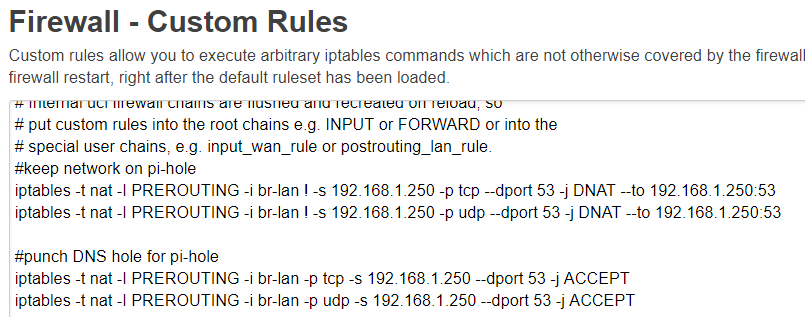
Hi, i tried to force all clients on LAN to use my local DNS server (even if the explicitly use different one). I tried 2 ways - an openwrt guide for luci with help of zones & port forwards, and also second way of custom iptables rules Redirect All Outbound DNS Traffic to Internal IP .
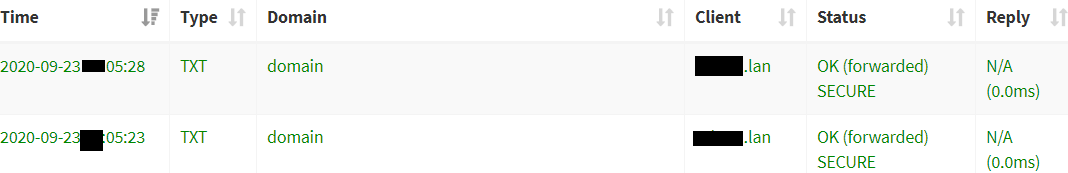
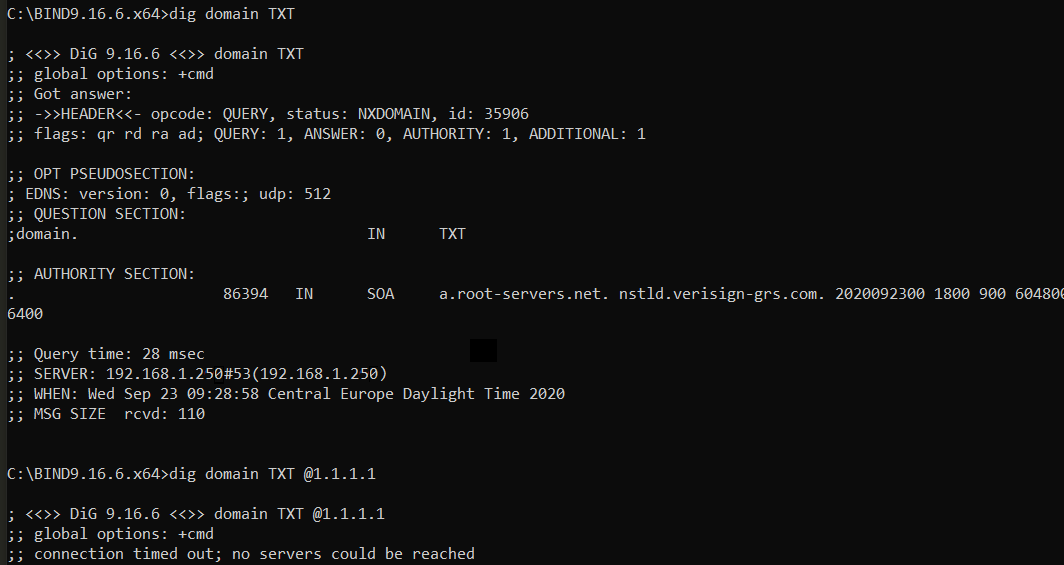
Im partially succesfull - in both cases, when i try to "dig domain @1.1.1.1" from a client, i can see it was succesfully forwarded to my DNS server. in my DNS server log i can see 3 requests for the domain, but then a timeout reply on a client.
If i try just "dig domain" it is correctly responded by my local DNS server.
Make sure to exclude your DNS server from the redirect rule.
Apply invert source IP or IP set match, or utilize DNS encryption.
that's already done, without that my local DNS wouldnt work at all
When querying my local DNS - it is able to find and provide an answer.
When querying external DNS from any client that is not my local DNS server, the query is hijacked and forward to my local DNS (as seen in local DNS server logs). But then the reply to the client seems to be lost
iptables -t nat -A postrouting_lan_rule -d 192.168.178.11 -p tcp -m tcp --dport 53 -m comment --comment "!fw3: DNS MASQ DNS QUERIES" -j MASQUERADE
iptables -t nat -A postrouting_lan_rule -d 192.168.178.11 -p udp -m udp --dport 53 -m comment --comment "!fw3: DNS MASQ DNS QUERIES" -j MASQUERADE
192.168.178.11 <-- replace this with the IP of your DNS server.
although it hinders my DNS server statistics with showing only the router IP as the query source, it works. The client gets a reply from my local DNS server even if they specify external DNS. thanks
Masquerade is necessary to make the client "think" the answer is comming from the source (in your case 1.1.1.1) it was asking. As a side effect your DNS server cannot log the query source anymore because its always your routers IP.
If you would use DNSmasq in between (redirect to 192.168.1.1 first and forward to 192.168.1.250 by DNSmasq) you could still log client quieries on your router (if necessary).
SNAT/Masquerade is only necessary when in the same zone, so the Pihole will not respond directly to the host and trigger the "reply from unexpected source".
This topic was automatically closed 10 days after the last reply. New replies are no longer allowed.