We have configured a GL.iNet GL-AR750S-Ext (Slate) device that uses OpenWRT and configure to use WireGuard for a VPN. The "Interface" is configured to use a private DNS server (see client config below). Invoking nslookup returns the following:
nslookup not-the-real-dns-name.com.
Server: console.gl-inet.com
Address: 192.168.8.1
*** No internal type for both IPv4 and IPv6 Addresses (A+AAAA) records available for not-the-real-dns-name.com.
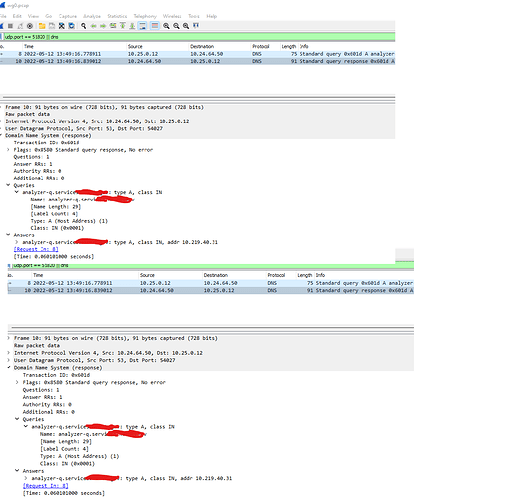
Wireshark capture shows:
- DNS query packet from 10.25.0.12 -> 10.24.64.50
- DNS response packet from 10.24.64.50 -> 10.25.0.12
But it also shows the following, which I'm guessing is because the nslookup checks eth0 as well as wg0:
- WireGuard packet from 65.64.123.123 -> 10.24.0.4
- DNS packet from 10.24.0.4 -> 10.24.64.50
- DNS packet from 10.24.64.50 -> 10.24.0.4
- WireGuard packet from 10.24.0.4 -> 65.64.123.123
Invoking "nslookup not-the-real-dns-name.com. 10.24.64.50" generates a similar packet capture and returns the expected IP address. This makes sense to me because the nslookup is an app performing the queries directly, though I don't understand why there are also packets using WireGuard.
Any ideas of where to look would be appreciated.
[Interface]
PrivateKey = ********************************************
Address = 10.25.0.12
DNS = 10.24.64.50
[Peer]
PublicKey = rtsPkzDDKF*******************MjQ=
AllowedIPs = 0.0.0.0/0
EndPoint = wireguard-1.our-domain.com:51820