Hi everyone,
we are trying to connect a device with ssid associated network with VLAN ID. Required scenario is explained in last shared snap.
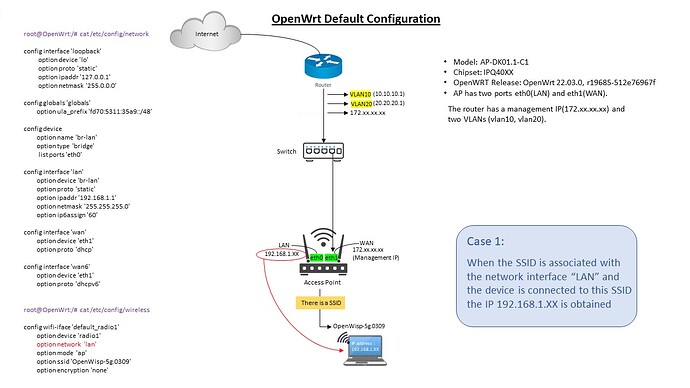
Actually i have a main router (which has a management IP and two vlans: VLAN10 and VLAN20) and an Access Point having two ports eth0(LAN) and eth1(WAN) as show in below snap. In AP there is an SSID .
CASE 1: when we use default openwrt configuration in that case a device connected to ssid associated with network "lan" IP 192.168.1.XX is obtained as shown is below snap 1-
root@OpenWrt:/# cat /etc/config/network
config interface 'loopback'
option device 'lo'
option proto 'static'
option ipaddr '127.0.0.1'
option netmask '255.0.0.0’
config globals 'globals'
option ula_prefix 'fd70:5311:35a9::/48’
config device
option name 'br-lan'
option type 'bridge'
list ports 'eth0’
config interface 'lan'
option device 'br-lan'
option proto 'static'
option ipaddr '192.168.1.1'
option netmask '255.255.255.0'
option ip6assign '60’
config interface 'wan'
option device 'eth1'
option proto 'dhcp’
config interface 'wan6'
option device 'eth1'
option proto 'dhcpv6’
root@OpenWrt:/# cat /etc/config/wireless
config wifi-iface 'default_radio1'
option device 'radio1'
option network 'lan'
option mode 'ap'
option ssid 'OpenWisp-5g.0309'
option encryption 'none'
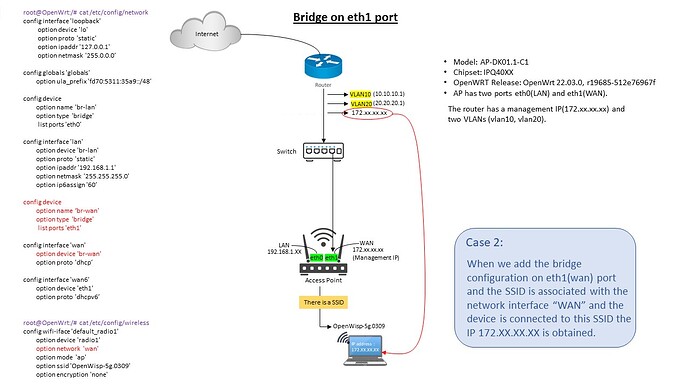
CASE 2: when we add a bridge configuration as shown below in network file, a device connected to ssid associated with a network interface "wan" a management IP (172.xx.xx.xx) is obtained as shown in below snap 2-
config device
option name ‘br-wan'
option type 'bridge'
list ports 'eth1'
config interface 'wan'
option device 'br-wan'
option proto 'dhcp’
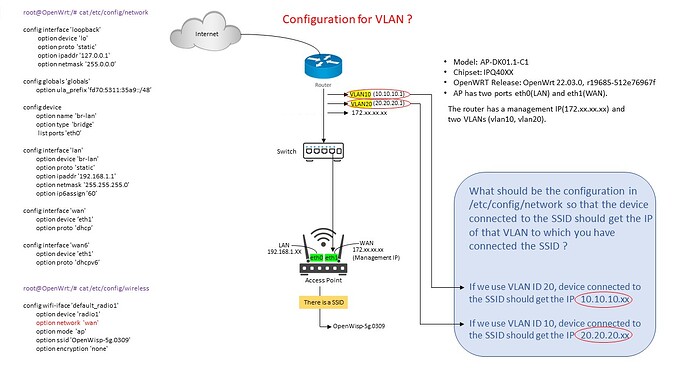
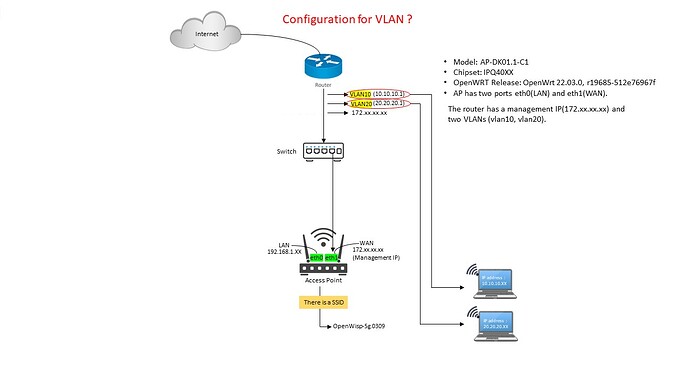
CASE 3: i required a such configuration by which a device connected to that SSID should get the IP of that vlan to which we have connected the SSID (10.10.10.xx or 20.20.20.xx) and scenario is shown in below snap 3-
If you or someone has an idea how to do such configuration... much appreciated
Thanks to the developers.