I have done some search on this and found a couple of threads which say to block the websites through FORWARD chain in iptables. That only seems to work for devices connected through that specific router where the command was issued.
I have a bridged ADSL2 router connected to an Openwrt Router where the internet gets connected through pppoe and then this router handles all the internet in the network. There is also another Openwrt router connected to the main router through WiFi with relayd configuration.
The network configuration is as follows:
ADSL2 Router @ 192.168.0.1 (Bridge mode)
|
| lan
|
Main Openwrt (Custom firmware LEDE latest release) @ 192.168.1.1
|
| wifi
|
2nd Openwrt (Custom firmware LEDE latest release) @ 192.168.1.254
The command I use to block the website for a particular mac address is:
iptables -I FORWARD -p ALL -m mac --mac-source xxxxxxxx -m string --string "youtube.com" --algo bm -m comment --comment "reject YouTube from ramzan mobile" -j REJECT
This command is executed in the main router FORWARD chain and then it only works in the main router. If a device is connected from the 2nd router the command has no effect on that device.
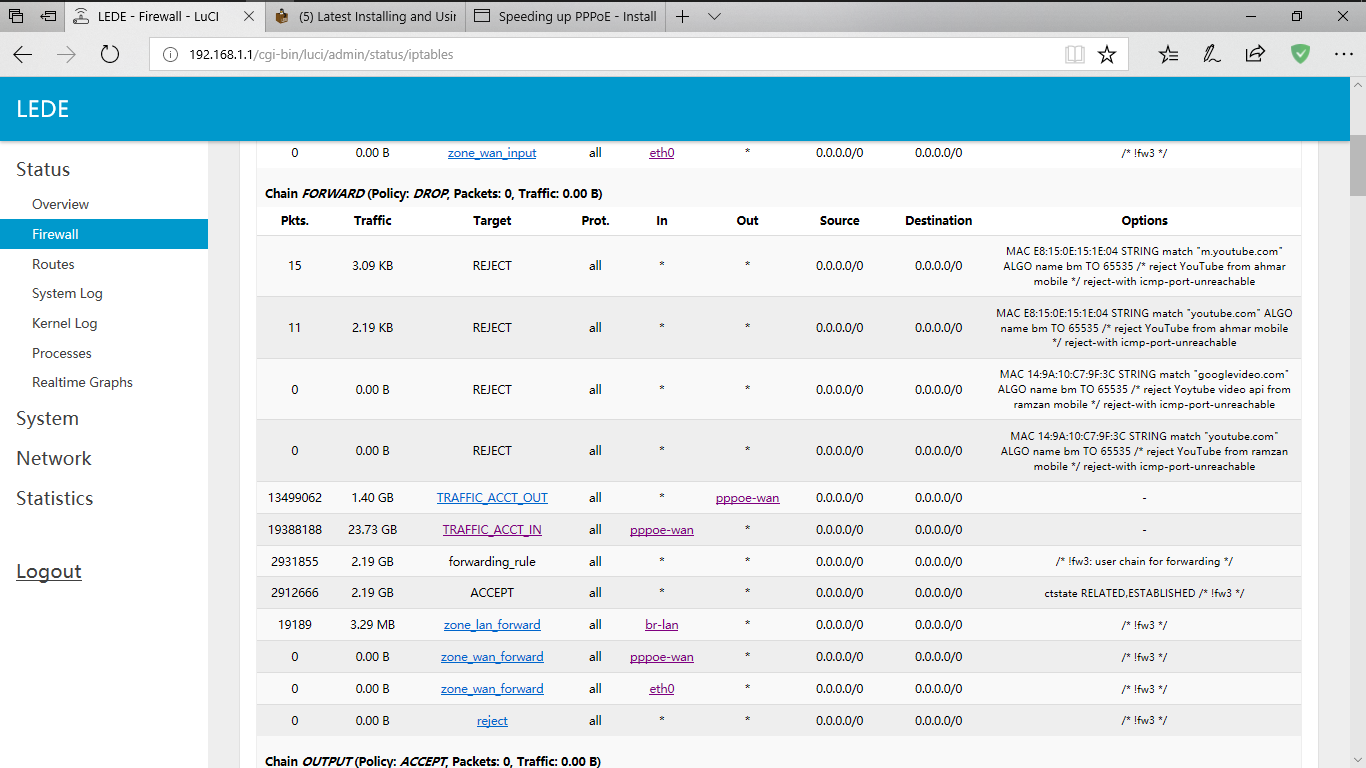
I have searched google for this issue but haven't found any possible solutions for it. You can see in the picture below that the command works for the device connected through the main router (first 2 rules in FORWARD chain) but the next two rules, there are no packets blocked.
I want to control the iptables from the main device only. I dont want to put the commands in different devices to do something. There must be something that I am doing wrong and cant figure out what it is yet. Anyone can help me with it? Thanks