I am building a router out of OpenWRT (in an LXC container).
I would appreciate some input form more experience users to solve this.
Here are the configs:https://pastebin.com/raw/dhenfW8G https://pastebin.com/raw/tWq25mza
Anyone? I am sure there is something simple I am missing.
Do you have a static IP on the WAN port ?
If that's the case, you manually have to provide DNSes in the DHCP for the clients.
DNS and DHCP examples See also: DNS and DHCP configuration, DNS encryption, DNS hijacking Introduction This how-to provides most common dnsmasq and odhcpd tuning scenarios adapted for OpenWrt. Instructions Static leases LuCI -> DHCP and DNS...
option 6 is DNS,
Apologies for not being clear. I cannot ping any external IP from the LAN (I can from the OpenWRT host). So that's not DNS-related.
Also, OpenWRT host gets its IP with DHCP from the ISP.
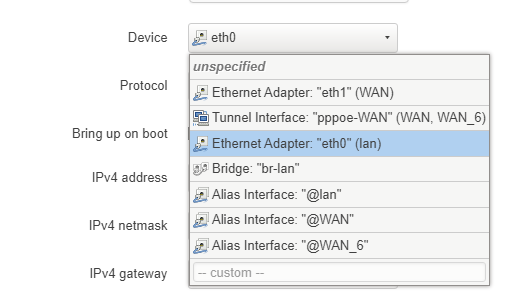
Is the LAN associated with the correct interface?
I installed OpenWrt yesterday on a Raspberry Pi 4 and the LAN was incorrectly associated with the 'br-lan' interface. I changed that to eth0 (your interface may differ), rebooted and everything was working.
I have three LAN interfaces bridged so it looks like this:
I can see you've configured VLAN107.
trendy
June 10, 2021, 8:27am
10
GRN interface doesn't have any RX or TX packets, so are you certain that the interfaces are up and lan hosts are able to communicate with OpenWrt?
trendy
June 10, 2021, 8:45am
12
Please run the following commands (copy-paste the whole block) and paste the output here, using the "Preformatted text </> " button:
ubus call system board; \
uci export network; uci export dhcp; uci export firewall; \
head -n -0 /etc/firewall.user; \
iptables-save -c; \
ip -4 addr ; ip -4 ro li tab all ; ip -4 ru
# ubus call system board
{
"kernel": "5.10.30-1-lts",
"hostname": "router",
"system": "AMD GX-420CA SOC with Radeon(tm) HD Graphics",
"model": "Hewlett-Packard HP t620 PLUS Quad Core TC",
"board_name": "hewlett-packard-hp-t620-plus-quad-core-tc",
"release": {
"distribution": "OpenWrt",
"version": "19.07.4",
"revision": "r11208-ce6496d796",
"target": "x86/64",
"description": "OpenWrt 19.07.4 r11208-ce6496d796"
}
}
# uci export network; uci export dhcp; uci export firewall;
package network
config interface 'loopback'
option ifname 'lo'
option proto 'static'
option ipaddr '127.0.0.1'
option netmask '255.0.0.0'
config globals 'globals'
option ula_prefix 'fdca:0a2a:ae66::/48'
config interface 'GRN'
option type 'bridge'
option proto 'static'
option netmask '255.255.255.0'
option ifname 'eth0 eth1 eth2'
list dns '1.1.1.1'
list dns '1.0.0.1'
option ipaddr '192.168.7.1'
option delegate '0'
config interface 'RED'
option ifname 'red0'
option proto 'dhcp'
option force_link '1'
option delegate '0'
config interface 'IoT'
option proto 'static'
option ipaddr '10.0.10.1'
option delegate '0'
option ifname 'eth10.2'
package dhcp
config dnsmasq
option domainneeded '1'
option localise_queries '1'
option rebind_protection '1'
option rebind_localhost '1'
option local '/lan/'
option domain 'lan'
option expandhosts '1'
option authoritative '1'
option readethers '1'
option leasefile '/tmp/dhcp.leases'
option resolvfile '/tmp/resolv.conf.auto'
option localservice '1'
config dhcp 'lan'
option interface 'lan'
option start '100'
option limit '150'
option leasetime '12h'
config dhcp 'wan'
option interface 'wan'
option ignore '1'
config odhcpd 'odhcpd'
option maindhcp '0'
option leasefile '/tmp/hosts/odhcpd'
option leasetrigger '/usr/sbin/odhcpd-update'
option loglevel '4'
config dhcp 'iot107'
option leasetime '12h'
option interface 'iot107'
option start '10'
option limit '99'
config dhcp 'eth1'
option start '100'
option leasetime '12h'
option limit '150'
option interface 'eth1'
config dhcp 'GRN'
option start '100'
option leasetime '12h'
option limit '150'
option interface 'GRN'
config dhcp 'IoT'
option start '100'
option leasetime '12h'
option limit '150'
option interface 'IoT'
package firewall
config defaults
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'REJECT'
option synflood_protect '1'
config zone
option name 'wan'
option input 'REJECT'
option output 'ACCEPT'
option masq '1'
option mtu_fix '1'
option network 'RED'
option forward 'DROP'
config zone
option name 'lan'
option input 'ACCEPT'
option output 'ACCEPT'
option network 'lan GRN'
option forward 'ACCEPT'
config forwarding
option src 'lan'
option dest 'wan'
config rule
option name 'Allow-DHCP-Renew'
option src 'wan'
option proto 'udp'
option dest_port '68'
option target 'ACCEPT'
option family 'ipv4'
config rule
option name 'Allow-Ping'
option src 'wan'
option proto 'icmp'
option icmp_type 'echo-request'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-IGMP'
option src 'wan'
option proto 'igmp'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-DHCPv6'
option src 'wan'
option proto 'udp'
option src_ip 'fc00::/6'
option dest_ip 'fc00::/6'
option dest_port '546'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-MLD'
option src 'wan'
option proto 'icmp'
option src_ip 'fe80::/10'
list icmp_type '130/0'
list icmp_type '131/0'
list icmp_type '132/0'
list icmp_type '143/0'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Input'
option src 'wan'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
list icmp_type 'router-solicitation'
list icmp_type 'neighbour-solicitation'
list icmp_type 'router-advertisement'
list icmp_type 'neighbour-advertisement'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Forward'
option src 'wan'
option dest '*'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-IPSec-ESP'
option src 'wan'
option dest 'lan'
option proto 'esp'
option target 'ACCEPT'
config rule
option name 'Allow-ISAKMP'
option src 'wan'
option dest 'lan'
option dest_port '500'
option proto 'udp'
option target 'ACCEPT'
config include
option path '/etc/firewall.user'
config zone
option input 'ACCEPT'
option forward 'REJECT'
option name 'iot'
option output 'ACCEPT'
option network 'IoT'
config forwarding
option dest 'lan'
option src 'wan'
config forwarding
option dest 'wan'
option src 'iot'
# head -n -0 /etc/firewall.user
# This file is interpreted as shell script.
# Put your custom iptables rules here, they will
# be executed with each firewall (re-)start.
# Internal uci firewall chains are flushed and recreated on reload, so
# put custom rules into the root chains e.g. INPUT or FORWARD or into the
# special user chains, e.g. input_wan_rule or postrouting_lan_rule.
# Fill DHCP checksums, try to work-around broken DHCP clients (such as FreeBSD).
# It requires iptables-mod-checksum which is installed by default in lxd-openwrt.
if [ -e /usr/lib/iptables/libxt_CHECKSUM.so ]; then
iptables -t mangle -A OUTPUT -p udp -m udp --dport 68 -j CHECKSUM --checksum-fill
fi
# iptables-save -c
# Generated by iptables-save v1.8.3 on Thu Jun 10 17:06:56 2021
*raw
:PREROUTING ACCEPT [4391:314077]
:OUTPUT ACCEPT [3633:373365]
:zone_iot_helper - [0:0]
:zone_lan_helper - [0:0]
[4343:311093] -A PREROUTING -i br-GRN -m comment --comment "!fw3: lan CT helper assignment" -j zone_lan_helper
[0:0] -A PREROUTING -i eth10.2 -m comment --comment "!fw3: iot CT helper assignment" -j zone_iot_helper
COMMIT
# Completed on Thu Jun 10 17:06:56 2021
# Generated by iptables-save v1.8.3 on Thu Jun 10 17:06:56 2021
*mangle
:PREROUTING ACCEPT [4391:314077]
:INPUT ACCEPT [3746:262477]
:FORWARD ACCEPT [0:0]
:OUTPUT ACCEPT [3635:373981]
:POSTROUTING ACCEPT [3635:373981]
[0:0] -A FORWARD -o red0 -p tcp -m tcp --tcp-flags SYN,RST SYN -m comment --comment "!fw3: Zone wan MTU fixing" -j TCPMSS --clamp-mss-to-pmtu
[0:0] -A FORWARD -i red0 -p tcp -m tcp --tcp-flags SYN,RST SYN -m comment --comment "!fw3: Zone wan MTU fixing" -j TCPMSS --clamp-mss-to-pmtu
[0:0] -A OUTPUT -p udp -m udp --dport 68 -j CHECKSUM --checksum-fill
COMMIT
# Completed on Thu Jun 10 17:06:56 2021
# Generated by iptables-save v1.8.3 on Thu Jun 10 17:06:56 2021
*nat
:PREROUTING ACCEPT [2800:204709]
:INPUT ACCEPT [2155:153109]
:OUTPUT ACCEPT [6:366]
:POSTROUTING ACCEPT [6:366]
:postrouting_iot_rule - [0:0]
:postrouting_lan_rule - [0:0]
:postrouting_rule - [0:0]
:postrouting_wan_rule - [0:0]
:prerouting_iot_rule - [0:0]
:prerouting_lan_rule - [0:0]
:prerouting_rule - [0:0]
:prerouting_wan_rule - [0:0]
:zone_iot_postrouting - [0:0]
:zone_iot_prerouting - [0:0]
:zone_lan_postrouting - [0:0]
:zone_lan_prerouting - [0:0]
:zone_wan_postrouting - [0:0]
:zone_wan_prerouting - [0:0]
[2800:204709] -A PREROUTING -m comment --comment "!fw3: Custom prerouting rule chain" -j prerouting_rule
[0:0] -A PREROUTING -i red0 -m comment --comment "!fw3" -j zone_wan_prerouting
[2800:204709] -A PREROUTING -i br-GRN -m comment --comment "!fw3" -j zone_lan_prerouting
[0:0] -A PREROUTING -i eth10.2 -m comment --comment "!fw3" -j zone_iot_prerouting
[6:366] -A POSTROUTING -m comment --comment "!fw3: Custom postrouting rule chain" -j postrouting_rule
[0:0] -A POSTROUTING -o red0 -m comment --comment "!fw3" -j zone_wan_postrouting
[0:0] -A POSTROUTING -o br-GRN -m comment --comment "!fw3" -j zone_lan_postrouting
[0:0] -A POSTROUTING -o eth10.2 -m comment --comment "!fw3" -j zone_iot_postrouting
[0:0] -A zone_iot_postrouting -m comment --comment "!fw3: Custom iot postrouting rule chain" -j postrouting_iot_rule
[0:0] -A zone_iot_prerouting -m comment --comment "!fw3: Custom iot prerouting rule chain" -j prerouting_iot_rule
[0:0] -A zone_lan_postrouting -m comment --comment "!fw3: Custom lan postrouting rule chain" -j postrouting_lan_rule
[2800:204709] -A zone_lan_prerouting -m comment --comment "!fw3: Custom lan prerouting rule chain" -j prerouting_lan_rule
[0:0] -A zone_wan_postrouting -m comment --comment "!fw3: Custom wan postrouting rule chain" -j postrouting_wan_rule
[0:0] -A zone_wan_postrouting -m comment --comment "!fw3" -j MASQUERADE
[0:0] -A zone_wan_prerouting -m comment --comment "!fw3: Custom wan prerouting rule chain" -j prerouting_wan_rule
[0:0] -A zone_wan_prerouting -p tcp -m tcp --dport 443 -m comment --comment "!fw3: HTTPs" -j DNAT --to-destination 192.168.7.101:443
COMMIT
# Completed on Thu Jun 10 17:06:56 2021
# Generated by iptables-save v1.8.3 on Thu Jun 10 17:06:56 2021
*filter
:INPUT ACCEPT [0:0]
:FORWARD DROP [0:0]
:OUTPUT ACCEPT [0:0]
:forwarding_iot_rule - [0:0]
:forwarding_lan_rule - [0:0]
:forwarding_rule - [0:0]
:forwarding_wan_rule - [0:0]
:input_iot_rule - [0:0]
:input_lan_rule - [0:0]
:input_rule - [0:0]
:input_wan_rule - [0:0]
:output_iot_rule - [0:0]
:output_lan_rule - [0:0]
:output_rule - [0:0]
:output_wan_rule - [0:0]
:reject - [0:0]
:syn_flood - [0:0]
:zone_iot_dest_ACCEPT - [0:0]
:zone_iot_dest_REJECT - [0:0]
:zone_iot_forward - [0:0]
:zone_iot_input - [0:0]
:zone_iot_output - [0:0]
:zone_iot_src_ACCEPT - [0:0]
:zone_lan_dest_ACCEPT - [0:0]
:zone_lan_forward - [0:0]
:zone_lan_input - [0:0]
:zone_lan_output - [0:0]
:zone_lan_src_ACCEPT - [0:0]
:zone_wan_dest_ACCEPT - [0:0]
:zone_wan_dest_DROP - [0:0]
:zone_wan_forward - [0:0]
:zone_wan_input - [0:0]
:zone_wan_output - [0:0]
:zone_wan_src_REJECT - [0:0]
[48:2984] -A INPUT -i lo -m comment --comment "!fw3" -j ACCEPT
[3739:261689] -A INPUT -m comment --comment "!fw3: Custom input rule chain" -j input_rule
[1345:91894] -A INPUT -m conntrack --ctstate RELATED,ESTABLISHED -m comment --comment "!fw3" -j ACCEPT
[1:60] -A INPUT -p tcp -m tcp --tcp-flags FIN,SYN,RST,ACK SYN -m comment --comment "!fw3" -j syn_flood
[0:0] -A INPUT -i red0 -m comment --comment "!fw3" -j zone_wan_input
[2394:169795] -A INPUT -i br-GRN -m comment --comment "!fw3" -j zone_lan_input
[0:0] -A INPUT -i eth10.2 -m comment --comment "!fw3" -j zone_iot_input
[0:0] -A FORWARD -m comment --comment "!fw3: Custom forwarding rule chain" -j forwarding_rule
[0:0] -A FORWARD -m conntrack --ctstate RELATED,ESTABLISHED -m comment --comment "!fw3" -j ACCEPT
[0:0] -A FORWARD -i red0 -m comment --comment "!fw3" -j zone_wan_forward
[0:0] -A FORWARD -i br-GRN -m comment --comment "!fw3" -j zone_lan_forward
[0:0] -A FORWARD -i eth10.2 -m comment --comment "!fw3" -j zone_iot_forward
[0:0] -A FORWARD -m comment --comment "!fw3" -j reject
[48:2984] -A OUTPUT -o lo -m comment --comment "!fw3" -j ACCEPT
[3626:382497] -A OUTPUT -m comment --comment "!fw3: Custom output rule chain" -j output_rule
[3626:382497] -A OUTPUT -m conntrack --ctstate RELATED,ESTABLISHED -m comment --comment "!fw3" -j ACCEPT
[0:0] -A OUTPUT -o red0 -m comment --comment "!fw3" -j zone_wan_output
[0:0] -A OUTPUT -o br-GRN -m comment --comment "!fw3" -j zone_lan_output
[0:0] -A OUTPUT -o eth10.2 -m comment --comment "!fw3" -j zone_iot_output
[0:0] -A reject -p tcp -m comment --comment "!fw3" -j REJECT --reject-with tcp-reset
[0:0] -A reject -m comment --comment "!fw3" -j REJECT --reject-with icmp-port-unreachable
[1:60] -A syn_flood -p tcp -m tcp --tcp-flags FIN,SYN,RST,ACK SYN -m limit --limit 25/sec --limit-burst 50 -m comment --comment "!fw3" -j RETURN
[0:0] -A syn_flood -m comment --comment "!fw3" -j DROP
[0:0] -A zone_iot_dest_ACCEPT -o eth10.2 -m comment --comment "!fw3" -j ACCEPT
[0:0] -A zone_iot_dest_REJECT -o eth10.2 -m comment --comment "!fw3" -j reject
[0:0] -A zone_iot_forward -m comment --comment "!fw3: Custom iot forwarding rule chain" -j forwarding_iot_rule
[0:0] -A zone_iot_forward -m comment --comment "!fw3: Zone iot to wan forwarding policy" -j zone_wan_dest_ACCEPT
[0:0] -A zone_iot_forward -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port forwards" -j ACCEPT
[0:0] -A zone_iot_forward -m comment --comment "!fw3" -j zone_iot_dest_REJECT
[0:0] -A zone_iot_input -m comment --comment "!fw3: Custom iot input rule chain" -j input_iot_rule
[0:0] -A zone_iot_input -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port redirections" -j ACCEPT
[0:0] -A zone_iot_input -m comment --comment "!fw3" -j zone_iot_src_ACCEPT
[0:0] -A zone_iot_output -m comment --comment "!fw3: Custom iot output rule chain" -j output_iot_rule
[0:0] -A zone_iot_output -m comment --comment "!fw3" -j zone_iot_dest_ACCEPT
[0:0] -A zone_iot_src_ACCEPT -i eth10.2 -m conntrack --ctstate NEW,UNTRACKED -m comment --comment "!fw3" -j ACCEPT
[0:0] -A zone_lan_dest_ACCEPT -o br-GRN -m comment --comment "!fw3" -j ACCEPT
[0:0] -A zone_lan_forward -m comment --comment "!fw3: Custom lan forwarding rule chain" -j forwarding_lan_rule
[0:0] -A zone_lan_forward -m comment --comment "!fw3: Zone lan to wan forwarding policy" -j zone_wan_dest_ACCEPT
[0:0] -A zone_lan_forward -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port forwards" -j ACCEPT
[0:0] -A zone_lan_forward -m comment --comment "!fw3" -j zone_lan_dest_ACCEPT
[2394:169795] -A zone_lan_input -m comment --comment "!fw3: Custom lan input rule chain" -j input_lan_rule
[0:0] -A zone_lan_input -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port redirections" -j ACCEPT
[2394:169795] -A zone_lan_input -m comment --comment "!fw3" -j zone_lan_src_ACCEPT
[0:0] -A zone_lan_output -m comment --comment "!fw3: Custom lan output rule chain" -j output_lan_rule
[0:0] -A zone_lan_output -m comment --comment "!fw3" -j zone_lan_dest_ACCEPT
[2394:169795] -A zone_lan_src_ACCEPT -i br-GRN -m conntrack --ctstate NEW,UNTRACKED -m comment --comment "!fw3" -j ACCEPT
[0:0] -A zone_wan_dest_ACCEPT -o red0 -m conntrack --ctstate INVALID -m comment --comment "!fw3: Prevent NAT leakage" -j DROP
[0:0] -A zone_wan_dest_ACCEPT -o red0 -m comment --comment "!fw3" -j ACCEPT
[0:0] -A zone_wan_dest_DROP -o red0 -m comment --comment "!fw3" -j DROP
[0:0] -A zone_wan_forward -m comment --comment "!fw3: Custom wan forwarding rule chain" -j forwarding_wan_rule
[0:0] -A zone_wan_forward -p esp -m comment --comment "!fw3: Allow-IPSec-ESP" -j zone_lan_dest_ACCEPT
[0:0] -A zone_wan_forward -p udp -m udp --dport 500 -m comment --comment "!fw3: Allow-ISAKMP" -j zone_lan_dest_ACCEPT
[0:0] -A zone_wan_forward -m comment --comment "!fw3: Zone wan to lan forwarding policy" -j zone_lan_dest_ACCEPT
[0:0] -A zone_wan_forward -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port forwards" -j ACCEPT
[0:0] -A zone_wan_forward -m comment --comment "!fw3" -j zone_wan_dest_DROP
[0:0] -A zone_wan_input -m comment --comment "!fw3: Custom wan input rule chain" -j input_wan_rule
[0:0] -A zone_wan_input -p udp -m udp --dport 68 -m comment --comment "!fw3: Allow-DHCP-Renew" -j ACCEPT
[0:0] -A zone_wan_input -p icmp -m icmp --icmp-type 8 -m comment --comment "!fw3: Allow-Ping" -j ACCEPT
[0:0] -A zone_wan_input -p igmp -m comment --comment "!fw3: Allow-IGMP" -j ACCEPT
[0:0] -A zone_wan_input -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port redirections" -j ACCEPT
[0:0] -A zone_wan_input -m comment --comment "!fw3" -j zone_wan_src_REJECT
[0:0] -A zone_wan_output -m comment --comment "!fw3: Custom wan output rule chain" -j output_wan_rule
[0:0] -A zone_wan_output -m comment --comment "!fw3" -j zone_wan_dest_ACCEPT
[0:0] -A zone_wan_src_REJECT -i red0 -m comment --comment "!fw3" -j reject
COMMIT
# Completed on Thu Jun 10 17:06:56 2021
# ip -4 addr ; ip -4 ro li tab all ; ip -4 ru
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN qlen 1000
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
5: br-GRN: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP qlen 1000
inet 192.168.7.1/24 brd 192.168.7.255 scope global br-GRN
valid_lft forever preferred_lft forever
192.168.7.0/24 dev br-GRN scope link src 192.168.7.1
broadcast 127.0.0.0 dev lo table local scope link src 127.0.0.1
local 127.0.0.0/8 dev lo table local scope host src 127.0.0.1
local 127.0.0.1 dev lo table local scope host src 127.0.0.1
broadcast 127.255.255.255 dev lo table local scope link src 127.0.0.1
broadcast 192.168.7.0 dev br-GRN table local scope link src 192.168.7.1
local 192.168.7.1 dev br-GRN table local scope host src 192.168.7.1
broadcast 192.168.7.255 dev br-GRN table local scope link src 192.168.7.1
0: from all lookup local
32766: from all lookup main
32767: from all lookup default
The VLAN is there because once I get basic LAN working, I plan to get a Guest and IoT WiFis connected from the AP to the OpenWRT router.
trendy
June 10, 2021, 3:29pm
14
The wan (or red) interface seems down. There is no IP, nor gateway. Check that it gets settings from the dhcp server first and then post again if there is still an issue. The configuration is more or less fine.
1 Like
WAN is down because the cable was unplugged. When it is plugged in, it gets the settings through DHCP no problem and I can access internet from the router itself.
@ Chatmandu
trendy
June 10, 2021, 7:15pm
17
Well, what is the point of posting a running configuration with wan down?
1 Like
The WAN side is working fine, so I did not think it would make a difference.
trendy
June 11, 2021, 8:45am
19
It would, if there is some IP conflict for example.
I appreciate you trying to help.https://pastebin.com/raw/NjmNMgFk
trendy
June 13, 2021, 6:44pm
21
There are no hits on the firewall for packets coming in from the lan and going to the wan[0:0] -A zone_lan_forward -m comment --comment "!fw3: Zone lan to wan forwarding policy" -j zone_wan_dest_ACCEPT
1 Like
There is one LAN machine connected and that's the one I am using to access OpenWRT through SSH.google.com , all timing out.