The modem being integrated in the Hub 5 makes our set-ups somewhat different, and I'm afraid I've no experience of Infinity product or Hub 5 hardware; but for what it's worth, I've got a similar setup working with BT-flavour fibre from Zen.
I have an Openreach modem (provided by Zen) plugged into the wall, and it's down to me to sort out my own PPPoE router. At the moment, it's a Linksys E4200v1 running LEDE 17.01.4; but for two or three years before that it was a Netgear WNDR3700v4 running OpenWrt 14.07 (the Linksys has taken its place while I upgrade).
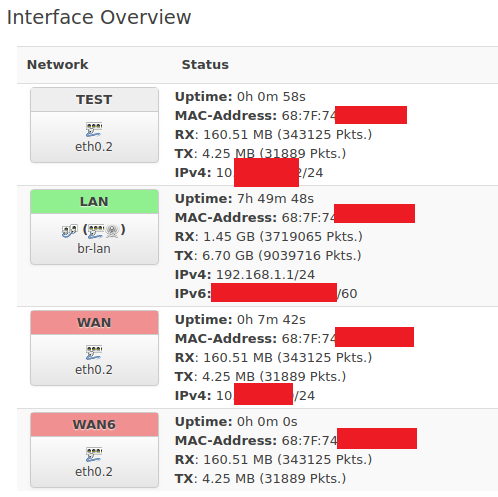
Switch configuration was a bit more fiddly on the Netgear due to peculiarities of its design (there's a pseudo fifth/second CPU port, and they're numbered back-to-front), but on the Linksys it was a breeze. I disabled a port (4) on the 'standard' NAT VLAN, and added a new one, in which the CPU was tagged and port 4 was untagged. I added an interface and firewall zone for the new VLAN, configured according to stuff I read on the OpenWrt Wiki/Forum - looking at it now, I'm a bit rusty on a couple of points, but it's pretty simple firewall zone/inter-zone configuration, and limiting masquerading only to the NAT range (if you intend to retain a NAT segment). I dare say there will be expert contributors who can help, or that we could find the info I managed to suss-it-out from, but if all else fails I can offer screenies and pointers.
In effect, my setup works like this...
Wall -> Modem -> PPPoE WAN in LEDE ... uses ___.___.___.166 public IP on its NAT/LAN interface which covers three of the four ports on the switch, and the wireless radios; it also uses ___.___.___.165 public IP for the public zone interface mapped to one port on the switch. In that port, I have a GigE switch, with two servers connected, one running .161, and the other .162
The machines on .161 and .162 are very much out in the wild, all ports dangling in the breeze. My LAN LAN runs just as it would with any old router behind NAT on .166 from all the other ports on the switch (and a few others). Port forwarding via .166 works fine (NB: be careful to specifiy which external IP to forward ports for, or you could have local machines 'pinching' traffic from your public ones); and with the firewall set-up 'correctly', machines inside the NAT can reach the public ones even if the WAN goes down (but the external machines can't 'see' the local ones without going through the NAT - i.e. pinging the external machines from 192.168.x.x always works, but never the other way around).
As I say, achieved pretty painlessly on both E4200v1 and WNDR3700v4 - I can't see the modem being integrated at/ahead of the WAN interface making a huge amount of difference (but again, I can't talk from experience on that point).
All the best,
Rob.