Hi
I’m looking for some advice, I’m a networking novice (apologies) but eager to learn.
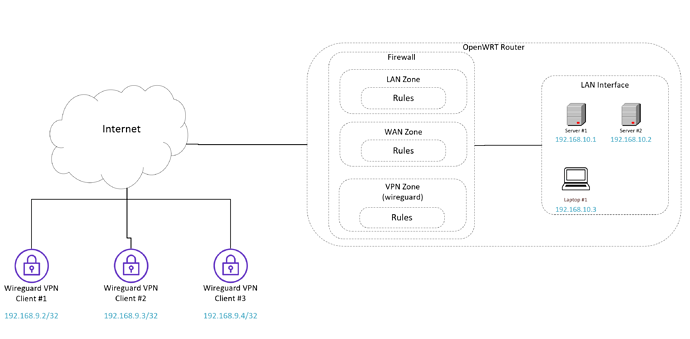
Background: I have a fully working wireguard server (OpenWRT router) / multi-client setup based on the excellent tutorial in the OpenWRT documentation (link). All remote wireguard clients can access any device on the local LAN. NOTE: Within section #3 of the linked documentation it reads “Consider VPN network as private. Assign VPN interface to LAN zone to minimize firewall setup. Allow access to VPN server from WAN zone.”
New Desired State:
My requirement now needs to change, I’d like to limit some, but not all, wireguard clients to a subset of local LAN IPs and their respective Ports.
Approach
To achieve the desired state, I initially assumed (incorrectly), I could simply add a new firewall traffic rule to restrict LAN access based on Wireguard Client IP -> Target LAN IP/Port, but this doesn’t seem possible (due to what I think is layer #2 switching?).
If the above statement is accurate (?), I believe I need to leverage layer #3 switching.
To do this I think I need to remove VPN interface from LAN (as originally instructed by the documentation I followed), and then create a new VPN Firewall Zone and add the VPN interface into this new zone. Once done build up the inbound firewall rules based on the wireguard client source IP Address and local LAN target (IP + Port). Given my lack of knowledge, I’d probably copy all existing WAN zone firewall rules into the newly created VPN Zone, before adding client-specific rules
Does the above sound like the right approach?? Anything I should be aware of, that I’m almost certainly overlooking (probably routing + other things)?
Rules:
An example of wireguard client rules would be:
Wireguard clients: 192.168.9.2, 192.168.9.3, 192.168.9.4
OpenWRT LAN Devices: 192.168.10.1, 192.168.10.2
- Client 192.168.9.2 Access all LAN devices /ports (no restriction)
- Client 192.168.9.3. Only access LAN Device 102.168.10.1 on Port 22
- Client 192.168.9.4. Only access LAN Device 192.168.10.2 on Port 443
Logical Network Diagram
All advice/help gratefully received. I have not tried configuring this yet - I'd like to validate the approach first.
Kind regards