Where I am right now is trying to figure out why traffic isn't making it out of the IPSEC / StrongSwan server:
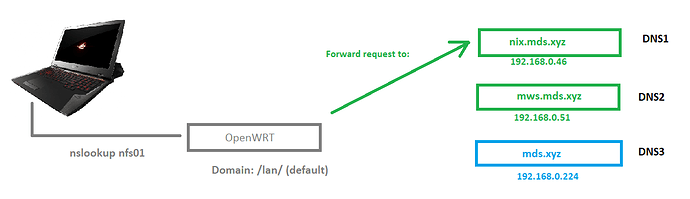
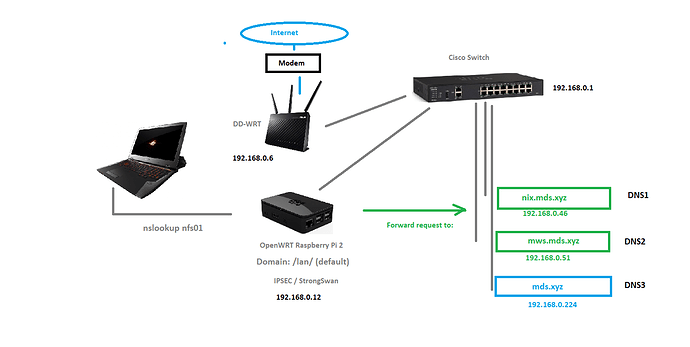
Referencing updated topology:
What I'm getting off the Raspberry PI 2:
Aug 9 17:03:57 OWRT01 : 13[IKE] giving up after 5 retransmits
Aug 9 17:03:57 OWRT01 : 13[IKE] peer not responding, trying again (2/3)
Aug 9 17:03:57 OWRT01 : 13[IKE] initiating IKE_SA AZURE[1] to 123.123.123.123
Aug 9 17:03:57 OWRT01 : 13[ENC] generating IKE_SA_INIT request 0 [ SA KE No N(NATD_S_IP) N(NATD_D_IP) N(FRAG_SUP) N(HASH_ALG) N(REDIR_SUP) ]
Aug 9 17:03:57 OWRT01 : 13[NET] sending packet: from 100.100.100.100[500] to 123.123.123.123[500] (1188 bytes)
Aug 9 17:03:57 OWRT01 : 04[NET] error writing to socket: Network unreachable
Aug 9 17:04:01 OWRT01 : 12[IKE] retransmit 1 of request with message ID 0
Aug 9 17:04:01 OWRT01 : 12[NET] sending packet: from 100.100.100.100[500] to 123.123.123.123[500] (1188 bytes)
Aug 9 17:04:01 OWRT01 : 04[NET] error writing to socket: Network unreachable
Aug 9 17:04:04 OWRT01 : 00[DMN] signal of type SIGINT received. Shutting down
Aug 9 17:04:04 OWRT01 : 00[IKE] destroying IKE_SA in state CONNECTING without notification
Aug 9 17:04:04 OWRT01 : 00[DMN] Starting IKE charon daemon (strongSwan 5.8.2, Linux 4.14.180, armv7l)
Aug 9 17:04:06 OWRT01 : 00[LIB] curl SSL backend 'mbedTLS/2.16.6' not supported, https:// disabled
Aug 9 17:04:06 OWRT01 : 00[CFG] disabling load-tester plugin, not configured
Aug 9 17:04:06 OWRT01 : 00[LIB] plugin 'load-tester': failed to load - load_tester_plugin_create returned NULL
Aug 9 17:04:06 OWRT01 : 00[LIB] created TUN device: ipsec0
Aug 9 17:04:06 OWRT01 : 00[LIB] plugin 'uci' failed to load: Error relocating /usr/lib/ipsec/plugins/libstrongswan-uci.so: uci_lookup: symbol not found
Aug 9 17:04:06 OWRT01 : 00[CFG] attr-sql plugin: database URI not set
Aug 9 17:04:06 OWRT01 : 00[NET] using forecast interface br-lan
Aug 9 17:04:06 OWRT01 : 00[CFG] joining forecast multicast groups: 224.0.0.1,224.0.0.22,224.0.0.251,224.0.0.252,239.255.255.250
Aug 9 17:04:06 OWRT01 : 00[CFG] loading ca certificates from '/etc/ipsec.d/cacerts'
Aug 9 17:04:06 OWRT01 : 00[CFG] loading aa certificates from '/etc/ipsec.d/aacerts'
Aug 9 17:04:06 OWRT01 : 00[CFG] loading ocsp signer certificates from '/etc/ipsec.d/ocspcerts'
Aug 9 17:04:06 OWRT01 : 00[CFG] loading attribute certificates from '/etc/ipsec.d/acerts'
Aug 9 17:04:06 OWRT01 : 00[CFG] loading crls from '/etc/ipsec.d/crls'
Aug 9 17:04:06 OWRT01 : 00[CFG] loading secrets from '/etc/ipsec.secrets'
Aug 9 17:04:06 OWRT01 : 00[CFG] loaded IKE secret for 100.100.100.100 123.123.123.123
Aug 9 17:04:06 OWRT01 : 00[CFG] sql plugin: database URI not set
Aug 9 17:04:06 OWRT01 : 00[CFG] loaded 0 RADIUS server configurations
Aug 9 17:04:06 OWRT01 : 00[CFG] HA config misses local/remote address
Aug 9 17:04:06 OWRT01 : 00[CFG] coupling file path unspecified
Aug 9 17:04:06 OWRT01 : 00[LIB] loaded plugins: charon test-vectors ldap pkcs11 aes des blowfish rc2 sha2 sha1 md4 md5 random nonce x509 revocation constraints pubkey pkcs1 pkcs7 pkcs8 pkcs12 pgp dnskey sshkey pem openssl gcrypt af-alg fips-prf gmp gmpdh curve25519 agent xcbc cmac hmac ctr ccm gcm curl mysql sqlite attr kernel-libipsec kernel-netlink resolve socket-default socket-dynamic connmark forecast farp stroke vici smp updown eap-identity eap-md5 eap-mschapv2 eap-radius eap-tls xauth-generic xauth-eap dhcp whitelist led duplicheck addrblock unity
Aug 9 17:04:06 OWRT01 : 00[JOB] spawning 16 worker threads
Aug 9 17:04:06 OWRT01 : 13[CFG] received stroke: add connection 'AZURE'
Aug 9 17:04:06 OWRT01 : 13[CFG] left nor right host is our side, assuming left=local
Aug 9 17:04:06 OWRT01 : 13[CFG] added configuration 'AZURE'
Aug 9 17:04:06 OWRT01 : 14[CFG] received stroke: initiate 'AZURE'
Aug 9 17:04:06 OWRT01 : 14[IKE] initiating IKE_SA AZURE[1] to 123.123.123.123
Aug 9 17:04:06 OWRT01 : 14[ENC] generating IKE_SA_INIT request 0 [ SA KE No N(NATD_S_IP) N(NATD_D_IP) N(FRAG_SUP) N(HASH_ALG) N(REDIR_SUP) ]
Aug 9 17:04:06 OWRT01 : 14[NET] sending packet: from 100.100.100.100[500] to 123.123.123.123[500] (1188 bytes)
Aug 9 17:04:06 OWRT01 : 04[NET] error writing to socket: Network unreachable
Aug 9 17:04:10 OWRT01 : 14[IKE] retransmit 1 of request with message ID 0
Aug 9 17:04:10 OWRT01 : 14[NET] sending packet: from 100.100.100.100[500] to 123.123.123.123[500] (1188 bytes)
Aug 9 17:04:10 OWRT01 : 04[NET] error writing to socket: Network unreachable
Aug 9 17:04:17 OWRT01 : 09[IKE] retransmit 2 of request with message ID 0
Aug 9 17:04:17 OWRT01 : 09[NET] sending packet: from 100.100.100.100[500] to 123.123.123.123[500] (1188 bytes)
Aug 9 17:04:17 OWRT01 : 04[NET] error writing to socket: Network unreachable
I don't have a WAN on this RB Pi 2. Just a single LAN. On the Asus AC68U, I don't see any packets leaving or coming to/from Azure VPN Gateway IP 123.123.123.123 when IPSEC on the OpenWRT is attempting a connection out to the AZ VPN GW:
root@DD-WRT-INTERNET-ASUS:~# tcpdump -n dst 123.123.123,123 or src 123,123,123,123
tcpdump: verbose output suppressed, use -v or -vv for full protocol decode
listening on eth0, link-type EN10MB (Ethernet), capture size 262144 bytes
root@DD-WRT-INTERNET-ASUS:~#
However, when I ping from the OpenWRT Raspberry PI 2 out to 123.123.123.123, I see the following off the DD-WRT:
root@DD-WRT-INTERNET-ASUS:~# tcpdump -n dst 123.123.123.123 or src 123.123.123.123
tcpdump: verbose output suppressed, use -v or -vv for full protocol decode
listening on eth0, link-type EN10MB (Ethernet), capture size 262144 bytes
17:03:31.877610 IP 192.168.0.12 > 123.123.123.123: ICMP echo request, id 62475, seq 0, length 64
17:03:32.877899 IP 192.168.0.12 > 123.123.123.123: ICMP echo request, id 62475, seq 1, length 64
17:03:33.878122 IP 192.168.0.12 > 123.123.123.123: ICMP echo request, id 62475, seq 2, length 64
17:03:34.878280 IP 192.168.0.12 > 123.123.123.123: ICMP echo request, id 62475, seq 3, length 64
17:03:35.878528 IP 192.168.0.12 > 123.123.123.123: ICMP echo request, id 62475, seq 4, length 64
So that's telling me traffic isn't really making it out at all. The Raspberry PI 2 doesn't have a WAN, just one LAN port, of course. I have a few NAT rules on the DD-WRT below. But that's irrelevant at this point since traffic isn't even getting sent out let alone returning anything:
# ----------------------
# Azure - Microsoft Azure Cloud: VPN Gateway
# ----------------------
iptables -I FORWARD -s 10.10.0.0/24 -d 192.168.0.0/24 -j ACCEPT
iptables -I INPUT -p icmp -s 10.10.0.0/24 -d 192.168.0.1/32 -j ACCEPT
# TCP
iptables -t nat -I PREROUTING -s 123.123.123.123 -p tcp --dport 500 -j DNAT --to 192.168.0.12:500
iptables -I FORWARD -p tcp -d 192.168.0.12 --dport 500 -j ACCEPT
iptables -t nat -I PREROUTING -s 123.123.123.123 -p tcp --dport 4500 -j DNAT --to 192.168.0.12:4500
iptables -I FORWARD -p tcp -d 192.168.0.12 --dport 4500 -j ACCEPT
# UDP
iptables -t nat -I PREROUTING -s 123.123.123.123 -p udp --dport 500 -j DNAT --to 192.168.0.12:500
iptables -I FORWARD -p udp -d 192.168.0.12 --dport 500 -j ACCEPT
iptables -t nat -I PREROUTING -s 123.123.123.123 -p udp --dport 4500 -j DNAT --to 192.168.0.12:4500
iptables -I FORWARD -p udp -d 192.168.0.12 --dport 4500 -j ACCEPT
# SHH: NAT Test Only
iptables -t nat -I PREROUTING -p tcp --dport 4522 -j DNAT --to 192.168.0.12:22
iptables -I FORWARD -p tcp -d 192.168.0.12 --dport 22 -j ACCEPT
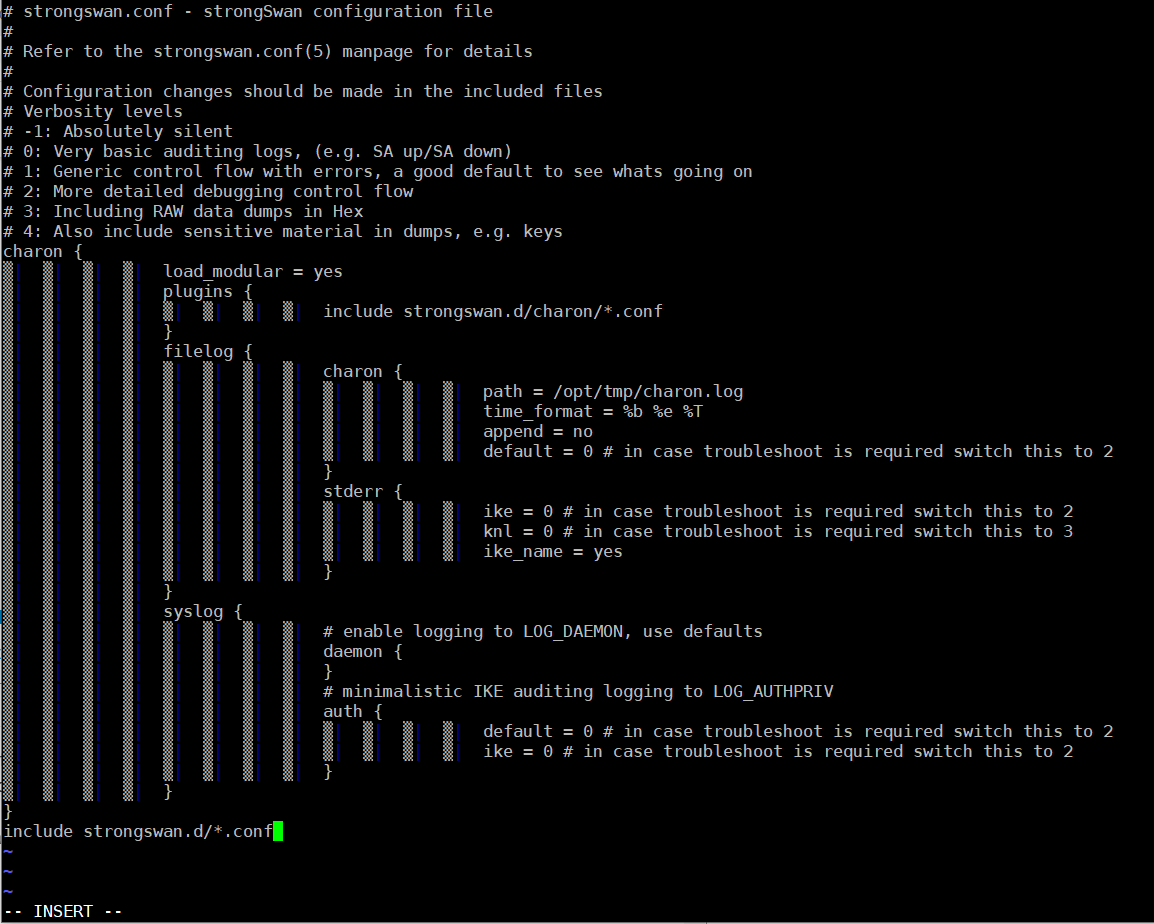
Relevant configuration:
root@OWRT01:~# cat /etc/ipsec.conf
# ipsec.conf - strongSwan IPsec configuration file
# basic configuration
config setup
# strictcrlpolicy=yes
# uniqueids = no
# Add connections here.
conn AZURE
authby=secret
auto=start
type=tunnel
keyexchange=ikev2
keylife=3600s
ikelifetime=28800s
left=100.100.100.100
leftsubnets={ 192.168.0.0/24, 10.0.0.0/24, 10.1.0.0/24, 10.2.0.0/24, 10.3.0.0/24, } # Network subnet located on-premises
# leftnexthop=%defaultroute
right=123.123.123.123
rightsubnets={ 10.10.0.0/24, 10.20.0.0/24, 10.30.0.0/24, 10.40.0.0/24, 10.50.0.0/24, } # Azure network subnet defined in cloud
ike=aes256-sha1-modp1024
esp=aes256-sha1
root@OWRT01:~#
root@OWRT01:~#
root@OWRT01:~#
root@OWRT01:~# cat /etc/strongswan.conf
# strongswan.conf - strongSwan configuration file
#
# Refer to the strongswan.conf(5) manpage for details
#
# Configuration changes should be made in the included files
# Verbosity levels
# -1: Absolutely silent
# 0: Very basic auditing logs, (e.g. SA up/SA down)
# 1: Generic control flow with errors, a good default to see whats going on
# 2: More detailed debugging control flow
# 3: Including RAW data dumps in Hex
# 4: Also include sensitive material in dumps, e.g. keys
charon {
load_modular = yes
plugins {
include strongswan.d/charon/*.conf
}
filelog {
charon {
path = /var/log/charon.log
time_format = %b %e %T
append = no
default = 0 # in case troubleshoot is required switch this to 2
}
stderr {
ike = 0 # in case troubleshoot is required switch this to 2
knl = 0 # in case troubleshoot is required switch this to 3
ike_name = yes
}
}
syslog {
# enable logging to LOG_DAEMON, use defaults
daemon {
}
# minimalistic IKE auditing logging to LOG_AUTHPRIV
auth {
default = 0 # in case troubleshoot is required switch this to 2
ike = 0 # in case troubleshoot is required switch this to 2
}
}
}
include strongswan.d/*.conf
root@OWRT01:~#
root@OWRT01:~#
root@OWRT01:~#
root@OWRT01:~#
root@OWRT01:~# cat /etc/ipsec.secrets
# /etc/ipsec.secrets - strongSwan IPsec secrets file
100.100.100.100 123.123.123.123 : PSK "PressEnter"
root@OWRT01:~#
Tcpdump on OpenWRT:
root@OWRT01:~#
root@OWRT01:~# tcpdump -i ipsec0 -n dst 123.123.123.123 or src 123.123.123.123
tcpdump: verbose output suppressed, use -v or -vv for full protocol decode
listening on ipsec0, link-type RAW (Raw IP), capture size 262144 bytes
tcpdump: pcap_loop: The interface went down
0 packets captured
0 packets received by filter
0 packets dropped by kernel
root@OWRT01:~# tcpdump -i ipsec0 -n dst 123.123.123.123 or src 123.123.123.123
tcpdump: verbose output suppressed, use -v or -vv for full protocol decode
listening on ipsec0, link-type RAW (Raw IP), capture size 262144 bytes
^C
0 packets captured
0 packets received by filter
0 packets dropped by kernel
root@OWRT01:~# tcpdump -i br-lan -n dst 123.123.123.123 or src 123.123.123.123
tcpdump: verbose output suppressed, use -v or -vv for full protocol decode
listening on br-lan, link-type EN10MB (Ethernet), capture size 262144 bytes
^C
0 packets captured
4 packets received by filter
0 packets dropped by kernel
root@OWRT01:~#
root@OWRT01:~# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc fq_codel master br-lan state UP group default qlen 1000
link/ether b8:27:eb:1c:55:8d brd ff:ff:ff:ff:ff:ff
3: sit0@NONE: <NOARP> mtu 1480 qdisc noop state DOWN group default qlen 1000
link/sit 0.0.0.0 brd 0.0.0.0
4: br-lan: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP group default qlen 1000
link/ether b8:27:eb:1c:55:8d brd ff:ff:ff:ff:ff:ff
inet 192.168.0.12/24 brd 192.168.0.255 scope global br-lan
valid_lft forever preferred_lft forever
inet6 fdc8:29db:a9ed::1/60 scope global noprefixroute
valid_lft forever preferred_lft forever
inet6 fe80::ba27:ebff:fe1c:558d/64 scope link
valid_lft forever preferred_lft forever
7: ipsec0: <POINTOPOINT,MULTICAST,NOARP,UP,LOWER_UP> mtu 1400 qdisc fq_codel state UNKNOWN group default qlen 500
link/none
inet6 fe80::d5de:6ac0:c375:534e/64 scope link stable-privacy
valid_lft forever preferred_lft forever
root@OWRT01:~#
On a side note IRT the opkg command, you're totally correct @ergamus . Needed to run opkg update first.
root@OWRT01:~# service ipsec restart
root@OWRT01:~# opkg install tcpdump
Unknown package 'tcpdump'.
Collected errors:
* opkg_install_cmd: Cannot install package tcpdump.
root@OWRT01:~#
root@OWRT01:~#
root@OWRT01:~#
root@OWRT01:~#
root@OWRT01:~#
root@OWRT01:~# opkg update
Downloading http://downloads.openwrt.org/releases/19.07.3/targets/brcm2708/bcm2709/packages/Packages.gz
Updated list of available packages in /var/opkg-lists/openwrt_core
Downloading http://downloads.openwrt.org/releases/19.07.3/targets/brcm2708/bcm2709/packages/Packages.sig
Signature check passed.
.
.
.
.
root@OWRT01:~#
root@OWRT01:~# opkg install tcpdump
Installing tcpdump (4.9.3-1) to root...
Downloading http://downloads.openwrt.org/releases/19.07.3/packages/arm_cortex-a7_neon-vfpv4/base/tcpdump_4.9.3-1_arm_cortex-a7_neon-vfpv4.ipk
Configuring tcpdump.
root@OWRT01:~#
Thank you,