Hi
To cut a long story short I'm in the process of making pre-configured files which I will be embedding into my own compiled router firmware.
The biggest task is setting up a VPN server so that outside traffic will be able to join my LAN, access LAN resources such as a SMB server, and ensure an encrypted connection when using open, unsecured AP's, therefore would like to use a secure VPN tunnel to encrypt the data.
I've been trying to setup OpenVPN following this guide https://openwrt.org/docs/guide-user/services/vpn/openvpn/basic
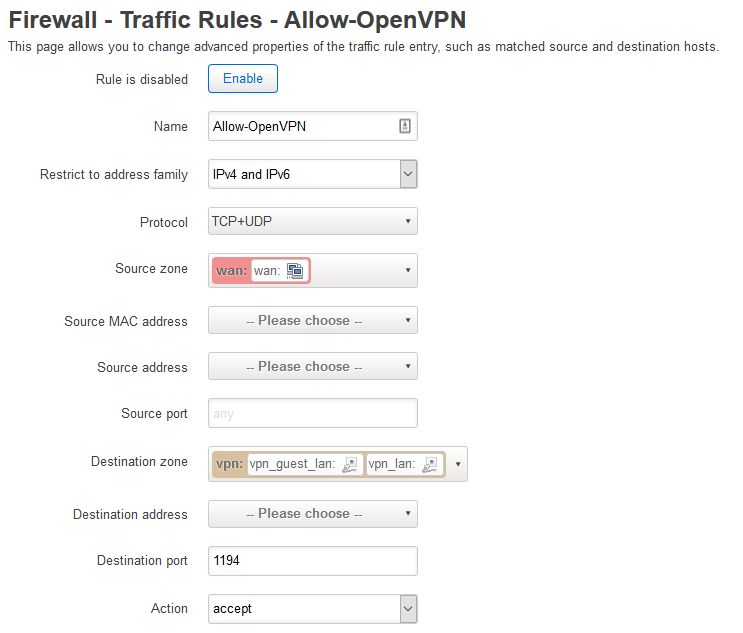
So far I have setup a VPN interface that is set to 'tun0'. The guide says to use firewall rules but I'd rather use firewall zone as it seems a better of keeping track of what interface is connected to what firewall zone whilst using LuCI.
The problem I find with the current guide is that the big blocks of commands are uneasy to follow, often losing track of what command(s) I Iast typed in as most of it is automated. I'd rather like to configure everything manually via the nano editor or accessing the configuration files via SFTP/SCP, modifying them and re-uploading them so I know how everything is working.
In terms of generating the CA, private and public keys, I'm leaning towards using my desktop PC for that as it's a lot more powerful. I'm already using OpenSSL to generate to make my own certificate authority that I was going to use to sign my private and public keys.
All I'm thinking of doing is generating the certificates on my Linux PC using the Easy-RSA package and then tweaking the '/etc/config/OpenVPN' config and setting the paths to where I have uploaded the certificates onto the router. So long as I set the hostnames, common names and SAN's (subject alternative names) I should be fine? I assume if I have setup a DDNS hostname, do I set this in the SAN's? Is there anything else that needs doing?
Is anyone able to supply a fully configured OpenVPN config file (excluding sensitive information)?
My last question is how do I setup the IP addresses for the VPN interface. In my case I would like the VPN clients to be able to access my home network, as though they're on the LAN. How do I achieve this?
For example if I set the VPN interface's network ID to 10.0.0.1/24 in the OpenVPN configuration do the clients connected get a host IP within the 10.0.0.0/24 range? If so how do I get the outside connecting client to communicate with existing LAN clients or is it a simple case of knowing the client IP address/hostname to connect to its resources?
Any help appreciated
Many thanks
Will