Hi,
I'm trying to learn some network stuff with OpenWRT on a virtual machine setup (VirtualBox two Internal Networks + NAT for Main Router)
My current setup is
OpenWRT Router Main
|
OpenWRT Router Secondary
|
Client Linux
I can ping the Main Router from Secondary Router using the address fd5f:a:a::1 just fine. Also, I can ping the Secondary Router from the client Linux using the address fd5f:a:a:1::1.
However, I cannot ping the main router from the client linux. I tried tcpdump on the secondary router on br-lan and it finds the packets with:
13:42:16.756117 IP6 alpine.lan > ff02::1:ff00:1: ICMP6, neighbor solicitation, who has fd5f:a:a::1, length 32
but for some reason, this does not get passed to the wlan6 interface. From the routing table below, it seems that the ICMP packet should be forwarded to the Main router but this does not happen. Using tcpdump on the wlan6 interface or the Main router does not yield results. So the packet simply stops at the secondary router. What could be the problem and how do I fix this? Thanks! I've listed more information about my setup below.
They have the following IP-Addresses:
Main Router:
eth1 (wlan6):
inet6 fd17:625c:f037:2:a00:27ff:fe48:b381/64 scope global noprefixroute
inet6 fe80::a00:27ff:fe48:b381/64 scope link
br-lan:
inet6 fd5f:a:a::1/56 scope global noprefixroute
inet6 fe80::a00:27ff:fe14:7d36/64 scope link
Secondary Router:
eth1 (wlan6):
inet6 fd5f:a:a:0:a00:27ff:fee8:3aa/64 scope global noprefixroute
inet6 fd5f:a:a::62a/128 scope global dynamic noprefixroute
inet6 fe80::a00:27ff:fee8:3aa/64 scope link
br-lan:
inet6 fd5f:a:a:1::1/64 scope global dynamic noprefixroute
inet6 fd5f:a:a:b::1/64 preferred_lft 42597sec
inet6 fe80::a00:27ff:fec8:1aa7/64 scope link
and my client PC has the IP addresses of:
eth0:
inet6 fd5f:a:a:b::5e1/128 scope global dynamic noprefixroute
inet6 fd5f:a:a:1::5e1/128 scope global dynamic noprefixroute
inet6 fd5f:a:a:b:f6de:baa1:3265:49f0/64 scope global noprefixroute flags 100
inet6 fd5f:a:a:1:30c0:ffaf:5135:196b/64 scope global dyamic noprefixroute flags 100
inet6 fe80::37da:cba7:ca37:554b/64 scope link
Main Router ifstatus lan:
{
"up": true,
"pending": false,
"available": true,
"autostart": true,
"dynamic": false,
"uptime": 1340,
"l3_device": "br-lan",
"proto": "static",
"device": "br-lan",
"updated": [
"addresses"
],
"metric": 0,
"dns_metric": 0,
"delegation": true,
"ipv4-address": [
{
"address": "192.168.1.1",
"mask": 24
}
],
"ipv6-address": [
],
"ipv6-prefix": [
],
"ipv6-prefix-assignment": [
{
"address": "fd5f:a:a::",
"mask": 56,
"local-address": {
"address": "fd5f:a:a::1",
"mask": 56
}
}
],
"route": [
],
"dns-server": [
],
"dns-search": [
],
"neighbors": [
],
"inactive": {
"ipv4-address": [
],
"ipv6-address": [
],
"route": [
],
"dns-server": [
],
"dns-search": [
],
"neighbors": [
]
},
"data": {
}
}
Secondary Router (ifstatus wan6)
{
"up": true,
"pending": false,
"available": true,
"autostart": true,
"dynamic": false,
"uptime": 1258,
"l3_device": "eth1",
"proto": "dhcpv6",
"device": "eth1",
"metric": 0,
"dns_metric": 0,
"delegation": true,
"ipv4-address": [
],
"ipv6-address": [
{
"address": "fd5f:a:a::62a",
"mask": 128,
"preferred": 41940,
"valid": 41940
},
{
"address": "fd5f:a:a:0:a00:27ff:fee8:3aa",
"mask": 64
}
],
"ipv6-prefix": [
{
"address": "fd5f:a:a:1::",
"mask": 64,
"preferred": 41940,
"valid": 41940,
"class": "wan6",
"assigned": {
"lan": {
"address": "fd5f:a:a:1::",
"mask": 64
}
}
}
],
"ipv6-prefix-assignment": [
],
"route": [
{
"target": "fd5f:a:a::",
"mask": 64,
"nexthop": "::",
"metric": 256,
"source": "::/0"
},
{
"target": "fd5f:a:a::",
"mask": 48,
"nexthop": "fe80::a00:27ff:fe14:7d36",
"metric": 512,
"valid": 1529,
"source": "fd5f:a:a:0:a00:27ff:fee8:3aa/64"
},
{
"target": "fd5f:a:a::",
"mask": 48,
"nexthop": "fe80::a00:27ff:fe14:7d36",
"metric": 512,
"valid": 1529,
"source": "fd5f:a:a:1::/64"
},
{
"target": "fd5f:a:a::",
"mask": 48,
"nexthop": "fe80::a00:27ff:fe14:7d36",
"metric": 512,
"valid": 1529,
"source": "fd5f:a:a::62a/128"
}
],
"dns-server": [
"fd5f:a:a::1"
],
"dns-search": [
],
"neighbors": [
],
"inactive": {
"ipv4-address": [
],
"ipv6-address": [
],
"route": [
],
"dns-server": [
],
"dns-search": [
],
"neighbors": [
]
},
"data": {
"passthru": "00170010fd5f000a000a00000000000000000001"
}
}
Secondary router (ifstatus lan):
{
"up": true,
"pending": false,
"available": true,
"autostart": true,
"dynamic": false,
"uptime": 1250,
"l3_device": "br-lan",
"proto": "static",
"device": "br-lan",
"updated": [
"addresses"
],
"metric": 0,
"dns_metric": 0,
"delegation": true,
"ipv4-address": [
{
"address": "192.168.2.1",
"mask": 24
}
],
"ipv6-address": [
{
"address": "fd5f:a:a:b::1",
"mask": 64
}
],
"ipv6-prefix": [
],
"ipv6-prefix-assignment": [
{
"address": "fd5f:a:a:1::",
"mask": 64,
"preferred": 41954,
"valid": 41954,
"local-address": {
"address": "fd5f:a:a:1::1",
"mask": 64
}
}
],
"route": [
],
"dns-server": [
],
"dns-search": [
],
"neighbors": [
],
"inactive": {
"ipv4-address": [
],
"ipv6-address": [
],
"route": [
],
"dns-server": [
],
"dns-search": [
],
"neighbors": [
]
},
"data": {
}
}
Main router configs:
#/etc/config/network
config interface 'loopback'
option device 'lo'
option proto 'static'
option ipaddr '127.0.0.1'
option netmask '255.0.0.0'
config globals 'globals'
option ula_prefix 'fd5f:a:a::/48'
config device
option name 'br-lan'
option type 'bridge'
list ports 'eth0'
config interface 'lan'
option device 'br-lan'
option proto 'static'
option ipaddr '192.168.1.1'
option netmask '255.255.255.0'
list ip6class 'local'
option ip6assign '56'
config interface 'wan'
option device 'eth1'
option proto 'dhcp'
config interface 'wan6'
option device 'eth1'
option proto 'dhcpv6'
Secondary router configs:
#/etc/config/network
config interface 'loopback'
option device 'lo'
option proto 'static'
option ipaddr '127.0.0.1'
option netmask '255.0.0.0'
#config globals 'globals'
# option ula_prefix 'fd5f:a:a::/48'
config device
option name 'br-lan'
option type 'bridge'
list ports 'eth0'
config interface 'lan'
option device 'br-lan'
option proto 'static'
option netmask '255.255.255.0'
#option ip6assign '60'
option ipaddr '192.168.2.1'
option ip6addr 'fd5f:a:a:b::1/64'
option ip6assign '64'
config interface 'wan'
option device 'eth1'
option proto 'dhcp'
config interface 'wan6'
option device 'eth1'
option proto 'dhcpv6'
option reqaddress 'try'
option defaultroute '0'
option reqprefix '64'
#/etc/config/firewall
config defaults
option syn_flood 1
option input ACCEPT
option output ACCEPT
option forward REJECT
# Uncomment this line to disable ipv6 rules
# option disable_ipv6 1
config zone
option name lan
list network 'lan'
option input ACCEPT
option output ACCEPT
option forward ACCEPT
config zone
option name wan
list network 'wan'
list network 'wan6'
option input REJECT
option output ACCEPT
option forward REJECT
option masq 1
option mtu_fix 1
config forwarding
option src lan
option dest wan
# We need to accept udp packets on port 68,
# see https://dev.openwrt.org/ticket/4108
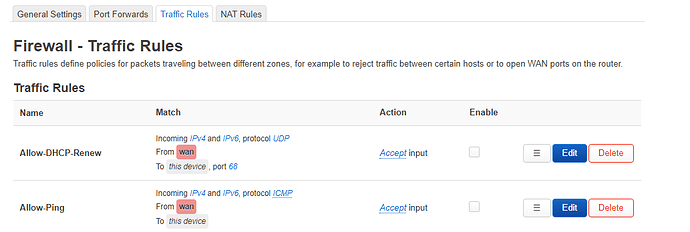
config rule
option name Allow-DHCP-Renew
option src wan
option proto udp
option dest_port 68
option target ACCEPT
option family ipv4
# Allow IPv4 ping
config rule
option name Allow-Ping
option src wan
option proto icmp
option icmp_type echo-request
option family ipv4
option target ACCEPT
config rule
option name Allow-IGMP
option src wan
option proto igmp
option family ipv4
option target ACCEPT
# Allow DHCPv6 replies
# see https://github.com/openwrt/openwrt/issues/5066
config rule
option name Allow-DHCPv6
option src wan
option proto udp
option dest_port 546
option family ipv6
option target ACCEPT
config rule
option name Allow-MLD
option src wan
option proto icmp
option src_ip fe80::/10
list icmp_type '130/0'
list icmp_type '131/0'
list icmp_type '132/0'
list icmp_type '143/0'
option family ipv6
option target ACCEPT
# Allow essential incoming IPv6 ICMP traffic
config rule
option name Allow-ICMPv6-Input
option src wan
option proto icmp
list icmp_type echo-request
list icmp_type echo-reply
list icmp_type destination-unreachable
list icmp_type packet-too-big
list icmp_type time-exceeded
list icmp_type bad-header
list icmp_type unknown-header-type
list icmp_type router-solicitation
list icmp_type neighbour-solicitation
list icmp_type router-advertisement
list icmp_type neighbour-advertisement
option limit 1000/sec
option family ipv6
option target ACCEPT
# Allow essential forwarded IPv6 ICMP traffic
config rule
option name Allow-ICMPv6-Forward
option src wan
option dest *
option proto icmp
list icmp_type echo-request
list icmp_type echo-reply
list icmp_type destination-unreachable
list icmp_type packet-too-big
list icmp_type time-exceeded
list icmp_type bad-header
list icmp_type unknown-header-type
option limit 1000/sec
option family ipv6
option target ACCEPT
config rule
option name Allow-IPSec-ESP
option src wan
option dest lan
option proto esp
option target ACCEPT
config rule
option name Allow-ISAKMP
option src wan
option dest lan
option dest_port 500
option proto udp
option target ACCEPT
The secondary router has the following routing table:
fd5f:a:a::/48 from fd5f:a:a::62a via fe80::a00:27ff:fe14:7d36 dev eth1 metric 512
fd5f:a:a::/48 from fd5f:a:a::/64 via fe80::a00:27ff:fe14:7d36 dev eth1 metric 512
fd5f:a:a::/48 from fd5f:a:a:1::/64 via fe80::a00:27ff:fe14:7d36 dev eth1 metric 512
fd5f:a:a::/64 dev eth1 metric 256
unreachable fd5f:a:a::/64 dev lo metric 2147483647
fd5f:a:a:1::/64 dev br-lan metric 1024
unreachable fd5f:a:a:1::/64 dev lo metric 2147483647
fd5f:a:a:b::/64 dev br-lan metric 256
fe80::/64 dev eth1 metric 256
fe80::/64 dev br-lan metric 256
anycast fd5f:a:a:: dev eth1 metric 0
anycast fd5f:a:a:1:: dev br-lan metric 0
anycast fd5f:a:a:b:: dev br-lan metric 0
anycast fe80:: dev eth1 metric 0
anycast fe80:: dev br-lan metric 0
multicast ff00::/8 dev br-lan metric 256
multicast ff00::/8 dev eth1 metric 256