Hello everybody,
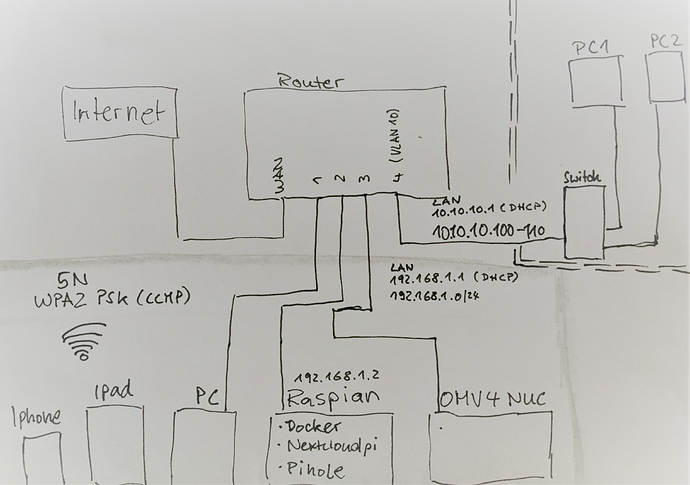
I have installed OWRT on my router few days ago. Now I've tried my hand at the Vlan. You will find a scheme in the appendix. I share my internet with a friend from the apartment building. The new VLAN 10 is for his apartment. There is a switch and 2 PCs. I don't want it that he come into my network and vice versa.
with a scan with nmap in the 10.10.10.1/24 network, the devices in the 192.168.1.1/24 network are recognized except for the raspi.
but you can only access the router. that looks ok to me.
can you take another look at the config / network and the config / firewall? i haven't done this yet and i want to avoid a big mistake.
many thanks and greetings from thuringia
root@OpenWrt:~# cat /etc/config/network
config interface 'loopback'
option ifname 'lo'
option proto 'static'
option ipaddr '127.0.0.1'
option netmask '255.0.0.0'
config globals 'globals'
option ula_prefix 'XXXXXXXXX:75a4::/48'
config interface 'lan'
option type 'bridge'
option ifname 'eth0.1'
option proto 'static'
option ipaddr '192.168.1.1'
option netmask '255.255.255.0'
option ip6assign '60'
list dns '192.168.1.2'
list dns 'XXXXXXXX.42'
config interface 'OG'
option type 'bridge'
option proto 'static'
option ipaddr '10.10.10.1'
option netmask '255.255.255.0'
option ip6assign '60'
option ifname 'eth0.10'
config interface 'wan'
option ifname 'eth0.2'
option proto 'dhcp'
config device 'wan_eth0_2_dev'
option name 'eth0.2'
option macaddr 'xxxxxxxx:xx:43'
config interface 'wan6'
option ifname 'eth0.2'
option proto 'dhcpv6'
config switch
option name 'switch0'
option reset '1'
option enable_vlan '1'
config switch_vlan
option device 'switch0'
option vlan '1'
option vid '1'
option ports '0t 2 3 4'
config switch_vlan
option device 'switch0'
option vlan '2'
option ports '0t 1'
option vid '2'
config switch_vlan
option device 'switch0'
option vlan '10'
option ports '0t 5'
option vid '10'
root@OpenWrt:~# cat /etc/config/firewall
config defaults
option syn_flood '1'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'REJECT'
config zone
option name 'lan'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'ACCEPT'
option network 'lan'
config zone
option name 'wan'
option input 'REJECT'
option output 'ACCEPT'
option forward 'REJECT'
option masq '1'
option mtu_fix '1'
option network 'wan wan6'
config forwarding
option src 'lan'
option dest 'wan'
config rule
option name 'Allow-ICMPv6-Forward'
option src 'wan'
option dest '*'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-IPSec-ESP'
option src 'wan'
option dest 'lan'
option proto 'esp'
option target 'ACCEPT'
config rule
option name 'Allow-ISAKMP'
option src 'wan'
option dest 'lan'
option dest_port '500'
option proto 'udp'
option target 'ACCEPT'
config include
option path '/etc/firewall.user'
config redirect
option dest_port '443'
option src 'wan'
option name 'nxt443'
option src_dport '443'
option target 'DNAT'
option dest_ip '192.168.1.2'
option dest 'lan'
config redirect
option dest_port '80'
option src 'wan'
option name 'nxt80'
option src_dport '80'
option target 'DNAT'
option dest_ip '192.168.1.2'
option dest 'lan'
config zone
option input 'ACCEPT'
option name 'OG'
option output 'ACCEPT'
option network 'OG'
option forward 'ACCEPT'
config forwarding
option dest 'wan'
option src 'OG'