Thanks for the replies.
Stangri
I am more then willing to try using TAP if you think that will help. However, In my process to determine where the problem was, I setup a StrongSWAN Server and had the identical issue using it to connect remotely. I am not sure what type of connection it uses, so I don't know if this will help you or not?
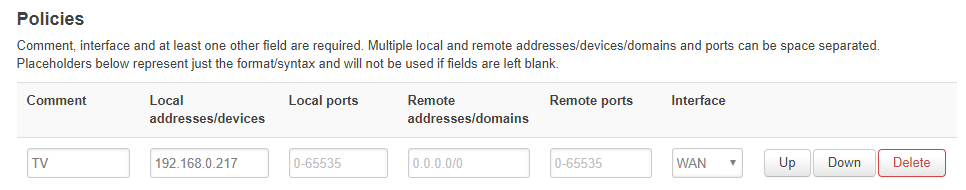
What I am wondering is when I set this policy (IP Address -> VPN Client) does it capture all traffic leaving that IP Address? I assume that there is some sort of exemption for my LAN, as I can access the IP Address just fine within my LAN (network shares, web pages, etc). However, since the OpenVPN Server is using a different subnet could the policy be capturing that traffic and sending it via VPN Client instead of back to the OpenVPNServer? Would a firewall rule, or manual entry into firewall.user override this behavior?
JW0914
The problem I am experiencing is almost option #2.
If I don't have any policies set for the IP Addresses in my LAN, everything works fine. (Wan -> OpenVPN Server -> Lan.)
However, as soon as I set a policy for any IP Address in my LAN, I can no longer access that machine via the OpenVPN Server. ( Wan -> OpenVPN Sever -> no response) Other IP Addresses work just fine. (Wan -> OpenVPN Server -> Lan.)
Here is the server log using verb 5
Mon Aug 13 10:02:08 2018 us=244193 OpenVPN 2.4.4 mips-openwrt-linux-gnu [SSL (OpenSSL)] [LZO] [LZ4] [EPOLL] [MH/PKTINFO] [AEAD]
Mon Aug 13 10:02:08 2018 us=244542 library versions: OpenSSL 1.0.2o 27 Mar 2018, LZO 2.10
Mon Aug 13 10:02:08 2018 us=268512 Diffie-Hellman initialized with 2048 bit key
Mon Aug 13 10:02:08 2018 us=274035 Outgoing Control Channel Authentication: Using 160 bit message hash 'SHA1' for HMAC authentication
Mon Aug 13 10:02:08 2018 us=274462 Incoming Control Channel Authentication: Using 160 bit message hash 'SHA1' for HMAC authentication
Mon Aug 13 10:02:08 2018 us=274867 TLS-Auth MTU parms [ L:1624 D:1182 EF:68 EB:0 ET:0 EL:3 ]
Mon Aug 13 10:02:08 2018 us=323669 TUN/TAP device ovpns0 opened
Mon Aug 13 10:02:08 2018 us=324097 TUN/TAP TX queue length set to 100
Mon Aug 13 10:02:08 2018 us=324489 do_ifconfig, tt->did_ifconfig_ipv6_setup=0
Mon Aug 13 10:02:08 2018 us=325013 /sbin/ifconfig ovpns0 192.168.200.1 netmask 255.255.255.0 mtu 1500 broadcast 192.168.200.255
Mon Aug 13 10:02:08 2018 us=355149 Data Channel MTU parms [ L:1624 D:1450 EF:124 EB:406 ET:0 EL:3 ]
Mon Aug 13 10:02:08 2018 us=355635 Could not determine IPv4/IPv6 protocol. Using AF_INET
Mon Aug 13 10:02:08 2018 us=356042 Socket Buffers: R=[87380->87380] S=[16384->16384]
Mon Aug 13 10:02:08 2018 us=356487 Listening for incoming TCP connection on [AF_INET][undef]:51194
Mon Aug 13 10:02:08 2018 us=356891 TCPv4_SERVER link local (bound): [AF_INET][undef]:51194
Mon Aug 13 10:02:08 2018 us=357366 TCPv4_SERVER link remote: [AF_UNSPEC]
Mon Aug 13 10:02:08 2018 us=357738 MULTI: multi_init called, r=256 v=256
Mon Aug 13 10:02:08 2018 us=358267 IFCONFIG POOL: base=192.168.200.2 size=252, ipv6=0
Mon Aug 13 10:02:08 2018 us=358833 MULTI: TCP INIT maxclients=1024 maxevents=1028
Mon Aug 13 10:02:08 2018 us=359695 Initialization Sequence Completed
Mon Aug 13 10:02:33 2018 us=136073 MULTI: multi_create_instance called
Mon Aug 13 10:02:33 2018 us=136808 Re-using SSL/TLS context
Mon Aug 13 10:02:33 2018 us=137322 LZ4 compression initializing
Mon Aug 13 10:02:33 2018 us=139020 Control Channel MTU parms [ L:1624 D:1182 EF:68 EB:0 ET:0 EL:3 ]
Mon Aug 13 10:02:33 2018 us=139812 Data Channel MTU parms [ L:1624 D:1450 EF:124 EB:406 ET:0 EL:3 ]
Mon Aug 13 10:02:33 2018 us=140537 Local Options String (VER=V4): 'V4,dev-type tun,link-mtu 1544,tun-mtu 1500,proto TCPv4_SERVER,comp-lzo,keydir 0,cipher BF-CBC,auth SHA1,keysize 128,tls-auth,key-method 2,tls-server'
Mon Aug 13 10:02:33 2018 us=140885 Expected Remote Options String (VER=V4): 'V4,dev-type tun,link-mtu 1544,tun-mtu 1500,proto TCPv4_CLIENT,comp-lzo,keydir 1,cipher BF-CBC,auth SHA1,keysize 128,tls-auth,key-method 2,tls-client'
Mon Aug 13 10:02:33 2018 us=141413 TCP connection established with [AF_INET]174.233.134.118:5541
Mon Aug 13 10:02:33 2018 us=141769 TCPv4_SERVER link local: (not bound)
Mon Aug 13 10:02:33 2018 us=142141 TCPv4_SERVER link remote: [AF_INET]174.233.134.118:5541
RMon Aug 13 10:02:34 2018 us=18195 174.233.134.118:5541 TLS: Initial packet from [AF_INET]174.233.134.118:5541, sid=8bcbf6e4 03b4d310
WRRWWWWRRRRWRWRMon Aug 13 10:02:35 2018 us=659468 174.233.134.118:5541 VERIFY OK: depth=1, C=GB, ST=London, O=WWW Ltd.
Mon Aug 13 10:02:35 2018 us=672654 174.233.134.118:5541 VERIFY OK: depth=0, CN=my-client
WRMon Aug 13 10:02:35 2018 us=944944 174.233.134.118:5541 peer info: IV_VER=2.5_master
Mon Aug 13 10:02:35 2018 us=945351 174.233.134.118:5541 peer info: IV_PLAT=android
Mon Aug 13 10:02:35 2018 us=945709 174.233.134.118:5541 peer info: IV_PROTO=2
Mon Aug 13 10:02:35 2018 us=946067 174.233.134.118:5541 peer info: IV_NCP=2
Mon Aug 13 10:02:35 2018 us=946424 174.233.134.118:5541 peer info: IV_LZ4=1
Mon Aug 13 10:02:35 2018 us=946778 174.233.134.118:5541 peer info: IV_LZ4v2=1
Mon Aug 13 10:02:35 2018 us=947265 174.233.134.118:5541 peer info: IV_LZO=1
Mon Aug 13 10:02:35 2018 us=947657 174.233.134.118:5541 peer info: IV_COMP_STUB=1
Mon Aug 13 10:02:35 2018 us=948063 174.233.134.118:5541 peer info: IV_COMP_STUBv2=1
Mon Aug 13 10:02:35 2018 us=948427 174.233.134.118:5541 peer info: IV_TCPNL=1
Mon Aug 13 10:02:35 2018 us=948803 174.233.134.118:5541 peer info: IV_GUI_VER=de.blinkt.openvpn_0.7.5
WRMon Aug 13 10:02:36 2018 us=76164 174.233.134.118:5541 Control Channel: TLSv1.2, cipher TLSv1/SSLv3 ECDHE-RSA-AES256-GCM-SHA384, 4096 bit RSA
Mon Aug 13 10:02:36 2018 us=76713 174.233.134.118:5541 [my-client] Peer Connection Initiated with [AF_INET]174.233.134.118:5541
Mon Aug 13 10:02:36 2018 us=77403 my-client/174.233.134.118:5541 MULTI_sva: pool returned IPv4=192.168.200.2, IPv6=(Not enabled)
Mon Aug 13 10:02:36 2018 us=78964 my-client/174.233.134.118:5541 MULTI: Learn: 192.168.200.2 -> my-client/174.233.134.118:5541
Mon Aug 13 10:02:36 2018 us=79374 my-client/174.233.134.118:5541 MULTI: primary virtual IP for my-client/174.233.134.118:5541: 192.168.200.2
RMon Aug 13 10:02:37 2018 us=216104 my-client/174.233.134.118:5541 PUSH: Received control message: 'PUSH_REQUEST'
Mon Aug 13 10:02:37 2018 us=216961 my-client/174.233.134.118:5541 SENT CONTROL [my-client]: 'PUSH_REPLY,topology subnet,redirect-gateway def1,route-gateway dhcp,route 192.168.200.0 255.255.255.0,dhcp-option DNS 192.168.1.1,compress lz4,persist-key,persist-tun,DOMAIN lan,route-gateway 192.168.200.1,topology subnet,ping 10,ping-restart 120,ifconfig 192.168.200.2 255.255.255.0,peer-id 0,cipher AES-256-GCM' (status=1)
Mon Aug 13 10:02:37 2018 us=217396 my-client/174.233.134.118:5541 Data Channel: using negotiated cipher 'AES-256-GCM'
Mon Aug 13 10:02:37 2018 us=217835 my-client/174.233.134.118:5541 Data Channel MTU parms [ L:1552 D:1450 EF:52 EB:406 ET:0 EL:3 ]
Mon Aug 13 10:02:37 2018 us=219287 my-client/174.233.134.118:5541 Outgoing Data Channel: Cipher 'AES-256-GCM' initialized with 256 bit key
Mon Aug 13 10:02:37 2018 us=219716 my-client/174.233.134.118:5541 Incoming Data Channel: Cipher 'AES-256-GCM' initialized with 256 bit key
WWRRwRwRwrWRwRwRwRwWRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwWRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwWRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwWRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwWRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwRwMon Aug 13 10:03:32 2018 us=935002 my-client/174.233.134.118:5541 Connection reset, restarting [0]
Mon Aug 13 10:03:32 2018 us=935388 my-client/174.233.134.118:5541 SIGUSR1[soft,connection-reset] received, client-instance restarting
Mon Aug 13 10:03:32 2018 us=936708 TCP/UDP: Closing socket
I am using android devices to connect to the Open VPN Server, using the "OpenVPN for Android" app. I can't seem to find an option to set the verb level within the app. If I set it in the OVPN file before importing it, the app resets it to verb 4 when importing it into the app. If I set a custom option to verb 7 after importing the OVPN file, the generated config file stills adds verb 4. Do you know of another android app I could use to get this log?