hello,
I've setup some network traffic monitoring tools for OpenWRT 21.2.01 described here. It's a good list.
iftop is pretty nifty and the ~/.iftoprc is helpful for getting simple outputs like on the iftop project page. This is what's in ~/.iftoprc:
hide-source: yes
line-display: one-line-both
port-display: on
port-resolution: yes
This, and the iftop filters make it simple to remove the clutter, like http port 80, https port 443, ntp on port 123 and dns on port 53 with this:
iftop -i wan -f "not port ntp and not port 80 and not port 443 and not port 53"
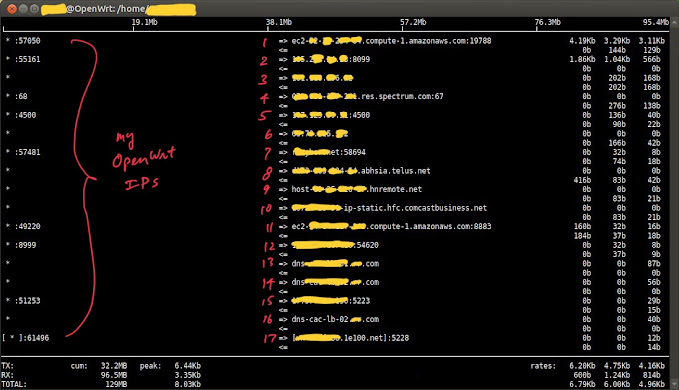
What's remaining appears to be some bizarre traffic happening on non-standard ports.
It's not at all clear what's going on with someone in Switzerland on port 8099 (thank you nslookup). And there are a few Amazon AWS instances that seem to communicate with something on my router or home network even after a reboot.
What are some good tools for OpenWRT for discovering more about the devices or processes associated with these external machines and network ports?
How can I find out who's doing what on my router or my network?