Hello every body, my name is Fabio and I have been for long time interested on putting openwrt on NETIS 2411 cheap router ( and other thousands of router with same specifications )
Before continue reading, as suggested from many members on this forum, would advice that the result could be affected from some vulnerabilities so it must be considered as a "study case " and not a production environment
Do it at your risk , not suggested for daily use
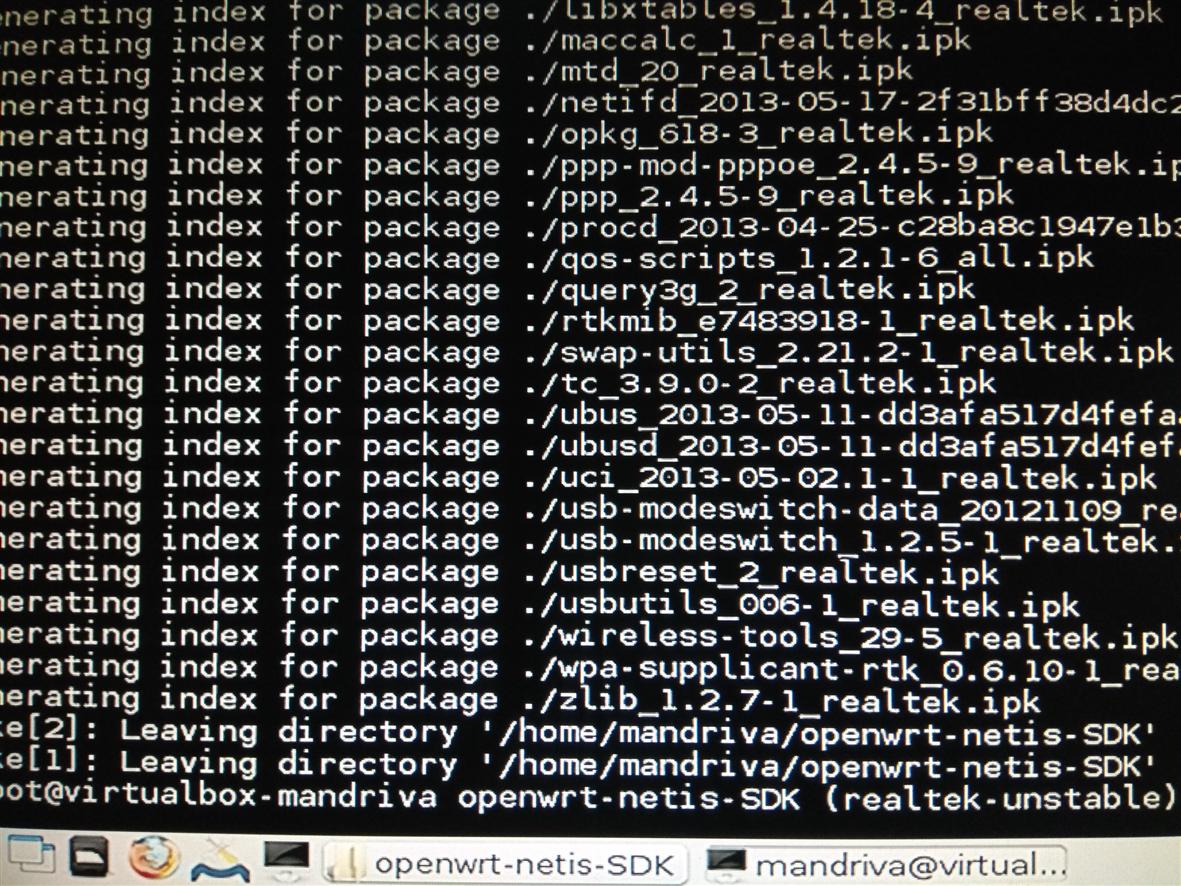
It has cpu RTL8196c , wifi RTL8188ce, only 4 mega of rom and 16 mega of ram, but finally I managed to make it run on it. I did not write ANY code, all the work has been made from other people and all the credits go to this people and their big work, such as the job from @wifisky
Here i talk about openwrt 12.09 and not of LEDE , where there is a specific post
The image i made ACTUALLY has some limitations:
-
for booting is needed a bootloader not LOCKED to any vendor and one bootloader suitable of this is found ( by accident, must recognize ) in WS-WN523N2 Wireless-N Router
-
wifi is working but only in WEP ( no wpa/wpa2) but i think is more a misconfiguration that a missing driver or maybe i missed any info
-
and of course NO LUCI at all, but is already a miracle that is booting and working
Since I am more a Frankenstein doctor ( copy paste pieces of hex codes ) and not a programmer , here looking for some interested in understanding and studying/debugging about
-
generating an image that flashes the bootloader too
-
understanding why wpa/wpa2 doesn't work
of course my actual work is avaible for anyone but would love to publish a final work with all things working out of the box