mk24
July 15, 2022, 10:51pm
101
Yes. In the wan section of /etc/config/network (assuming it is proto dhcp), set peerdns to 0 and add the DNS IPs there with list dns.
Since those servers aren't reachable from outside the tunnel, DNS will stop working if the tunnel goes down-- so you'll need to reconfigure back to regular DNS if you ever need the Pi to reach the Internet to fix that.
And that's why I probably don't have internet acces right now. I am with my phone (wirelessly) connected to my Pi and I don't have internet access.
Is that also because I did not (yet) configure my firewall for my interface?
mk24
July 15, 2022, 10:55pm
103
Yes you need that firewall setting because the LAN has to NAT into the tunnel the same as it NATs into the regular Internet. NAT (masq) is enabled on the wan zone by default.
From the router CLI, do a traceroute to a numeric IP like 8.8.8.8 (or even better, Nord's private DNS server). It should show that it is going through the tunnel and out into the other country. Then try a traceroute to a named site to see if DNS works.
Do you have some firewall configurations for my so I can apply them?
I will do the traceroute in the background.
mk24
July 15, 2022, 10:59pm
105
Since this is the simple case of sending everything unfiltered into the tunnel, you just need to add that one line.
Also like any routing situation, the Pi's LAN has to be a different subnet than your home LAN which is immediately upstream.
mk24
July 15, 2022, 11:01pm
107
MennoEmmerik:
list device 'wg0'
Yes. Put it in the config zone named wan.
This is assuming you haven't changed anything in the firewall from default.
1 Like
Yeah I did that, but since then I do not have an internet connection anymore.
mk24
July 15, 2022, 11:04pm
109
Actually since you've named the wireguard interface interface_wg instead of the conventional wg0, you need to use your name.
Then examine your routing table by running route with no parameters.
Bill
July 15, 2022, 11:05pm
110
Catch us all up:
From the CLI run
ip route show default; uci export network; uci export firewall
1 Like
I will do that.
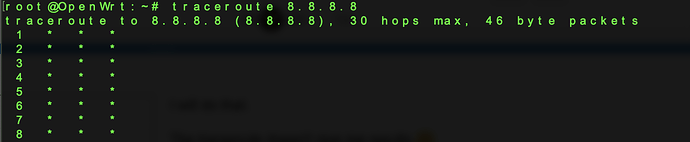
The traceroute doesn't give me results
mk24
July 15, 2022, 11:06pm
112
Bill:
Catch us all up:
Another very viable option is to reset the router to defaults and start over now that you somewhat know what needs to be done.
Make sure to kill your Linux VM because if two connections are both running at the same time with the same keys, the server doesn't know what to do.
1 Like
Also an option.
That's also an good to know fact.
Bill
July 15, 2022, 11:08pm
114
> BusyBox v1.35.0 (2022-07-06 19:09:39 UTC) built-in shell (ash)
>
> _______ ________ __
> | |.-----.-----.-----.| | | |.----.| |_
> | - || _ | -__| || | | || _|| _|
> |_______|| __|_____|__|__||________||__| |____|
> |__| W I R E L E S S F R E E D O M
> -----------------------------------------------------
> OpenWrt 22.03.0-rc5, r19523-bfd070e7fa
> -----------------------------------------------------
> root@Dachshund:~# traceroute 8.8.8.8
> traceroute to 8.8.8.8 (8.8.8.8), 30 hops max, 46 byte packets
> 1 * * *
> 2 * * *
> 3 * * *
> 4 * * *
> 5 * * *
> 6 * * *
> 7 * * *
> 8 * * *
> 9 * * *
> 10 * * *
> 11 * * *
> 12 * * *
> 13 * * *
> 14 * * *
> 15 * * *
> 16 * * *
> 17 * * *
> 18 * * *
> 19 * * *
> 20 * * *
> 21 * * *
> 22 * * *
> 23 * * *
> 24 * * *
> 25 * * *
> 26 * * *
> 27 * * *
> 28 * * *
> 29 * * *
> 30 * * *
> root@Dachshund:~#
Don't worry about that.. I had the same on my known good wg0 tunnel
I did this.
And this was the result:
root@OpenWrt:~# ip route show default; uci export network; uci export firewall
default dev dutch scope link
192.168.1.0/24 dev wlan0 scope link src 192.168.1.3
213.152.188.241 via 192.168.1.1 dev wlan0
package network
config interface 'loopback'
option device 'lo'
option proto 'static'
option ipaddr '127.0.0.1'
option netmask '255.0.0.0'
config globals 'globals'
option ula_prefix 'fdf2:a309:9b81::/48'
config device
option name 'br-lan'
option type 'bridge'
list ports 'eth0'
config interface 'lan'
option device 'br-lan'
option proto 'static'
option ipaddr '192.168.1.1'
option netmask '255.255.255.0'
option ip6assign '60'
option force_link '1'
option ip4table '1'
option ip6table '1'
config interface 'wwan'
option proto 'dhcp'
option peerdns '0'
option dns '103.86.96.100 103.86.99.100'
config rule 'lan_wan'
option in 'lan'
option lookup '2'
option priority '40000'
config rule6 'lan_wan6'
option in 'lan'
option lookup '2'
option priority '40000'
config interface 'dutch'
option proto 'wireguard'
option private_key '<private-key>'
config wireguard_dutch
list allowed_ips '0.0.0.0/0'
option endpoint_host '213.152.188.241'
option endpoint_port '51820'
option persistent_keepalive '25'
option public_key '<public-key>'
option route_allowed_ips '1'
package firewall
config defaults
option syn_flood '1'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'REJECT'
config zone
option name 'lan'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'ACCEPT'
list network 'lan'
config zone
option name 'wan'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'REJECT'
option masq '1'
option mtu_fix '1'
list network 'wan'
list network 'wan6'
list network 'wwan'
list device 'dutch'
config forwarding
option src 'lan'
option dest 'wan'
config rule
option name 'Allow-DHCP-Renew'
option src 'wan'
option proto 'udp'
option dest_port '68'
option target 'ACCEPT'
option family 'ipv4'
config rule
option name 'Allow-Ping'
option src 'wan'
option proto 'icmp'
option icmp_type 'echo-request'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-IGMP'
option src 'wan'
option proto 'igmp'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-DHCPv6'
option src 'wan'
option proto 'udp'
option src_ip 'fc00::/6'
option dest_ip 'fc00::/6'
option dest_port '546'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-MLD'
option src 'wan'
option proto 'icmp'
option src_ip 'fe80::/10'
list icmp_type '130/0'
list icmp_type '131/0'
list icmp_type '132/0'
list icmp_type '143/0'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Input'
option src 'wan'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
list icmp_type 'router-solicitation'
list icmp_type 'neighbour-solicitation'
list icmp_type 'router-advertisement'
list icmp_type 'neighbour-advertisement'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Forward'
option src 'wan'
option dest '*'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-IPSec-ESP'
option src 'wan'
option dest 'lan'
option proto 'esp'
option target 'ACCEPT'
config rule
option name 'Allow-ISAKMP'
option src 'wan'
option dest 'lan'
option dest_port '500'
option proto 'udp'
option target 'ACCEPT'
config rule
option name 'Support-UDP-Traceroute'
option src 'wan'
option dest_port '33434:33689'
option proto 'udp'
option family 'ipv4'
option target 'REJECT'
option enabled 'false'
config include
option path '/etc/firewall.user'
config zone
option name 'wg_dutch'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'REJECT'
config forwarding
option src 'wg_dutch'
option dest 'lan'
config forwarding
option src 'wg_dutch'
option dest 'wan
Also my ping doesn't work
mk24
July 15, 2022, 11:18pm
117
You don't need multiple route tables or a separate firewall zone (which will not work the way you have it since there is no assigned device or network).
It is looking better and better to start over. Do copy out your network file which has the working keys, but only reuse that part.
1 Like
you're missing an address here.
1 Like
mk24
July 15, 2022, 11:19pm
119
And that too. Copy the wireguard config parameters exactly from the Linux machine.
Okay, then I will start over and use the network file for coping things over