS0
# Youtube is also isolated by my isp
ipset=/g.live.com/googlevideo.com/*.googlevideo.com/rr1---sn-vgqskned.googlevideo.com/rr2---sn-vgqskned.googlevideo.com/rr3---sn-vgqskned.googlevideo.com/rr4---sn-vgqskned.googlevideo.com/bulk
# AmazonVideo
ipset=/s3.ll.dash.row.aiv-cdn.net/aiv-delivery.net/amazonaws.com/bulk
# Facebook
ipset=/fbcdn.net/bulk
# Twitch
ipset=/ttvnw.net/bulk
# VeVo
ipset=/vevo.com/events.cid.samba.tv/bulk
# Spotify
ipset=/audio-fa.scdn.cot/oldtv.lan/streaming
# Deezer
ipset=/deezer.com/bulk
# SoundCloud
ipset=/sndcdn.com/bulk
# last.fm
ipset=/last.fm/bulk
#reddit videos
ipset=/v.redd.it/bulk
#twitch.tv
ipset=/ttvnw.net/par10s27-in-f206.1e100.net/bulk
#Netflix
ipset=/*nflxvideo*/nrdp.prod.ftl.netflix.com/secure.netflix.com/occ-0-132-1239.1.nflxso.net/bulk
ipset=/*.googlevideo.com/bulk
ipset=/*.amazon.com/bulk
ipset=/download.qq.com/bulk
ipset=/*.1drv.*/bulk
ipset=/*.onedrive.*/bulk
ipset=/*.mega.*/bulk
ipset=/*.steamcontent.*/bulk
ipset=/*.tiktok.*/frontier.us.tiktokv.com/*.us.tiktokv.com/Bedroom.lan/Fortune-3.lan/sonytv.lan/lds-ldr-production.tvinteractive.tv/bulk
ipset=/*.ttvnw.*/bulk
ipset=/api.amazonalexa.com/tvmeta-dynamic.tvinteractive.tv/events.cid.samba.tv/service-stitcher.clusters.pluto.tv/siloh-fs.plutotv.net/plutotv.com/k.pluto.tv/siloh.pluto.tv/*.pluto.tv/*.1.oca.nflxvideo.net/ord37s24-in-f8.1e100.net/api-global.netflix.com/*.netflix.com/bulk
# Steam Download
ipset=/steamcontent.com/bulk
# PSN Download
ipset=/gs2.ww.prod.dl.playstation.net/clientsettingscdn.roblox.com/ecsv2.roblox.com/*.roblox.com/.ubisoft.com/bulk
# DropBox
ipset=/dropbox.com/dropboxstatic.com/dropbox-dns.com/log.getdropbox.com/*dropboxusercontent*/*drive.google*/bulk
# Google Drive
ipset=/drive.google.com/drive-thirdparty.googleusercontent.com/bulk
# Google Docs
ipset=/docs.google.com/docs.googleusercontent.com/bulk
# PlayStore Download
ipset=/gvt1.com/bulk
# WhatsApp Files
ipset=/mmg-fna.whatsapp.net/bulk
# Youtube Upload
ipset=/upload.youtube.com/upload.video.google.com/bulk
# WindowsUpdate
ipset=/windowsupdate.com/update.microsoft.com/bulk
Also added /etc/iproute2/rt_dsfields
# Differentiated field values
# These include the DSCP and unused bits
0x0 default
CS0 000000 0 [RFC2474]
CS1 001000 8 [RFC2474]
CS2 010000 16 [RFC2474]
CS3 011000 24 [RFC2474]
CS4 100000 32 [RFC2474]
CS5 101000 40 [RFC2474]
CS6 110000 48 [RFC2474]
CS7 111000 56 [RFC2474]
AF11 001010 10 [RFC2597]
AF12 001100 12 [RFC2597]
AF13 001110 14 [RFC2597]
AF21 010010 18 [RFC2597]
AF22 010100 20 [RFC2597]
AF23 010110 22 [RFC2597]
AF31 011010 26 [RFC2597]
AF32 011100 28 [RFC2597]
AF33 011110 30 [RFC2597]
AF41 100010 34 [RFC2597]
AF42 100100 36 [RFC2597]
AF43 100110 38 [RFC2597]
EF 101110 46 [RFC3246]
VOICE-ADMIT 101100 44
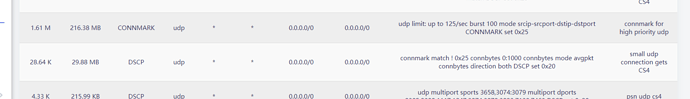
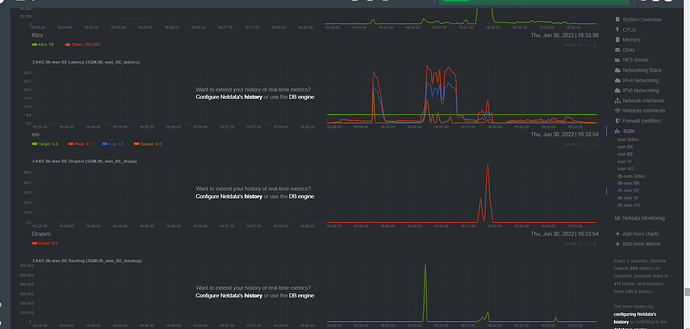
Firewall pics... kids pissed me off so made all streaming bulk for now also put everyone else on guest_network to limit priority and use of upnp...
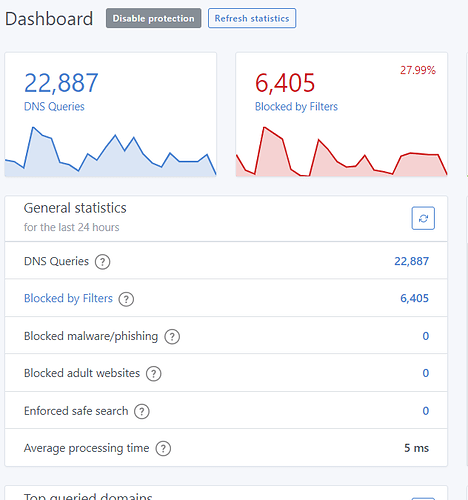
also 5ms dns with adguardhome...