I used to use this tutorial to block a certain ip range from accessing WAN : https://forum.archive.openwrt.org/viewtopic.php?id=64562
after upgrading to FW4, I can't as above method uses iptables.
There is a package that will translate old rules. You just have to run the syntax thru it.
Can you share package name?
Lynx
July 4, 2022, 7:53am
4
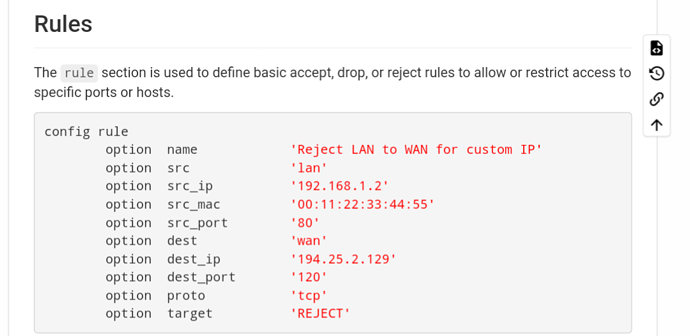
I think it should be possible to work it out from here:
Seems like a close example is given:
I imagine you can ditch the source MAC and destination IP.
Actually probably just a rule in LuCi can be added:
For entering range I think this may be the only way:
Ranges can be specified in CIDR notation (e.g. 192.168.0.0/16). This means the size of the range must be a power of two. Odd sized ranges could use multiple such rules.
Nftables support intervals by default.
config rule
option name 'Test'
option src 'lan'
option dest 'wan'
option target 'REJECT'
list src_ip '192.168.1.135-192.168.1.150'
list proto 'all'
option start_time '23:55:00'
option stop_time '07:30:00'
Verify that the rule was created correctly:
root@OpenWrt:~# nft list chain inet fw4 forward_lan
table inet fw4 {
chain forward_lan {
ip saddr 192.168.1.135-192.168.1.150 meta hour "23:55"-"07:30" counter packets 0 bytes 0 jump reject_to_wan comment "!fw4: Test"
jump accept_to_wan comment "!fw4: Accept lan to wan forwarding"
ct status dnat accept comment "!fw4: Accept port forwards"
jump accept_to_lan
}
}
2 Likes
Lynx
July 4, 2022, 6:57pm
6
Oh wow so LuCi needs updating! Who's the person to tag for this? @jow ?
1 Like
You would need a new validator function to allow non-CIDR input, then update the firewall application. At least that’s how I think it would need to be changed.
},
ip6hostid: function() {
if (this.value == "eui64" || this.value == "random")
return true;
var v6 = this.factory.parseIPv6(this.value);
return this.assert(!(!v6 || v6[0] || v6[1] || v6[2] || v6[3]), _('valid IPv6 host id'));
},
ipmask: function(negative) {
return this.assert(this.apply('ipmask4', null, [negative]) || this.apply('ipmask6', null, [negative]),
_('valid network in address/netmask notation'));
},
ipmask4: function(negative) {
return this.assert(this.apply('cidr4', null, [negative]) || this.apply('ipnet4') || this.apply('ip4addr'),
_('valid IPv4 network'));
},
ipmask6: function(negative) {
};
return dl;
}
}),
addIPOption: function(s, tab, name, label, description, family, hosts, multiple) {
var o = s.taboption(tab, multiple ? this.CBIDynamicMultiValueList : form.Value, name, label, description);
o.modalonly = true;
o.datatype = 'list(neg(ipmask("true")))';
o.placeholder = multiple ? _('-- add IP --') : _('any');
if (family != null) {
var choices = this.transformHostHints(family, hosts);
for (var i = 0; i < choices[0].length; i++)
o.value(choices[0][i], choices[1][choices[0][i]]);
}
/* force combobox rendering */
2 Likes
Lynx
July 4, 2022, 8:46pm
8
Excellent. Really seems like this should be there in 22.03. I mean facilitating setting up IP range seems like a good idea.
1 Like
iptables-translate
(Available on desktop distros.)
But it seems your issue is with the syntax.
Hats off to You brother, You really saved my day.
Thanks to everyone who replied here.
IPtables is not supported in FW4.
I know that. That's why you translate.
system
July 16, 2022, 12:56pm
15
This topic was automatically closed 10 days after the last reply. New replies are no longer allowed.