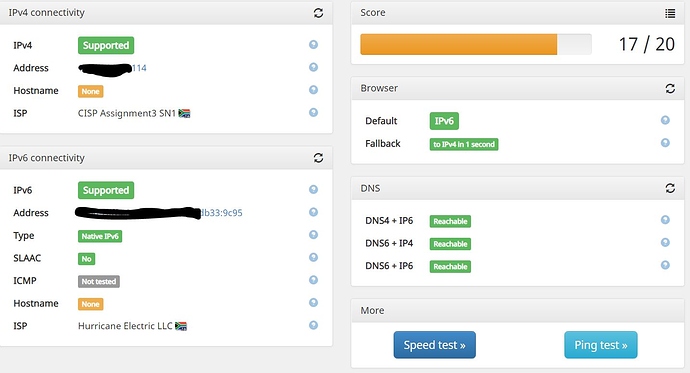
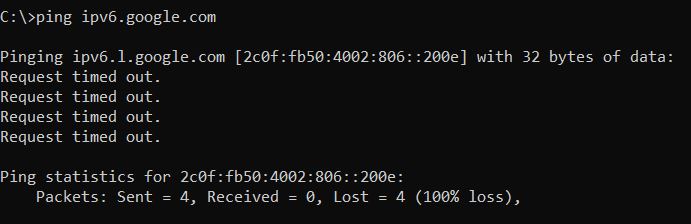
But he is complaining that LAN clients can't ping to the outside, not that he is not able to receive pings. Weird is, that he can access IPv6 websites, but can't ping. Leads me to believe that it has something to do with the firewall settings.
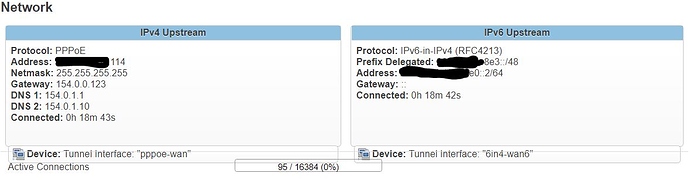
But to clarify some things: the /64 is enough! You can distribute this to your LAN downstream from the router. The tunnel will have it's own prefix. Also, "IPv6 routed prefix" is available and must be set both for WAN6 and for LAN:
WAN6:
Common configuration/General Setup:
-Local IPv6 address: the one from your tunnel which ends with :2/64 (it's listed as "Client IPv6 address" on HE's homepage). Make sure to put the /64 at the end.
-IPv6 routed prefix: the one listed as "Routed /64", e.g. 2001:470:xy:zzzz::/64
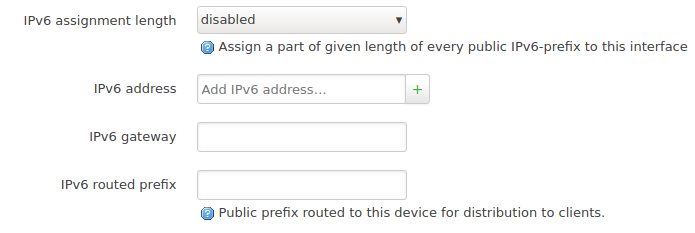
LAN:
Common configuration/General Setup:
-IPv6 assignment length: disabled
-IPv6 address: chose address from your /64. E.g. 2001:470:xy:zzzz::1/64
-IPv6 gateway: leave empty
-IPv6 routed prefix: again your routed /64, e.g. 2001:470:xy:zzzz::/64
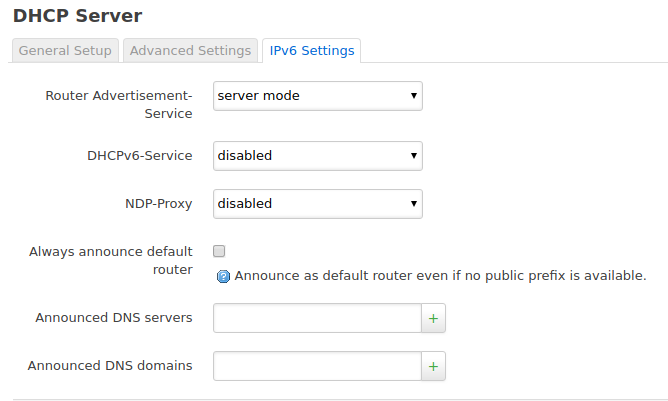
DHCP server/IPv6 settings:
-Router Advertisement-Service: server mode
-DHCPv6-Service: disabled (but all my clients are fine with SLAAC and RDNSS)
-Always announce default router: check
Now, to rule out misconfigured firewall, you could try to delete all routes (DANGEROUS, only for testing!). Or try to create a new rule that is permissive for all ICMP:
Network->Firewall->Traffic Rules:
New forward rule:
Enter name: e.g. ICMP-Test, leave the rest, click "Add and edit..."
-Restrict to address family: IPv4 and IPv6
-Protocol: ICMP
-Match ICMP type: any
-Source zone: Any zone
-Destination zone: Any zone
-Action: accept
Click "Save & Apply"
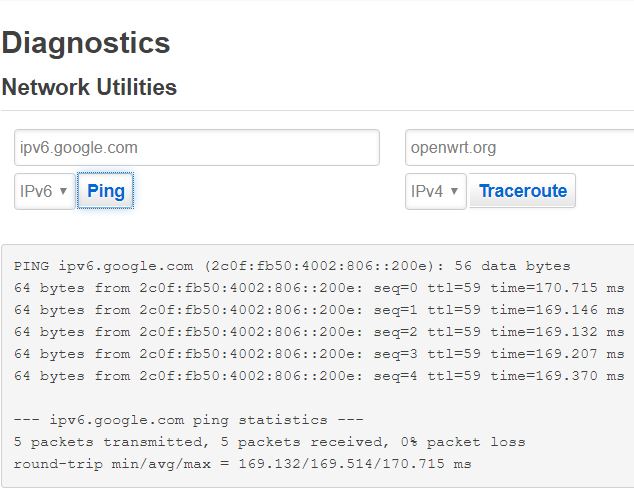
PS: I find it weird that the tracert seems to work in the beginning. It should also use ICMP. Anyway, I can tracert to openwrt.org.
PPS: Sometimes there really are issues in HE's end. In those cases it's useful to ask on HE's forums. The admins read the requests and have solved many similar problems.
Let us know if you need any clarifications!