Hi again.
I am really frustrated with this issue. Everyone tells me it should work but no matter what I try, it simply does not work consistently.
I have read as much as I can on it and tried all sorts of variants but I cannot get the two networks to talk to each other. They can ping each other but I cannot browse from one to the other. I have loaded the DNS fields with every possible access point but it still will not work.
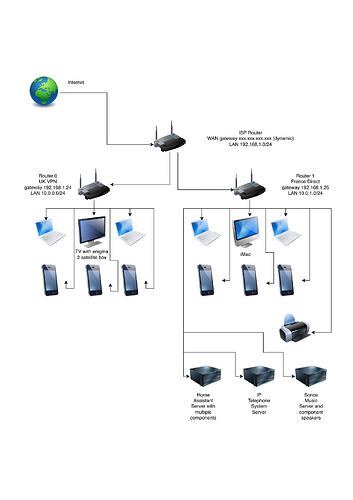
IN SUMMARY I can ping everywhere from each subnet but cannot browse to all adresses (which is shown in the tables below). I cannot ping or browse to either subnet from the main (ISP) network, 192.168.0.0/24. I accept there may be issues with the server I am trying to connect to (Home Assistant, Sonos, etc.) but I should at least be able to connect to the openwrt routers controlling each subnet, each of which is connected to the main network (via .24 and .25).
Additionally the access appears intermittent. Sometimes it does connect (say, to Home Assistant server), other times there is no response and sometimes it recognises the server as it shows an address it is trying to reach (in a private browser so no cache involved) but cannot show the full connection.
This is how I would like my network to operate:
Currently, these are the results of pinging and browsing:
Ping
From > 192.168.1.0/24 10.0.0.0/24 10.0.1.0/24 Notes
To
V
192.168.1.24 1 1 0 Gateway 10.0.0.0/24
192.168.1.25 1 0 1 Gateway 10.0.1.0/24
192.168.1.40 X X X iMac
192.168.1.65 1 1 1 IP Phones Server
192.168.1.200 1 1 0 Home Assistant Server
192.168.1.254 1 1 1 Gateway 192.168.1.0/24
10.0.0.1 0 1 1 Gateway 10.0.0.0/24
10.0.0.40 X 1 X iMac
10.0.0.140 0 1 1 Satellite Box
10.0.1.1 0 1 1 Gateway 10.0.1.0/24
10.0.1.175 X X 1 iMac
1 Yes
0 No
X Not Applicable
Browse
From > 192.168.1.0/24 10.0.0.0/24 10.0.1.0/24 Notes
To
V
192.168.1.24 0 1 0 Gateway 10.0.0.0/24
192.168.1.25 0 0 1 Gateway 10.0.1.0/24
192.168.1.40 1 X X iMac
192.168.1.65 1 1 1 IP Phones
192.168.1.200 1 1 1 Home Assistant
192.168.1.254 1 1 1 Gateway 192.168.1.0/24
10.0.0.1 0 1 0 Gateway 10.0.0.0/24
10.0.0.40 X 1 X iMac
10.0.0.140 0 1 0 Satellite Box
10.0.1.1 0 0 1 Gateway 10.0.1.0/24
10.0.1.175 X X 1 iMac
1 Yes
0 No
X Not Applicable
Here are the relevant network and firewall files as currently configured:
10.0.0.1
Network
config interface 'loopback'
option device 'lo'
option proto 'static'
option ipaddr '127.0.0.1'
option netmask '255.0.0.0'
config globals 'globals'
option packet_steering '1'
option ula_prefix 'fd33:1ec6:00a8::/48'
config device
option name 'br-lan'
option type 'bridge'
list ports 'lan1'
list ports 'lan2'
config interface 'lan'
option device 'br-lan'
option proto 'static'
option netmask '255.255.255.0'
option ip6assign '60'
option ipaddr '10.0.0.1'
option broadcast '10.0.0.255'
option gateway '192.168.1.24'
list ipaddr '10.0.0.1/24'
list dns '8.8.8.8'
list dns '8.8.4.4'
list dns '10.0.0.1'
list dns '10.0.1.1'
list dns '192.168.1.24'
list dns '192.168.1.25'
config device
option type '8021q'
option ifname 'lan4'
option vid '1'
option name 'lan4.1'
option mtu '1500'
option mtu6 '1500'
config interface 'ovpn_wan_free'
option proto 'none'
option metric '20'
option device 'tun0'
option defaultroute '0'
config device
option type '8021q'
option ifname 'lan3'
option vid '1'
option name 'lan3.1'
option mtu '1500'
config interface 'wan_fbx'
option device 'wan'
option proto 'static'
option ipaddr '192.168.1.24'
option netmask '255.255.255.0'
option gateway '192.168.1.254'
option broadcast '192.168.1.255'
list ipaddr '192.168.1.24/24'
option metric '10'
option dns_metric '10'
list dns '8.8.8.8'
list dns '8.8.4.4'
list dns '10.0.0.1'
list dns '10.0.1.1'
list dns '1.1.1.1'
config device
option name 'eth0'
config device
option name 'wan'
option ipv6 '0'
config interface 'WS_Biscuits'
option proto 'wireguard'
option private_key 'mK44X9eeidbC/mfYnsIjoeXlVMNTo2BPNZJwCSDxcmw='
list addresses '100.70.36.218/32'
list dns '10.255.255.3'
option listen_port '51820'
option auto '0'
config wireguard_WS_Biscuits
option description 'Windscribe-London-Biscuits-WG.conf'
option public_key 'qWSr7Tf40kvS+0kv4TbpSb6EevhSvn3kuXsjn2eWbA4='
option private_key 'mK44X9eeidbC/mfYnsIjoeXlVMNTo2BPNZJwCSDxcmw='
option preshared_key 'wm4wayzPVgphDKnvI3yZns4YiA8my9GE199RT+wxD4Q='
list allowed_ips '0.0.0.0/0'
list allowed_ips '::/0'
option endpoint_host 'lhr-335-wg.whiskergalaxy.com'
option endpoint_port '443'
option persistent_keepalive '25'
config route
option interface 'wan_fbx'
option target '10.0.1.0/24'
option gateway '192.168.1.25'
Firewall
config defaults
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'REJECT'
option synflood_protect '1'
option flow_offloading '1'
option flow_offloading_hw '1'
config zone
option name 'lan'
list network 'lan'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'ACCEPT'
option mtu_fix '1'
config zone
option name 'wan'
option output 'ACCEPT'
option forward 'REJECT'
option input 'REJECT'
option masq '1'
option mtu_fix '1'
option family 'ipv4'
list network 'wan_fbx'
list network 'WS_Biscuits'
list device 'tun0'
list device 'wan'
list masq_dest '!10.0.1.0/24'
config forwarding
option src 'lan'
option dest 'wan'
config rule
option name 'Allow-DHCP-Renew'
option src 'wan'
option proto 'udp'
option dest_port '68'
option target 'ACCEPT'
option family 'ipv4'
config rule
option name 'Allow-Ping'
option src 'wan'
option proto 'icmp'
option icmp_type 'echo-request'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-IGMP'
option src 'wan'
option proto 'igmp'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-DHCPv6'
option src 'wan'
option proto 'udp'
option src_ip 'fc00::/6'
option dest_ip 'fc00::/6'
option dest_port '546'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-MLD'
option src 'wan'
option proto 'icmp'
option src_ip 'fe80::/10'
list icmp_type '130/0'
list icmp_type '131/0'
list icmp_type '132/0'
list icmp_type '143/0'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Input'
option src 'wan'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
list icmp_type 'router-solicitation'
list icmp_type 'neighbour-solicitation'
list icmp_type 'router-advertisement'
list icmp_type 'neighbour-advertisement'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Forward'
option src 'wan'
option dest '*'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-IPSec-ESP'
option src 'wan'
option dest 'lan'
option proto 'esp'
option target 'ACCEPT'
config rule
option name 'Allow-ISAKMP'
option src 'wan'
option dest 'lan'
option dest_port '500'
option proto 'udp'
option target 'ACCEPT'
config rule
option name 'Support-UDP-Traceroute'
option src 'wan'
option dest_port '33434:33689'
option proto 'udp'
option family 'ipv4'
option target 'REJECT'
option enabled '0'
config include
option path '/etc/firewall.user'
config zone
option name 'VPN'
option input 'REJECT'
option output 'ACCEPT'
option forward 'REJECT'
option masq '1'
option mtu_fix '1'
list network 'London_Crumpets'
list network 'ovpn_wan_free'
config forwarding
option src 'lan'
option dest 'VPN'
config rule
option name 'Allow from LAN 10.0.1.0'
list proto 'all'
option src 'wan'
list src_ip '10.0.1.0/24'
option dest 'lan'
option target 'ACCEPT'
10.0.1.1
Network
config interface 'loopback'
option device 'lo'
option proto 'static'
option ipaddr '127.0.0.1'
option netmask '255.0.0.0'
config globals 'globals'
option packet_steering '1'
option ula_prefix 'fdce:b829:eed4::/48'
config device
option name 'br-lan'
option type 'bridge'
list ports 'lan1'
list ports 'lan2'
list ports 'lan3'
list ports 'lan4'
config interface 'lan'
option device 'br-lan'
option proto 'static'
option netmask '255.255.255.0'
option ip6assign '60'
option ipaddr '10.0.1.1'
option broadcast '10.0.1.255'
option gateway '192.168.1.25'
list ipaddr '10.0.1.1/24'
list dns '8.8.8.8'
list dns '8.8.4.4'
list dns '10.0.0.1'
list dns '10.0.1.1'
list dns '192.168.1.24'
list dns '192.168.1.25'
config interface 'wan'
option device 'wan'
option proto 'static'
option ipaddr '192.168.1.25'
option netmask '255.255.255.0'
option gateway '192.168.1.254'
option broadcast '192.168.1.255'
list ipaddr '192.168.1.25/24'
list dns '8.8.8.8'
list dns '8.8.4.4'
list dns '10.0.0.1'
list dns '10.0.1.1'
list dns '1.1.1.1'
config interface 'wan6'
option device 'wan'
option proto 'dhcpv6'
config route
option interface 'wan'
option target '10.0.0.0/24'
option gateway '192.168.1.24'
Firewall
config defaults
option input 'ACCEPT'
option output 'ACCEPT'
option synflood_protect '1'
option forward 'REJECT'
config zone
option name 'lan'
list network 'lan'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'ACCEPT'
config zone
option name 'wan'
option output 'ACCEPT'
option input 'REJECT'
option forward 'REJECT'
option masq '1'
option mtu_fix '1'
option family 'ipv4'
list network 'wan'
list network 'wan6'
list device 'wan'
list masq_dest '!10.0.0.0/24'
config forwarding
option src 'lan'
option dest 'wan'
config rule
option name 'Allow-DHCP-Renew'
option src 'wan'
option proto 'udp'
option dest_port '68'
option target 'ACCEPT'
option family 'ipv4'
config rule
option name 'Allow-Ping'
option src 'wan'
option proto 'icmp'
option icmp_type 'echo-request'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-IGMP'
option src 'wan'
option proto 'igmp'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-DHCPv6'
option src 'wan'
option proto 'udp'
option dest_port '546'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-MLD'
option src 'wan'
option proto 'icmp'
option src_ip 'fe80::/10'
list icmp_type '130/0'
list icmp_type '131/0'
list icmp_type '132/0'
list icmp_type '143/0'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Input'
option src 'wan'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
list icmp_type 'router-solicitation'
list icmp_type 'neighbour-solicitation'
list icmp_type 'router-advertisement'
list icmp_type 'neighbour-advertisement'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Forward'
option src 'wan'
option dest '*'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-IPSec-ESP'
option src 'wan'
option dest 'lan'
option proto 'esp'
option target 'ACCEPT'
config rule
option name 'Allow-ISAKMP'
option src 'wan'
option dest 'lan'
option dest_port '500'
option proto 'udp'
option target 'ACCEPT'
config rule
option name 'Support-UDP-Traceroute'
option src 'wan'
option dest_port '33434:33689'
option proto 'udp'
option family 'ipv4'
option target 'REJECT'
option enabled '0'
config include
option path '/etc/firewall.user'
config forwarding
option src 'wan'
option dest 'lan'
config rule
option name 'Allow from LAN 10.0.0.0'
list proto 'all'
option src 'wan'
list src_ip '10.0.0.0/24'
option dest 'lan'
option target 'ACCEPT'
An area I do not understand is forwarding from LAN to WAN etc. Could someone check these for me please?
Is the fact that 10.0.0.1 is on a VPN prevent the subnets seeing each other? DO I need some sort of push command in the VPN config file?
I hope someone can find the time to help me resolve this as I cannot move forward without it working.
Thanks if you read this far!
Geoff