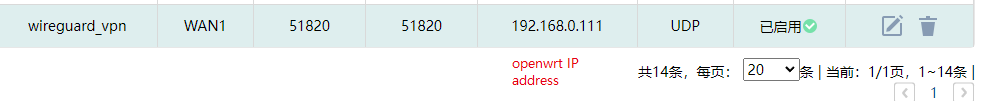
First off, for a road warrior phone somewhere away from home to reach the VPN server running at home (but not on the home main router, instead it is a separate device), the Wireguard port (51820) must be forwarded from the Internet through the home network to the NAS IP on the home LAN. Encrypted packets from the phone will arrive on this port.
This generally involves using a DDNS server so that the phone can find your home's IP by name, as ISPs change the customer's IP numbers sometimes. Also the ISP has to allow incoming connections and not NAT your connection.
When testing turn off wifi in the phone so it is using the cellular ISP and not your home LAN.
Once the above has been taken care of and a VPN tunnel is even possible, then you can start to think of what to do with VPN'd traffic that arrives through the tunnel. Assuming you want all of the phone's Internet usage to tunnel to home and go out on the home IP:
- phone wg0 interface and home wg0 interface close but different IPs-- in the same subnet-- (an obscure /24 is typically used for this)
- At home, allowed_ips from the phone are just the phone's wg IP /32.
- On phone, allowed_ips are 0.0.0.0/0 since the whole Internet will be coming through the tunnel.
- set route_allowed_ips flag both places.
- At home, wg0 in a separate firewall zone.
- Rule to allow forwarding from wg0 to lan.
- Set masquerade on the lan zone.