Hello everybody,
this is a small guide for Adguard Home, an equivalent alternative to Pi-Hole.
To use Adguard Home on an OpenWrt router you need at least 20 MB free storage and about 100 MB free RAM (it can be started from a USB stick; the more RAM, the better). I‘m running Adguard Home on a Netgear R7800.
Ads/trackers/malware etc. are blocked by DNS. The DNS lists can be copied 1:1 from Pi-Hole or equivalent sources. Regex is also supported.
- The big advantage over Pi-Hole is that Adguard Home does not need any dependencies and can be started from a single binary file.
- Adguard Home comes with its own web interface, which can be accessed on a self-selected port.
- The DNS server can be operated in parallel to dnsmasq.
- DNS over TLS and HTTPS are supported by default.
- Adguard Home can be started automatically via /etc/rc.local by simply executing the binary
Since it is programmed in Go, many architectures are already supported:
https://github.com/AdguardTeam/AdGuardHome/releases
1. Installation
The installation is relatively simple. The corresponding release must be downloaded and unpacked.
The application starts via ./AdguardHome and all necessary settings can be made via the web interface.
ssh root@192.168.1.1
opkg update && opkg install wget
mkdir /opt/ && cd /opt
wget -c https://github.com/AdguardTeam/AdGuardHome/releases/download/v0.101.0/AdGuardHome_linux_armv5.tar.gz
tar xfvz AdGuardHome_linux_armv5.tar.gz
rm AdGuardHome_linux_armv5.tar.gz
Either just run it:
/opt/AdGuardHome/AdGuardHome
or install it directly with:
/opt/AdGuardHome/AdGuardHome -s install
It is also possible to run it in the background (manually started):
opkg update && opkg install coreutils-nohup
nohup /mnt/usb/AdGuardHome/AdGuardHome > /dev/null 2>&1&
1.1. Attention
!!!! It is possible to install AdguardHome under /opt/, but this directory can grow. Old binaries are moved as backup after an update. blocklists can become relatively large. it is better to move AdGuardHome to a USB stick. So it will survive future OpenWRT updates !!!!
2. Configuration
After AdguardHome is started on the router, open the browser and start the AdGuard Home web interface
2.1 DNS Port
I have the Adguard Home DNS server running at 192.168.1.1:5353
2.1 HTTP Port
web interface at 192.168.1.1:8080.
2.2 /etc/conf/dhcp
Accordingly, the /etc/conf/dhcp config must be adjusted and the new DNS server must be defined:
config dnsmasq
option domainneeded '1'
option localise_queries '1'
option rebind_protection '1'
option rebind_localhost '1'
option local '/lan/'
option domain 'lan'
option expandhosts '1'
option authoritative '1'
option readethers '1'
option leasefile '/tmp/dhcp.leases'
option localservice '1'
list server '192.168.1.1#5353'
2.3 /etc/firewall.user
Prevent DNS leaks and force all connected devices to use the new DNS port:
iptables -t nat -A PREROUTING -i br-lan -p udp --dport 53 -j DNAT --to 192.168.1.1:5353
iptables -t nat -A PREROUTING -i br-lan -p tcp --dport 53 -j DNAT --to 192.168.1.1:5353
3. Blocklists and tuning
Good Blocklists:
You may want to add those lists to your http://192.168.1.1:8080/#filters lists.
https://firebog.net/
https://dbl.oisd.nl/
Adguard Home Regex:
Those are really good regex rules which already block 50% of all ads/trackers/bots etc.
You have to add the to http://192.168.1.1:8080/#custom_rules
https://github.com/mmotti/adguard-home-filters/blob/master/regex.txt
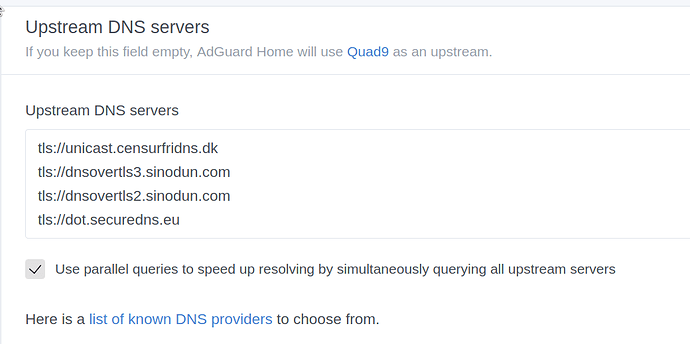
DNS over TLS Upstream Server:
AdGuardHome supports TLS DNS for more privacy. Dhe dns requests are much slower though. some dns servers are sometimes down and somehow it is still a bit buggy. sometimes AdGuardHome crashes if you do the upstream test more often.
https://dnsprivacy.org/wiki/display/DP/DNS+Privacy+Test+Servers#DNSPrivacyTestServers-DoTservers
DNS Leak Test:
https://www.dnsleaktest.com/results.html
Recommended modifications:
DNS over TLS
Good no-logging-policy DNS Server:
tls://fdns1.dismail.de
tls://dns.neutopia.org
tls://dns.digitale-gesellschaft.ch
Make sure that the upstream servers are working. This is also a good resource: https://kb.adguard.com/en/general/dns-providers
For me it is a super easy alternative to Pi-Hole, without installation effort and many dependencies.
Have fun with it!