Hello all,
I am using OpenWRT since a while and were able to configure some settings, like multiple wifis and vlans.
Also managing ports was not a problem in the past. But currently I am stuck and out of ideas. I went trough several posts and checked if there is anything that might help me. So far I had no luck.
I try to get a certificate from Let's encrypt, but it fails and hints to a firewall issue. I checked with two different PortScanners from outside, if the port 443 is open, no luck. Only ports 80 and 53 are open. I don't understand, why 53 is open, as I didn't setup any rule for that.
My setup is plain. ISP modem -> Router (OpenWRT 18.06.02) - > Server. Router and Server are in the same vlan.
Firewall Server
To Action From
-- ------ ----
[ 1] 80,443/tcp ALLOW IN Anywhere
My /etc/config/firewall is
Note: I do not have any additional rules in /etc/firewall.user
config defaults
option syn_flood '1'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'REJECT'
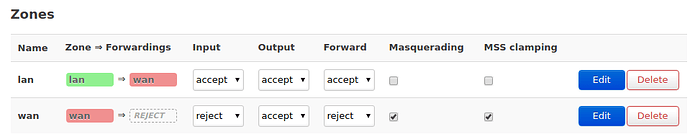
config zone
option name 'lan'
option output 'ACCEPT'
option forward 'ACCEPT'
option network 'lan'
option masq '1'
option input 'ACCEPT'
config zone
option name 'wan'
option output 'ACCEPT'
option masq '1'
option network 'wan wan6'
option input 'ACCEPT'
option forward 'ACCEPT'
option mtu_fix '1'
config rule
option name 'Allow-DHCP-Renew'
option src 'wan'
option proto 'udp'
option dest_port '68'
option target 'ACCEPT'
option family 'ipv4'
config rule
option name 'Allow-Ping'
option src 'wan'
option proto 'icmp'
option icmp_type 'echo-request'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-IGMP'
option src 'wan'
option proto 'igmp'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-DHCPv6'
option src 'wan'
option proto 'udp'
option src_ip 'fc00::/6'
option dest_ip 'fc00::/6'
option dest_port '546'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-MLD'
option src 'wan'
option proto 'icmp'
option src_ip 'fe80::/10'
list icmp_type '130/0'
list icmp_type '131/0'
list icmp_type '132/0'
list icmp_type '143/0'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Input'
option src 'wan'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
list icmp_type 'router-solicitation'
list icmp_type 'neighbour-solicitation'
list icmp_type 'router-advertisement'
list icmp_type 'neighbour-advertisement'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Forward'
option src 'wan'
option dest '*'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-IPSec-ESP'
option src 'wan'
option dest 'lan'
option proto 'esp'
option target 'ACCEPT'
config rule
option name 'Allow-ISAKMP'
option src 'wan'
option dest 'lan'
option dest_port '500'
option proto 'udp'
option target 'ACCEPT'
config include
option path '/etc/firewall.user'
config zone
option name 'guest'
option forward 'REJECT'
option output 'ACCEPT'
option network 'guest'
option input 'REJECT'
config forwarding
option dest 'wan'
option src 'guest'
config rule
option target 'ACCEPT'
option proto 'tcp udp'
option dest_port '53'
option name 'Guest-DNS'
option src 'guest'
config rule
option target 'ACCEPT'
option proto 'udp'
option dest_port '67-68'
option name 'Guest-DHCP'
option src 'guest'
config zone
option forward 'REJECT'
option output 'ACCEPT'
option name 'home'
option network 'home'
option input 'ACCEPT'
option masq '1'
config forwarding
option dest 'wan'
option src 'home'
config rule
option target 'ACCEPT'
option proto 'tcp udp'
option dest_port '53'
option name 'Home-DNS'
option src 'home'
config rule
option target 'ACCEPT'
option proto 'udp'
option dest_port '67-68'
option name 'Home-DHCP'
option src 'home'
config forwarding
option dest 'wan'
option src 'lan'
config forwarding
option dest 'lan'
option src 'wan'
config redirect
option target 'DNAT'
option src 'wan'
option dest 'lan'
option proto 'tcp'
option src_dport '443'
option dest_port '443'
option name 'NextCloud HTTPS'
option dest_ip '192.168.22.130'
option enabled '0'
config redirect
option target 'DNAT'
option src 'wan'
option dest 'lan'
option proto 'tcp'
option src_dport '80'
option dest_port '80'
option name 'NextCloud HTTP'
option dest_ip '192.168.22.130'
option enabled '0'
config rule
option target 'ACCEPT'
option src 'wan'
option proto 'tcp'
option dest_port '443'
option name 'HTTPS'
option enabled '0'
config rule
option target 'ACCEPT'
option src 'wan'
option proto 'tcp'
option dest_port '443'
option name 'HTTPS forward'
option family 'ipv4'
option src_port '443'
option dest 'lan'
option enabled '0'
config redirect
option target 'SNAT'
option src 'lan'
option dest 'wan'
option proto 'all'
option src_dip '192.168.22.1'
option name 'HTTPS SNAT'
option src_ip '192.168.22.130'
option enabled '0'
My thought was, that the router is using the port 443 already and some configuration I don't know might prevent me to open or forward the port to not expose the router. There is this uhttpd process, that makes me think that way.
/usr/sbin/uhttpd -f -h /www -r OpenWrt -x /cgi-bin -t 60 -T 30 -k 20 -A 1 -n 3 -N 100 -R -p 0.0.0.0:80 -p [::]:80 -C /etc/uhttpd.crt -K /etc/uhttpd.key -s 0.0.0.0:443 -s [::]:443 -q
I already remove uhttpd via opkg, but it seems there are still some leftovers.
I hope you can help me and I can make progress.
Thanks,
Sputnik