Most likely some typographic error with the keys, keys reused from other device, or bad time on the device (I tend to think it is more possible).
This is not going to work:
The pi WiFi hardware doesn’t support simultaneous sta and AP modes. Further, the sta mode connection is associated with the wan network, but that interface is set to use eth0, not wireless.
You will need two physical interfaces - either WiFi + Ethernet or two WiFi devices.
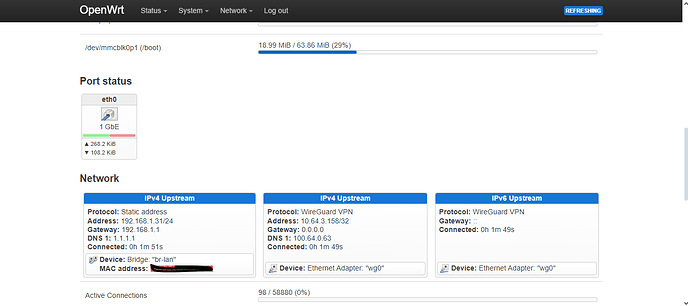
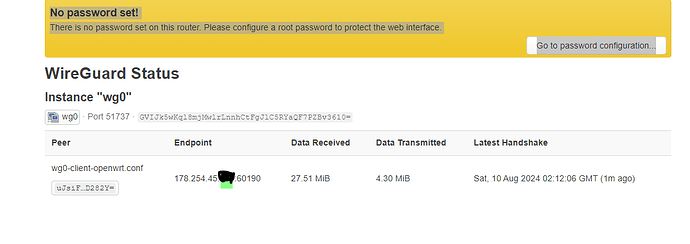
I just did a sysupgrade and configurate again the Wireguard-VPN with my 1blu-Server and it works. I also connect to the Openwrt-Spot and couls easily surf in the internet, also blocked sites. So seems the problem is with the Mullvad configuration. Even i checked the keys many times. Somewhere should be the problem,
root@OpenWrt:~# ip route show
default dev wg0 scope link
178.254.45.XXX via 192.168.1.1 dev br-lan
192.168.1.0/24 dev br-lan scope link src 192.168.1.31
root@OpenWrt:~# wg show
interface: wg0
public key: redact=
private key: (hidden)
listening port: 48895
peer: redact=
preshared key: (hidden)
endpoint: 178.254.45.XXX:54199
allowed ips: 0.0.0.0/0, ::/0
latest handshake: 1 minute, 30 seconds ago
transfer: 2.67 KiB received, 2.44 KiB sent
root@OpenWrt:~# curl -4 ifconfig.co
178.254.45.XXX
root@OpenWrt:~#
root@OpenWrt:~# ubus call system board
{
"kernel": "5.15.162",
"hostname": "OpenWrt",
"system": "ARMv8 Processor rev 4",
"model": "Raspberry Pi 3 Model B Plus Rev 1.3",
"board_name": "raspberrypi,3-model-b-plus",
"rootfs_type": "ext4",
"release": {
"distribution": "OpenWrt",
"version": "23.05.4",
"revision": "r24012-d8dd03c46f",
"target": "bcm27xx/bcm2710",
"description": "OpenWrt 23.05.4 r24012-d8dd03c46f"
}
}
root@OpenWrt:~# cat /etc/config/network
config interface 'loopback'
option device 'lo'
option proto 'static'
option ipaddr '127.0.0.1'
option netmask '255.0.0.0'
config globals 'globals'
option ula_prefix 'fdc8:355a:2f12::/48'
config device
option name 'br-lan'
option type 'bridge'
list ports 'eth0'
config interface 'lan'
option device 'br-lan'
option proto 'static'
option ipaddr '192.168.1.31'
option netmask '255.255.255.0'
option ip6assign '60'
option gateway '192.168.1.1'
list dns '1.1.1.1'
config interface 'wan'
option proto 'dhcp'
option device 'eth0'
config interface 'wg0'
option proto 'wireguard'
option private_key 'redact='
list addresses '10.66.66.2/32'
list addresses 'fd42:42:42::2/128'
list dns '1.1.1.1'
list dns '1.0.0.1'
config wireguard_wg0
option description 'wg0-client-openwrt.conf'
option public_key 'redact'
option preshared_key 'redact='
list allowed_ips '0.0.0.0/0'
list allowed_ips '::/0'
option endpoint_host '178.254.45.XXX'
option endpoint_port '54199'
option route_allowed_ips '1'
root@OpenWrt:~# cat /etc/config/wireless
config wifi-device 'radio0'
option type 'mac80211'
option path 'platform/soc/3f300000.mmcnr/mmc_host/mmc1/mmc1:0001/mmc1:0001:1'
option channel '36'
option band '5g'
option htmode 'VHT40'
option cell_density '0'
config wifi-iface 'default_radio0'
option device 'radio0'
option mode 'ap'
option ssid 'OpenWrt'
option encryption 'none'
option network 'lan'
root@OpenWrt:~# cat /etc/config/dhcp
config dnsmasq
option domainneeded '1'
option boguspriv '1'
option filterwin2k '0'
option localise_queries '1'
option rebind_protection '1'
option rebind_localhost '1'
option local '/lan/'
option domain 'lan'
option expandhosts '1'
option nonegcache '0'
option cachesize '1000'
option authoritative '1'
option readethers '1'
option leasefile '/tmp/dhcp.leases'
option resolvfile '/tmp/resolv.conf.d/resolv.conf.auto'
option nonwildcard '1'
option localservice '1'
option ednspacket_max '1232'
option filter_aaaa '0'
option filter_a '0'
config dhcp 'lan'
option interface 'lan'
option start '100'
option limit '150'
option leasetime '12h'
option dhcpv4 'server'
option dhcpv6 'server'
option ra 'server'
list ra_flags 'managed-config'
list ra_flags 'other-config'
option ignore '1'
config dhcp 'wan'
option interface 'wan'
option ignore '1'
config odhcpd 'odhcpd'
option maindhcp '0'
option leasefile '/tmp/hosts/odhcpd'
option leasetrigger '/usr/sbin/odhcpd-update'
option loglevel '4'
root@OpenWrt:~# cat /etc/config/firewall
config defaults
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'ACCEPT'
option synflood_protect '1'
option flow_offloading '1'
config zone
option name 'lan'
list network 'lan'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'ACCEPT'
config zone
option name 'wan'
list network 'wan'
list network 'wan6'
option input 'REJECT'
option output 'ACCEPT'
option forward 'REJECT'
option masq '1'
option mtu_fix '1'
config forwarding
option src 'lan'
option dest 'wan'
config rule
option name 'Allow-DHCP-Renew'
option src 'wan'
option proto 'udp'
option dest_port '68'
option target 'ACCEPT'
option family 'ipv4'
config rule
option name 'Allow-Ping'
option src 'wan'
option proto 'icmp'
option icmp_type 'echo-request'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-IGMP'
option src 'wan'
option proto 'igmp'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-DHCPv6'
option src 'wan'
option proto 'udp'
option dest_port '546'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-MLD'
option src 'wan'
option proto 'icmp'
option src_ip 'fe80::/10'
list icmp_type '130/0'
list icmp_type '131/0'
list icmp_type '132/0'
list icmp_type '143/0'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Input'
option src 'wan'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
list icmp_type 'router-solicitation'
list icmp_type 'neighbour-solicitation'
list icmp_type 'router-advertisement'
list icmp_type 'neighbour-advertisement'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Forward'
option src 'wan'
option dest '*'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-IPSec-ESP'
option src 'wan'
option dest 'lan'
option proto 'esp'
option target 'ACCEPT'
config rule
option name 'Allow-ISAKMP'
option src 'wan'
option dest 'lan'
option dest_port '500'
option proto 'udp'
option target 'ACCEPT'
config zone
option name 'vpn'
option input 'REJECT'
option output 'ACCEPT'
option forward 'REJECT'
list network 'wg0'
option masq '1'
config forwarding
option src 'lan'
option dest 'vpn'
root@OpenWrt:~#
SSID: OpenWrt
Protocol: Wi-Fi 5 (802.11ac)
Security type: Open
Network band: 5 GHz
Network channel: 36
Link speed (Receive/Transmit): 180/180 (Mbps)
IPv6 address: 2409:8a1e:6a54:d8e0:a2a5:5dce:f9ce:35da
fdc8:355a:2f12::d36
fdc8:355a:2f12:0:4673:f000:3b72:53cd
Link-local IPv6 address: fe80::a345:9e89:d9e3:44f8%14
IPv6 DNS servers: fdc8:355a:2f12::1
IPv4 address: 192.168.1.4
IPv4 DNS servers: 192.168.1.1
Manufacturer: Intel Corporation
Description: Intel(R) Dual Band Wireless-AC 7260
Driver version: 18.33.17.1
Physical address (MAC): redact
I have asked before and will do again how is your Pi connected to the main router?
Are you using the Ethernet port?
I am connected to my main router with the ethernet port. so i use a lan cable.
The mai point is: When i use the config file of my 1blu Wireguard -VPN-Server i can tunneling, but not with my Mullvad-VPN configs. Their is not a difference except the data.
i follow this tutorial:https://mullvad.net/en/help/running-wireguard-router
Maybe there is nothing wrong with the WireGuard setup but with your router setup, see the comment of @psherman: Mullvad Wireguard Installation - No handshake - #22 by psherman
You have connected with ethernet but your br-lan setup does not show it
This is more or less setup as a Dumb AP so no WAN and the ethernet port should be assigned to br-lan.
Compare a working set up and look how br-lan is setup
Thank you all for your help. I will follow your suggestions and do the modifications and then come back. Need few time. Meanwhile wish the best for you all. ![]()
So this week i installed fresh installation of openwrt. first with my own vps-wireguard- server in germany and i could tunneling all the blocked websites. also youtube and google and so on. after that with the same conditions i used mullvad wireguard, but no succes. even no ping outside. means mullvad problem for me. i contact the support and waiting now for response.
thanks again all for help.
BusyBox v1.36.1 (2024-08-02 21:18:03 UTC) built-in shell (ash)
| |.-----.-----.-----.| | | |.----.| |_
| - || _ | -| || | | || || |
|_____|| |||||___||| |____|
|| W I R E L E S S F R E E D O M
OpenWrt 23.05.4, r24012-d8dd03c46f
=== WARNING! =====================================
There is no root password defined on this device!
Use the "passwd" command to set up a new password
in order to prevent unauthorized SSH logins.
root@OpenWrt:~# ip -4 ru
0: from all lookup local
32766: from all lookup main
32767: from all lookup default
root@OpenWrt:~# ifconfig
br-lan Link encap:Ethernet HWaddr BA:27:EB:EE:XX:XX
inet addr:192.168.10.1 Bcast:192.168.10.255 Mask:255.255.255.0
inet6 addr: fd32:6e79:a598::1/60 Scope:Global
inet6 addr: fe80::b827:ebff:feee:4552/64 Scope:Link
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
RX packets:3217 errors:0 dropped:0 overruns:0 frame:0
TX packets:10874 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:400816 (391.4 KiB) TX bytes:5161031 (4.9 MiB)
eth0 Link encap:Ethernet HWaddr 00:E0:4C:99:XX:XX
inet addr:192.168.1.5 Bcast:192.168.1.255 Mask:255.255.255.0
inet6 addr: fe80::2e0:4cff:fe99:384/64 Scope:Link
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
RX packets:7379 errors:0 dropped:400 overruns:0 frame:0
TX packets:3999 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:4508548 (4.2 MiB) TX bytes:1219990 (1.1 MiB)
lo Link encap:Local Loopback
inet addr:127.0.0.1 Mask:255.0.0.0
inet6 addr: ::1/128 Scope:Host
UP LOOPBACK RUNNING MTU:65536 Metric:1
RX packets:89 errors:0 dropped:0 overruns:0 frame:0
TX packets:89 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:8699 (8.4 KiB) TX bytes:8699 (8.4 KiB)
phy0-ap0 Link encap:Ethernet HWaddr BA:27:EB:EE:XX:XX
inet6 addr: fe80::b827:ebff:feee:4552/64 Scope:Link
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
RX packets:6408 errors:0 dropped:0 overruns:0 frame:0
TX packets:11285 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:1130719 (1.0 MiB) TX bytes:5288212 (5.0 MiB)
wg0 Link encap:UNSPEC HWaddr 00-00-00-00-00-00-00-00-00-00-00-00-00-00-00-00
inet addr:10.66.66.2 P-t-P:10.66.66.2 Mask:255.255.255.255
inet6 addr: fd42:42:42::2/128 Scope:Global
UP POINTOPOINT RUNNING NOARP MTU:1420 Metric:1
RX packets:6731 errors:0 dropped:0 overruns:0 frame:0
TX packets:3912 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:4285308 (4.0 MiB) TX bytes:1048548 (1023.9 KiB)
root@OpenWrt:~# ping 10.66.66.2
PING 10.66.66.2 (10.66.66.2): 56 data bytes
64 bytes from 10.66.66.2: seq=0 ttl=64 time=0.543 ms
64 bytes from 10.66.66.2: seq=1 ttl=64 time=0.829 ms
64 bytes from 10.66.66.2: seq=2 ttl=64 time=0.551 ms
64 bytes from 10.66.66.2: seq=3 ttl=64 time=0.537 ms
64 bytes from 10.66.66.2: seq=4 ttl=64 time=0.564 ms
64 bytes from 10.66.66.2: seq=5 ttl=64 time=0.549 ms
64 bytes from 10.66.66.2: seq=6 ttl=64 time=0.556 ms
^C
--- 10.66.66.2 ping statistics ---
7 packets transmitted, 7 packets received, 0% packet loss
round-trip min/avg/max = 0.537/0.589/0.829 ms
root@OpenWrt:~# ping 178.254.45.XXX
PING 178.254.45.210 (178.254.45.XXX): 56 data bytes
64 bytes from 178.254.45.XXX: seq=0 ttl=50 time=196.192 ms
64 bytes from 178.254.45.XXX: seq=1 ttl=50 time=196.664 ms
64 bytes from 178.254.45.XXX: seq=2 ttl=50 time=197.715 ms
64 bytes from 178.254.45.XX: seq=3 ttl=50 time=195.677 ms
C
--- 178.254.45.210 ping statistics ---
35 packets transmitted, 35 packets received, 0% packet loss
round-trip min/avg/max = 194.292/195.266/200.799 ms
.
root@OpenWrt:~# ubus call system board
{
"kernel": "5.15.162",
"hostname": "OpenWrt",
"system": "ARMv6-compatible processor rev 7 (v6l)",
"model": "Raspberry Pi Zero W Rev 1.1",
"board_name": "raspberrypi,model-zero-w",
"rootfs_type": "ext4",
"release": {
"distribution": "OpenWrt",
"version": "23.05.4",
"revision": "r24012-d8dd03c46f",
"target": "bcm27xx/bcm2708",
"description": "OpenWrt 23.05.4 r24012-d8dd03c46f"
}
}
root@OpenWrt:~# cat /etc/config/network
config interface 'loopback'
option device 'lo'
option proto 'static'
option ipaddr '127.0.0.1'
option netmask '255.0.0.0'
config globals 'globals'
option ula_prefix 'fd32:6e79:a598::/48'
config device
option name 'br-lan'
option type 'bridge'
list ports 'wlan0'
config interface 'lan'
option device 'br-lan'
option proto 'static'
option ipaddr '192.168.10.1'
option netmask '255.255.255.0'
option ip6assign '60'
list dns '1.1.1.1'
config device
option name 'eth0'
config interface 'wan'
option proto 'dhcp'
option device 'eth0'
config interface 'wwan'
option proto 'dhcp'
config interface 'wg0'
option proto 'wireguard'
option private_key '0JlKoAzWB1CIXmtwedSZDBk2cqftWm0qG4wZXXXX='
list addresses '10.66.66.2/32'
list addresses 'fd42:42:42::2/128'
list dns '1.1.1.1'
list dns '1.0.0.1'
config wireguard_wg0
option description 'wg0-client-openwrt.conf'
option public_key 'uJsiFFDbTjU+SgVz+IPAjbbrTCT1KkFSR8P86KXXXX='
option preshared_key '/c+SjbsaZx9dZk1XYLuvYNKzh2aG3p1OvUgSCKXXXX='
list allowed_ips '0.0.0.0/0'
list allowed_ips '::/0'
option endpoint_host '178.254.45.XXX'
option endpoint_port '60190'
option route_allowed_ips '1'
root@OpenWrt:~# cat /etc/config/wireless
config wifi-device 'radio0'
option type 'mac80211'
option path 'platform/soc/20300000.mmcnr/mmc_host/mmc1/mmc1:0001/mmc1:0001:1'
option channel '1'
option band '2g'
option htmode 'HT20'
option cell_density '0'
config wifi-iface 'wifinet1'
option device 'radio0'
option mode 'sta'
option network 'wwan'
option ssid 'CMCC-ThPb'
option encryption 'psk2'
option key 'XXXXXXXX'
config wifi-iface 'wifinet2'
option device 'radio0'
option mode 'ap'
option ssid 'OpenWrt'
option encryption 'psk2'
option key 'XXXXXXXXX'
option network 'lan'
root@OpenWrt:~# cat /etc/config/dhcp
config dnsmasq
option domainneeded '1'
option boguspriv '1'
option filterwin2k '0'
option localise_queries '1'
option rebind_protection '1'
option rebind_localhost '1'
option local '/lan/'
option domain 'lan'
option expandhosts '1'
option nonegcache '0'
option cachesize '1000'
option authoritative '1'
option readethers '1'
option leasefile '/tmp/dhcp.leases'
option resolvfile '/tmp/resolv.conf.d/resolv.conf.auto'
option nonwildcard '1'
option localservice '1'
option ednspacket_max '1232'
option filter_aaaa '0'
option filter_a '0'
config dhcp 'lan'
option interface 'lan'
option start '100'
option limit '150'
option leasetime '12h'
option dhcpv4 'server'
option dhcpv6 'server'
option ra 'server'
list ra_flags 'managed-config'
list ra_flags 'other-config'
config dhcp 'wan'
option interface 'wan'
option ignore '1'
config odhcpd 'odhcpd'
option maindhcp '0'
option leasefile '/tmp/hosts/odhcpd'
option leasetrigger '/usr/sbin/odhcpd-update'
option loglevel '4'
root@OpenWrt:~# cat /etc/config/firewall
config defaults
option input 'REJECT'
option output 'ACCEPT'
option forward 'REJECT'
option synflood_protect '1'
option flow_offloading '1'
config zone
option name 'lan'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'ACCEPT'
list network 'lan'
config zone
option name 'wan'
option input 'REJECT'
option output 'ACCEPT'
option forward 'REJECT'
option masq '1'
option mtu_fix '1'
list network 'wan'
list network 'wan6'
list network 'wwan'
config forwarding
option src 'lan'
option dest 'wan'
config rule
option name 'Allow-DHCP-Renew'
option src 'wan'
option proto 'udp'
option dest_port '68'
option target 'ACCEPT'
option family 'ipv4'
config rule
option name 'Allow-Ping'
option src 'wan'
option proto 'icmp'
option icmp_type 'echo-request'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-IGMP'
option src 'wan'
option proto 'igmp'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-DHCPv6'
option src 'wan'
option proto 'udp'
option dest_port '546'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-MLD'
option src 'wan'
option proto 'icmp'
option src_ip 'fe80::/10'
list icmp_type '130/0'
list icmp_type '131/0'
list icmp_type '132/0'
list icmp_type '143/0'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Input'
option src 'wan'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
list icmp_type 'router-solicitation'
list icmp_type 'neighbour-solicitation'
list icmp_type 'router-advertisement'
list icmp_type 'neighbour-advertisement'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Forward'
option src 'wan'
option dest '*'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-IPSec-ESP'
option src 'wan'
option dest 'lan'
option proto 'esp'
option target 'ACCEPT'
config rule
option name 'Allow-ISAKMP'
option src 'wan'
option dest 'lan'
option dest_port '500'
option proto 'udp'
option target 'ACCEPT'
config zone
option name 'vpn'
option input 'REJECT'
option output 'ACCEPT'
option forward 'REJECT'
list network 'wg0'
option masq '1'
option mtu_fix '1'
config forwarding
option src 'lan'
option dest 'vpn'
root@OpenWrt:~#
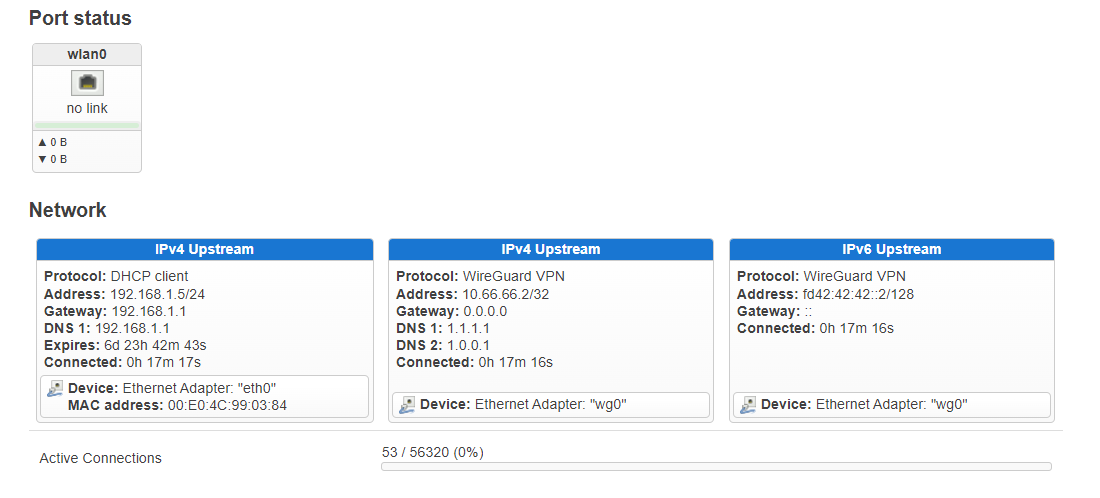
Finally i could solve it.
I folloved Mullvads own guide for installing Wireguard "https://mullvad.net/en/help/running-wireguard-router", but didnt work it. When i create the keys like described with "wg genkey | tee privatekey | wg pubkey > publickey" and use is could not a connection to internet. My workaround was to generate the keys with Openwrt-Wireguardmask and then use it for Mullvad-Keys was successfull. So the Topic can be closed. Works with RPI 3b+ as Pizero W.
Thank you all
This topic was automatically closed 10 days after the last reply. New replies are no longer allowed.