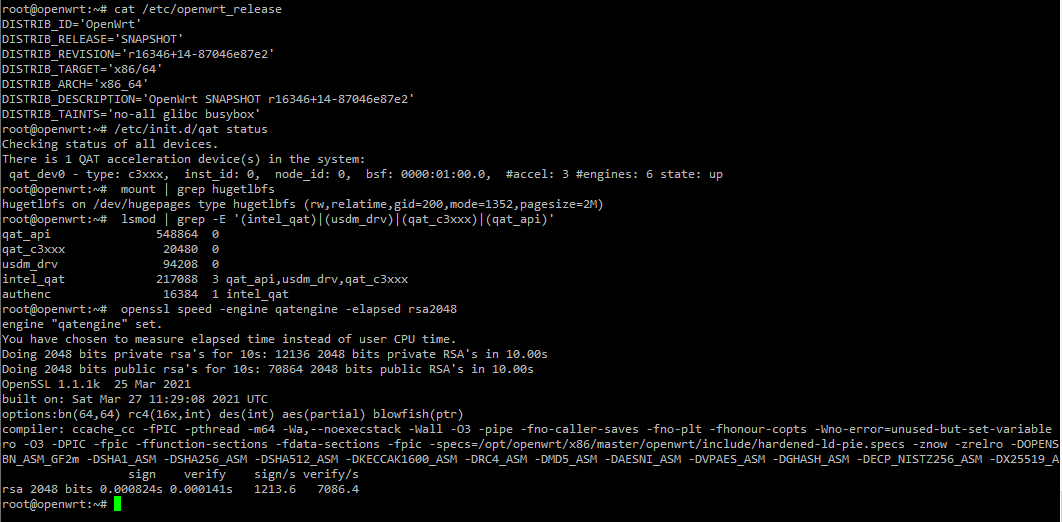
Yes, of course. See image below: it shows my openwrt release (it's about a year and a half old version of Master), the QAT driver status as being loaded, the Intel QAT kernel modules loaded, the hugetables filesystem loaded (used by QAT's contiguous memory driver) and a run of an openssl speed test for RSA using the QAT engine.
My build is using glibc and has a custom kernel obviously, not only because of the QAT drivers, but also because it has some optimizations for a non-resource-constrained system. These used to be many, but in recent years the x86_64 build has improved considerably and the kernel config is much better now than it was, say 10 years ago.
I have, however, noted to you in a previous reply that it is pointless implementing QAT on OpenWRT as the workloads are a mismatch and AES-NI outperforms it by a large margin.
Intel QAT only outperforms AES-NI when there are multiple asynchronous processes doing crypto operations on large buffers simultaneously.
Performing AES operations on anything less than an 8K sized buffer is much quicker using AES-NI than Intel's QAT engine.
This is because a lot of data needs to be shunted across the bus to the QAT hardware, whereas AES-NI is a CPU instruction.
Furthermore, the speed of the openssl AES software implementation suffers considerably when not offloading due to engine related polling that happens when the QAT engine is compiled into openssl, resulting in up to a 40% performance hit for small buffer sized, software-based encryption/decryption (Intel is aware of this - the Intel folk responsible for QAT gave me some good assistance and support while I was porting it, extending to giving me access even to updated code at the time that they'd not yet published).
So, as a result of this polling-related inefficiency, even though I have QAT installed on my openwrt, I deliberately compile QAT's AES implementation out, since 1.) I never use it as it performs like a dog and 2.) it slows down the software implementation that I DO use by 40%.
Please read this long thread for more insight into hardware crypto engines on OpenWRT and more specifically QAT: https://forum.openwrt.org/t/which-wifi-routers-have-hardware-aes-encryption-support. There's lots of useful information, explanations and benchmarks.
Here's the port of Intel QAT to OpenWRT: https://github.com/dl12345/quickassist-openwrt-denverton
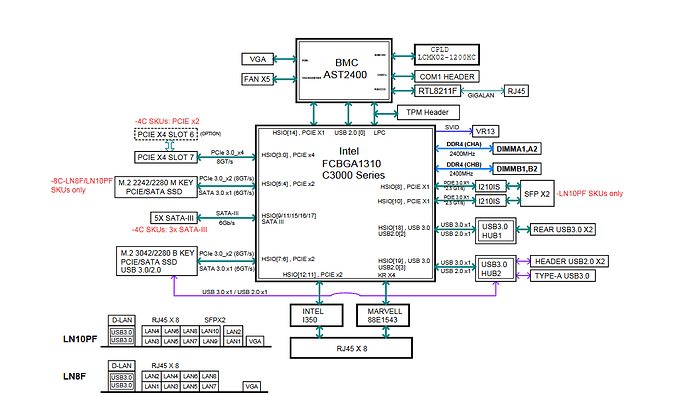
When it comes to network communications, Intel QAT is a blatant workload mismatch unless you're running a very busy public-facing nginx that is patched with Intel QAT routines. I recommend forgetting about it and not even trying to implement it, as you won't use it. These Supermicro Denverton platforms have a lot to recommend them other than the QAT technology.