just trying to understand how pbr manages default gateways.
this is my setup:
I have two different vpn interfaces a wireguard interface which is the default gateway. every device on the network ]goes through wireguard interface.
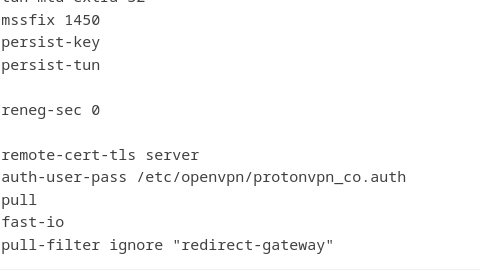
an ovpn interface connected to another vpn
I have installed pbr and added two rules one to go through wan... no vpn at all.. (it is a nas and it only connects to the internet when i need to download files from an external sftp server to have max bandwith. )
my question is as follows..
if i configure a device to use the ovpn interface.. will it also go through the wireguard interface which is the default gateway? so i will have double vpn for that device?
device > ovpn network > wireguard network > internet?
should i set the wan as default gateway but then how do i configure pbr to route all the devices on the network via wireguard except the ones i need to route without vpn or through the ovpn interface?
this is my pbr config:
root@OpenWrt:~# cat /etc/config/pbr
config pbr 'config'
option verbosity '2'
option strict_enforcement '1'
option resolver_set 'none'
option ipv6_enabled '0'
list ignored_interface 'vpnserver'
list ignored_interface 'wgserver'
option boot_timeout '30'
option rule_create_option 'add'
option procd_reload_delay '1'
option webui_show_ignore_target '0'
list webui_supported_protocol 'all'
list webui_supported_protocol 'tcp'
list webui_supported_protocol 'udp'
list webui_supported_protocol 'tcp udp'
list webui_supported_protocol 'icmp'
option enabled '1'
config include
option path '/usr/share/pbr/pbr.user.aws'
option enabled '0'
config include
option path '/usr/share/pbr/pbr.user.netflix'
option enabled '0'
config policy
option name 'Plex/Emby Local Server'
option interface 'wan'
option src_port '8096 8920 32400'
option enabled '0'
config policy
option name 'Plex/Emby Remote Servers'
option interface 'wan'
option dest_addr 'plex.tv my.plexapp.com emby.media app.emby.media tv.emby.media'
option enabled '0'
config policy
option interface 'wan'
option name 'synology'
option src_addr '192.168.1.12'
config policy
option name 'test co '
option src_addr '192.168.1.185'
option interface 'ovpn'
root@OpenWrt:~# /etc/init.d/pbr status
============================================================
pbr - environment
pbr 1.0.1-16 running on OpenWrt 22.03.2. WAN (IPv4): wan/wan.1081/85.10.107.254.
============================================================
Dnsmasq version 2.86 Copyright (c) 2000-2021 Simon Kelley
Compile time options: IPv6 GNU-getopt no-DBus UBus no-i18n no-IDN DHCP no-DHCPv6 no-Lua TFTP no-conntrack no-ipset no-auth no-cryptohash no-DNSSEC no-ID loop-detect inotify dumpfile
============================================================
pbr chains - policies
chain pbr_forward {
}
chain pbr_input {
}
chain pbr_output {
}
chain pbr_prerouting {
ip saddr @pbr_wan_4_src_ip_cfg066ff5 goto pbr_mark_0x010000 comment "synology"
ip saddr @pbr_ovpn_4_src_ip_cfg076ff5 goto pbr_mark_0x030000 comment "test co "
}
chain pbr_postrouting {
}
============================================================
pbr chains - marking
chain pbr_mark_0x010000 {
counter packets 5 bytes 364 meta mark set meta mark & 0xff01ffff | 0x00010000
return
}
chain pbr_mark_0x020000 {
counter packets 0 bytes 0 meta mark set meta mark & 0xff02ffff | 0x00020000
return
}
chain pbr_mark_0x030000 {
counter packets 1049 bytes 117931 meta mark set meta mark & 0xff03ffff | 0x00030000
return
}
============================================================
pbr nft sets
set pbr_wan_4_src_ip_cfg066ff5 {
type ipv4_addr
flags interval
auto-merge
comment "synology"
elements = { 192.168.1.12 }
}
set pbr_ovpn_4_src_ip_cfg076ff5 {
type ipv4_addr
flags interval
auto-merge
comment "test co "
elements = { 192.168.1.185 }
}
============================================================
IPv4 table 256 route: default via x.x.x.x dev wan.1081
IPv4 table 256 rule(s):
30000: from all fwmark 0x10000/0xff0000 lookup pbr_wan
IPv4 table 257 route: default via 10.x.x.x dev wg0
IPv4 table 257 rule(s):
30001: from all fwmark 0x20000/0xff0000 lookup pbr_wg0
IPv4 table 258 route: default via 10.x.x.x dev tun0
IPv4 table 258 rule(s):
30002: from all fwmark 0x30000/0xff0000 lookup pbr_ovpn
root@OpenWrt:~# cat /etc/config/network
config interface 'loopback'
option device 'lo'
option proto 'static'
option ipaddr '127.0.0.1'
option netmask '255.0.0.0'
config globals 'globals'
config device
option name 'br-lan'
option type 'bridge'
list ports 'lan1'
list ports 'lan2'
list ports 'lan3'
list ports 'lan4'
config interface 'lan'
option device 'br-lan'
option proto 'static'
option ip6assign '60'
list ipaddr '192.168.1.254/24'
option ipv6 '0'
option delegate '0'
config device
option name 'wan'
option macaddr '62:38:e0:c5:36:18'
config interface 'wan'
option proto 'dhcp'
option ipv6 '0'
option device 'wan.1081'
option metric '20'
config interface 'wan6'
option proto 'dhcpv6'
option device 'wan.1081'
option reqaddress 'try'
option reqprefix 'auto'
config device
option type '8021q'
option ifname 'wan'
option vid '1081'
option name 'wan.1081'
config interface 'wg0'
option proto 'wireguard'
option private_key 'x.x.x.x'
list addresses '10..x.x.x/32'
option peerdns '0'
list dns '10.2.0.1'
option metric '10'
config wireguard_wg0
option description 'US-NJ#9'
option public_key 'xxxxxxxxxxxxxx'
list allowed_ips '0.0.0.0/0'
option route_allowed_ips '1'
option endpoint_host '69.x.x.x'
option endpoint_port '51820'
config interface 'ovpn'
option proto 'none'
option device 'tun
root@OpenWrt:~# ubus -S call luci.pbr getInterfaces '{"name": "pbr" }'
{"pbr":{"interfaces":["wan","wg0","ovpn"]}}
root@OpenWrt:~# service pbr start
Activating traffic killswitch [✓]
Setting up routing for 'wan/wan.1081/x.x.x.x' [✓]
Setting up routing for 'wg0/a.b.c.d' [✓]
Setting up routing for 'ovpn/tun0/y.y.y.y' [✓]
Routing 'synology' via wan [✓]
Routing 'test co ' via ovpn [✓]
Deactivating traffic killswitch [✓]
pbr 1.0.1-16 monitoring interfaces: wan wg0 ovpn
pbr 1.0.1-16 (nft) started with gateways:
wan/wan.1081/x.x.x.x
wg0/a.b.c.d [✓]
ovpn/tun0/y.y.y.y