hello everyone,
so my end goal is

my goal is that networks coming out of openwrt to be isolated from each other ...
my question is whats the right approach here?
one other thing i want is to be able access luci from pfsense (ie my lans)...
i tried some fiddling with firewall rules but i think im not doing it right...
EDIT:
im running x86 openwrt so i dont have a internal switch but 4 discrete nics...(two wans coming from dsl modems and two lans carrying internet to pfsene
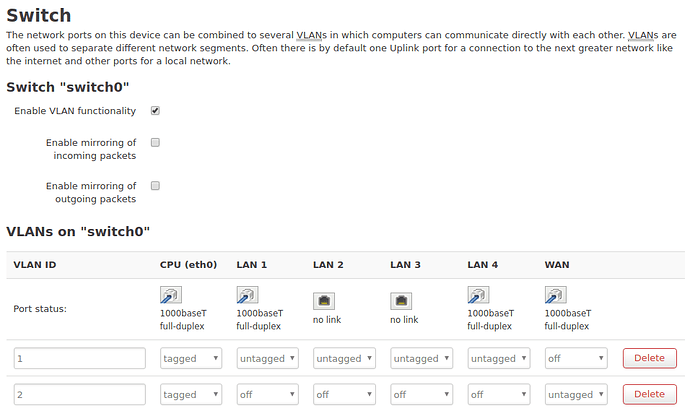
You should have at least 4 VLANs in the OpenWrt, then:
- VLAN 1 (bridged) - Default LAN
- VLAN 2 - Default WAN ADSL 1
- VLAN 3 (bridged) - Second LAN
- VLAN 4 - Second WAN ADSL 2
- VLANs 1 and 2 should already be configured properly
- VLANs 3 and 4, permit forwarding from second LAN to Second WAN
- Done
Switch Ports
- you can edit access VLANs in OpenWrt on the LuCI web GUI at Network > Switch.
Hope this helps.
I think you should explain why you need two routers and what role is each one supposed to play.
so no special firewall rules is requierd ..hmm..
since im running a x86 installation(no switches - ie. no switch tab) i need to find some other way to do vlan ill see what i can do..
..................................................
ive added openwrt box behind pfsense mainly for it to be vpn gateway due to pfsense not supporting that many vpn protocols
It seems to me if it's just a VPN gateway it'd be better to put it on the LAN side of the PFSense box, so that it only handles the VPN traffic not piping ALL the traffic through the OpenWrt and PFSense
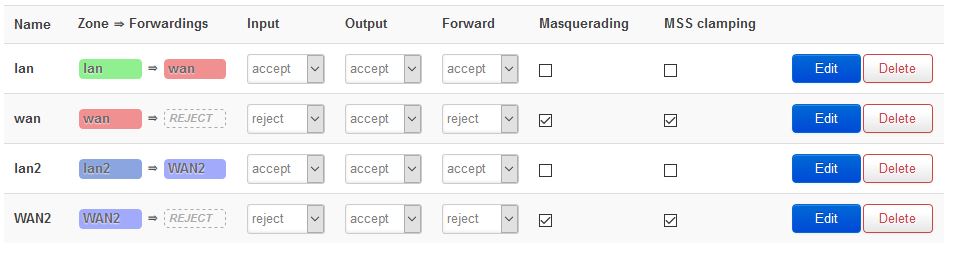
Yes, you have to create the LAN2 and WAN2 firewall zones in order to configure Allow Forwarding form LAN2 to WAN2.
so i have to do both firewall rules and Vlans?
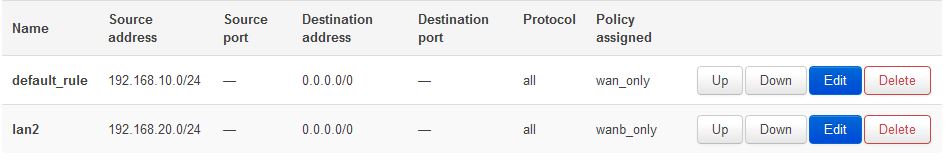
here is my current firewall rules nothing interesting..
lan 1 i working fine
right now im stuck trying to make openwrt unerstand there are 2 wan gateway and make it assign each to a lan...
In Interfaces, under Advanced > Firewall Settings.
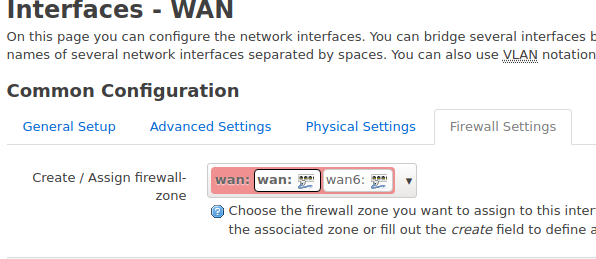
@lleachii i did that and it did not work .....
lan1 did have internet but through whichever gateway was online first so it could be WAN2>Lan1
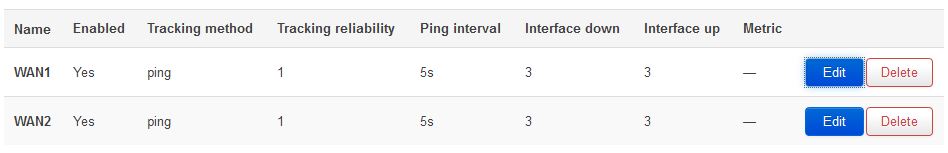
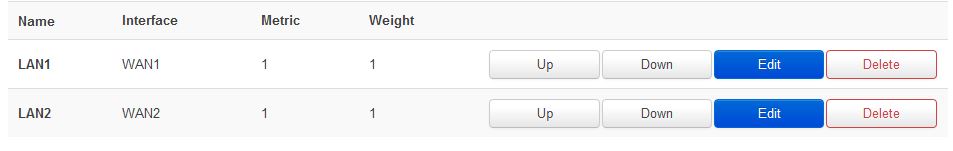
i did made it "work" using mwan3 but idont think its the right approach ....
here is my current mwan3 setting:
right now WAN1>LAN1 & WAN2>LAN2 is "working"...
so far so good ...
Ummmm...this is the first time you mentioned mwan3...
I'm not familiar with that package - I thought we were doing:
Is this not the case?
mwan3 is the "Load Balance" tab...
.............
they are isolated from what ive seen so far ie WAN1>LAN1 & WAN2>LAN2 is working and lan1 cant ping lan2 ...
so isolated i would say ...
basically what i did with mwan3 is not really its use case but its working for now .... need more testing to be 100% sure there is no problem though...