Hello! I'm trying to "upgrade" from DietPi + manual settings + Pi Hole + Unbound to OpenWrt + AdGuardHome + <something else?> on my Raspberry Pi 3B+.
My reason for the "upgrade" is that with OpenWrt I'll have more (advanced) control over the network, the manual settings I had previously.
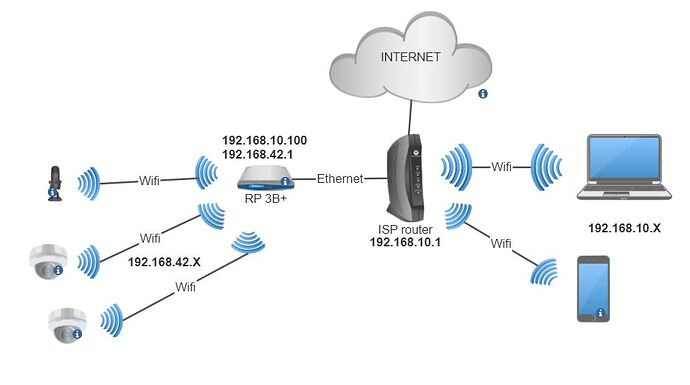
This is my network currently:
The ISP router has its DHCP server off. The Raspberry has a DHCP server for the 192.168.10.X network, that comes from ethernet from the Wifi clients connected to ISP router and (another?) DHCP server for the 192.168.42.X network for the devices that connect to the internal Wifi of the Raspberry that's in hotspot/ap mode.
The idea here is to have the unimportant/guest devices in a separated network from the main devices and all protected with the same instance of Pi Hole. If the ISP folks weren't such cof cof I could do this without this mess but they blocked the DNS settings of it.
I know that this could be achieved in a better way but I wanted to use the hardware available here instead of buying new one.
So far it works, but like I said, I wish I had more control and more security over what's going on in the network (eg I don't really know what devices are connected to the guest network in real time).
Backstory out of the way, I'm trying to replicate this with OpenWrt. I was able to have the two separated networks in the same way however I'm struggling to have them connect to the Internet. The Raspberry Pi (openWrt) itself has access to it, tested with ping to openwrt.org, however none of the devices of both networks have access to it. I already tried a few different settings but nothing worked. This is what I have at the moment:
network
config interface 'loopback'
option device 'lo'
option proto 'static'
option ipaddr '127.0.0.1'
option netmask '255.0.0.0'
config globals 'globals'
option ula_prefix 'fd8a:f1f3:73b3::/48'
config device
option name 'br-lan'
option type 'bridge'
list ports 'eth0'
config interface 'lan'
option device 'eth0'
option proto 'static'
option ipaddr '192.168.10.100'
option netmask '255.255.255.0'
option gateway '192.168.10.1'
option broadcast '192.168.10.255'
list dns '8.8.8.8'
config interface 'wlan'
option proto 'static'
option ipaddr '192.168.42.100'
option netmask '255.255.255.0'
option gateway '192.168.10.1'
option device 'phy0-ap0'
list dns '8.8.8.8'
wireless
config wifi-device 'radio0'
option type 'mac80211'
option path 'platform/soc/3f300000.mmcnr/mmc_host/mmc1/mmc1:0001/mmc1:0001:1'
option channel '1'
option band '2g'
option htmode 'HT20'
option cell_density '1'
option country 'PT'
config wifi-iface 'wifinet0'
option device 'radio0'
option mode 'ap'
option ssid '************'
option encryption 'psk2'
option key '************'
option wmm '0'
dhcp
config dnsmasq
option domainneeded '1'
option boguspriv '1'
option filterwin2k '0'
option localise_queries '1'
option rebind_protection '1'
option rebind_localhost '1'
option local '/lan/'
option domain 'lan'
option expandhosts '1'
option nonegcache '0'
option cachesize '1000'
option authoritative '1'
option readethers '1'
option leasefile '/tmp/dhcp.leases'
option resolvfile '/tmp/resolv.conf.d/resolv.conf.auto'
option nonwildcard '1'
option localservice '1'
option ednspacket_max '1232'
option filter_aaaa '0'
option filter_a '0'
config dhcp 'lan'
option interface 'lan'
option start '10'
option limit '100'
option leasetime '24h'
option dhcpv4 'server'
option dhcpv6 'hybrid'
option ra 'hybrid'
list ra_flags 'managed-config'
list ra_flags 'other-config'
config odhcpd 'odhcpd'
option maindhcp '0'
option leasefile '/tmp/hosts/odhcpd'
option leasetrigger '/usr/sbin/odhcpd-update'
option loglevel '4'
config dhcp 'wlan'
option interface 'wlan'
option start '10'
option limit '100'
option leasetime '24h'
firewall
config defaults
option input 'REJECT'
option output 'ACCEPT'
option forward 'REJECT'
option synflood_protect '1'
config zone
option name 'lan'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'ACCEPT'
list network 'lan'
config zone
option name 'wlan'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'ACCEPT'
list network 'wlan'
config zone
option name 'wan'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'REJECT'
option masq '1'
option mtu_fix '1'
list network 'wan6'
config forwarding
option src 'lan'
option dest 'wan'
config rule
option name 'Allow-DHCP-Renew'
option src 'wan'
option proto 'udp'
option dest_port '68'
option target 'ACCEPT'
option family 'ipv4'
config rule
option name 'Allow-Ping'
option src 'wan'
option proto 'icmp'
option icmp_type 'echo-request'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-IGMP'
option src 'wan'
option proto 'igmp'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-DHCPv6'
option src 'wan'
option proto 'udp'
option dest_port '546'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-MLD'
option src 'wan'
option proto 'icmp'
option src_ip 'fe80::/10'
list icmp_type '130/0'
list icmp_type '131/0'
list icmp_type '132/0'
list icmp_type '143/0'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Input'
option src 'wan'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
list icmp_type 'router-solicitation'
list icmp_type 'neighbour-solicitation'
list icmp_type 'router-advertisement'
list icmp_type 'neighbour-advertisement'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Forward'
option src 'wan'
option dest '*'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-IPSec-ESP'
option src 'wan'
option dest 'lan'
option proto 'esp'
option target 'ACCEPT'
config rule
option name 'Allow-ISAKMP'
option src 'wan'
option dest 'lan'
option dest_port '500'
option proto 'udp'
option target 'ACCEPT'
config forwarding
option src 'wlan'
option dest 'wan'
Model
Raspberry Pi 3B/3B+/3CM (64bit) / Raspberry Pi 2B-1.2 (64bit)
Platform bcm27xx/bcm2710
Version 22.03.5 (r20134-5f15225c1e)
I can't just copy the settings I have from the previous configuration to this one, right?
So if anyone could help me on how to do it I would appreciate (preferably with the LuCI web interface).
PS: I know that after installing AdGuardHome some settings on these will change. For now I just want Internet on all devices to see how they perform.