Hello,
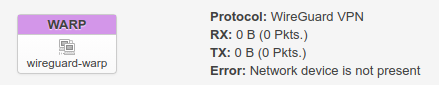
I set up Cloudflare warp on my bt home hub 5a running openwrt, all works as expected until wan goes down (loss of dsl link), the wireguard interface disappears (wg show has no output) and the only way to get it back is to reboot the device.
syslog
Sat Jan 9 12:40:43 2021 daemon.info pppd[3781]: LCP terminated by peer
Sat Jan 9 12:40:43 2021 daemon.info pppd[3781]: Connect time 1440.0 minutes.
Sat Jan 9 12:40:43 2021 daemon.info pppd[3781]: Sent 1064113744 bytes, received 874240258 bytes.
Sat Jan 9 12:40:43 2021 daemon.notice netifd: Network device 'pppoe-wan' link is down
Sat Jan 9 12:40:43 2021 daemon.notice netifd: Interface 'wan' has lost the connection
Sat Jan 9 12:40:43 2021 daemon.notice netifd: Interface 'warp' has lost the connection
Sat Jan 9 12:40:43 2021 daemon.notice netifd: Network device 'warp' link is down
Sat Jan 9 12:40:43 2021 daemon.notice netifd: Interface 'warp' is now down
Sat Jan 9 12:40:43 2021 daemon.notice netifd: Interface 'warp' is setting up now
Sat Jan 9 12:40:44 2021 daemon.notice netifd: Interface 'warp' is now down
Sat Jan 9 12:40:44 2021 daemon.notice pppd[3781]: Modem hangup
Sat Jan 9 12:40:44 2021 daemon.notice pppd[3781]: Connection terminated.
Sat Jan 9 12:40:44 2021 daemon.info pppd[3781]: Sent PADT
Sat Jan 9 12:40:44 2021 daemon.info pppd[3781]: Exit.
Sat Jan 9 12:40:44 2021 daemon.notice netifd: Interface 'wan' is now down
Sat Jan 9 12:40:44 2021 daemon.notice netifd: Interface 'wan' is disabled
Sat Jan 9 12:40:44 2021 daemon.notice netifd: Interface 'wan' is enabled
Sat Jan 9 12:40:44 2021 daemon.notice netifd: Interface 'wan' is setting up now
Sat Jan 9 12:40:45 2021 daemon.err insmod: module is already loaded - slhc
Sat Jan 9 12:40:45 2021 daemon.err insmod: module is already loaded - ppp_generic
Sat Jan 9 12:40:45 2021 daemon.err insmod: module is already loaded - pppox
Sat Jan 9 12:40:45 2021 daemon.err insmod: module is already loaded - pppoe
Sat Jan 9 12:40:45 2021 daemon.info pppd[6851]: Plugin rp-pppoe.so loaded.
Sat Jan 9 12:40:45 2021 daemon.info pppd[6851]: RP-PPPoE plugin version 3.8p compiled against pppd 2.4.7
Sat Jan 9 12:40:45 2021 daemon.notice pppd[6851]: pppd 2.4.7 started by root, uid 0
Sat Jan 9 12:40:45 2021 daemon.info pppd[6851]: PPP session is 213
Sat Jan 9 12:40:45 2021 daemon.warn pppd[6851]: Connected to *:*:*:*:*:* via interface dsl0
Sat Jan 9 12:40:45 2021 kern.info kernel: [86613.629818] pppoe-wan: renamed from ppp0
Sat Jan 9 12:40:45 2021 daemon.info pppd[6851]: Renamed interface ppp0 to pppoe-wan
Sat Jan 9 12:40:45 2021 daemon.info pppd[6851]: Using interface pppoe-wan
Sat Jan 9 12:40:45 2021 daemon.notice pppd[6851]: Connect: pppoe-wan <--> dsl0
Sat Jan 9 12:40:45 2021 daemon.info pppd[6851]: CHAP authentication succeeded: CHAP authentication success, unit 14765
Sat Jan 9 12:40:45 2021 daemon.notice pppd[6851]: CHAP authentication succeeded
Sat Jan 9 12:40:45 2021 daemon.notice pppd[6851]: peer from calling number 00:02:3B:10:04:0B authorized
Sat Jan 9 12:40:46 2021 daemon.notice pppd[6851]: local IP address *.*.*.*
Sat Jan 9 12:40:46 2021 daemon.notice pppd[6851]: remote IP address *.*.*.*
Sat Jan 9 12:40:46 2021 daemon.notice pppd[6851]: primary DNS address *.*.*.*
Sat Jan 9 12:40:46 2021 daemon.notice pppd[6851]: secondary DNS address 8.8.8.8
Sat Jan 9 12:40:46 2021 daemon.notice netifd: Network device 'pppoe-wan' link is up
Sat Jan 9 12:40:46 2021 daemon.notice netifd: Interface 'wan' is now up
Sat Jan 9 12:40:47 2021 user.notice firewall: Reloading firewall due to ifup of wan (pppoe-wan)
Sat Jan 9 12:41:04 2021 daemon.err dnscrypt-proxy[1211]: [2021-01-09 11:41:04] [NOTICE] Server with the lowest initial latency: cisco-familyshield (rtt: 77ms)
Sat Jan 9 12:43:01 2021 daemon.notice hostapd: wlan1: AP-STA-DISCONNECTED *:*:*:*:*:*
Sat Jan 9 12:43:01 2021 daemon.info hostapd: wlan1: STA *:*:*:*:*:* IEEE 802.11: disassociated
Sat Jan 9 12:43:02 2021 daemon.info hostapd: wlan1: STA *:*:*:*:*:* IEEE 802.11: deauthenticated due to inactivity (timer DEAUTH/REMOVE)
network
config interface 'loopback'
option ifname 'lo'
option proto 'static'
option ipaddr '127.0.0.1'
option netmask '255.0.0.0'
config globals 'globals'
option ula_prefix 'fd94:a621:fb8b::/48'
config atm-bridge 'atm'
option encaps 'llc'
option payload 'bridged'
option nameprefix 'dsl'
option vci '38'
option vpi '0'
config dsl 'dsl'
option ds_snr_offset '0'
option firmware '/lib/firmware/vr9-A-dsl.bin'
option annex 'a2p'
option xfer_mode 'atm'
option line_mode 'adsl'
config interface 'lan'
option type 'bridge'
option ifname 'eth0.1'
option proto 'static'
option ipaddr '192.168.1.1'
option netmask '255.255.255.0'
option ip6assign '60'
config device 'lan_eth0_1_dev'
option name 'eth0.1'
option macaddr '34:8a:ae:d6:6d:e2'
config interface 'wan'
option ifname 'dsl0'
option proto 'pppoe'
option ipv6 '1'
option username '***'
option password '***'
option keepalive '7,3'
option keepalive_adaptive '1'
option peerdns '0'
option mtu '1452'
config device 'wan_dsl0_dev'
option name 'dsl0'
option macaddr '34:8a:ae:d6:6d:e3'
config switch
option name 'switch0'
option reset '1'
option enable_vlan '1'
config switch_vlan
option device 'switch0'
option vlan '1'
option ports '0 1 2 4 6t'
config switch_vlan
option device 'switch0'
option vlan '2'
option ports '5 6t'
config interface 'warp'
option proto 'wireguard'
option private_key '***'
list addresses '172.16.0.2/32'
option force_link '1'
option mtu '1372'
config wireguard_warp
option public_key '***'
option persistent_keepalive '25'
list allowed_ips '0.0.0.0/0'
option route_allowed_ips '1'
option endpoint_host 'engage.cloudflareclient.com'
option endpoint_port '2408'
firewall
config defaults
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'REJECT'
option synflood_protect '1'
config zone
option name 'lan'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'ACCEPT'
option network 'lan'
config zone
option name 'wan'
option input 'REJECT'
option output 'ACCEPT'
option forward 'REJECT'
option masq '1'
option mtu_fix '1'
option network 'wan'
config rule
option name 'Allow-DHCP-Renew'
option src 'wan'
option proto 'udp'
option dest_port '68'
option target 'ACCEPT'
option family 'ipv4'
config rule
option name 'Allow-Ping'
option src 'wan'
option proto 'icmp'
option icmp_type 'echo-request'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-IGMP'
option src 'wan'
option proto 'igmp'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-DHCPv6'
option src 'wan'
option proto 'udp'
option src_ip 'fc00::/6'
option dest_ip 'fc00::/6'
option dest_port '546'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-MLD'
option src 'wan'
option proto 'icmp'
option src_ip 'fe80::/10'
list icmp_type '130/0'
list icmp_type '131/0'
list icmp_type '132/0'
list icmp_type '143/0'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Input'
option src 'wan'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
list icmp_type 'router-solicitation'
list icmp_type 'neighbour-solicitation'
list icmp_type 'router-advertisement'
list icmp_type 'neighbour-advertisement'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Forward'
option src 'wan'
option dest '*'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-IPSec-ESP'
option src 'wan'
option dest 'lan'
option proto 'esp'
option target 'ACCEPT'
config rule
option name 'Allow-ISAKMP'
option src 'wan'
option dest 'lan'
option dest_port '500'
option proto 'udp'
option target 'ACCEPT'
config redirect
option name 'Divert-DNS, port 53'
option src 'lan'
option proto 'tcp udp'
option src_dport '53'
option dest_port '53'
option target 'DNAT'
config include
option path '/etc/firewall.user'
config zone
option name 'wgzone'
option mtu_fix '1'
option input 'REJECT'
option forward 'REJECT'
option masq '1'
option output 'ACCEPT'
option network 'warp'
config forwarding
option dest 'wgzone'
option src 'lan'