I will definitely look into it tomorrow. I'll try to flash a stock 17.01.4 to a spare router tomorrow to test.
Please help me work out why none of my connections are being routed through my wireguard interface (which according to the status is connected).
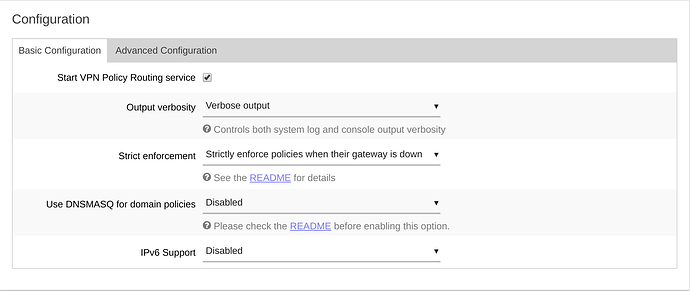
edit 1: after some investigating I think it may be because the domain is being routed via its ipv6 address. However, when I enable ipv6 in vpn-policy-routing I get a lot of errors when reloading the configuration.
edit 2: resolved.
For anyone else having issues with wireguard, the GUI does not add all the options. Add the line below to /etc/config/network and then run /etc/init.d/network reload
option route_allowed_ips '0'
It's more a general troubleshooting tip. Maybe a comment along the line of "don't assume the GUI will add all the options for you, check them via SSH"
Stangri,
I've installed LEDE 17.04.1 x86/64 build with AirVPN and am trying vpn-policy-routing to route one local ip address outside my vpn, and am getting an error 'unknown interface: wan'
I get this error using luci-app-vpn-policy-routing, and also when manually configuring /etc/config/vpn-policy-routing
I've uploaded the results of /etc/init.d/vpn-policy-routing to https://paste.ee/p/xwe3Q and other results into https://pastebin.com/dtwvFXiY
I've tried totally renaming the wan interface, but I still get the same error. If I route the ip address to VPN0 interface using luci-app-vpn-policy-routing, I don't get any errors (but no re-routing!).
Could you please take a look?
Thanks, Kevin
Stangri,
Problem solved!
In your reply to my post re problems with vpn-bypass you wrote:
=================================================================
Kevin,
in my setup I don’t have the network.lan.gateway and instead of network.wan.dns I set the default DNS server with dhcp.@dnsmasq[0].server='8.8.8.8' '4.4.4.4'.
Otherwise I don’t see what could be messing things up. Just to be on a safe side, what’s the output of route?
I've just removed the lan gateway and wan dns entries, and set the dns servers in dnsmasq, and now all works perfectly!
It looks like it's necessary to configure the dns servers in dnsmasq, rather than in the wan interface.
Many thanks for your help, and for these very useful packages.
I'll also test this solution with vpn-bypass and report back
Will be fixed in luci-app-vpn-policy-routing 12. I'll push it to repo later tonight.
Awesome work. I can confirm that enabling DNSMASQ through the Web UI is working again.
@stangri
Thanks sir. I know you put a lot of time into making these packages work and improving on them. They are only getting better over time. I'll continue to help in any way I can.
Just was redirected to this new thread, thx @stangri for continue working on this, I gotta update the package.
However I have a question which settings I have to set for my current setup to work.
I'll try to recall it now as good as possible, can give details later if needed:
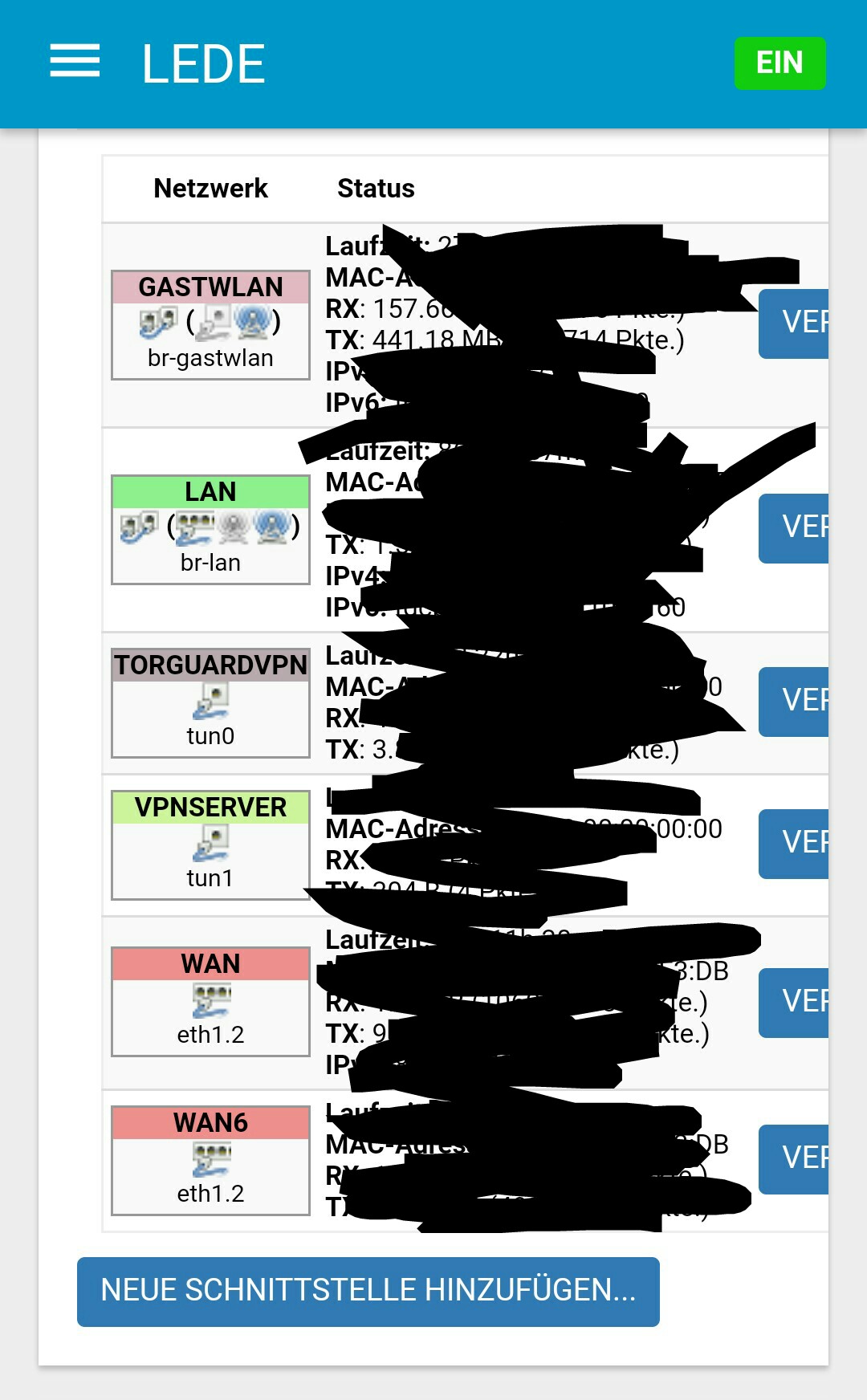
I have set up both a vpn client and a vpn server on my router.
For both I have specific interfaces and firewalls set up.
I only want one ip (homeserver) in my lan to "use" the vpn client and go through vpn tunnel to my vpn provider.
This works with your app.
From away I also can connect to my vpn server, there's just one problem: Connecting to my vpn server I can reach all ip's except of the homeserver 
I'm a noob and happy whit how far I got but that last step is missing.
I'm unsure if it's just some setting in your app or if I have to change something in the firewall zones, but maybe someone here can help me.
Uhm, I don't even know where to start. If the homeserver is accessible from LAN it should be accessible via OpenVPN Server connection as well, especially if all other local devices are accessible.
You may want to post your openvpn, firewall and vpn-policy-routing configs, as well as the service/port you're trying to access on your homeserver.
Yes, homeserver is accessible via lan.
But not via ovpn server connection, this concerns every port I tried so far.
Where are all the config files i should post..also I don't really know which info better not post publicly.
Can you help me here?
I'll attach pics of interfaces and fw zones.
@stangri helped me, I added this in /etc/config/firewall :
config policy
option comment 'hummingboard’
option local_addresses '192.168.1.103’
option local_ports '22’
option interface ‘wan’
Now connecting to my vpn server I can reach Port 22 (SSH) on my homeserver. 
@stangri Just updated today and none of the IP's I have set to go through wan interface are working. Everything is going through my VPN tunnel
here is the out put of 'opkg list-installed | grep vpn-policy-routing'
luci-app-vpn-policy-routing - git-18.023.74248-ee409b6-12
vpn-policy-routing - 0.0.1-15
All was working fine before the update ![]()
I noticed that in the config file " option ipset_enable '1' " is no longer available and manually inputting it into the config does nothing. Maybe this has something to do with it?
this is all that shows not in the config file now
config vpn-policy-routing 'config'
option verbosity '2'
option strict_enforcement '1'
option enabled '1'
option output_chain_enabled '1'
list ignored_interface 'vpnserver'
option dnsmasq_enabled '1'Make sure to read this. I'm very curious what might have happened tho, so make sure to post required information.
And once again I refer you to README. With dnsmasq enabled, the ipset is assumed enabled. The actual setting only plays if you disable dnsmasq support. ![]()
Yes sir, this I am aware. Here is what my config looks like when I disable DNSMASQ
config vpn-policy-routing 'config'
option verbosity '2'
option strict_enforcement '1'
option enabled '1'
option output_chain_enabled '1'
list ignored_interface 'vpnserver'
This is what I meant earlier when I said IPSET is no longer available
Even with DNSMASQ disabled it does not show up in Web UI, and adding manually through config does nothing.
Edit: @stangri by the way I just posted output of /etc/init.d/vpn-policy-routing support -p to paste.ee
May have figured it out. It seems that vpn-policy-routing was set to "DISABLED" in the system startup tasks. I noticed this because I tried running /etc/init.d/vpn-policy-routing restart and everything started working. After restarting the router I noticed I had to run a restart again on vpn-policy-routing. So I checked the startup page and what do you know it was DISABLED. Idk if maybe it is set to disabled by default from when I updated. maybe something you can check out? Otherwise I must have hit disable by accident
Ah, I see. My bad -- you quoted the config file and I assumed you're talking about the actual configuration, not the luci page. Thanks for bringing it up, fixed in luci-app-vpn-policy-routing 13.
Consequence of using old luci app probably. It had a bug that it disabled the service every time you tried to stop it from Web UI. Once you enable it once tho (or on the new installs), it should be good to go. Thank you for sticking with it. ![]()
Hi,
Does anyone know the most effective way to bypass the BBC iplayer service (android app)? What are the IPs/domain names that have to be bypassed? I have multiple devices that access iplayer and bypassing the entire device is not ideal.
Thanks