Hi All. I had a very happy network running for months on end without any problem. A recent power outage has resulted in me needing to rebuild my router. I did a fresh install and then configured everything manually using backup files as reference. I've been searching the forum and Reddit for any hints that may put me out of my misery, but I can't seem to find anything that works.
My original working config is as follows:
- OpenWRT router with Wireguard VPN peer to Mullvad - all devices on LAN are routed through the VPN with the exception of some smart TVs that are routed via WAN with Policy Based Routing.
- Wireguard "server" peer running on OpenWRT that provides remote access to my LAN and internet (with ad blocking) when I'm out on my Pixel phone.
This was all working happily until the rebuild and now nothing I do works. I can get a handshake if my phone is connected to my WiFi, on cellular, or other Wi-Fi, it won't work.
I can see packets arriving and being sent on my VPN interface on OpenWRT, but no handshake when attempting to connect via cellular network.
I have manually generated keys repeatedly and re-configured configurations. I tried using the automated config scripts too. All end up with the same result - can only handshake on my Wi-Fi. Unfortunately I don't have a networking background so all of my attempts have been trial and error without being 100% certain of the outcome of some of the commands.
Wireguard client on the Pixel is set to connect to my WAN static IP address.
/etc/config/network
config interface 'loopback'
option device 'lo'
option proto 'static'
option ipaddr '127.0.0.1'
option netmask '255.0.0.0'
config globals 'globals'
option ula_prefix 'fd00:ab:cd::/48'
config device
option name 'eth2'
option macaddr 'redacted'
config interface 'wan'
option device 'eth2'
option proto 'dhcp'
option peerdns '0'
list dns '9.9.9.9'
list dns '149.112.112.112'
option ipv6 '0'
option delegate '0'
config device
option name 'br-lan'
option type 'bridge'
list ports 'eth1'
list ports 'eth0'
config device
option name 'eth1'
option macaddr 'redacted'
config device
option name 'eth0'
option macaddr 'redacted'
config interface 'lan'
option device 'br-lan'
option proto 'static'
option ipaddr '10.0.0.254'
option netmask '255.255.255.0'
option ip6assign '60'
list dns '10.0.0.254'
list dns '127.0.0.1'
option ipv6 'off'
option delegate '0'
option force_link '0'
config interface 'WG0'
option proto 'wireguard'
option private_key 'redacted'
list addresses 'redacted/32'
list addresses 'redacted/128'
config wireguard_WG0
option description ' au-per-wg-301 '
option public_key 'hQXsNk/9R2We0pzP1S9J3oNErEu2CyENlwTdmDUYFhg='
list allowed_ips '0.0.0.0/0'
option route_allowed_ips '1'
option endpoint_host 'au-per-wg-301.relays.mullvad.net'
option endpoint_port '51820'
option persistent_keepalive '25'
config interface 'vpn'
option proto 'wireguard'
option private_key 'redacted'
option listen_port '991'
list addresses '192.168.9.1/24'
config wireguard_vpn 'wgclient'
option public_key 'redacted'
option preshared_key 'redacted'
option description 'Pixel'
option persistent_keepalive '25'
list allowed_ips '192.168.9.2/32'
option route_allowed_ips '1'
config route
option interface 'vpn'
option target '192.168.9.2/32'
option gateway '192.168.9.1'
Wireguard OpenWRT Config
interface: WG0
public key: redacted
private key: (hidden)
listening port: 26162
peer: redacted
endpoint: redacted:51820
allowed ips: 0.0.0.0/0
latest handshake: 1 minute, 45 seconds ago
transfer: 66.31 GiB received, 4.91 GiB sent
persistent keepalive: every 25 seconds
interface: vpn
public key: redacted
private key: (hidden)
listening port: 991
peer: redacted
preshared key: (hidden)
endpoint: redacted1951
allowed ips: 192.168.9.2/32
transfer: 3.61 KiB received, 2.01 MiB sent
persistent keepalive: every 25 seconds
Wireguard Pixel Config
[Interface]
Address = 192.168.9.2/32
DNS = 10.0.0.254
PrivateKey = redacted
[Peer]
AllowedIPs = 0.0.0.0/0, 10.0.0.0/24
Endpoint = my_public_static_ip:991
PreSharedKey = redacted
PublicKey = redacted
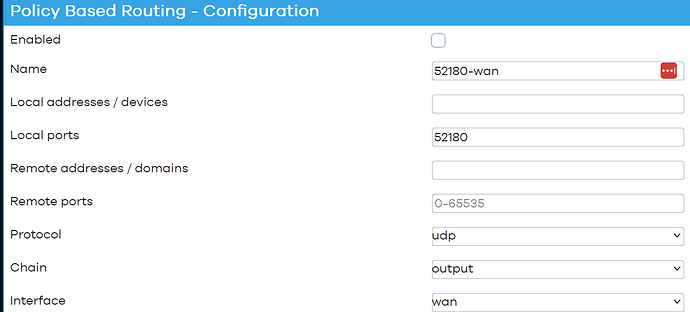
/etc/config/pbr
config pbr 'config'
option verbosity '2'
option strict_enforcement '1'
option resolver_set 'none'
option ipv6_enabled '0'
option boot_timeout '30'
option rule_create_option 'add'
option procd_reload_delay '1'
list webui_supported_protocol 'all'
list webui_supported_protocol 'tcp'
list webui_supported_protocol 'udp'
list webui_supported_protocol 'tcp udp'
list webui_supported_protocol 'icmp'
option enabled '1'
option webui_show_ignore_target '1'
list ignored_interface 'vpn'
list ignored_interface 'vpnserver'
list ignored_interface 'wgserver'
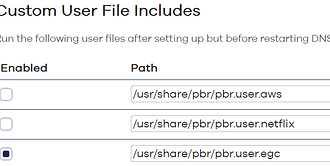
config include
option path '/usr/share/pbr/pbr.user.aws'
option enabled '1'
config include
option path '/usr/share/pbr/pbr.user.netflix'
option enabled '1'
config policy
option name 'Bypass VPN'
option interface 'wan'
option src_addr '10.0.0.65/27'
/etc/config/firewall
config defaults
option input 'ACCEPT'
option output 'ACCEPT'
option fullcone '1'
option forward 'ACCEPT'
option synflood_protect '1'
config zone 'lan'
option name 'lan'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'ACCEPT'
list network 'lan'
list network 'vpn'
config zone 'wan'
option name 'wan'
option input 'REJECT'
option output 'ACCEPT'
option forward 'REJECT'
option fullcone4 '1'
option fullcone6 '1'
option masq '1'
option mtu_fix '1'
list network 'wan'
config forwarding
option src 'lan'
option dest 'wan'
config rule
option name 'Allow-DHCP-Renew'
option src 'wan'
option proto 'udp'
option dest_port '68'
option target 'ACCEPT'
option family 'ipv4'
config rule
option name 'Allow-Ping'
option src 'wan'
option proto 'icmp'
option icmp_type 'echo-request'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-IGMP'
option src 'wan'
option proto 'igmp'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-DHCPv6'
option src 'wan'
option proto 'udp'
option dest_port '546'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-MLD'
option src 'wan'
option proto 'icmp'
option src_ip 'fe80::/10'
list icmp_type '130/0'
list icmp_type '131/0'
list icmp_type '132/0'
list icmp_type '143/0'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Input'
option src 'wan'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
list icmp_type 'router-solicitation'
list icmp_type 'neighbour-solicitation'
list icmp_type 'router-advertisement'
list icmp_type 'neighbour-advertisement'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Forward'
option src 'wan'
option dest '*'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-IPSec-ESP'
option src 'wan'
option dest 'lan'
option proto 'esp'
option target 'ACCEPT'
config rule
option name 'Allow-ISAKMP'
option src 'wan'
option dest 'lan'
option dest_port '500'
option proto 'udp'
option target 'ACCEPT'
config include 'miniupnpd'
option type 'script'
option path '/usr/share/miniupnpd/firewall.include'
config rule
option name 'Reject-IPv6'
option family 'ipv6'
option src 'wan'
option dest '*'
option target 'REJECT'
option enabled '0'
config zone
option name 'wgzone'
option input 'REJECT'
option output 'ACCEPT'
option forward 'REJECT'
option masq '1'
option mtu_fix '1'
list network 'WG0'
config forwarding
option src 'lan'
option dest 'wgzone'
config include 'pbr'
option fw4_compatible '1'
option type 'script'
option path '/usr/share/pbr/pbr.firewall.include'
config nat
option name 'dns_masq'
list proto 'tcp'
list proto 'udp'
option src 'lan'
option dest_ip '10.0.0.254'
option dest_port '53'
option target 'MASQUERADE'
config redirect
option dest 'lan'
option target 'DNAT'
option name 'HASS App via WAN'
option src 'wan'
option src_dport '54962'
option dest_ip '10.0.0.85'
option dest_port '8123'
config rule
option name 'Incoming Wireguard'
list proto 'udp'
option dest_port '991'
option target 'ACCEPT'
option src 'wan'
Thanks for any tips and / or guidance.