Thanks @psherman ,
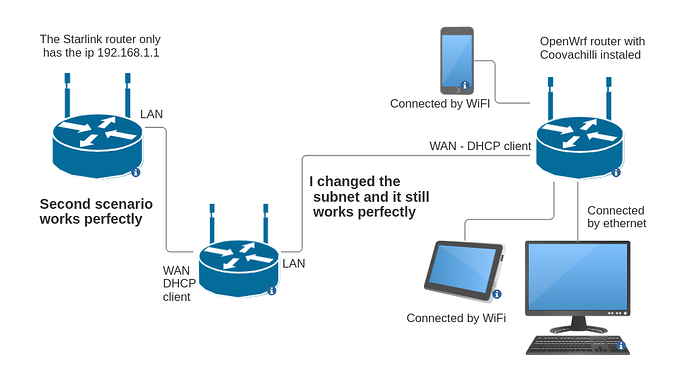
In the second scenario I have tried several subnets and they have all worked perfectly. I think that's not the problem, but I'm not sure.
I tryed with various Openwrt versions, 19, 21 and 22 without success.
ubus call system board
{
"kernel": "5.10.201",
"hostname": "e-Nuup",
"system": "MediaTek MT7621 ver:1 eco:3",
"model": "Linksys E5600",
"board_name": "linksys,e5600",
"rootfs_type": "squashfs",
"release": {
"distribution": "OpenWrt",
"version": "22.03.6",
"revision": "r20265-f85a79bcb4",
"target": "ramips/mt7621",
"description": "OpenWrt 22.03.6 r20265-f85a79bcb4"
}
}
cat /etc/config/network
(I use the nuup interface for router admin with a luci mod)
config interface 'loopback'
option device 'lo'
option proto 'static'
option ipaddr '127.0.0.1'
option netmask '255.0.0.0'
config globals 'globals'
option ula_prefix 'fd46:d325:2dd4::/48'
option packet_steering '1'
config device
option name 'br-lan'
option type 'bridge'
list ports 'lan1'
list ports 'lan2'
list ports 'lan3'
list ports 'lan4'
config device
option name 'lan1'
config device
option name 'lan2'
config device
option name 'lan3'
config device
option name 'lan4'
config interface 'lan'
option device 'br-lan'
option proto 'static'
option ipaddr '11.1.0.1'
option netmask '255.255.255.0'
option ip6assign '60'
config device
option name 'wan'
config interface 'wan'
option device 'wan'
option dns '8.8.8.8'
option proto 'static'
option ipaddr '192.168.99.50'
option gateway '192.168.99.1'
option netmask '255.255.255.0'
config interface 'wan6'
option device 'wan'
option proto 'dhcpv6'
config device 'nuup_dev'
option type 'bridge'
option name 'br-nuup'
config interface 'nuup'
option proto 'static'
option device 'br-nuup'
option ipaddr '10.5.0.1'
option netmask '255.255.255.0'
cat /etc/config/wireless
config wifi-device 'radio0'
option type 'mac80211'
option path '1e140000.pcie/pci0000:00/0000:00:00.0/0000:01:00.0'
option band '2g'
option htmode 'HT20'
option country 'CO'
option txpower '20'
option cell_density '1'
option disabled '0'
option channel '11'
config wifi-iface 'default_radio0'
option device 'radio0'
option network 'lan'
option mode 'ap'
option encryption 'none'
option hidden '0'
option ssid 'Compra_WiFi_Remote'
config wifi-device 'radio1'
option type 'mac80211'
option path '1e140000.pcie/pci0000:00/0000:00:01.0/0000:02:00.0'
option channel '36'
option band '5g'
option htmode 'VHT80'
option disabled '1'
config wifi-iface 'default_radio1'
option device 'radio1'
option network 'lan'
option mode 'ap'
option ssid 'OpenWrt'
option encryption 'none'
config wifi-iface 'nuup'
option device 'radio0'
option mode 'ap'
option network 'nuup'
option ssid 'xxxxx'
option encryption 'psk2'
option key 'xxxxxxxxxx'
cat /etc/config/dhcp
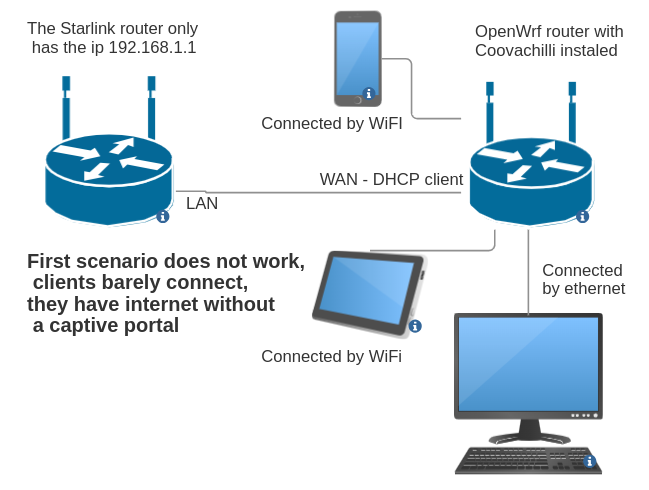
(I tryed with DHCP client without success, now I have a WAN static IP )
config dnsmasq
option domainneeded '1'
option boguspriv '1'
option filterwin2k '0'
option localise_queries '1'
option rebind_protection '1'
option rebind_localhost '1'
option local '/lan/'
option domain 'lan'
option expandhosts '1'
option nonegcache '0'
option cachesize '1000'
option authoritative '1'
option readethers '1'
option leasefile '/tmp/dhcp.leases'
option resolvfile '/tmp/resolv.conf.d/resolv.conf.auto'
option nonwildcard '1'
option localservice '1'
option ednspacket_max '1232'
option filter_aaaa '0'
option filter_a '0'
config dhcp 'lan'
option interface 'lan'
option start '10'
option limit '250'
option leasetime '8h'
option dhcpv4 'server'
option dhcpv6 'server'
option ra 'server'
option ra_slaac '1'
list ra_flags 'managed-config'
list ra_flags 'other-config'
config dhcp 'wan'
option interface 'wan'
option ignore '1'
config odhcpd 'odhcpd'
option maindhcp '0'
option leasefile '/tmp/hosts/odhcpd'
option leasetrigger '/usr/sbin/odhcpd-update'
option loglevel '4'
config dhcp 'nuup'
option interface 'nuup'
option start '100'
option limit '150'
option leasetime '3h'
option netmask '255.255.255.0'
cat /etc/config/firewall
( I have open all WAN traffic for admin and tests but I changed without success)
config defaults
option syn_flood 1
option input ACCEPT
option output ACCEPT
option forward ACCEPT
# Uncomment this line to disable ipv6 rules
# option disable_ipv6 1
config zone
option name lan
list network 'lan'
option input ACCEPT
option output ACCEPT
option forward ACCEPT
config zone
option name wan
list network 'wan'
list network 'wan6'
option input ACCEPT
option output ACCEPT
option forward ACCEPT
option masq 1
option mtu_fix 1
config forwarding
option src lan
option dest wan
# We need to accept udp packets on port 68,
# see https://dev.openwrt.org/ticket/4108
config rule
option name Allow-DHCP-Renew
option src wan
option proto udp
option dest_port 68
option target ACCEPT
option family ipv4
# Allow IPv4 ping
config rule
option name Allow-Ping
option src wan
option proto icmp
option icmp_type echo-request
option family ipv4
option target ACCEPT
config rule
option name Allow-IGMP
option src wan
option proto igmp
option family ipv4
option target ACCEPT
# Allow DHCPv6 replies
# see https://github.com/openwrt/openwrt/issues/5066
config rule
option name Allow-DHCPv6
option src wan
option proto udp
option dest_port 546
option family ipv6
option target ACCEPT
config rule
option name Allow-MLD
option src wan
option proto icmp
option src_ip fe80::/10
list icmp_type '130/0'
list icmp_type '131/0'
list icmp_type '132/0'
list icmp_type '143/0'
option family ipv6
option target ACCEPT
# Allow essential incoming IPv6 ICMP traffic
config rule
option name Allow-ICMPv6-Input
option src wan
option proto icmp
list icmp_type echo-request
list icmp_type echo-reply
list icmp_type destination-unreachable
list icmp_type packet-too-big
list icmp_type time-exceeded
list icmp_type bad-header
list icmp_type unknown-header-type
list icmp_type router-solicitation
list icmp_type neighbour-solicitation
list icmp_type router-advertisement
list icmp_type neighbour-advertisement
option limit 1000/sec
option family ipv6
option target ACCEPT
# Allow essential forwarded IPv6 ICMP traffic
config rule
option name Allow-ICMPv6-Forward
option src wan
option dest *
option proto icmp
list icmp_type echo-request
list icmp_type echo-reply
list icmp_type destination-unreachable
list icmp_type packet-too-big
list icmp_type time-exceeded
list icmp_type bad-header
list icmp_type unknown-header-type
option limit 1000/sec
option family ipv6
option target ACCEPT
config rule
option name Allow-IPSec-ESP
option src wan
option dest lan
option proto esp
option target ACCEPT
config rule
option name Allow-ISAKMP
option src wan
option dest lan
option dest_port 500
option proto udp
option target ACCEPT
# allow interoperability with traceroute classic
# note that traceroute uses a fixed port range, and depends on getting
# back ICMP Unreachables. if we're operating in DROP mode, it won't
# work so we explicitly REJECT packets on these ports.
config rule
option name Support-UDP-Traceroute
option src wan
option dest_port 33434:33689
option proto udp
option family ipv4
option target REJECT
option enabled false
# include a file with users custom iptables rules
config include
option path /etc/firewall.user
### EXAMPLE CONFIG SECTIONS
# do not allow a specific ip to access wan
#config rule
# option src lan
# option src_ip 192.168.45.2
# option dest wan
# option proto tcp
# option target REJECT
# block a specific mac on wan