I have an recursive caching DNS server on my LAN used by my Openwrt as it's DNS server. My LAN clients all point to my Openwrt dnsmasq as their DNS server.
To prevent rogue DNS queries from android devices, I have some iptables rules setup to DNAT all outgoing DNS queries not coming from my DNS server to the Openwrt's LAN interface. They're clearly working as you can see from the packet counters below.
Chain PREROUTING (policy ACCEPT 615K packets, 77M bytes)
pkts bytes target prot opt in out source destination
632K 78M prerouting_rule all -- * * 0.0.0.0/0 0.0.0.0/0 /* !fw3: Custom prerouting rule chain */
Chain prerouting_rule (1 references)
pkts bytes target prot opt in out source destination
10704 642K RETURN tcp -- br-lan * <mydnsserver> 0.0.0.0/0 tcp dpt:53
249K 23M RETURN udp -- br-lan * <mydnsserver> 0.0.0.0/0 udp dpt:53
16943 1135K DNAT udp -- br-lan * 0.0.0.0/0 !<openwrt> udp dpt:53 to:<openwrt>:53
0 0 DNAT tcp -- br-lan * 0.0.0.0/0 !<openwrt> tcp dpt:53 to:<openwrt>:53
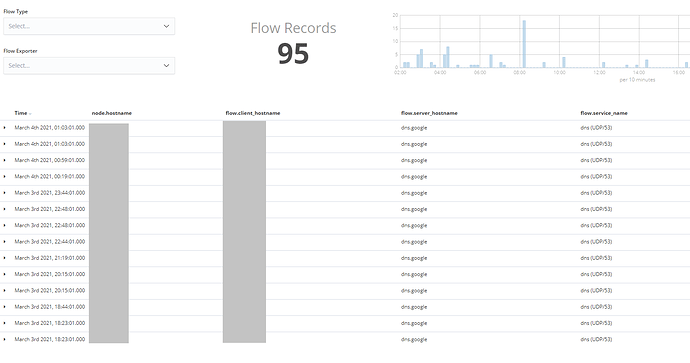
I also have softflowd running on Openwrt and uploading everything to an ELK stack, where I use a Kibana dashboard known as Elastiflow to visualize the data.
The softflow daemon hangs off the br-lan interface, not the wan interface, so that proper source and destination addresses show up in the netflow records, otherwise it just shows the firewall WAN IP, which isn't very helpful when trying to identify which clients are doing what.
Looking at the netflow data, it shows flow records for outgoing dns queries from multiple LAN clients to Google DNS servers, among others, which theoretically should not be possible with the above iptables rules in place.
Is it safe to assume that this is precisely because the softflow daemon is hanging off the br-lan device and seeing the packets before their IP address is NAT'ed and thus reporting the flow as being between the client and Google when in reality it's actually between the client and my Openwrt due to the DNAT rules?