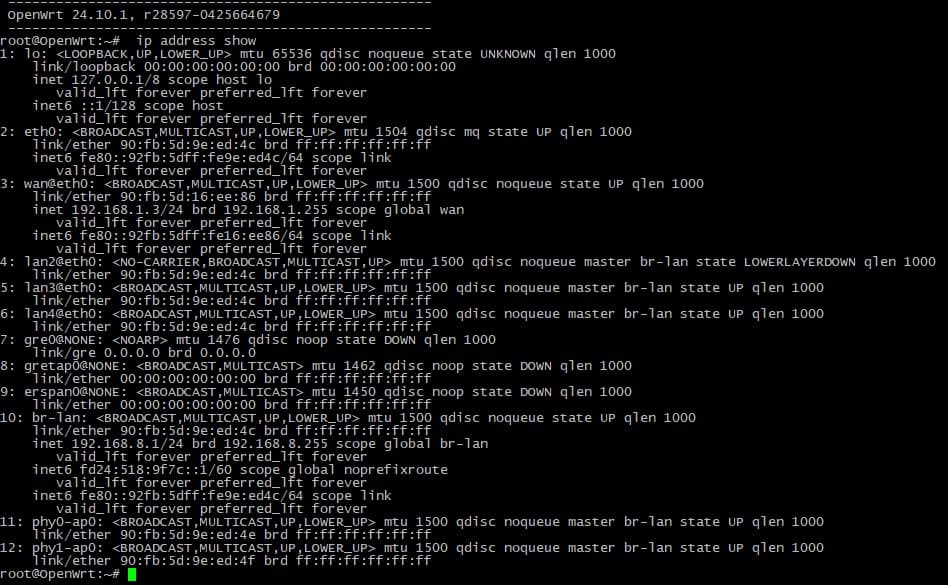
root@OpenWrt:~# ip address show
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1504 qdisc mq state UP qlen 1000
link/ether 90:fb:5d:9e:ed:4c brd ff:ff:ff:ff:ff:ff
inet6 fe80::92fb:5dff:fe9e:ed4c/64 scope link
valid_lft forever preferred_lft forever
3: wan@eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP qlen 1000
link/ether 90:fb:5d:16:ee:86 brd ff:ff:ff:ff:ff:ff
inet 192.168.1.3/24 brd 192.168.1.255 scope global wan
valid_lft forever preferred_lft forever
inet6 fe80::92fb:5dff:fe16:ee86/64 scope link
valid_lft forever preferred_lft forever
4: lan2@eth0: <NO-CARRIER,BROADCAST,MULTICAST,UP> mtu 1500 qdisc noqueue master br-lan state LOWERLAYERDOWN qlen 1000
link/ether 90:fb:5d:9e:ed:4c brd ff:ff:ff:ff:ff:ff
5: lan3@eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue master br-lan state UP qlen 1000
link/ether 90:fb:5d:9e:ed:4c brd ff:ff:ff:ff:ff:ff
6: lan4@eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue master br-lan state UP qlen 1000
link/ether 90:fb:5d:9e:ed:4c brd ff:ff:ff:ff:ff:ff
7: gre0@NONE: <NOARP> mtu 1476 qdisc noop state DOWN qlen 1000
link/gre 0.0.0.0 brd 0.0.0.0
8: gretap0@NONE: <BROADCAST,MULTICAST> mtu 1462 qdisc noop state DOWN qlen 1000
link/ether 00:00:00:00:00:00 brd ff:ff:ff:ff:ff:ff
9: erspan0@NONE: <BROADCAST,MULTICAST> mtu 1450 qdisc noop state DOWN qlen 1000
link/ether 00:00:00:00:00:00 brd ff:ff:ff:ff:ff:ff
10: br-lan: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP qlen 1000
link/ether 90:fb:5d:9e:ed:4c brd ff:ff:ff:ff:ff:ff
inet 192.168.8.1/24 brd 192.168.8.255 scope global br-lan
valid_lft forever preferred_lft forever
inet6 fd24:518:9f7c::1/60 scope global noprefixroute
valid_lft forever preferred_lft forever
inet6 fe80::92fb:5dff:fe9e:ed4c/64 scope link
valid_lft forever preferred_lft forever
11: phy0-ap0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue master br-lan state UP qlen 1000
link/ether 90:fb:5d:9e:ed:4e brd ff:ff:ff:ff:ff:ff
12: phy1-ap0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue master br-lan state UP qlen 1000
link/ether 90:fb:5d:9e:ed:4f brd ff:ff:ff:ff:ff:ff
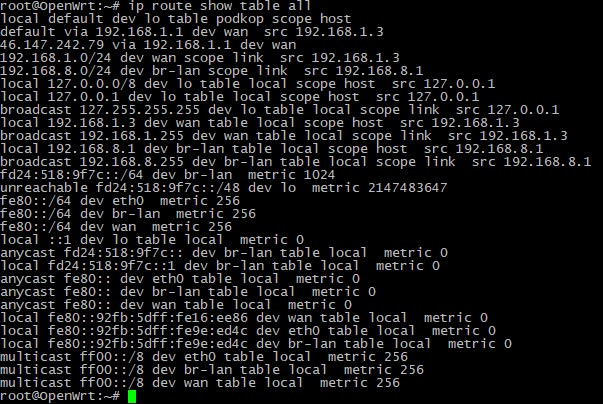
root@OpenWrt:~# ip route show table all
local default dev lo table podkop scope host
default via 192.168.1.1 dev wan src 192.168.1.3
46.147.242.79 via 192.168.1.1 dev wan
192.168.1.0/24 dev wan scope link src 192.168.1.3
192.168.8.0/24 dev br-lan scope link src 192.168.8.1
local 127.0.0.0/8 dev lo table local scope host src 127.0.0.1
local 127.0.0.1 dev lo table local scope host src 127.0.0.1
broadcast 127.255.255.255 dev lo table local scope link src 127.0.0.1
local 192.168.1.3 dev wan table local scope host src 192.168.1.3
broadcast 192.168.1.255 dev wan table local scope link src 192.168.1.3
local 192.168.8.1 dev br-lan table local scope host src 192.168.8.1
broadcast 192.168.8.255 dev br-lan table local scope link src 192.168.8.1
fd24:518:9f7c::/64 dev br-lan metric 1024
unreachable fd24:518:9f7c::/48 dev lo metric 2147483647
fe80::/64 dev eth0 metric 256
fe80::/64 dev br-lan metric 256
fe80::/64 dev wan metric 256
local ::1 dev lo table local metric 0
anycast fd24:518:9f7c:: dev br-lan table local metric 0
local fd24:518:9f7c::1 dev br-lan table local metric 0
anycast fe80:: dev eth0 table local metric 0
anycast fe80:: dev br-lan table local metric 0
anycast fe80:: dev wan table local metric 0
local fe80::92fb:5dff:fe16:ee86 dev wan table local metric 0
local fe80::92fb:5dff:fe9e:ed4c dev eth0 table local metric 0
local fe80::92fb:5dff:fe9e:ed4c dev br-lan table local metric 0
multicast ff00::/8 dev eth0 table local metric 256
multicast ff00::/8 dev br-lan table local metric 256
multicast ff00::/8 dev wan table local metric 256
root@OpenWrt:~# ip rule show
0: from all lookup local
105: from all fwmark 0x105 lookup podkop
32766: from all lookup main
32767: from all lookup default
root@OpenWrt:~# ip -6 rule show
0: from all lookup local
32766: from all lookup main
root@OpenWrt:~# nft list ruleset
table inet fw4 {
ct helper amanda {
type "amanda" protocol udp
l3proto inet
}
ct helper RAS {
type "RAS" protocol udp
l3proto inet
}
ct helper Q.931 {
type "Q.931" protocol tcp
l3proto inet
}
ct helper irc {
type "irc" protocol tcp
l3proto ip
}
ct helper netbios-ns {
type "netbios-ns" protocol udp
l3proto ip
}
ct helper pptp {
type "pptp" protocol tcp
l3proto ip
}
ct helper sane {
type "sane" protocol tcp
l3proto inet
}
ct helper sip {
type "sip" protocol udp
l3proto inet
}
ct helper snmp {
type "snmp" protocol udp
l3proto ip
}
ct helper tftp {
type "tftp" protocol udp
l3proto inet
}
chain input {
type filter hook input priority filter; policy drop;
iif "lo" accept comment "!fw4: Accept traffic from loopback"
ct state vmap { established : accept, related : accept } comment "!fw4: Handle inbound flows"
tcp flags & (fin | syn | rst | ack) == syn jump syn_flood comment "!fw4: Rate limit TCP syn packets"
iifname "br-lan" jump input_lan comment "!fw4: Handle lan IPv4/IPv6 input traffic"
iifname "wan" jump input_wan comment "!fw4: Handle wan IPv4/IPv6 input traffic"
jump handle_reject
}
chain forward {
type filter hook forward priority filter; policy drop;
ct state vmap { established : accept, related : accept } comment "!fw4: Handle forwarded flows"
iifname "br-lan" jump forward_lan comment "!fw4: Handle lan IPv4/IPv6 forward traffic"
iifname "wan" jump forward_wan comment "!fw4: Handle wan IPv4/IPv6 forward traffic"
jump handle_reject
}
chain output {
type filter hook output priority filter; policy accept;
oif "lo" accept comment "!fw4: Accept traffic towards loopback"
ct state vmap { established : accept, related : accept } comment "!fw4: Handle outbound flows"
oifname "br-lan" jump output_lan comment "!fw4: Handle lan IPv4/IPv6 output traffic"
oifname "wan" jump output_wan comment "!fw4: Handle wan IPv4/IPv6 output traffic"
}
chain prerouting {
type filter hook prerouting priority filter; policy accept;
iifname "br-lan" jump helper_lan comment "!fw4: Handle lan IPv4/IPv6 helper assignment"
}
chain handle_reject {
meta l4proto tcp reject with tcp reset comment "!fw4: Reject TCP traffic"
reject comment "!fw4: Reject any other traffic"
}
chain syn_flood {
limit rate 25/second burst 50 packets return comment "!fw4: Accept SYN packets below rate-limit"
drop comment "!fw4: Drop excess packets"
}
chain input_lan {
jump accept_from_lan
}
chain output_lan {
jump accept_to_lan
}
chain forward_lan {
jump accept_to_wan comment "!fw4: Accept lan to wan forwarding"
jump accept_to_lan
}
chain helper_lan {
udp dport 10080 ct helper set "amanda" comment "!fw4: Amanda backup and archiving proto"
udp dport 1719 ct helper set "RAS" comment "!fw4: RAS proto tracking"
tcp dport 1720 ct helper set "Q.931" comment "!fw4: Q.931 proto tracking"
meta nfproto ipv4 tcp dport 6667 ct helper set "irc" comment "!fw4: IRC DCC connection tracking"
meta nfproto ipv4 udp dport 137 ct helper set "netbios-ns" comment "!fw4: NetBIOS name service broadcast tracking"
meta nfproto ipv4 tcp dport 1723 ct helper set "pptp" comment "!fw4: PPTP VPN connection tracking"
tcp dport 6566 ct helper set "sane" comment "!fw4: SANE scanner connection tracking"
udp dport 5060 ct helper set "sip" comment "!fw4: SIP VoIP connection tracking"
meta nfproto ipv4 udp dport 161 ct helper set "snmp" comment "!fw4: SNMP monitoring connection tracking"
udp dport 69 ct helper set "tftp" comment "!fw4: TFTP connection tracking"
}
chain accept_from_lan {
iifname "br-lan" counter packets 152551 bytes 22437072 accept comment "!fw4: accept lan IPv4/IPv6 traffic"
}
chain accept_to_lan {
oifname "br-lan" counter packets 29608 bytes 5202728 accept comment "!fw4: accept lan IPv4/IPv6 traffic"
}
chain input_wan {
meta nfproto ipv4 udp dport 68 counter packets 0 bytes 0 accept comment "!fw4: Allow-DHCP-Renew"
icmp type echo-request counter packets 0 bytes 0 accept comment "!fw4: Allow-Ping"
meta nfproto ipv4 meta l4proto igmp counter packets 783 bytes 28188 accept comment "!fw4: Allow-IGMP"
meta nfproto ipv6 udp dport 546 counter packets 0 bytes 0 accept comment "!fw4: Allow-DHCPv6"
ip6 saddr fe80::/10 icmpv6 type . icmpv6 code { mld-listener-query . 0, mld-listener-report . 0, mld-listener-done . 0, mld2-listener-report . 0 } counter packets 0 bytes 0 accept comment "!fw4: Allow-MLD"
icmpv6 type { destination-unreachable, time-exceeded, echo-request, echo-reply, nd-router-solicit, nd-router-advert } limit rate 1000/second burst 5 packets counter packets 3 bytes 152 accept comment "!fw4: Allow-ICMPv6-Input"
icmpv6 type . icmpv6 code { packet-too-big . 0, parameter-problem . 0, nd-neighbor-solicit . 0, nd-neighbor-advert . 0, parameter-problem . 1 } limit rate 1000/second burst 5 packets counter packets 0 bytes 0 accept comment "!fw4: Allow-ICMPv6-Input"
jump reject_from_wan
}
chain output_wan {
jump accept_to_wan
}
chain forward_wan {
icmpv6 type { destination-unreachable, time-exceeded, echo-request, echo-reply } limit rate 1000/second burst 5 packets counter packets 0 bytes 0 accept comment "!fw4: Allow-ICMPv6-Forward"
icmpv6 type . icmpv6 code { packet-too-big . 0, parameter-problem . 0, parameter-problem . 1 } limit rate 1000/second burst 5 packets counter packets 0 bytes 0 accept comment "!fw4: Allow-ICMPv6-Forward"
meta l4proto esp counter packets 0 bytes 0 jump accept_to_lan comment "!fw4: Allow-IPSec-ESP"
udp dport 500 counter packets 0 bytes 0 jump accept_to_lan comment "!fw4: Allow-ISAKMP"
jump reject_to_wan
}
chain accept_to_wan {
meta nfproto ipv4 oifname "wan" ct state invalid counter packets 1063 bytes 51509 drop comment "!fw4: Prevent NAT leakage"
oifname "wan" counter packets 460681 bytes 34195447 accept comment "!fw4: accept wan IPv4/IPv6 traffic"
}
chain reject_from_wan {
iifname "wan" counter packets 431 bytes 69131 jump handle_reject comment "!fw4: reject wan IPv4/IPv6 traffic"
}
chain reject_to_wan {
oifname "wan" counter packets 0 bytes 0 jump handle_reject comment "!fw4: reject wan IPv4/IPv6 traffic"
}
chain dstnat {
type nat hook prerouting priority dstnat; policy accept;
}
chain srcnat {
type nat hook postrouting priority srcnat; policy accept;
oifname "wan" jump srcnat_wan comment "!fw4: Handle wan IPv4/IPv6 srcnat traffic"
}
chain srcnat_wan {
meta nfproto ipv4 masquerade comment "!fw4: Masquerade IPv4 wan traffic"
}
chain raw_prerouting {
type filter hook prerouting priority raw; policy accept;
}
chain raw_output {
type filter hook output priority raw; policy accept;
}
chain mangle_prerouting {
type filter hook prerouting priority mangle; policy accept;
}
chain mangle_postrouting {
type filter hook postrouting priority mangle; policy accept;
oifname "wan" tcp flags & (fin | syn | rst) == syn tcp option maxseg size set rt mtu comment "!fw4: Zone wan IPv4/IPv6 egress MTU fixing"
}
chain mangle_input {
type filter hook input priority mangle; policy accept;
}
chain mangle_output {
type route hook output priority mangle; policy accept;
}
chain mangle_forward {
type filter hook forward priority mangle; policy accept;
iifname "wan" tcp flags & (fin | syn | rst) == syn tcp option maxseg size set rt mtu comment "!fw4: Zone wan IPv4/IPv6 ingress MTU fixing"
}
}
table inet PodkopTable {
set podkop_subnets {
type ipv4_addr
flags interval
auto-merge
}
chain mangle {
type filter hook prerouting priority mangle; policy accept;
iifname "br-lan" ip daddr @podkop_subnets meta l4proto tcp meta mark set 0x00000105 counter packets 0 bytes 0
iifname "br-lan" ip daddr @podkop_subnets meta l4proto udp meta mark set 0x00000105 counter packets 0 bytes 0
iifname "br-lan" ip daddr 198.18.0.0/15 meta l4proto tcp meta mark set 0x00000105 counter packets 20302 bytes 5232935
iifname "br-lan" ip daddr 198.18.0.0/15 meta l4proto udp meta mark set 0x00000105 counter packets 104602 bytes 23792217
}
chain proxy {
type filter hook prerouting priority dstnat; policy accept;
meta mark 0x00000105 meta l4proto tcp tproxy ip to :1602 counter packets 20302 bytes 5232935
meta mark 0x00000105 meta l4proto udp tproxy ip to :1602 counter packets 104602 bytes 23792217
}
}