Solved, solution at the bottom
TP-LINK Archer C7 v5 running 18.06.1
I read all posts I could find and the solution seems to be routing policies. However I'm having trouble understanding them.
What I want:
- br-lan (192.168.1.0/24) => normal ISP connection
- br-lan2 (192.168.10.0/24) => OpenVPN client
- Both LANs can communicate to each other
(done with by forwarding LANs to each other)No longer works with the solution I found.
What happens
OpenVPN down:
- br-lan (192.168.1.0/24) => ISP
- br-lan2 (192.168.10.0/24) => ISP
OpenVPN up:
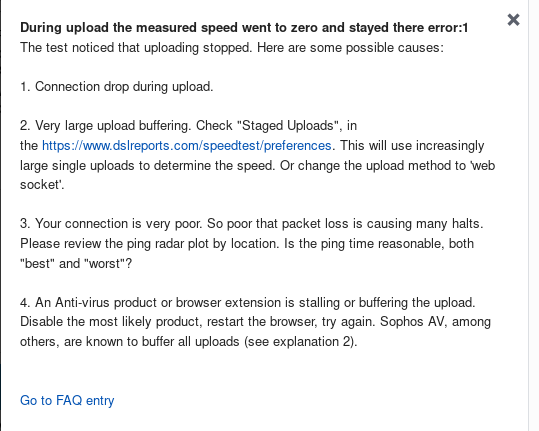
- br-lan => no connection (can't ping 8.8.8.8, so I don't think it's a DNS problem)
- br-lan2 => connects to VPN
What's been done
From what I understood when the OpenVPN is up everything goes through tun0.
According to the wiki I need to use via <ip_of_the_far_end_of_your_tunnel>, but I don't understand what that means. Is the gateway for the br-lan? Or the default gateway from the ISP?
I tried the following (no change noticed):
ip route add default via 192.168.1.1 dev br-lan table lan
ip route flush cache
ip rule add from 192.168.1.0/24 table lan
I also tried (lost connection to the router and had to reboot it):
ip route add default via 100.64.192.1 dev eth0.2 table lan
ip route flush cache
ip rule add from 192.168.1.0/24 table lan
Question
How I make it so:
- 192.168.1.0/24 => ISP
- 192.168.10.0/24 => VPN
- LANs can ping/communicate with eachother
Configs
etc/config/network
config interface 'loopback'
option ifname 'lo'
option proto 'static'
option ipaddr '127.0.0.1'
option netmask '255.0.0.0'
config globals 'globals'
option ula_prefix 'fd32:c7d2:6fa8::/48'
config interface 'lan'
option type 'bridge'
option ifname 'eth0.1'
option proto 'static'
option ipaddr '192.168.1.1'
option netmask '255.255.255.0'
option ip6assign '60'
config interface 'wan'
option ifname 'eth0.2'
option proto 'dhcp'
config interface 'wan6'
option ifname 'eth0.2'
option proto 'dhcpv6'
config switch
option name 'switch0'
option reset '1'
option enable_vlan '1'
config switch_vlan
option device 'switch0'
option vlan '1'
option ports '2 3 4 5 0t'
config switch_vlan
option device 'switch0'
option vlan '2'
option ports '1 0t'
config interface 'vpn'
option proto 'none'
option ifname 'tun0'
config interface 'lan2'
option type 'bridge'
option proto 'static'
option ipaddr '192.168.10.1'
option netmask '255.255.255.0'
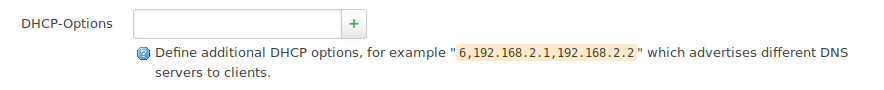
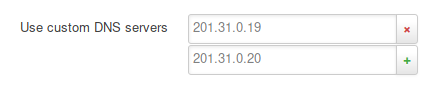
option dns '10.21.0.1'
option ip6assign '60'
etc/config/firewall
config defaults
option syn_flood '1'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'REJECT'
config zone
option name 'lan'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'ACCEPT'
option network 'lan'
config zone
option name 'wan'
option input 'REJECT'
option output 'ACCEPT'
option forward 'REJECT'
option masq '1'
option mtu_fix '1'
option network 'wan wan6'
config rule
option name 'Allow-DHCP-Renew'
option src 'wan'
option proto 'udp'
option dest_port '68'
option target 'ACCEPT'
option family 'ipv4'
config rule
option name 'Allow-Ping'
option src 'wan'
option proto 'icmp'
option icmp_type 'echo-request'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-IGMP'
option src 'wan'
option proto 'igmp'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-DHCPv6'
option src 'wan'
option proto 'udp'
option src_ip 'fc00::/6'
option dest_ip 'fc00::/6'
option dest_port '546'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-MLD'
option src 'wan'
option proto 'icmp'
option src_ip 'fe80::/10'
list icmp_type '130/0'
list icmp_type '131/0'
list icmp_type '132/0'
list icmp_type '143/0'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Input'
option src 'wan'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
list icmp_type 'router-solicitation'
list icmp_type 'neighbour-solicitation'
list icmp_type 'router-advertisement'
list icmp_type 'neighbour-advertisement'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Forward'
option src 'wan'
option dest '*'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-IPSec-ESP'
option src 'wan'
option dest 'lan'
option proto 'esp'
option target 'ACCEPT'
config rule
option name 'Allow-ISAKMP'
option src 'wan'
option dest 'lan'
option dest_port '500'
option proto 'udp'
option target 'ACCEPT'
config include
option path '/etc/firewall.user'
config zone
option input 'ACCEPT'
option output 'ACCEPT'
option name 'lan2'
option forward 'ACCEPT'
option network 'lan2'
config forwarding
option dest 'wan'
option src 'lan2'
config zone
option name 'vpnclient'
option network 'vpn'
option input 'REJECT'
option output 'ACCEPT'
option forward 'REJECT'
option masq '1'
option mtu_fix '1'
config forwarding
option src 'lan2'
option dest 'vpn'
config forwarding
option src 'lan2'
option dest 'vpnclient'
config forwarding
option dest 'wan'
option src 'lan'
VPN Down
ip route (VPN down)
default via xxx.xx.192.1 dev eth0.2 proto static src xxx.xx.196.32
100.64.192.0/18 dev eth0.2 proto kernel scope link src xxx.xx.196.32
192.168.1.0/24 dev br-lan proto kernel scope link src 192.168.1.1
192.168.10.0/24 dev br-lan2 proto kernel scope link src 192.168.10.1
route (VPN down)
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
default xxx.xx.192.1 0.0.0.0 UG 0 0 0 eth0.2
xxx.xx.192.0 * 255.255.192.0 U 0 0 0 eth0.2
192.168.1.0 * 255.255.255.0 U 0 0 0 br-lan
192.168.10.0 * 255.255.255.0 U 0 0 0 br-lan2
VPN up
ip route (VPN up)
0.0.0.0/1 via xx.xx.0.102 dev tun0
default via xxx.xx.192.1 dev eth0.2 proto static src xxx.xx.196.32
xx.xx.0.1 via xx.xx.0.102 dev tun0
xx.xx.0.102 dev tun0 proto kernel scope link src xx.xx.0.101
xx.xxx.143.250 via 100.64.192.1 dev eth0.2
xxx.xx.192.0/18 dev eth0.2 proto kernel scope link src xxx.xx.196.32
128.0.0.0/1 via 10.21.0.102 dev tun0
192.168.1.0/24 dev br-lan proto kernel scope link src 192.168.1.1
192.168.10.0/24 dev br-lan2 proto kernel scope link src 192.168.10.1
route (VPN up)
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
default xx.xx.0.102 128.0.0.0 UG 0 0 0 tun0
default xxx.xx.192.1 0.0.0.0 UG 0 0 0 eth0.2
xx.xx.0.1 xx.xx.0.102 255.255.255.255 UGH 0 0 0 tun0
xx.xx.0.102 * 255.255.255.255 UH 0 0 0 tun0
xx.xxx.143.250 xxx.xx.192.1 255.255.255.255 UGH 0 0 0 eth0.2
xxx.xx.192.0 * 255.255.192.0 U 0 0 0 eth0.2
128.0.0.0 xx.xx.0.102 128.0.0.0 UG 0 0 0 tun0
192.168.1.0 * 255.255.255.0 U 0 0 0 br-lan
192.168.10.0 * 255.255.255.0 U 0 0 0 br-lan2
Some Related Questions
Links
SOLVED: 2 VLAN's and no internet on 1 VLAN
https://serverfault.com/questions/775865/openvpn-on-openwrt-routing-a-specific-subnet-through-a-vpn-tunnel
https://serverfault.com/questions/894412/lede-two-vlans-when-one-connects-to-openvpn-the-other-has-no-internet-connec
https://superuser.com/questions/1309236/configure-vpn-tunnel-just-for-one-vlan
Use WireGuard interface for specific devices only
Edit: typo/formatting