vernonjvs wrote:wifidog would only see the IP and MAC address of the OpenWrt device when it is configured in AP+STA mode so wifi dog should not be able to identify any computers connected to the OpenWrt AP and de-authenticate them.
Yes, and exactly this (not be able to identify any computers) is the problem.
vernonjvs wrote:Are you saying that if a user who logged in closes their web browser that this will cause their computer to get de-authenticated from the hotel WiFi hotspot?
Not by closing the browser. Any user gets de-authenticated in wifidog if:
they turn of their wifi connection for more than a few minutes (see below) - be it by leaving the location or by the device entering sleep mode,
the browser's session on the auth server expires (usually after one or more hours),
they log out manually through the login/logout page which is left open in a separate tab.
The code in wifidog responsibe for auto-logout after 10 minutes (or whatever you set as timeout) of inactivity is:
/* Ping the client, if he responds it'll keep activity on the link */
icmp_ping(ip);
/* Update the counters on the remote server only if we have an auth server */
if (config->auth_servers != NULL) {
auth_server_request(&authresponse, REQUEST_TYPE_COUNTERS, ip, mac, token, incoming, outgoing);
}
LOCK_CLIENT_LIST();
if (!(p1 = client_list_find(ip, mac))) {
debug(LOG_ERR, "Node %s was freed while being re-validated!", ip);
} else {
if (p1->counters.last_updated + (config->checkinterval * config->clienttimeout) <= time(NULL)) {
/* Timing out user */
debug(LOG_INFO, "%s - Inactive for %ld seconds, removing client and denying in firewall",
p1->ip, config->checkinterval * config->clienttimeout);
fw_deny(p1->ip, p1->mac, p1->fw_connection_state);
client_list_delete(p1);
/* Advertise the logout if we have an auth server */
if (config->auth_servers != NULL) {
UNLOCK_CLIENT_LIST();
auth_server_request(&authresponse, REQUEST_TYPE_LOGOUT, ip, mac, token, 0, 0);
LOCK_CLIENT_LIST();
}
As you can see, it even advertises the gateway's auto-logout to the central auth server, therefore destroying the session there also.
vernonjvs wrote:I have never seen hotel wifi requiring a special URL to log in. Typically, all web addresses are initially resolved to the portal log in page. Once you log in, normal DNS resolution occurs and there is no log out page.
Absolutely right, the Captive Portal will intercept URLs addressed by the user to re-direct them to the login page. But often users don't even start a browser after connecting to the hotspot's wifi card. They instead start a mailer program or another app on their smart phone/table/laptop and wonder why they "don't get Internet access".
They even tend to ignore the notification e.g. of Android due to the NLA requests send out by the device after associating with the router's wifi card. In latest OS/X the NLA will even prominently show the login page in a big web view window on the screen (implemented in Preferences AFAIK) if such a re-direct appears after connection to the wifi card of the router. There is no doubt, that the NLA scheme has been introduced b/c of high-volume support calls at vendors why "their device won't work with public hotspots" :-)
In the past, hotel managers asked for a flyer with step-by-step instruction on how to log in. The URL of the login page on the central auth server in wifidog is something like login.authserver.domain. This page stays open in a separate tab, not only to allow manual logout, but also to show URLs for the hotel's own website, the city's website, the link to the user's profile, the status of other routers of this hotspot etc. It is not just a cheap login form in wifidog, it's more a fully featured portal page.
Since in Germany we have very stupid laws allowing even lawyers (no judge needed!) to punish hotspot owners or users, which let others download copyrighted material from the web, people here insist of being able to explicitely log out from a public hotspot. I wish, those stupid laws would be dropped, but just yesterday the high court of Germany has refused to declare the new law for prophylactical data storage by ISPs as un-constitutional, therefore allowing lawyer firms to continue spying on IPs, which is an important issue for owners of public hotspots. Each copyright infringment can cost them as much as 700 to 1.500 USD for every single download done by some unauthorized user either because he didn't need to log-in or because he abused some other's account.
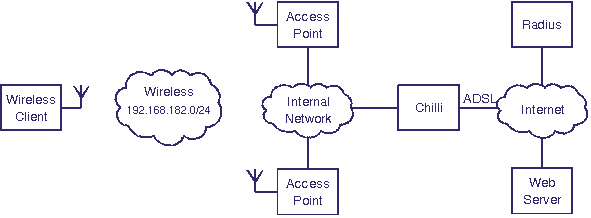
Therefore it is very risky for hotspot owners to set up a repeater which does not enforce a login-/logout-scheme. But it's only a specific usage case, which does not apply to using a repeater for only yourself to avoid having log in with every devices you use, so I completely agree with you in that a STA+AP bridge might be sufficient for most people - but not for all and that was it, what I wanted to point out, especially b/c OpenWRT offers a solution even for this usage case, where devices need to be uniquely identifyable by the hotspot.
(Last edited by R1D2 on 28 Jan 2016, 13:54)