Hello guys.
What I used to do with the cable connected was just setup the Mi 3g as a Dumb Ap and configure samba. His SMB server was shown to every device in my network.
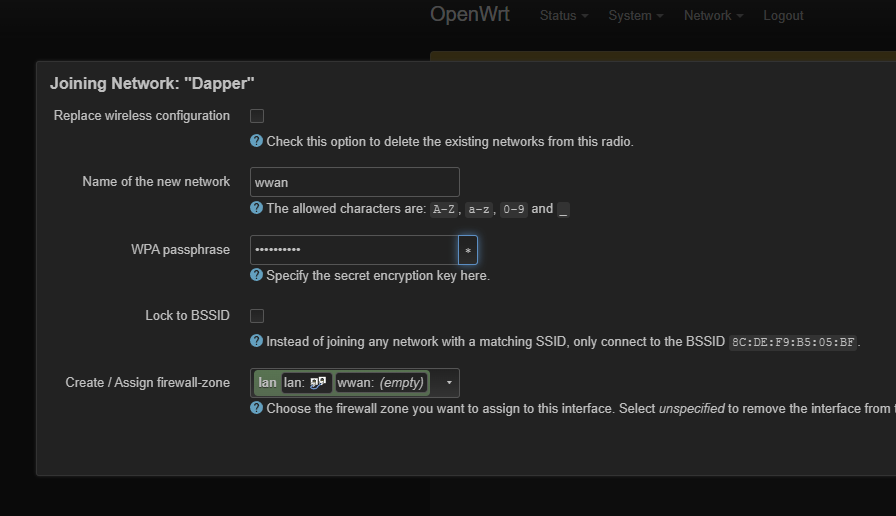
This time I did the same thing, but now since I can't connect the router through cable, I connected my 3G in my 5GHZ wifi in the wireless interfaces > scan > add (lan option).
Now, I can't even acess openwrt web page of the 3G modem through the main router or other devices in my lan, I just have acess to the 3G router, when a plug the cable to it.
Can you guys pls help me out? I'm struggling a lot.
I'm kinda noob and this may be a very easy thing to adjust but I really dont know what else to do.
I'm going to guess that your wifi uplink is not associated with the right network or firewall zone. We need to see how it is configured, though.
Please copy the output of the following commands and post it here using the "Preformatted text </> " button:
ubus call system board
cat /etc/config/network
cat /etc/config/wireless
cat /etc/config/dhcp
cat /etc/config/firewall
Hey there!
ubus call system board
{
"kernel": "5.15.127",
"hostname": "OpenWrt",
"system": "MediaTek MT7621 ver:1 eco:3",
"model": "Xiaomi Mi Router 3G",
"board_name": "xiaomi,mi-router-3g",
"rootfs_type": "squashfs",
"release": {
"distribution": "OpenWrt",
"version": "23.05.0-rc3",
"revision": "r23389-5deed175a5",
"target": "ramips/mt7621",
"description": "OpenWrt 23.05.0-rc3 r23389-5deed175a5"
}
}
root@OpenWrt:~# cat /etc/config/network
config interface 'loopback'
option device 'lo'
option proto 'static'
option ipaddr '127.0.0.1'
option netmask '255.0.0.0'
config globals 'globals'
option ula_prefix 'fd21:086e:808b::/48'
option packet_steering '1'
config device
option name 'br-lan'
option type 'bridge'
list ports 'lan1'
list ports 'lan2'
config interface 'lan'
option device 'br-lan'
option proto 'static'
option ipaddr '192.168.1.1'
option netmask '255.255.255.0'
option ip6assign '60'
config interface 'wan'
option device 'wan'
option proto 'dhcp'
config interface 'wan6'
option device 'wan'
option proto 'dhcpv6'
config interface 'wwan'
option proto 'dhcp'
root@OpenWrt:~# cat /etc/config/wireless
config wifi-device 'radio0'
option type 'mac80211'
option path '1e140000.pcie/pci0000:00/0000:00:00.0/0000:01:00.0'
option channel '1'
option band '2g'
option htmode 'HT20'
option disabled '1'
config wifi-device 'radio1'
option type 'mac80211'
option path '1e140000.pcie/pci0000:00/0000:00:01.0/0000:02:00.0'
option channel 'auto'
option band '5g'
option htmode 'VHT80'
option cell_density '0'
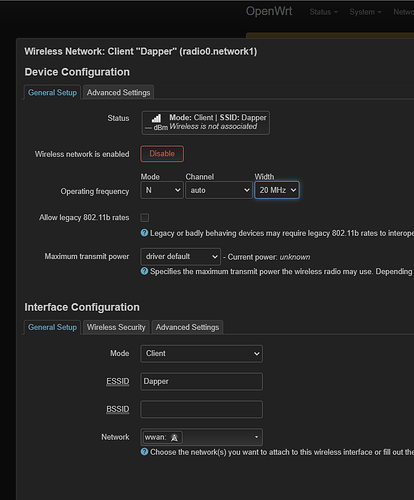
config wifi-iface 'wifinet0'
option device 'radio1'
option mode 'sta'
option network 'wwan'
option ssid 'Dapper 5G'
option encryption 'psk2'
option key 'Dapper1991'
root@OpenWrt:~# cat /etc/config/dhcp
config dnsmasq
option domainneeded '1'
option boguspriv '1'
option filterwin2k '0'
option localise_queries '1'
option rebind_protection '1'
option rebind_localhost '1'
option local '/lan/'
option domain 'lan'
option expandhosts '1'
option nonegcache '0'
option cachesize '1000'
option authoritative '1'
option readethers '1'
option leasefile '/tmp/dhcp.leases'
option resolvfile '/tmp/resolv.conf.d/resolv.conf.auto'
option nonwildcard '1'
option localservice '1'
option ednspacket_max '1232'
option filter_aaaa '0'
option filter_a '0'
config dhcp 'lan'
option interface 'lan'
option start '100'
option limit '150'
option leasetime '12h'
option dhcpv4 'server'
option dhcpv6 'server'
option ra 'server'
option ra_slaac '1'
list ra_flags 'managed-config'
list ra_flags 'other-config'
config dhcp 'wan'
option interface 'wan'
option ignore '1'
config odhcpd 'odhcpd'
option maindhcp '0'
option leasefile '/tmp/hosts/odhcpd'
option leasetrigger '/usr/sbin/odhcpd-update'
option loglevel '4'
root@OpenWrt:~# cat /etc/config/firewall
config defaults
option syn_flood '1'
option input 'REJECT'
option output 'ACCEPT'
option forward 'REJECT'
config zone
option name 'lan'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'ACCEPT'
list network 'lan'
list network 'wwan'
config zone
option name 'wan'
option input 'REJECT'
option output 'ACCEPT'
option forward 'REJECT'
option masq '1'
option mtu_fix '1'
list network 'wan'
list network 'wan6'
config forwarding
option src 'lan'
option dest 'wan'
config rule
option name 'Allow-DHCP-Renew'
option src 'wan'
option proto 'udp'
option dest_port '68'
option target 'ACCEPT'
option family 'ipv4'
config rule
option name 'Allow-Ping'
option src 'wan'
option proto 'icmp'
option icmp_type 'echo-request'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-IGMP'
option src 'wan'
option proto 'igmp'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-DHCPv6'
option src 'wan'
option proto 'udp'
option dest_port '546'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-MLD'
option src 'wan'
option proto 'icmp'
option src_ip 'fe80::/10'
list icmp_type '130/0'
list icmp_type '131/0'
list icmp_type '132/0'
list icmp_type '143/0'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Input'
option src 'wan'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
list icmp_type 'router-solicitation'
list icmp_type 'neighbour-solicitation'
list icmp_type 'router-advertisement'
list icmp_type 'neighbour-advertisement'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Forward'
option src 'wan'
option dest '*'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-IPSec-ESP'
option src 'wan'
option dest 'lan'
option proto 'esp'
option target 'ACCEPT'
config rule
option name 'Allow-ISAKMP'
option src 'wan'
option dest 'lan'
option dest_port '500'
option proto 'udp'
option target 'ACCEPT'
BTW, I even tried changing the subnet, still doesn't show. main router is 10.10.10.10 and Mi3g 192.168.1.1.
Mi 3g is getting the ip 10.10.10.217 on the main router.
opaulodapper:
10.10.10.217
This is the address you should use to access the Mi 3g, since that is the IP of your main subnet. So, from a computer on your 10.10.10.0/24 network, can you ping 10.10.10.217? Can you access the LuCI web interface and/or ssh at that address?
So, through the main router, I can ping.
root@OpenWrt:~# ping 10.10.10.217
PING 10.10.10.217 (10.10.10.217): 56 data bytes
64 bytes from 10.10.10.217: seq=0 ttl=64 time=19.916 ms
64 bytes from 10.10.10.217: seq=1 ttl=64 time=1.635 ms
64 bytes from 10.10.10.217: seq=2 ttl=64 time=1.708 ms
64 bytes from 10.10.10.217: seq=3 ttl=64 time=1.694 ms
64 bytes from 10.10.10.217: seq=4 ttl=64 time=1.661 ms
64 bytes from 10.10.10.217: seq=5 ttl=64 time=1.952 ms
But through the windows terminal, it cant acess the 3G.
>ping 10.10.10.217
Firing 10.10.10.217 with 32 bytes of data:
Response from 10.10.10.236: Destination host unreachable.
Response from 10.10.10.236: Destination host unreachable.
Response from 10.10.10.236: Destination host unreachable.
Response from 10.10.10.236: Destination host unreachable.
Ping stats for 10.10.10.217:
Packets: Sent = 4, Received = 4, Lost = 0 (0% of
10.10.10.236 is my pc.
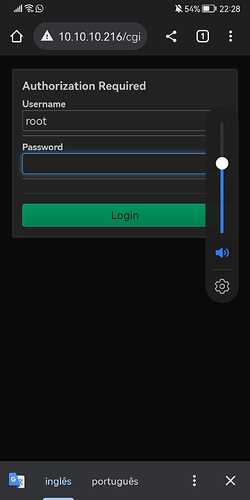
I can't acess the router in that link through luci or ssh, i just can acess it again pluging his cable in my pc.
thaat doesn't make a lot of sense, but we'll figure out why. I don't think there is an issue with your OpenWrt configuration, though.
Try disabling the windows firewall and then test the pings again.
Is there a chance of the issue being on the main router? (ax3600 with rc3)
I don't think it's a windows firewall issue since i cant acess the mi3g through 10.10.10.217 even on my android phone.
oh... well there is one other possibility... do you have wifi client isolation enabled on your main router? Let's see the config from that device...
Well, I don't think I do, unless it comes activated by default on owrt
root@OpenWrt:~# ubus call system board
{
"kernel": "5.15.127",
"hostname": "OpenWrt",
"system": "ARMv8 Processor rev 4",
"model": "Xiaomi AX3600",
"board_name": "xiaomi,ax3600",
"rootfs_type": "squashfs",
"release": {
"distribution": "OpenWrt",
"version": "23.05.0-rc3",
"revision": "r23389-5deed175a5",
"target": "ipq807x/generic",
"description": "OpenWrt 23.05.0-rc3 r23389-5deed175a5"
}
}
root@OpenWrt:~# cat /etc/config/network
config interface 'loopback'
option device 'lo'
option proto 'static'
option ipaddr '127.0.0.1'
option netmask '255.0.0.0'
config globals 'globals'
option ula_prefix 'fdd9:7e94:a2fe::/48'
config device
option name 'br-lan'
option type 'bridge'
list ports 'lan1'
list ports 'lan2'
list ports 'lan3'
config interface 'lan'
option device 'br-lan'
option proto 'static'
option ipaddr '10.10.10.10'
option netmask '255.255.255.0'
option ip6assign '60'
config interface 'wan'
option device 'wan'
option proto 'pppoe'
option username 'cliente@cliente'
option password 'cliente'
option ipv6 'auto'
config interface 'wan6'
option device 'wan'
option proto 'dhcpv6'
config device
option name 'phy1-ap0'
option macaddr 'XXXXXXX'
root@OpenWrt:~# cat /etc/config/wireless
config wifi-device 'radio0'
option type 'mac80211'
option path 'soc/20000000.pci/pci0000:00/0000:00:00.0/0000:01:00.0'
option channel '36'
option band '5g'
option htmode 'VHT80'
option disabled '1'
config wifi-device 'radio1'
option type 'mac80211'
option path 'platform/soc/c000000.wifi'
option channel 'auto'
option band '5g'
option htmode 'VHT80'
option cell_density '0'
config wifi-device 'radio2'
option type 'mac80211'
option path 'platform/soc/c000000.wifi+1'
option channel 'auto'
option band '2g'
option htmode 'HT20'
option cell_density '0'
config wifi-iface 'wifinet0'
option device 'radio2'
option mode 'ap'
option ssid 'Dapper'
option encryption 'psk2'
option key 'Dapper1983'
option network 'lan'
config wifi-iface 'wifinet1'
option device 'radio1'
option mode 'ap'
option ssid 'Dapper 5G'
option encryption 'psk2'
option key 'Dapper1991'
option network 'lan'
root@OpenWrt:~# cat /etc/config/dhcp
config dnsmasq
option domainneeded '1'
option boguspriv '1'
option filterwin2k '0'
option localise_queries '1'
option rebind_protection '1'
option rebind_localhost '1'
option local '/lan/'
option domain 'lan'
option expandhosts '1'
option nonegcache '0'
option cachesize '1000'
option authoritative '1'
option readethers '1'
option leasefile '/tmp/dhcp.leases'
option resolvfile '/tmp/resolv.conf.d/resolv.conf.auto'
option nonwildcard '1'
option localservice '1'
option ednspacket_max '1232'
option filter_aaaa '0'
option filter_a '0'
config dhcp 'lan'
option interface 'lan'
option start '100'
option limit '150'
option leasetime '12h'
option dhcpv4 'server'
option dhcpv6 'server'
option ra 'server'
list ra_flags 'managed-config'
list ra_flags 'other-config'
config dhcp 'wan'
option interface 'wan'
option ignore '1'
config odhcpd 'odhcpd'
option maindhcp '0'
option leasefile '/tmp/hosts/odhcpd'
option leasetrigger '/usr/sbin/odhcpd-update'
option loglevel '4'
root@OpenWrt:~# cat /etc/config/firewall
config defaults
option syn_flood 1
option input REJECT
option output ACCEPT
option forward REJECT
# Uncomment this line to disable ipv6 rules
# option disable_ipv6 1
config zone
option name lan
list network 'lan'
option input ACCEPT
option output ACCEPT
option forward ACCEPT
config zone
option name wan
list network 'wan'
list network 'wan6'
option input REJECT
option output ACCEPT
option forward REJECT
option masq 1
option mtu_fix 1
config forwarding
option src lan
option dest wan
# We need to accept udp packets on port 68,
# see https://dev.openwrt.org/ticket/4108
config rule
option name Allow-DHCP-Renew
option src wan
option proto udp
option dest_port 68
option target ACCEPT
option family ipv4
# Allow IPv4 ping
config rule
option name Allow-Ping
option src wan
option proto icmp
option icmp_type echo-request
option family ipv4
option target ACCEPT
config rule
option name Allow-IGMP
option src wan
option proto igmp
option family ipv4
option target ACCEPT
# Allow DHCPv6 replies
# see https://github.com/openwrt/openwrt/issues/5066
config rule
option name Allow-DHCPv6
option src wan
option proto udp
option dest_port 546
option family ipv6
option target ACCEPT
config rule
option name Allow-MLD
option src wan
option proto icmp
option src_ip fe80::/10
list icmp_type '130/0'
list icmp_type '131/0'
list icmp_type '132/0'
list icmp_type '143/0'
option family ipv6
option target ACCEPT
# Allow essential incoming IPv6 ICMP traffic
config rule
option name Allow-ICMPv6-Input
option src wan
option proto icmp
list icmp_type echo-request
list icmp_type echo-reply
list icmp_type destination-unreachable
list icmp_type packet-too-big
list icmp_type time-exceeded
list icmp_type bad-header
list icmp_type unknown-header-type
list icmp_type router-solicitation
list icmp_type neighbour-solicitation
list icmp_type router-advertisement
list icmp_type neighbour-advertisement
option limit 1000/sec
option family ipv6
option target ACCEPT
# Allow essential forwarded IPv6 ICMP traffic
config rule
option name Allow-ICMPv6-Forward
option src wan
option dest *
option proto icmp
list icmp_type echo-request
list icmp_type echo-reply
list icmp_type destination-unreachable
list icmp_type packet-too-big
list icmp_type time-exceeded
list icmp_type bad-header
list icmp_type unknown-header-type
option limit 1000/sec
option family ipv6
option target ACCEPT
config rule
option name Allow-IPSec-ESP
option src wan
option dest lan
option proto esp
option target ACCEPT
config rule
option name Allow-ISAKMP
option src wan
option dest lan
option dest_port 500
option proto udp
option target ACCEPT
### EXAMPLE CONFIG SECTIONS
# do not allow a specific ip to access wan
#config rule
# option src lan
# option src_ip 192.168.45.2
# option dest wan
# option proto tcp
# option target REJECT
# block a specific mac on wan
#config rule
# option dest wan
# option src_mac 00:11:22:33:44:66
# option target REJECT
# block incoming ICMP traffic on a zone
#config rule
# option src lan
# option proto ICMP
# option target DROP
# port redirect port coming in on wan to lan
#config redirect
# option src wan
# option src_dport 80
# option dest lan
# option dest_ip 192.168.16.235
# option dest_port 80
# option proto tcp
# port redirect of remapped ssh port (22001) on wan
#config redirect
# option src wan
# option src_dport 22001
# option dest lan
# option dest_port 22
# option proto tcp
### FULL CONFIG SECTIONS
#config rule
# option src lan
# option src_ip 192.168.45.2
# option src_mac 00:11:22:33:44:55
# option src_port 80
# option dest wan
# option dest_ip 194.25.2.129
# option dest_port 120
# option proto tcp
# option target REJECT
#config redirect
# option src lan
# option src_ip 192.168.45.2
# option src_mac 00:11:22:33:44:55
# option src_port 1024
# option src_dport 80
# option dest_ip 194.25.2.129
# option dest_port 120
# option proto tcp
No, client isolation is not enabled by default. And it's not enabled in your config, either, so that's not the cause of the issue.
Are there any other infrastructure devices in your network? Do you have multiple APs, for example? Or managed switches or anything like that?
There isn't. I have my ISP router as bridge and the AX3600 is connected to it on PPPoE.
All my devices are connected to the AX3600 (Only PC on the lan port and others on the 2.4g or 5g wifi)
Mi 3G is on another subnet and connected to the 5G wifi of the AX3600.
to be clear, you're talking about the lan interface of the mi 3g, right? I saw that it is using the address 192.168.1.1 for the lan. And the wwan network interface you said is on 10.10.10.217, right? And this 10.10.10.0/24 network is the main lan subnet, where your PC and android phone are located, correct?
One more thing -- are you by any chance running a VPN client on your phone and/or windows computer?
Exactly, MI3G lan is 192.168.1.1 and AX3600 lan is 10.10.10.10
Once I connected the MI3G through the AX3600 wifi, on wan, it got the 10.10.10.217 through DHCP.
My pc and phone are clients to the AX3600 and I'm not running VPN on them.
I even tried to put MI3G lan on 10.10.10.20, but it didn't received internet, as it was on the same subnet as the AX3600, and I couldn't download packages. (samba)
This is expected. Best to leave your Mi3g on a different subnet for its lan interface.
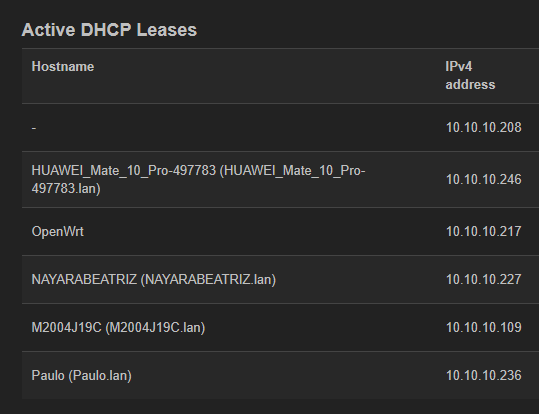
I see you have 6 devices shown in the DHCP leases there... that means you have 3 other devices that you haven't talked about. Are those phones/tables or computers or something else entirely (like IoT devices or printers, etc.)?
Can any of those remaining 3 devices ping the mi3g? Can the Windows machine ping any of the 5 other leases?
In order:
Tried to ping my phone and got a good response
ping 10.10.10.246
Disparando 10.10.10.246 com 32 bytes de dados:
Resposta de 10.10.10.246: bytes=32 tempo=155ms TTL=64
Resposta de 10.10.10.246: bytes=32 tempo=370ms TTL=64
Resposta de 10.10.10.246: bytes=32 tempo=384ms TTL=64
Resposta de 10.10.10.246: bytes=32 tempo=399ms TTL=64
Estatísticas do Ping para 10.10.10.246:
Pacotes: Enviados = 4, Recebidos = 4, Perdidos = 0 (0% de
perda),
Aproximar um número redondo de vezes em milissegundos:
Mínimo = 155ms, Máximo = 399ms, Média = 327ms
Sorry, it's in portuguese but it worked out.
Tried to ping the router on the laptop and still got the same message as I got in My PC.
So, got some news.
I've Plugged my PC into the 3G, and remove the 5g wifi and conected to the 2,4g one.
MI 3G received a new ip (10.10.10.216) and was visible on other devices this time..
Its the exactly same setup I did for 5G..
strange... I have no idea why the 5G network wasn't working. I will keep thinking about it, but I certainly can't explain that situation.
I see.. thanks anyway for your support. Sadly I really needed to use it in the 5g for better speeds, I'll see what I can do about that..