For my usage i want a multi VPN tunnel compatible system
on a TL-WR2543ND i built install and create openvpn client tunnel under OpenWrt.
ping my.fqdn.org never works
ping ip.ad.dr.es works
all i can see it's my request and dns server response behind this tun0 but no more
i'am using up_down_script.sh from https://openwrt.org/docs/guide-user/services/vpn/openvpn/extra#dokuwiki__top at ### DNS and domain chapter
and all seem to work ... but without dns response into my ssh
client for openwrt can acces by ssh thru Openvpn client session to all network behind openvpn server like a charm.
Business_lan <==> OpenvpnServer <==> Internet <==> Openwrt & openvpn client mode <==> client_lan
i found this command line and used it link there https://github.com/StreisandEffect/streisand/wiki/Setting-an-OpenWrt-Based-Router-as-OpenVPN-Client
change "none" by "dhcp"
# a new network interface for tun:
uci set network.My_vpn_conf_name=interface
uci set network.My_vpn_conf_name.proto='dhcp' #dhcp #none
uci set network.My_vpn_conf_name.ifname='tun0'
# a new firewall zone (for VPN):
uci add firewall zone
oci set firewall.@zone[-1].name='vpn'
uci set firewall.@zone[-1].input='REJECT'
uci set firewall.@zone[-1].output='ACCEPT'
uci set firewall.@zone[-1].forward='REJECT'
uci set firewall.@zone[-1].masq='1'
uci set firewall.@zone[-1].mtu_fix='1'
uci add_list firewall.@zone[-1].network='My_vpn_conf_name'
# enable forwarding from LAN to VPN:
uci add firewall forwarding
uci set firewall.@forwarding[-1].src='lan'
uci set firewall.@forwarding[-1].dest='vpn'
# Finally, you should commit UCI changes:
uci commit`
what was wrong ?my.fqdn.org never works
i view by tcpdump dns resolved response bytcpdump -i tun0 -n
trendy
April 7, 2020, 10:21am
2
Could you post here the capture? tcpdump -i tun0 -vvvn -c 10 udp port 53
arafolie:
change "none" by "dhcp"
Nope, switch it back to none.uci export network; uci export dhcp; uci export firewall; uci export openvpn
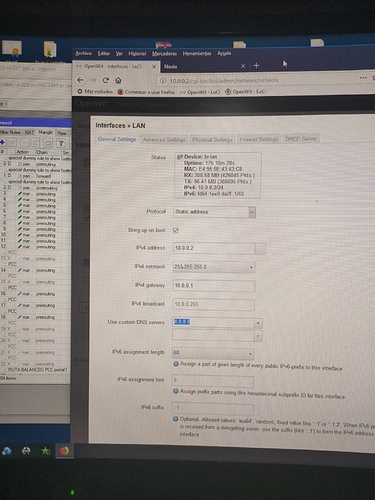
go to the Lan network and set a custom dns 8.8.8.8
trendy
April 7, 2020, 11:32am
4
This is not a correct solution. Nameserver 8.8.8.8 is not reachable from the lan interface, hence the correct would be to assign it to wan interface. Regardless of that, if the corporate nameserver needs to be used to resolve internal IPs, the GoogleDNS won't help.
nothing in UDP
root@OpenWrt:~# tcpdump -i tun0 -n | grep -v BOOTP/DHCP
tcpdump: verbose output suppressed, use -v or -vv for full protocol decode
listening on tun0, link-type RAW (Raw IP), capture size 262144 bytes
13:31:35.109198 IP 172.21.108.12.29284 > 172.20.108.17.53: 46076+ A? mitnick.Mycompany.tech. (34)
13:31:35.110635 IP 172.21.108.12.18269 > 172.20.108.17.53: 14418+ AAAA? mitnick.Mycompany.tech. (34)
13:31:35.114332 IP 172.20.108.17.53 > 172.21.108.12.29284: 46076 NXDomain* 0/1/0 (96)
13:31:35.118226 IP 172.20.108.17.53 > 172.21.108.12.18269: 14418 NXDomain* 0/1/0 (96)
ok back to none and reboot to be sure ;_)
root@OpenWrt:~# uci export network; uci export dhcp; uci export firewall; uci export openvpn
package network
config interface 'loopback'
option ifname 'lo'
option proto 'static'
option ipaddr '127.0.0.1'
option netmask '255.0.0.0'
config globals 'globals'
option ula_prefix 'fd60:e04e:7aed::/48'
config interface 'lan'
option type 'bridge'
option ifname 'eth0.1'
option proto 'static'
option netmask '255.255.255.0'
option ip6assign '60'
option ipaddr '172.22.109.1'
config interface 'wan'
option ifname 'eth0.2'
option proto 'dhcp'
config interface 'wan6'
option ifname 'eth0.2'
option proto 'dhcpv6'
config switch
option name 'switch0'
option reset '1'
option enable_vlan '1'
config switch_vlan
option device 'switch0'
option vlan '1'
option ports '1 2 3 4 9t'
config switch_vlan
option device 'switch0'
option vlan '2'
option ports '0 9t'
config interface 'My_vpn_conf_name_ovpn'
option ifname 'tun0'
option proto 'none'
package dhcp
config dnsmasq
option domainneeded '1'
option boguspriv '1'
option filterwin2k '0'
option localise_queries '1'
option rebind_protection '1'
option rebind_localhost '1'
option local '/lan/'
option domain 'lan'
option expandhosts '1'
option nonegcache '0'
option authoritative '1'
option readethers '1'
option leasefile '/tmp/dhcp.leases'
option nonwildcard '1'
option localservice '1'
option enable_tftp '1'
option tftp_root '/srv/tftp'
option resolvfile '/tmp/resolv.conf.My_vpn_conf_name_ovpn'
config dhcp 'lan'
option interface 'lan'
option start '100'
option limit '150'
option leasetime '12h'
option dhcpv6 'server'
option ra 'server'
config dhcp 'wan'
option interface 'wan'
option ignore '1'
config odhcpd 'odhcpd'
option maindhcp '0'
option leasefile '/tmp/hosts/odhcpd'
option leasetrigger '/usr/sbin/odhcpd-update'
option loglevel '4'
package firewall
config defaults
option syn_flood '1'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'REJECT'
config zone
option name 'lan'
list network 'lan'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'ACCEPT'
config zone
option name 'wan'
list network 'wan'
list network 'wan6'
option input 'REJECT'
option output 'ACCEPT'
option forward 'REJECT'
option masq '1'
option mtu_fix '1'
config forwarding
option src 'lan'
option dest 'wan'
config rule
option name 'Allow-DHCP-Renew'
option src 'wan'
option proto 'udp'
option dest_port '68'
option target 'ACCEPT'
option family 'ipv4'
config rule
option name 'Allow-Ping'
option src 'wan'
option proto 'icmp'
option icmp_type 'echo-request'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-IGMP'
option src 'wan'
option proto 'igmp'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-DHCPv6'
option src 'wan'
option proto 'udp'
option src_ip 'fc00::/6'
option dest_ip 'fc00::/6'
option dest_port '546'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-MLD'
option src 'wan'
option proto 'icmp'
option src_ip 'fe80::/10'
list icmp_type '130/0'
list icmp_type '131/0'
list icmp_type '132/0'
list icmp_type '143/0'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Input'
option src 'wan'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
list icmp_type 'router-solicitation'
list icmp_type 'neighbour-solicitation'
list icmp_type 'router-advertisement'
list icmp_type 'neighbour-advertisement'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Forward'
option src 'wan'
option dest '*'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-IPSec-ESP'
option src 'wan'
option dest 'lan'
option proto 'esp'
option target 'ACCEPT'
config rule
option name 'Allow-ISAKMP'
option src 'wan'
option dest 'lan'
option dest_port '500'
option proto 'udp'
option target 'ACCEPT'
config include
option path '/etc/firewall.user'
config redirect
option dest_port '22'
option src 'wan'
option name 'ssh_internet_2_lan'
option src_dport '22'
option target 'DNAT'
option dest 'lan'
option proto 'tcp'
option dest_ip '172.22.109.1'
config zone
option name 'vpn'
option input 'REJECT'
option output 'ACCEPT'
option forward 'REJECT'
option masq '1'
option mtu_fix '1'
list network 'My_vpn_conf_name_ovpn'
config forwarding
option src 'lan'
option dest 'vpn'
package openvpn
config openvpn 'My_vpn_conf_name'
option config '/etc/openvpn/My_vpn_conf_name.ovpn'
option enabled '1'
and for complete information
root@OpenWrt:~# cat /tmp/resolv.conf.My_vpn_conf_name_ovpn
domain Mycompany.lan
domain Mycompany.tech
domain Mycompany2.net
nameserver 172.20.108.17
if you need
root@OpenWrt:~# ip -o -f inet addr ls
1: lo inet 127.0.0.1/8 scope host lo\ valid_lft forever preferred_lft forever
5: br-lan inet 172.22.109.1/24 brd 172.22.109.255 scope global br-lan\ valid_lft forever preferred_lft forever
7: eth0.2 inet 192.168.1.37/24 brd 192.168.1.255 scope global eth0.2\ valid_lft forever preferred_lft forever
11: tun0 inet 172.21.108.12/24 brd 172.21.108.255 scope global tun0\ valid_lft forever preferred_lft forever
root@OpenWrt:~# netstat -rn
Kernel IP routing table
Destination Gateway Genmask Flags MSS Window irtt Iface
0.0.0.0 192.168.1.254 0.0.0.0 UG 0 0 0 eth0.2
10.1.0.0 172.21.108.1 255.255.248.0 UG 0 0 0 tun0
172.20.108.0 172.21.108.1 255.255.252.0 UG 0 0 0 tun0
172.21.108.0 0.0.0.0 255.255.255.0 U 0 0 0 tun0
172.22.109.0 0.0.0.0 255.255.255.0 U 0 0 0 br-lan
192.168.1.0 0.0.0.0 255.255.255.0 U 0 0 0 eth0.2
trendy
April 7, 2020, 11:42am
6
This isn't nothing, it's a legitimate response from the NS that the name you are querying doesn't exist. Discuss with the NS administrator that there is such a record in the NS.
1 Like
is there an issue around local /lan/ in openwrt and my receive outside openvpn domain in *.lan form ?
My company domain Mycompany.lan
you are right, for Mycompany.tech but my first domain is Mycompany.lan and this one never responding
Ok i realise an other test for you
root@OpenWrt:~# ping mitnick.Mycompany.lan
ping: bad address 'mitnick.Mycompany.lan'
root@OpenWrt:~# nslookup cetautomatix.Mycompany.lan
Server: 127.0.0.1
Address: 127.0.0.1#53
** server can't find cetautomatix.Mycompany.lan: NXDOMAIN
** server can't find cetautomatix.Mycompany.lan: NXDOMAIN
root@OpenWrt:~# nslookup cetautomatix.Mycompany.lan 172.22.109.1
Server: 172.22.109.1
Address: 172.22.109.1#53
** server can't find cetautomatix.Mycompany.lan: NXDOMAIN
** server can't find cetautomatix.Mycompany.lan: NXDOMAIN
root@OpenWrt:~# nslookup cetautomatix.Mycompany.lan 172.20.108.17
Server: 172.20.108.17
Address: 172.20.108.17#53
Name: cetautomatix.Mycompany.lan
Address 1: 172.20.109.32
*** Can't find cetautomatix.Mycompany.lan: No answer
and in my tcpdump i receive this
13:48:57.938223 IP 172.21.108.12.47806 > 172.20.109.32.22: Flags [.], ack 2518, win 5092, options [nop,nop,TS val 2262523785 ecr 2623681549], length 0
13:50:14.478482 IP 172.21.108.12.32886 > 172.20.108.17.53: 26870+ A? cetautomatix.Mycompany.lan. (38)
13:50:14.479116 IP 172.21.108.12.32886 > 172.20.108.17.53: 42565+ AAAA? cetautomatix.Mycompany.lan. (38)
13:50:14.482506 IP 172.20.108.17.53 > 172.21.108.12.32886: 26870* 1/1/2 A 172.20.109.32 (121)
and finally, my first need
root@OpenWrt:~# ping cetautomatix.Mycompany.lan
trendy
April 7, 2020, 12:12pm
9
ah your company uses the .lan domain? Lovely...
i have changed openwrt.lan to openwrt.inside but no more for my local resolving issue ...
dhcp.@dnsmasq[0].domain='inside'
dhcp.@dnsmasq[0].local='/inside/'
How do i change to make my Mycompany.lan resolved into my openwrt and is local network client
rage to see this packet inside my tun0 and no response in lan or localhost
root@OpenWrt:~# nslookup japet.Mycompany.lan
Server: 127.0.0.1
Address: 127.0.0.1#53
*** Can't find japet.Mycompany.lan: No answer
*** Can't find japet.Mycompany.lan: No answer
and this tcpdump in tun0 few seconde later
20:28:54.002242 IP 172.21.108.12.64475 > 172.20.108.17.53: 23706+ A? japet.Mycompany.lan. (31)
20:28:54.003703 IP 172.21.108.12.12578 > 172.20.108.17.53: 46836+ AAAA? japet.Mycompany.lan. (31)
20:28:54.006570 IP 172.20.108.17.53 > 172.21.108.12.64475: 23706* 1/1/2 A 172.20.108.26 (114)
Why doesn't return inside ??
trendy
April 7, 2020, 9:43pm
11
You'll need to disable rebind protection.
Enables DNS rebind attack protection by discarding upstream RFC1918 responses
Normally an upstream NS will not respond with a private IP.
trendy
April 8, 2020, 8:37am
13
Sorry mate, but you are off topic. The OP is using a specific nameserver to resolve internal corporate addresses. GoogleDNS and any other public dns will not resolve that.