Hi!
I have two routers: TCL (home WiFi) and Fritz (my WiFi). Fritz is connected to TCL via WiFi. I can access 192.168.1.1 (TCL panel) using Fritz. Typing 192.168.2.1 (Fritz panel) using TCL WiFi gives DNS_PROBE_FINISHED_NXDOMAIN error. How do I need to set up firewall rules to achieve this?
Depends on how things are cabled and configured. It might be a simple firewall rule change, or there might be some additional changes needed.
But first up, it primarily depends on whether or not you are using OpenWRT. Are you using OpenWRT? If so, on which of the two devices you mentioned?
I'm using OpenWRT on Fritz7362SL and TCL is on default firmware. A week ago I accidentally did this, so it is possible.
OpenWRT as a Wi-Fi client is both possible and reasonably easy to accomplish... so let's start with checking your configuration.
What are the contents of /etc/config/network, /etc/config/wireless, and /etc/config/firewall from OpenWRT?
Redact any keys/passwords which may be revealed.
wireless:
config wifi-device 'radio0'
option type 'mac80211'
option path 'pci0000:00/0000:00:00.0/0000:01:00.0'
option band '2g'
option htmode 'HT20'
option cell_density '0'
option channel 'auto'
option disabled '0'
config wifi-iface 'wifinet1'
option device 'radio0'
option mode 'sta'
option network 'wwan'
option ssid 'TCL-F65Z-2.4GHz'
option encryption 'psk2'
option key '********'
config wifi-iface 'wifinet2'
option device 'radio0'
option mode 'ap'
option ssid 'nuke-wifi'
option key '********'
option network 'lan'
option encryption 'psk-mixed'
network:
config interface 'loopback'
option device 'lo'
option proto 'static'
option ipaddr '127.0.0.1'
option netmask '255.0.0.0'
config globals 'globals'
option ula_prefix 'fdfc:0dba:6830::/48'
config atm-bridge 'atm'
option vpi '1'
option vci '32'
option encaps 'llc'
option payload 'bridged'
option nameprefix 'dsl'
config dsl 'dsl'
option tone 'av'
option ds_snr_offset '0'
option annex 'b'
config device
option name 'br-lan'
option type 'bridge'
list ports 'lan1'
list ports 'lan2'
list ports 'lan3'
list ports 'lan4'
config device
option name 'lan1'
option macaddr '**:**:**:**:**:**'
config device
option name 'lan2'
option macaddr '**:**:**:**:**:**'
config device
option name 'lan3'
option macaddr '**:**:**:**:**:**'
config device
option name 'lan4'
option macaddr '**:**:**:**:**:**'
config interface 'lan'
option device 'br-lan'
option proto 'static'
option netmask '255.255.255.0'
option ip6assign '60'
option ipaddr '192.168.2.1'
config device
option name 'dsl0'
option macaddr '**:**:**:**:**:**'
config interface 'wan'
option device 'dsl0'
option proto 'pppoe'
option username 'username'
option password 'password'
option ipv6 '1'
option ifname 'usb0'
config interface 'wan6'
option device '@wan'
option proto 'dhcpv6'
option ifname 'usb0'
config interface 'wwan'
option proto 'dhcp'
firewall:
config defaults
option syn_flood 1
option input ACCEPT
option output ACCEPT
option forward REJECT
# Uncomment this line to disable ipv6 rules
# option disable_ipv6 1
config zone
option name lan
list network 'lan'
option input ACCEPT
option output ACCEPT
option forward ACCEPT
config zone
option name wan
list network 'wan'
list network 'wan6'
option input REJECT
option output ACCEPT
option forward REJECT
option masq 1
option mtu_fix 1
config forwarding
option src lan
option dest wan
# We need to accept udp packets on port 68,
# see https://dev.openwrt.org/ticket/4108
config rule
option name Allow-DHCP-Renew
option src wan
option proto udp
option dest_port 68
option target ACCEPT
option family ipv4
# Allow IPv4 ping
config rule
option name Allow-Ping
option src wan
option proto icmp
option icmp_type echo-request
option family ipv4
option target ACCEPT
config rule
option name Allow-IGMP
option src wan
option proto igmp
option family ipv4
option target ACCEPT
# Allow DHCPv6 replies
# see https://github.com/openwrt/openwrt/issues/5066
config rule
option name Allow-DHCPv6
option src wan
option proto udp
option dest_port 546
option family ipv6
option target ACCEPT
config rule
option name Allow-MLD
option src wan
option proto icmp
option src_ip fe80::/10
list icmp_type '130/0'
list icmp_type '131/0'
list icmp_type '132/0'
list icmp_type '143/0'
option family ipv6
option target ACCEPT
# Allow essential incoming IPv6 ICMP traffic
config rule
option name Allow-ICMPv6-Input
option src wan
option proto icmp
list icmp_type echo-request
list icmp_type echo-reply
list icmp_type destination-unreachable
list icmp_type packet-too-big
list icmp_type time-exceeded
list icmp_type bad-header
list icmp_type unknown-header-type
list icmp_type router-solicitation
list icmp_type neighbour-solicitation
list icmp_type router-advertisement
list icmp_type neighbour-advertisement
option limit 1000/sec
option family ipv6
option target ACCEPT
# Allow essential forwarded IPv6 ICMP traffic
config rule
option name Allow-ICMPv6-Forward
option src wan
option dest *
option proto icmp
list icmp_type echo-request
list icmp_type echo-reply
list icmp_type destination-unreachable
list icmp_type packet-too-big
list icmp_type time-exceeded
list icmp_type bad-header
list icmp_type unknown-header-type
option limit 1000/sec
option family ipv6
option target ACCEPT
config rule
option name Allow-IPSec-ESP
option src wan
option dest lan
option proto esp
option target ACCEPT
config rule
option name Allow-ISAKMP
option src wan
option dest lan
option dest_port 500
option proto udp
option target ACCEPT
### EXAMPLE CONFIG SECTIONS
# do not allow a specific ip to access wan
#config rule
# option src lan
# option src_ip 192.168.45.2
# option dest wan
# option proto tcp
# option target REJECT
# block a specific mac on wan
#config rule
# option dest wan
# option src_mac 00:11:22:33:44:66
# option target REJECT
# block incoming ICMP traffic on a zone
#config rule
# option src lan
# option proto ICMP
# option target DROP
# port redirect port coming in on wan to lan
#config redirect
# option src wan
# option src_dport 80
# option dest lan
# option dest_ip 192.168.16.235
# option dest_port 80
# option proto tcp
# port redirect of remapped ssh port (22001) on wan
#config redirect
# option src wan
# option src_dport 22001
# option dest lan
# option dest_port 22
# option proto tcp
### FULL CONFIG SECTIONS
#config rule
# option src lan
# option src_ip 192.168.45.2
# option src_mac 00:11:22:33:44:55
# option src_port 80
# option dest wan
# option dest_ip 194.25.2.129
# option dest_port 120
# option proto tcp
# option target REJECT
#config redirect
# option src lan
# option src_ip 192.168.45.2
# option src_mac 00:11:22:33:44:55
# option src_port 1024
# option src_dport 80
# option dest_ip 194.25.2.129
# option dest_port 120
# option proto tcp
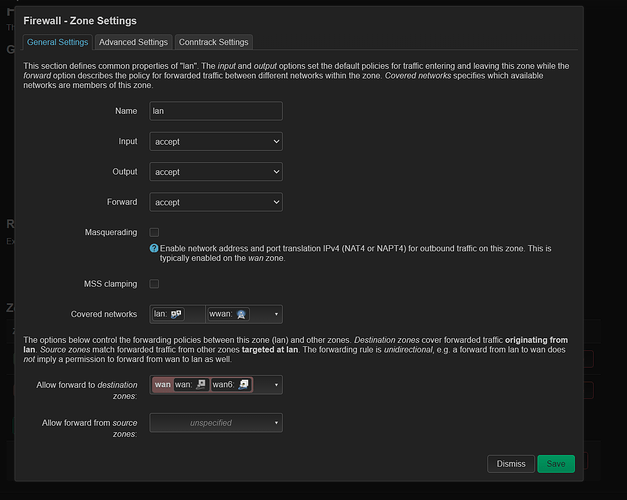
Looks like you have an interface defined for the uplink - wwan - but do not appear to have a corresponding firewall zone for it.
If you trust the other subnet, it should be possible to permit the traffic in both directions by adding wwan to the lan firewall zone.
If you don't trust the other subnet, it should be possible to permit the traffic in one direction by adding wwan to the wan firewall zone.
Or, if you prefer, you can create a separate zone altogether for the wwan interface, and configure forwarding from lan to the new zone.
Yes. The result in /etc/config/firewall will be these two lines next to each other:
list network 'lan'
list network 'wwan'
in
config zone
option name 'lan'
?
Yes. That's the zone in question. Any changes you make in LuCI are reflected in the files in /etc/config, and vice-versa.
ok. asking bc i still cant access 192.168.1.1 (home router) using openwrt (192.168.2.1)
That's because I wasn't paying sufficient attention.
Apologies.
I've just re-read your initial description. Do you want to be able to connect to both routers' administration pages from both networks, without any isolation taking place?
yes, exactly
Right. I misunderstood. Apologies again.
So, to achieve something like this...
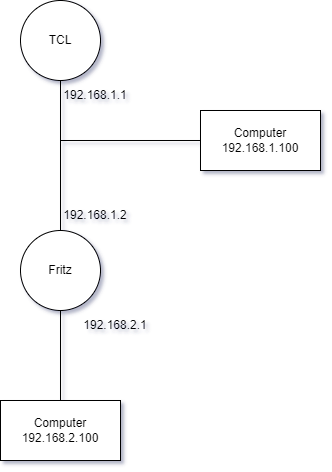
...there are several approaches. (The IP addresses in the diagrams are placeholders; adapt to your scenario).
You could configure the computer at 192.168.1.100 with a static route for 192.168.2.0/24 going via 192.168.1.2. That static route would apply to only that one computer and would have to be repeated for every device.
You would also have to configure the firewall on Fritz to allow inbound connections from the WAN (or add all interfaces to the same zone).
It works, and it's not difficult to do, but it's laborious and it doesn't scale well.
Instead, here's an alternate approach: now that you've added all the interfaces to the same zone... when connected to the TCL Wi-Fi network, try connecting to Fritz's admin page using its WAN IP address (in my diagram, that would be 192.168.1.2).
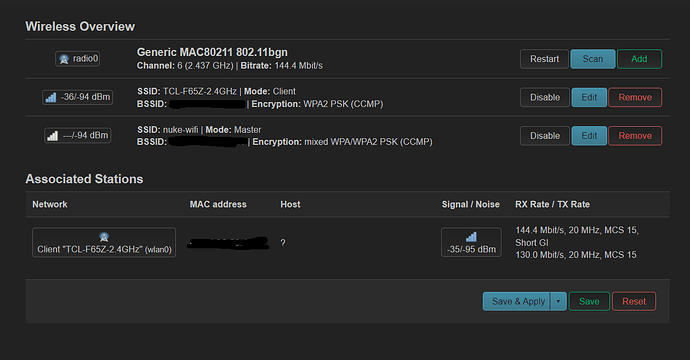
by that, you mean this
also on TCL Wi-Fi when i try to connect using both 192.168.2.1 and 192.168.1.113 (openwrt's ip @ tcl) i get ERR_ADDRESS_UNREACHABLE
That would make sense for 192.168.2.1, because of a possible lack of a route to that address from the 192.168.1.0/24 network. But it's odd that 192.168.1.113 is inaccessible.
Just out of curiosity, do you have two Internet connections? Fritz has some DSL configuration details in it. Does TCL also have an Internet connection?
What is the output of route -n and/or ip route on Fritz?
TCL has SIM card in it and Fritz is connected to its WiFi
root@OpenWrt:~# route -n
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
0.0.0.0 192.168.1.1 0.0.0.0 UG 0 0 0 wlan0
192.168.1.0 0.0.0.0 255.255.255.0 U 0 0 0 wlan0
192.168.2.0 0.0.0.0 255.255.255.0 U 0 0 0 br-lan
root@OpenWrt:~# ip route
default via 192.168.1.1 dev wlan0 src 192.168.1.113
192.168.1.0/24 dev wlan0 scope link src 192.168.1.113
192.168.2.0/24 dev br-lan scope link src 192.168.2.1
Okay. That looks consistent. But I'm now scratching my head.
Fritz has obtained the address you indicated by DHCP.
You added the wwan interface to the lan zone.
And uhttpd - OpenWRT's web server - listens by default on all interfaces; in an unmodified installation it is only the firewall which prevents connections to OpenWRT's WAN interface. And adding the interface to the lan zone works around that.
But for some reason the attempt to connect to OpenWRT at 192.168.1.113 is failing.
Did you restart the firewall service? Might be worth doing that. Also might be worth rebooting Fritz altogether.
Something else which might prove helpful is to check whether the attempts to connect to 192.168.1.113 are actually reaching OpenWRT. A useful tool for this is tcpdump, an optional package which can be installed through LuCI or opkg.
rebooting the Fritz solved the problem. Now I can access 192.168.1.133. Thanks!
No worries. Glad it's all working now.