I have a Linksys router WRT3200ACM with four ethernet ports. The house is wired for ethernet and there are 16 port GB switches attached to 1 & 3. 1 for the adults and 3 for the kids.
I think I’ve set it up so the LAN and WAN (internet) are available on 1,2 & 4 and a VLAN for 3. The intention is that devices connected to 3 (my kid’s Windows & Apple boxes) can access only the internet and not the LAN.
To test it, I have a raspberry pi wired to the switch that’s plugged into port 3 on the router but also has wireless access to the router. I can access the internet via wireless (192.168.7.1/24) but if I disable wireless, wired (192.168.8.1/24) cannot access the internet but can access local web pages on the LAN
/etc/config/network:
config interface 'loopback'
option device 'lo'
option proto 'static'
option ipaddr '127.0.0.1'
option netmask '255.0.0.0'
config globals 'globals'
option ula_prefix 'numbers::/48'
config device
option name 'br-lan'
option type 'bridge'
list ports 'lan1'
list ports 'lan2'
list ports 'lan4'
config interface 'lan'
option device 'br-home'
option proto 'static'
option ip6assign '60'
list ipaddr '192.168.7.1/24'
option dns_metric '300'
config device
option name 'wan'
option macaddr 'numbers'
config interface 'wan'
option device 'wan'
option proto 'dhcp'
option peerdns '0'
list dns '1.1.1.1'
list dns '1.0.0.1'
config interface 'wan6'
option device 'wan'
option proto 'dhcpv6'
option reqaddress 'try'
option reqprefix 'auto'
option peerdns '0'
list dns '2606:4700:4700::64'
list dns '2606:4700:4700::6400'
config device
option type 'bridge'
option name 'br-home'
list ports 'lan1'
list ports 'lan2'
list ports 'lan4'
config device
option type 'bridge'
option name 'kids'
list ports 'lan3'
config interface 'kids'
option proto 'static'
option device 'kids'
option ipaddr '192.168.8.1'
option netmask '255.255.255.0'
option dns_metric '300'
option ip6assign '64'
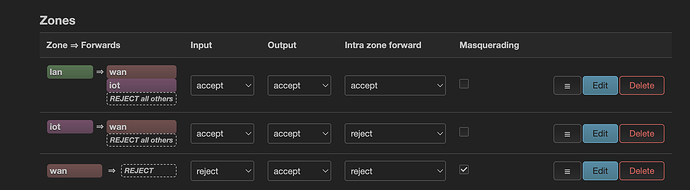
/etc/config/firewall: (edited)
config defaults
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'REJECT'
option synflood_protect '1'
config zone
option name 'lan'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'ACCEPT'
list network 'lan'
list network 'kids'
config zone
option name 'wan'
option input 'REJECT'
option output 'ACCEPT'
option forward 'REJECT'
option masq '1'
option mtu_fix '1'
list network 'wan'
list network 'wan6'
list network 'wwan'
config forwarding
option src 'lan'
option dest 'wan'
<snipped various rules & redirects>
config zone
option name 'VLAN2'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'REJECT'
list network 'wan'
list network 'wan6'
config forwarding
option src 'VLAN2'
option dest 'wan'
config forwarding
option src 'lan'
option dest 'VLAN2'
I have PiHole running, if that’s relevant - do I need to adapt that for VLAN2?
What am I missing?
Thanks
Greg