Curious if anyone is willing to advise on the best way to setup a global printer on a network made up of multiple VLANS. I'm thinking put the printer on a separate VLAN on its on firewall zone. All access from all networks to the this firewall zone as well as creating static routes from each VLAN.
Should be fine. And you won't need static routes if all the vlans are connecting to the same router. All devices will use default gateway the appropriate subinterface IP of the router for their designated vlan.
I guess if you're scared of the printer.
Your ideas about a new VLAN sounds OK.
You just have to allow forward to that firewall zone you create for the printer and the VLAN interface from the LAN.
Hardly tinfoil-hat to not trust a printer
I wouldn't configure a printer to be "global."
But I know of some applications where just sending a print to a port on the Internet is like the new faxing.
By "global" I think you mean "common for use by all the VLANS" not "available to anyone on the internet" right?
Your idea of a separate VLAN for the printer sounds fine, just set up the firewalls to forward TO the printer. You will not get "automatic" discovery of your printer in this setup though.
When I say global, I meant interanet internal network company wide. Not having it open to print from the internet. Its an odd requirement. They want to silo 3 firms private networks with VLANS in one building but allow all three firms to print to a large printer downstairs in a reception area.
Not that strange -- broadly applies, such as to a home situation where the "trusted" machines and those on a guest network both would like to print, but should remain as separate as possible.
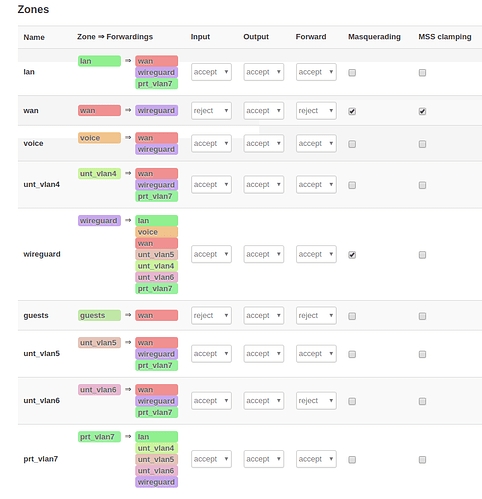
Would it be best to create a separate VLAN for printers and use firewall zones, or bridge the printer VLAN with the other VLANs, or both? I've currently setup it this way about to reboot and statically assign printers addresses in VLAN7
I was also considering using a DHCP option e.g. 132 that would tell the DHCP server to give the printers an address in VLAN7, however, they do need to be static. This would allow for not have to accommodate specific hardware ports on the switch to printers only.
Yes
This will create one big LAN. I am not sure that you want that.
That is not possible.
It is not so clear why do you forward from wan to wireguard and back. Are you certain you want that?
No need for any special option. You can give static leases under Network-DHCP and DNS. Also make sure that the DHCP is enabled for the interface on Vlan7. That should do it.
You don't want to give forwarding priveleges to any zone unless that zone should be able to initiate connections to the other zone.
So printer zone should have zero forwarding priveleges. All other zones should be able to forward to the printer zone. Connection tracking takes care of reply traffic.
And printer zone should have zero input or forward allowed policy.
Input policy should be reject for all vlans except the one you configure for management.
@dlakelan I so appreciate the security input you shared, thank you! The printer does need to be able to send scanned email to an smtp gateway so initiating connections was a requirement. @trendy your input as well! Entire setup is running like a charm now. The only issues I had were applying SQM to specific VLAN interfaces and allowing AP mode to disconnect STAs based on low ACK condition. 30 wireless endpoints kept getting booted then rejoining. Turned off the advanced feature and all went well today.
Disallow printer forwarding in policy and then add a specific traffic rule for this specific service ![]()
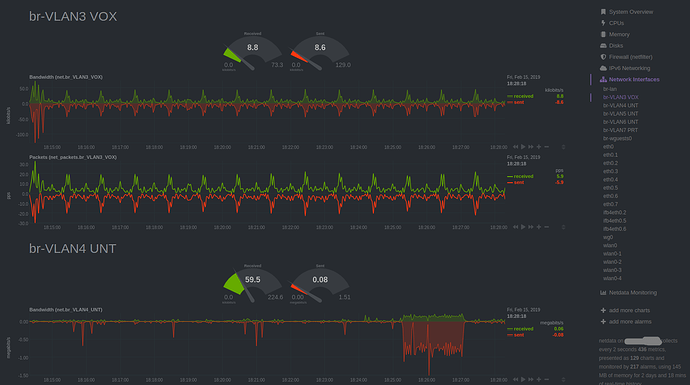
Nice! Will do, thanks! Here is some NetData eye candy for this good Friday monitoring this setup. Cheers.
No problem. You might also disallow all forwarding TO the printer vlan (except from admin vlan) and set a traffic rule allowing access to the specific printing port.