ok this is my understanding based on my experience:
this is a typical architecture usually we have
[[ pc (client) --- lan --- owrt ]] --- wan --- isp modem --- isp network --- other isp networks --- wan --- isp modem -- server router --- lan ...
using my previous tcpdump as example
# tcpdump -i eth1 -n -v 'host 8.8.8.8 and port 53'
tcpdump: listening on eth1, link-type EN10MB (Ethernet), capture size 262144 bytes
21:30:52.017370 IP (tos 0xb8, ttl 64, id 24059, offset 0, flags [DF], proto UDP (17), length 71)
x.x.x.x.53333 > 8.8.8.8.53: 13116+ A? www.elhorrindeclaudia.com. (43)
21:30:52.017427 IP (tos 0xb8, ttl 64, id 24060, offset 0, flags [DF], proto UDP (17), length 71)
x.x.x.x.53333 > 8.8.8.8.53: 16104+ AAAA? www.elhorrindeclaudia.com. (43)
21:30:52.064501 IP (tos 0x0, ttl 122, id 10850, offset 0, flags [none], proto UDP (17), length 119)
8.8.8.8.53 > x.x.x.x.53333: 13116 3/0/0 www.elhorrindeclaudia.com. A 172.67.71.33, www.elhorrindeclaudia.com. A 104.26.4.54, www.elhorrindeclaudia.com. A 104.26.5.54 (91)
21:30:52.083051 IP (tos 0x0, ttl 122, id 23645, offset 0, flags [none], proto UDP (17), length 155)
8.8.8.8.53 > x.x.x.x.53333: 16104 3/0/0 www.elhorrindeclaudia.com. AAAA 2606:4700:20
which means the followings:
- anything between [ ] is under you control (to some extent because obviously you cannot control for example the network stack actually implemented in your device NIC, you may have limited control over OS network stack etc). anything not in [ ] is not under your control. you cannot tell your ISP how to prioritize your traffic, you cannot tell the other ISPs who are providing the inter-connect chain towards your destination neither. and you cannot control how your destination process packets.
- as result of point 1) any prioritization makes only sense if you prioritize your outgoing traffic. that's all you can do. nothing more.
- as result of point 1) any incoming traffic is not under your control. in which order incoming packets are delivered is totally out of your control. (with a beauty spot you can tamper a little bit though, see later)
using the example above let's check what happens:
1st line tells that from my x.x.x.x (which is my public IP given be my ISP) assigned to my wan interface, so from the wan interface i am sending an outgoing udp packet to destination ip 8.8.8.8 and destination port 53. so my source ip is x.x.x.x, src port is 53333, and dst ip=8.8.8.8 and dst port=53. and i request A records (ipv4) from 8.8.8.8 (google.dns).
2nd line tells similar as 1st line but requesting AAAA records (ipv6)
3rd line tells that google.dns from src ip=8.8.8.8 and src port=53 answering to dst ip=my public ip and dst port=53333 with the requested A records.
4th line tells similar to 3rd line but with AAAA records.
now, back to point 2) - any prioritization tool qosify, sqm will mark outgoing traffic. so any config line in qosify such as
udp:53 voice
ip:x.x.x.x besteffort
dns:*googledrive* bulk
just means that any traffic from your lan to destination on wan with dst port=53 will be marked as voice (in my example TOS=0xb8=DSCP=0x22=EF). or any traffic from your lan to destination wan ip=x.x.x.x will be marked as besteffort. or any traffic to destination on wan to the resolved ips corresponding to a dns query including the specified phrase will be marked as bulk.
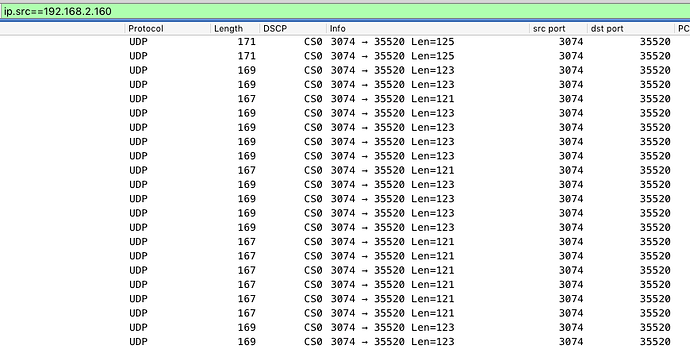
so specifying your local listening port 3074 in qosify does not make sense at all!
back to point 3) - as a beauty spot you can do ingress prioritization too which may, i emphasize again may help but thumb rule is: you cannot control in which order the remote end sends traffic to you.
qosify is great in handling this aspect in a very simple way: any traffic you send and classify as outgoing traffic according to a rule, for example via udp:53 voice rule then the reply traffic which is originating from wan from src port 53 will be automatically classified as voice. for example in my case traffic from 8.8.8.8:53 to x.x.x.x:53333 as reply traffic will be classified also [if someone uses option ingress 1] because i have an outgoing rule udp:53 voice.
another misconception regarding marking values: check https://man7.org/linux/man-pages/man8/tc-cake.8.html. diffserv4 defines 4 tins (=queues) called bulk, besteffort, video, voice assigning various set of DSCP values as the base of classification.
diffserv4
Provides a general-purpose Diffserv implementation with four
tins:
Bulk (CS1, LE in kernel v5.9+), 6.25% threshold,
generally low priority.
Best Effort (general), 100% threshold.
Video (AF4x, AF3x, CS3, AF2x, CS2, TOS4, TOS1), 50%
threshold.
Voice (CS7, CS6, EF, VA, CS5, CS4), 25% threshold.
this means a packet marked with CS7 or CS6 or EF or VA or CS5 or CS4, does not matter which but any of this set, will be processed in the voice tin. similarly, a packet marked with AF41 or AF32 or CS2 will be equally handled and processed in the video tin. so when you create your qosify class config i think it is better to pick distinguished values for each class belong to a tin. imho better to define only four classes and pick DSCP values accordingly. the best is to leave the default settings on, and just modify the rule set.
and lastly, i started this post as this is my experience for a reason. because something may work for me but not for you. i may have different preference, i want priority on different kind of traffic than you. i have different internet access than you with different bandwidth, different ISP rules, different load pattern than you. so any config you see here may not fit for your environment. so better to treat any "best config ever" with salt of grain.
and don't forget: you can prioritize a kind of traffic on a cost of other types will be slowed.
![]() After 4 minutes of watching the game just remembered why I don't play FPS.
After 4 minutes of watching the game just remembered why I don't play FPS. ![]()