Hi!
First I'd like to apologize for asking in these forums, as my problem is not directly OpenWRT related. But I feel the only experts are here. And who knows, maybe any results here can help future OpenWRT hardware support.
Recently I acquired a box of broken routers with a "Telekom Speedport 4 Type A" (made by Arcadyan) inside. This device was initially dead as a doornail. All step down converters on the board were not operating. I found the short circuit at the VCC/GND pads of the NAND IC. It was soaked in flux, and whoever swapped it out apparently overlooked the tiny solder bridge between a pair of Vcc/GND pads. After removing that bridge, the device started and showed a Telekom logo on the front display while flashing a green LED. But that was it all. No DHCP, no WiFi.
I then soldered a serial connection to the board. Here's the boot log.
boot.txt
It looks like CFE first tries to boot an image at offset 0x00100000. After the last output of "got hash for rootfs" the device then seems to reset and it attempts another boot, this time from offset 0x05100000. It then stalls at the output of "got hash for rootfs". Unfortunately, there's no output from the booted kernel itself. So there's no hint on what it doesn't like about the two apparently existing 010139.2.1.002.0 images. My guess is that the rootfs hashes don't match the NAND content.
I can enter commands in the CFE environment. But anything I can find in the net about CFE seems to relate to other CFE versions with different commands. It seems that these commands are available to me: "Available commands: otpcfg, erase_misc_parti, x, find, comp, bb, fb, rn, dn, phy, meminfo, kernp, sm, db, dh, dw, ddw, wc, w, e, ws, ba, ldt, go, loadb, r, p, c, i, avs, ddr, a, b, reset, pmdio, spi, pmclog, pmc, closeavs, cpufreq, force, help"
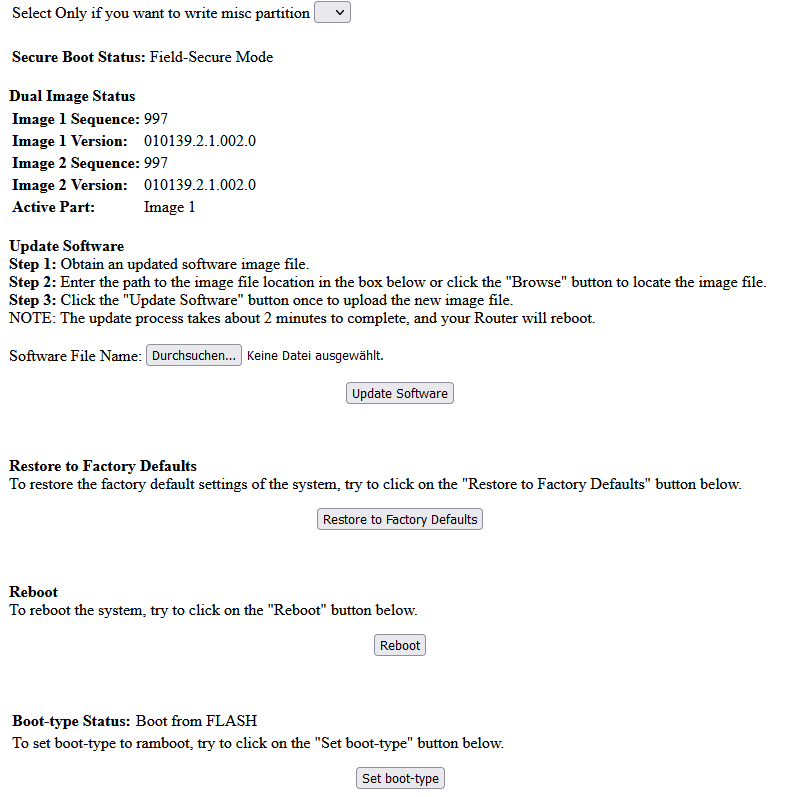
Also, I can connect to the (CFE?) web interface available at 192.168.2.1:
As it offers a firmware update option, I thought that I may be able to just update the firmware to replace the possibly damaged firmware images in the flash. However, official firmware update files are rejected ("invalid image format"). If I take a closer look at those official firmware update files, they seem very much completely encrypted to me (and not compressed). As expected, binwalk shows no results at all.
I really would like to get this thing to work. Would be a shame to throw away a modern WiFi 6 router just because of stupid software restrictions.
Any ideas what I could try next? I -could- remove the NAND again and read it to get unencrypted access to the installed images for some reverse engineering, but I'd rather like to avoid that if possible ![]()
Thanks!