Hi, after two weeks of tweaking and some frustration, I did get to run snort in openwrt (19.07.2, on a Zyxel Armor Z2, it has 512MB of RAM, this is important as I'll explain later).
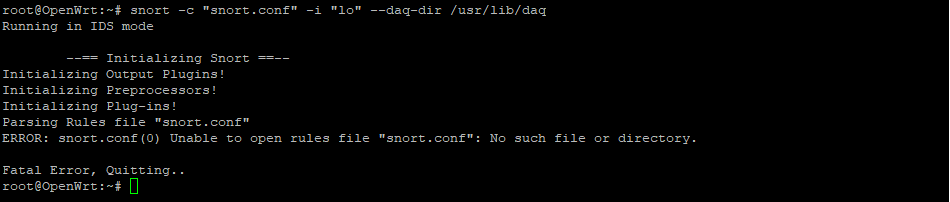
the command that you are trying to execute:
it only activates snort in IDS mode using DAQ in passive mode.
in order to activate snort in IPS mode (Intrusion Prevention) you need to be able to run it in inline mode, which in OpenWRT you only have "AFPACKET" to run it, BUT, this is pretty hard on the RAM, I only get about 25MB of free RAM on average when running snort in inline mode with all of my other configuration in place (VPN Server and client, DPI, are the next more intensive after snort, and dont come even close to the RAM demands of snort 6% and 8% respectively). Snort by itself is consuming 48% of my RAM, and that is after getting a lot of rules out just running with the bare minimum.
It is important to note, that even in IDS snort is pretty intensive, where it gobbles a hefty 41% of RAM with the same ruleset that is used in inline, the difference is due to the preprocessors that are the ones that do the trick for inline mode.
The command to execute snort in IPS (afpacket, in inline mode) if you have the resources is:
snort -de -Q -i eth0:eth1 --daq afpacket --daq-dir /usr/lib/daq -c "/etc/snort/snort.conf"
where:
"-Q" is for "inline mode";
"-i eth0:eth1" is for the pair of interfaces required for afpacket, depending on your configuration could be other interfaces but it is required always to be in pair.;
"--daq afpacket", indicates that the DAQ to use is "afpacket", "pcap", can only run in passive mode (IDS), and IPFW only supports IP4 traffic, and requires that you define the ports you want it to listen (so just keep it on afpacket if you have a mixed environment;
"--daq-dir /usr/lib/daq" is where the daq components are installed; and lastly,
"-c "/etc/snort/snort.conf" " is to indicates where ths snort configuration file is.
keep in mind that running this command if it works, then you need to make it the default mode when ever the router is started, you need to modify the snort file on "/etc/init.d/", in the "#start_snort_instance", the "procd_set_param command" line.
wrapping up, SNORT in openwrt, whether in IDS or IPS mode it requires a lot of memory, 512MB at minimum (256MB just wont work) for even a very stripped version, curiously it does not impact to much the processor, but there is a small caveat, it tends to "eat" some of the bandwidth, but is normal for an IPS, all that said, it is possible to run snort in IPS mode in openwrt, but just with the required hardware.
PS. keep in mind that you need to keep an eye on the logs, it can become a headache eating your precious space in the router, and It is not worth it to have snort run without the logs, because what is the purpose then? you could define a process to periodicaly download the log file, or just generate the log on a remote destination, probably syslog-ng could be useful for that matter, or if your router allows it, attach a usbstick, format it for use in openwrt and your all set.
hope this is useful.
VM.