Hi,
I have setup a Wireguard "client" to Mullvad vpn.
My default route remains WAN, I only route my NAS (192.168.1.3), running Transmission, through wireguard with policy routing.
/etc/config/vpn-policy-routing:
config policy
option src_addr '192.168.1.3'
option interface 'WGc_MULLVAD'
option name 'NAS via vpn'
I also run a Wireguard "server" (192.168.5.0/24).
/etc/config/network:
config interface 'WGS_MULLVAD'
option proto 'wireguard'
option private_key '[redacted]'
option listen_port '51820'
list addresses '192.168.5.1/24'
config wireguard_WGS_MULLVAD
list allowed_ips '192.168.5.2/32'
option description 'GalaxyNote10plus'
option persistent_keepalive '25'
option route_allowed_ips '1'
option public_key '[redacted]'
PROBLEM: When I connect my phone to my home network via Wireguard, I can't reach my NAS.
TROUBLESHOOTING
- I understand I route all my NAS traffic to the Wireguard client, while I'm trying to reach the NAS via the Wireguard server, but the firewall zone forwarding rules should allow that (see config files below).
- When I disable the vpn policy routing (meaning NAS traffic follows the default routing to WAN), I can reach the NAS.
- I tried adding the append_src_rules option to /etc/config/network:
option append_src_rules '! -d 192.168.5.0/24'
Or a dest_addr to the rule:
config policy
option src_addr '192.168.1.3'
option interface 'WGc_MULLVAD'
option name 'NAS via vpn'
option dest_addr '!192.168.5.0/24'
CONFIG FILES
/etc/config/firewall
config rule
option name 'Allow-DHCP-Renew'
option src 'wan'
option proto 'udp'
option dest_port '68'
option target 'ACCEPT'
option family 'ipv4'
config rule
option name 'Allow-Ping'
option src 'wan'
option proto 'icmp'
option icmp_type 'echo-request'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-DHCPv6'
option src 'wan'
option proto 'udp'
option src_ip 'fe80::/10'
option src_port '547'
option dest_ip 'fe80::/10'
option dest_port '546'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-MLD'
option src 'wan'
option proto 'icmp'
option src_ip 'fe80::/10'
list icmp_type '130/0'
list icmp_type '131/0'
list icmp_type '132/0'
list icmp_type '143/0'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Input'
option src 'wan'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
list icmp_type 'router-solicitation'
list icmp_type 'neighbour-solicitation'
list icmp_type 'router-advertisement'
list icmp_type 'neighbour-advertisement'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Forward'
option src 'wan'
option dest '*'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option dest_port '1010'
option src 'wan'
option name 'Allow-OpenVPN-Inbound-UDP'
option target 'ACCEPT'
list proto 'udp'
config rule
option target 'ACCEPT'
option name 'Allow-OpenVPN-Inbound-TCP'
option src 'wan'
option dest_port '443'
list proto 'tcp'
config rule
option target 'ACCEPT'
option proto 'udp'
option dest_port '67-68'
option name 'Allow DHCP request'
option src 'guest'
option src_port '67-68'
config rule
option target 'ACCEPT'
option proto 'tcp udp'
option dest_port '53'
option name 'Allow DNS Queries'
option src 'guest'
config rule
option dest 'lan'
option target 'DROP'
option src 'guest'
option name 'Deny guest -> LAN'
config defaults
option input 'ACCEPT'
option output 'ACCEPT'
option syn_flood '1'
option forward 'REJECT'
config zone
option name 'lan'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'ACCEPT'
option masq '1'
option mtu_fix '1'
option network 'lan'
config zone
option input 'ACCEPT'
option output 'ACCEPT'
option name 'vpnserver'
option mtu_fix '1'
option forward 'ACCEPT'
option network 'OVPNs_udp OVPNs_tcp WGS_MULLVAD'
option masq '1'
config include
option path '/etc/firewall.user'
config forwarding
option dest 'wan'
option src 'vpnserver'
config forwarding
option src 'lan'
option dest 'vpnserver'
config forwarding
option dest 'wan'
option src 'lan'
config forwarding
option dest 'lan'
option src 'vpnserver'
config zone
option forward 'REJECT'
option output 'ACCEPT'
option name 'guest'
option network 'guest'
option input 'REJECT'
config zone
option name 'wan'
option output 'ACCEPT'
option forward 'REJECT'
option masq '1'
option mtu_fix '1'
option input 'REJECT'
option network 'wan wan6'
config forwarding
option dest 'wan'
option src 'guest'
config zone
option name 'vpnclient'
option input 'REJECT'
option masq '1'
option forward 'REJECT'
option output 'ACCEPT'
option mtu_fix '1'
option network 'OVPNc_MULLVAD WGc_MULLVAD'
config forwarding
option dest 'vpnclient'
option src 'lan'
config forwarding
option dest 'vpnclient'
option src 'vpnserver'
config rule
list proto 'all'
option name 'block nas to wan'
list src_ip '192.168.1.3'
option dest 'wan'
option target 'REJECT'
option src 'lan'
config redirect
option dest_port '30892'
option name 'NAS Transmission peer listening port'
option src_dport '30892'
option target 'DNAT'
option dest_ip '192.168.1.3'
option dest 'lan'
option src 'vpnclient'
config redirect 'adblock_dns_53'
option name 'Adblock DNS, port 53'
option src 'lan'
option proto 'tcp udp'
option src_dport '53'
option dest_port '53'
option target 'DNAT'
config redirect 'adblock_dns_853'
option name 'Adblock DNS, port 853'
option src 'lan'
option proto 'tcp udp'
option src_dport '853'
option dest_port '853'
option target 'DNAT'
config redirect 'adblock_dns_5353'
option name 'Adblock DNS, port 5353'
option src 'lan'
option proto 'tcp udp'
option src_dport '5353'
option dest_port '5353'
option target 'DNAT'
config rule
option src 'wan'
option name 'Allow-Wireguard'
option target 'ACCEPT'
list proto 'udp'
option dest_port '51820'
/etc/config/network
config interface 'loopback'
option ifname 'lo'
option proto 'static'
option ipaddr '127.0.0.1'
option netmask '255.0.0.0'
config globals 'globals'
option ula_prefix '[redacted]'
config interface 'lan'
option type 'bridge'
option proto 'static'
option ipaddr '192.168.1.1'
option netmask '255.255.255.0'
option ip6assign '60'
option ifname 'eth0'
config interface 'wan'
option ifname 'eth1'
option proto 'dhcp'
option peerdns '0'
list dns '1.1.1.1'
list dns '1.0.0.1'
config interface 'wan6'
option proto 'dhcpv6'
option reqaddress 'try'
option reqprefix 'auto'
option ifname 'eth1'
option peerdns '0'
list dns '2606:4700:4700::1111'
list dns '2606:4700:4700::1001'
config interface 'OVPNs_udp'
option ifname 'tun0'
option proto 'none'
config interface 'OVPNs_tcp'
option proto 'none'
option ifname 'tun1'
config interface 'OVPNc_MULLVAD'
option ifname 'tun2'
option proto 'none'
config interface 'guest'
option proto 'static'
option netmask '255.255.255.0'
option ipaddr '192.168.4.1'
option type 'bridge'
config switch
option name 'switch0'
option reset '1'
option enable_vlan '1'
config switch_vlan
option device 'switch0'
option vlan '1'
option vid '1'
option ports '0 1 2 3t 5'
config switch_vlan
option device 'switch0'
option vlan '5'
option vid '2'
option ports '3t 4 6'
config interface 'WGc_MULLVAD'
option proto 'wireguard'
list addresses '[redacted]'
list addresses [redacted]'
option private_key '[redacted]'
config wireguard_WGc_MULLVAD
option endpoint_port '51820'
option public_key '[redacted]'
option endpoint_host '[redacted]'
list allowed_ips '0.0.0.0/0'
list allowed_ips '::0/0'
option description 'NL Amsterdam'
option persistent_keepalive '25'
config interface 'WGS_MULLVAD'
option proto 'wireguard'
option private_key '[redacted]'
option listen_port '51820'
list addresses '192.168.5.1/24'
config wireguard_WGS_MULLVAD
list allowed_ips '192.168.5.2/32'
option description 'GalaxyNote10plus'
option persistent_keepalive '25'
option route_allowed_ips '1'
option public_key '[redacted]'
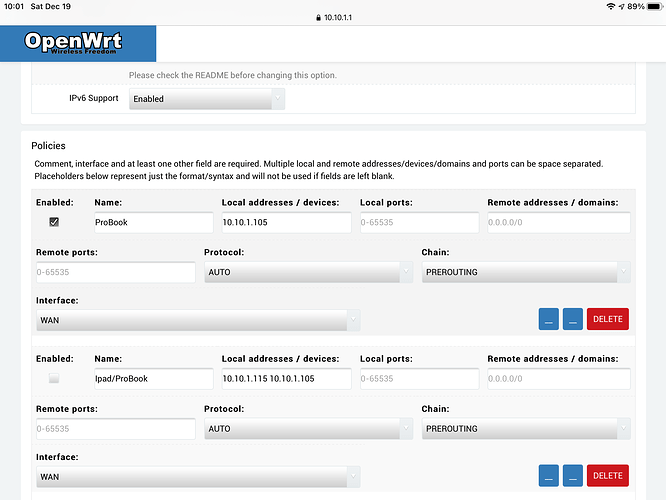
/etc/config/vpn-policy-routing
config vpn-policy-routing 'config'
option verbosity '2'
option strict_enforcement '1'
option src_ipset '0'
option dest_ipset 'dnsmasq.ipset'
option boot_timeout '30'
option iptables_rule_option 'append'
option iprule_enabled '0'
option webui_sorting '1'
list webui_supported_protocol 'tcp'
list webui_supported_protocol 'udp'
list webui_supported_protocol 'tcp udp'
list webui_supported_protocol 'icmp'
list webui_supported_protocol 'all'
option webui_enable_column '1'
option webui_protocol_column '1'
option webui_chain_column '0'
option enabled '1'
option ipv6_enabled '0'
config include
option path '/etc/vpn-policy-routing.netflix.user'
option enabled '0'
config include
option path '/etc/vpn-policy-routing.aws.user'
option enabled '0'
config policy
option src_addr '192.168.1.3'
option interface 'WGc_MULLVAD'
option name 'NAS via vpn'
config policy
option src_addr '192.168.1.23'
option interface 'WGc_MULLVAD'
option name 'SB2 via vpn'
option enabled '0'
root@WRT1900AC:/etc/config# /etc/init.d/vpn-policy-routing support
vpn-policy-routing 0.2.1-7 running on OpenWrt 19.07.2. WAN (IPv4): wan/dev/192.168.0.1.
============================================================
Dnsmasq version 2.80 Copyright (c) 2000-2018 Simon Kelley
Compile time options: IPv6 GNU-getopt no-DBus no-i18n no-IDN DHCP DHCPv6 no-Lua TFTP conntrack ipset auth DNSSEC no-ID loop-detect inotify dumpfile
============================================================
Routes/IP Rules
default 192.168.0.1 0.0.0.0 UG 0 0 0 eth1
IPv4 Table 201: default via 192.168.0.1 dev eth1
192.168.4.0/24 dev br-guest proto kernel scope link src 192.168.4.1
IPv4 Table 201 Rules:
32699: from all fwmark 0x10000/0xff0000 lookup 201
IPv4 Table 202: default via 192.168.2.1 dev tun0
192.168.4.0/24 dev br-guest proto kernel scope link src 192.168.4.1
IPv4 Table 202 Rules:
32698: from all fwmark 0x20000/0xff0000 lookup 202
IPv4 Table 203: default via 192.168.3.1 dev tun1
192.168.4.0/24 dev br-guest proto kernel scope link src 192.168.4.1
IPv4 Table 203 Rules:
32697: from all fwmark 0x30000/0xff0000 lookup 203
IPv4 Table 204: unreachable default
192.168.4.0/24 dev br-guest proto kernel scope link src 192.168.4.1
IPv4 Table 204 Rules:
32696: from all fwmark 0x40000/0xff0000 lookup 204
IPv4 Table 205: default via 10.69.232.202 dev WGc_MULLVAD
192.168.4.0/24 dev br-guest proto kernel scope link src 192.168.4.1
IPv4 Table 205 Rules:
32695: from all fwmark 0x50000/0xff0000 lookup 205
IPv4 Table 206: default via 192.168.5.1 dev WGS_MULLVAD
192.168.4.0/24 dev br-guest proto kernel scope link src 192.168.4.1
IPv4 Table 206 Rules:
32694: from all fwmark 0x60000/0xff0000 lookup 206
============================================================
IP Tables PREROUTING
-N VPR_PREROUTING
-A VPR_PREROUTING -s 192.168.1.3/32 -m comment --comment NAS_via_vpn -c 10569 2644644 -j MARK --set-xmark 0x50000/0xff0000
-A VPR_PREROUTING -m set --match-set WGS_MULLVAD dst -c 0 0 -j MARK --set-xmark 0x60000/0xff0000
-A VPR_PREROUTING -m set --match-set WGc_MULLVAD dst -c 0 0 -j MARK --set-xmark 0x50000/0xff0000
-A VPR_PREROUTING -m set --match-set OVPNc_MULLVAD dst -c 0 0 -j MARK --set-xmark 0x40000/0xff0000
-A VPR_PREROUTING -m set --match-set OVPNs_tcp dst -c 0 0 -j MARK --set-xmark 0x30000/0xff0000
-A VPR_PREROUTING -m set --match-set OVPNs_udp dst -c 0 0 -j MARK --set-xmark 0x20000/0xff0000
-A VPR_PREROUTING -m set --match-set wan dst -c 0 0 -j MARK --set-xmark 0x10000/0xff0000
============================================================
IP Tables FORWARD
-N VPR_FORWARD
============================================================
IP Tables INPUT
-N VPR_INPUT
============================================================
IP Tables OUTPUT
-N VPR_OUTPUT
============================================================
Current ipsets
create wan hash:net family inet hashsize 1024 maxelem 65536 comment
create OVPNs_udp hash:net family inet hashsize 1024 maxelem 65536 comment
create OVPNs_tcp hash:net family inet hashsize 1024 maxelem 65536 comment
create OVPNc_MULLVAD hash:net family inet hashsize 1024 maxelem 65536 comment
create WGc_MULLVAD hash:net family inet hashsize 1024 maxelem 65536 comment
create WGS_MULLVAD hash:net family inet hashsize 1024 maxelem 65536 comment
============================================================
Your support details have been logged to '/var/vpn-policy-routing-support'. [✓]
root@WRT1900AC:/etc/config# /etc/init.d/vpn-policy-routing reload
Creating table 'wan/eth1/192.168.0.1' [✓]
Creating table 'OVPNs_udp/tun0/192.168.2.1' [✓]
Creating table 'OVPNs_tcp/tun1/192.168.3.1' [✓]
Creating table 'OVPNc_MULLVAD/tun2/0.0.0.0' [✓]
Creating table 'WGc_MULLVAD/10.69.232.202' [✓]
Creating table 'WGS_MULLVAD/192.168.5.1' [✓]
Routing 'NAS via vpn' via WGc_MULLVAD [✓]
vpn-policy-routing 0.2.1-7 started with gateways:
wan/eth1/192.168.0.1 [✓]
OVPNs_udp/tun0/192.168.2.1
OVPNs_tcp/tun1/192.168.3.1
OVPNc_MULLVAD/tun2/0.0.0.0
WGc_MULLVAD/10.69.232.202
WGS_MULLVAD/192.168.5.1

 ... I will try setting it up again and post debugs again at that time.
... I will try setting it up again and post debugs again at that time.