need help can not get to open port 443 to work
got a raspberry pi 4 running the latest firmware and every thing is working like it is supposed to , but can not get port 443 open
tcpdump por 443 not working
port 443
root@rpi4-router /37# tcpdump -v -n -i eth1 port 443 and src canyouseeme.org
tcpdump: listening on eth1, link-type EN10MB (Ethernet), capture size 262144 bytes
09:23:56.603033 IP (tos 0x20, ttl 46, id 0, offset 0, flags [DF], proto TCP (6), length 52)
52.202.215.126.443 > 73.232.38.41.49601: Flags [S.], cksum 0xedc4 (correct), seq 3757102762, ack 1513867147, win 26883, options [mss 1460,nop,nop,sackOK,nop,wscale 7], length 0
09:23:56.603462 IP (tos 0x20, ttl 46, id 0, offset 0, flags [DF], proto TCP (6), length 52)
52.202.215.126.443 > 73.232.38.41.57980: Flags [S.], cksum 0xf0d3 (correct), seq 2196234883, ack 3227553484, win 26883, options [mss 1460,nop,nop,sackOK,nop,wscale 7], length 0
09:23:56.649319 IP (tos 0x20, ttl 46, id 59772, offset 0, flags [DF], proto TCP (6), length 40)
52.202.215.126.443 > 73.232.38.41.49601: Flags [.], cksum 0x94ba (correct), ack 518, win 219, length 0
09:23:56.649557 IP (tos 0x20, ttl 46, id 56659, offset 0, flags [DF], proto TCP (6), length 40)
52.202.215.126.443 > 73.232.38.41.57980: Flags [.], cksum 0x97c9 (correct), ack 518, win 219, length 0
09:23:56.650242 IP (tos 0x20, ttl 46, id 59773, offset 0, flags [DF], proto TCP (6), length 1500)
52.202.215.126.443 > 73.232.38.41.49601: Flags [.], cksum 0xb31f (correct), seq 1:1461, ack 518, win 219, length 1460
09:23:56.650669 IP (tos 0x20, ttl 46, id 59774, offset 0, flags [DF], proto TCP (6), length 1500)
52.202.215.126.443 > 73.232.38.41.49601: Flags [.], cksum 0x20c4 (correct), seq 1461:2921, ack 518, win 219, length 1460
09:23:56.650670 IP (tos 0x20, ttl 46, id 59775, offset 0, flags [DF], proto TCP (6), length 1216)
52.202.215.126.443 > 73.232.38.41.49601: Flags [P.], cksum 0x98f5 (correct), seq 2921:4097, ack 518, win 219, length 1176
09:23:56.651118 IP (tos 0x20, ttl 46, id 56660, offset 0, flags [DF], proto TCP (6), length 1500)
52.202.215.126.443 > 73.232.38.41.57980: Flags [.], cksum 0x9faf (correct), seq 1:1461, ack 518, win 219, length 1460
09:23:56.651119 IP (tos 0x20, ttl 46, id 56661, offset 0, flags [DF], proto TCP (6), length 1500)
52.202.215.126.443 > 73.232.38.41.57980: Flags [.], cksum 0x23d3 (correct), seq 1461:2921, ack 518, win 219, length 1460
09:23:56.651120 IP (tos 0x20, ttl 46, id 56662, offset 0, flags [DF], proto TCP (6), length 1216)
52.202.215.126.443 > 73.232.38.41.57980: Flags [P.], cksum 0x9c04 (correct), seq 2921:4097, ack 518, win 219, length 1176
09:23:56.651759 IP (tos 0x20, ttl 46, id 56663, offset 0, flags [DF], proto TCP (6), length 438)
52.202.215.126.443 > 73.232.38.41.57980: Flags [P.], cksum 0xb517 (correct), seq 4097:4495, ack 518, win 219, length 398
09:23:56.651759 IP (tos 0x20, ttl 46, id 59776, offset 0, flags [DF], proto TCP (6), length 438)
52.202.215.126.443 > 73.232.38.41.49601: Flags [P.], cksum 0x1f75 (correct), seq 4097:4495, ack 518, win 219, length 398
09:23:56.694506 IP (tos 0x20, ttl 46, id 59777, offset 0, flags [DF], proto TCP (6), length 314)
52.202.215.126.443 > 73.232.38.41.49601: Flags [P.], cksum 0xf4f1 (correct), seq 4495:4769, ack 644, win 219, length 274
09:23:56.694507 IP (tos 0x20, ttl 46, id 56664, offset 0, flags [DF], proto TCP (6), length 314)
52.202.215.126.443 > 73.232.38.41.57980: Flags [P.], cksum 0xbd3c (correct), seq 4495:4769, ack 644, win 219, length 274
09:23:56.746637 IP (tos 0x20, ttl 47, id 49684, offset 0, flags [DF], proto TCP (6), length 60)
52.202.215.126.46241 > 73.232.38.41.443: Flags [S], cksum 0x56bb (correct), seq 765394427, win 26883, options [mss 1460,sackOK,TS val 3925950447 ecr 0,nop,wscale 7], length 0
09:23:56.783646 IP (tos 0x20, ttl 46, id 56665, offset 0, flags [DF], proto TCP (6), length 40)
52.202.215.126.443 > 73.232.38.41.57980: Flags [.], cksum 0x8113 (correct), ack 1550, win 233, length 0
09:23:57.744387 IP (tos 0x20, ttl 47, id 49685, offset 0, flags [DF], proto TCP (6), length 60)
52.202.215.126.46241 > 73.232.38.41.443: Flags [S], cksum 0x55c1 (correct), seq 765394427, win 26883, options [mss 1460,sackOK,TS val 3925950697 ecr 0,nop,wscale 7], length 0
09:23:59.747779 IP (tos 0x20, ttl 47, id 49686, offset 0, flags [DF], proto TCP (6), length 60)
52.202.215.126.46241 > 73.232.38.41.443: Flags [S], cksum 0x53cc (correct), seq 765394427, win 26883, options [mss 1460,sackOK,TS val 3925951198 ecr 0,nop,wscale 7], length 0
09:23:59.904045 IP (tos 0x20, ttl 46, id 56666, offset 0, flags [DF], proto TCP (6), length 1500)
52.202.215.126.443 > 73.232.38.41.57980: Flags [.], cksum 0xbc20 (correct), seq 4769:6229, ack 1550, win 233, length 1460
09:23:59.904368 IP (tos 0x20, ttl 46, id 56667, offset 0, flags [DF], proto TCP (6), length 1500)
52.202.215.126.443 > 73.232.38.41.57980: Flags [.], cksum 0x2e77 (correct), seq 6229:7689, ack 1550, win 233, length 1460
09:23:59.904596 IP (tos 0x20, ttl 46, id 56668, offset 0, flags [DF], proto TCP (6), length 1176)
52.202.215.126.443 > 73.232.38.41.57980: Flags [P.], cksum 0x840a (correct), seq 7689:8825, ack 1550, win 233, length 1136
tcpdump port 80 it is working
port 80
root@rpi4-router /37# tcpdump -v -n -i eth1 port 80 and src canyouseeme.org
tcpdump: listening on eth1, link-type EN10MB (Ethernet), capture size 262144 bytes
09:24:58.139300 IP (tos 0x20, ttl 47, id 62609, offset 0, flags [DF], proto TCP (6), length 60)
52.202.215.126.53449 > 73.232.38.41.80: Flags [S], cksum 0xe639 (correct), seq 3052638069, win 26883, options [mss 1460,sackOK,TS val 3925965796 ecr 0,nop,wscale 7], length 0
09:24:58.179983 IP (tos 0x20, ttl 47, id 62610, offset 0, flags [DF], proto TCP (6), length 52)
52.202.215.126.53449 > 73.232.38.41.80: Flags [.], cksum 0x664e (correct), ack 1650098655, win 211, options [nop,nop,TS val 3925965806 ecr 2049095793], length 0
09:24:58.180420 IP (tos 0x20, ttl 47, id 62611, offset 0, flags [DF], proto TCP (6), length 52)
52.202.215.126.53449 > 73.232.38.41.80: Flags [F.], cksum 0x664d (correct), seq 0, ack 1, win 211, options [nop,nop,TS val 3925965806 ecr 2049095793], length 0
09:24:58.221335 IP (tos 0x20, ttl 47, id 62612, offset 0, flags [DF], proto TCP (6), length 52)
52.202.215.126.53449 > 73.232.38.41.80: Flags [.], cksum 0x6619 (correct), ack 2, win 211, options [nop,nop,TS val 3925965816 ecr 2049095834], length 0
firewall config
config defaults
option syn_flood '1'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'REJECT'
config zone
option name 'lan'
list network 'lan'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'ACCEPT'
config zone
option name 'wan'
list network 'wan'
list network 'wan6'
option input 'REJECT'
option output 'ACCEPT'
option forward 'REJECT'
option masq '1'
option mtu_fix '1'
config forwarding
option src 'lan'
option dest 'wan'
config rule
option name 'Allow-DHCP-Renew'
option src 'wan'
option proto 'udp'
option dest_port '68'
option target 'ACCEPT'
option family 'ipv4'
config rule
option name 'Allow-Ping'
option src 'wan'
option proto 'icmp'
option icmp_type 'echo-request'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-IGMP'
option src 'wan'
option proto 'igmp'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-DHCPv6'
option src 'wan'
option proto 'udp'
option src_ip 'fc00::/6'
option dest_ip 'fc00::/6'
option dest_port '546'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-MLD'
option src 'wan'
option proto 'icmp'
option src_ip 'fe80::/10'
list icmp_type '130/0'
list icmp_type '131/0'
list icmp_type '132/0'
list icmp_type '143/0'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Input'
option src 'wan'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
list icmp_type 'router-solicitation'
list icmp_type 'neighbour-solicitation'
list icmp_type 'router-advertisement'
list icmp_type 'neighbour-advertisement'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Forward'
option src 'wan'
option dest '*'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-IPSec-ESP'
option src 'wan'
option dest 'lan'
option proto 'esp'
option target 'ACCEPT'
config rule
option name 'Allow-ISAKMP'
option src 'wan'
option dest 'lan'
option dest_port '500'
option proto 'udp'
option target 'ACCEPT'
config rule
option name 'Support-UDP-Traceroute'
option src 'wan'
option dest_port '33434:33689'
option proto 'udp'
option family 'ipv4'
option target 'REJECT'
option enabled 'false'
config include
option path '/etc/firewall.user'
option reload '1'
config redirect
option target 'DNAT'
option name 'QukyNASPort5000'
option src 'wan'
option src_dport '5000'
option dest 'lan'
option dest_ip '192.168.1.180'
option dest_port '5000'
list proto 'tcp'
list proto 'udp'
config redirect
option target 'DNAT'
option name 'QukyNASPort50001'
option src 'wan'
option src_dport '5001'
option dest 'lan'
option dest_ip '192.168.1.180'
option dest_port '5001'
list proto 'tcp'
list proto 'udp'
config redirect
option target 'DNAT'
option name 'OctodashPort80'
list proto 'tcp'
option src 'wan'
option src_dport '55001'
option dest 'lan'
option dest_ip '192.168.1.114'
option dest_port '5002'
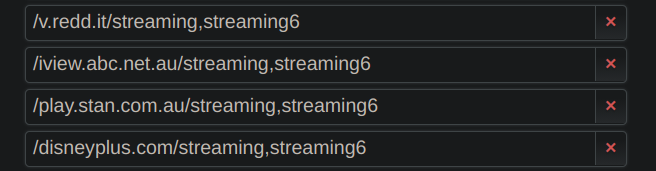
config redirect
option target 'DNAT'
option name 'OctodashPort443'
option src 'wan'
option src_dport '443'
option dest 'lan'
option dest_ip '192.168.1.114'
option dest_port '443'
list proto 'tcp'
list proto 'udp'
option enabled '0'
config redirect
option target 'DNAT'
option name 'QukyNASPort443'
option src 'wan'
option src_dport '443'
option dest 'lan'
option dest_ip '192.168.1.180'
option dest_port '443'
list proto 'tcp'
list proto 'udp'
option enabled '0'
config redirect
option target 'DNAT'
option name 'trasnmission9091'
list proto 'tcp'
option src 'wan'
option src_dport '9091'
option dest 'lan'
option dest_ip '192.168.1.180'
option dest_port '9091'
config redirect
option target 'DNAT'
option name 'FTP_PCPort22'
option src 'wan'
option src_dport '22'
option dest 'lan'
option dest_ip '192.168.1.170'
option dest_port '22'
list proto 'tcp'
list proto 'udp'
config include 'timecontrol'
option type 'script'
option path '/var/etc/timecontrol.include'
option reload '1'
config redirect
option target 'DNAT'
option name 'webserber80'
option src 'wan'
option dest 'lan'
list proto 'tcp'
option src_dport '80'
option dest_port '80'
option dest_ip '192.168.1.233'
config redirect
option target 'DNAT'
option name 'Webserber443'
option src 'wan'
option src_dport '443'
option dest 'lan'
option dest_ip '192.168.1.233'
list proto 'tcp'
option dest_port '443'
any help would be really appreciated