I'll try and move away from the 255.252.0.0 netmask on the lan interface later. I though I needed it to be able to connect to my servers.
earlier I thought that the DHCP issue had been solved but I spoke to soon.
I have segmented the 5GHzx ssid's from the 2.4GHz ssid's by adding a + to the 5GHz Trusted and Guests.
Also I have enabled the radio 0 and 1 on the OpenWRT router and created there OpenWrt-Trusted(+) and OpenWRT-Guests(+)
When connecting to Trusted ssid:
I mostly get a 10.4.4.1 DHCP lease which is good. Sometimes though it fails and then I get a 10.1.4.1 as if there still is a DHCP active on the lan interface which there should not be as far as I intended.
When connecting to Trusted+ ssid:
I only get a 10.1.4.1 as if there still is a DHCP active on the lan interface which there should not be as far as I intended. When evert I get this IP (whether comming in via here or another ssid) I can't connect to anything. Which is good I guess but I should not be getting IP's in this range at all.
When connecting to Guests ssid:
I mostly get a 10.5.4.1 DHCP lease which is good. Sometimes though it fails and then I get a 10.1.4.1.
But like now I can't reach anything. No internet and no local.
When connecting to Guests+ ssid:
Mostly I get a 10.1.4.1 and switching back to Guests I also get a 10.1.4.1
Connecting to OpenWrt-Trusted(+) and OpenWRT-Guests(+) ssid's always results in a10.1.4.1 DHCP lease even though they are explicitly for the if-Trusted and if-Guests interfaces respectively.
It looks like the lan interface is somehow not configured correctly because this is what I see in the system log when things have gone wrong:
Tue Nov 10 18:44:06 2020 daemon.warn dnsmasq-dhcp[3200]: no address range available for DHCP request via br-lan
Tue Nov 10 18:44:06 2020 daemon.warn dnsmasq-dhcp[3200]: no address range available for DHCP request via br-lan
Tue Nov 10 18:44:07 2020 daemon.warn dnsmasq-dhcp[3200]: no address range available for DHCP request via br-lan
Tue Nov 10 18:44:08 2020 daemon.warn dnsmasq-dhcp[3200]: no address range available for DHCP request via br-lan
Tue Nov 10 18:44:10 2020 daemon.warn dnsmasq-dhcp[3200]: no address range available for DHCP request via br-lan
root@OpenWrt:~# uci export network; \
> uci export dhcp; uci export firewall; \
> head -n -0 /etc/firewall.user; \
> iptables-save -c; \
> ip -4 addr ; ip -4 ro li tab all ; ip -4 ru; \
> ls -l /etc/resolv.* /tmp/resolv.* /tmp/resolv.*/* ; head -n -0 /etc/resolv.*
/tmp/resolv.* /tmp/resolv.*/*
package network
config interface 'loopback'
option ifname 'lo'
option proto 'static'
option ipaddr '127.0.0.1'
option netmask '255.0.0.0'
config globals 'globals'
option ula_prefix 'fd68:74a7:6e62::/48'
config interface 'lan'
option type 'bridge'
option ifname 'eth0.1'
option proto 'static'
content removed due to considerations
option netmask '255.252.0.0'
list dns '8.8.8.8'
config interface 'wan'
option ifname 'eth1.2'
option proto 'dhcp'
config switch
option name 'switch0'
option reset '1'
option enable_vlan '1'
config switch_vlan
option device 'switch0'
option vlan '1'
option vid '1'
option ports '0 1 2 3 5t'
config switch_vlan
option device 'switch0'
option vlan '2'
option vid '2'
option ports '4 6t'
config interface 'if_Trusted'
option proto 'static'
option force_link '0'
option type 'bridge'
content removed due to considerations
option netmask '255.255.0.0'
option ifname 'eth0.40'
list dns '8.8.8.8'
config switch_vlan
option device 'switch0'
option vlan '3'
option ports '2t 5t'
option vid '40'
config interface 'if_Guests'
option proto 'static'
option type 'bridge'
content removed due to considerations
option netmask '255.255.0.0'
option ifname 'eth0.50'
list dns '8.8.8.8'
config switch_vlan
option device 'switch0'
option vlan '4'
option ports '2t 5t'
option vid '50'
config interface 'if_tmp_oldlan'
option ifname 'br-lan'
option proto 'static'
option ipaddr '192.168.1.1'
option netmask '255.255.255.0'
package dhcp
config dnsmasq
option localise_queries '1'
option rebind_protection '1'
option rebind_localhost '1'
option local '/lan/'
option domain 'lan'
option expandhosts '1'
option readethers '1'
option leasefile '/tmp/dhcp.leases'
option sequential_ip '1'
option localservice '0'
option boguspriv '0'
config dhcp 'wan'
option interface 'wan'
option ignore '1'
config odhcpd 'odhcpd'
option maindhcp '0'
option leasefile '/tmp/hosts/odhcpd'
option leasetrigger '/usr/sbin/odhcpd-update'
option loglevel '4'
config dhcp 'if_Trusted'
option interface 'if_Trusted'
option start '1025'
option limit '1000'
option leasetime '2m'
option force '1'
config dhcp 'if_Guests'
option interface 'if_Guests'
option start '1025'
option limit '1000'
option leasetime '2m'
option force '1'
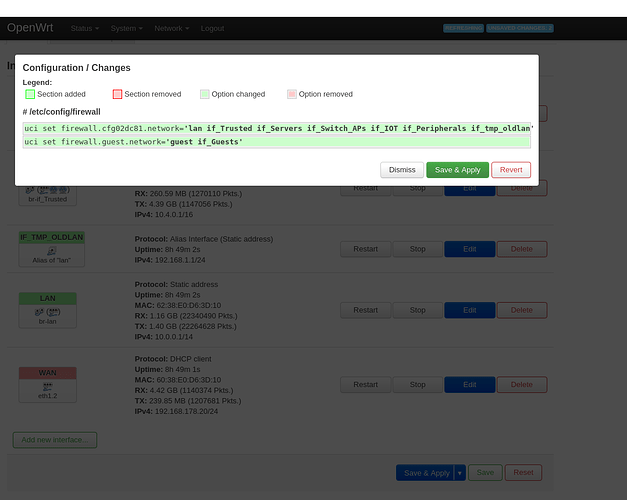
package firewall
config defaults
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'ACCEPT'
option synflood_protect '1'
config zone
option name 'lan'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'ACCEPT'
option network 'lan if_Trusted if_Servers if_Switch_APs if_IOT if_Peripherals if_tmp_oldlan'
config zone
option name 'wan'
option input 'REJECT'
option output 'ACCEPT'
option forward 'REJECT'
option masq '1'
option mtu_fix '1'
option network 'wan wan6'
config forwarding
option src 'lan'
option dest 'wan'
config rule
option name 'Allow-DHCP-Renew'
option src 'wan'
option proto 'udp'
option dest_port '68'
option target 'ACCEPT'
option family 'ipv4'
config rule
option name 'Allow-Ping'
option src 'wan'
option proto 'icmp'
option icmp_type 'echo-request'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-IGMP'
option src 'wan'
option proto 'igmp'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-DHCPv6'
option src 'wan'
option proto 'udp'
option src_ip 'fc00::/6'
option dest_ip 'fc00::/6'
option dest_port '546'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-MLD'
option src 'wan'
option proto 'icmp'
option src_ip 'fe80::/10'
list icmp_type '130/0'
list icmp_type '131/0'
list icmp_type '132/0'
list icmp_type '143/0'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Input'
option src 'wan'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
list icmp_type 'router-solicitation'
list icmp_type 'neighbour-solicitation'
list icmp_type 'router-advertisement'
list icmp_type 'neighbour-advertisement'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Forward'
option src 'wan'
option dest '*'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-IPSec-ESP'
option src 'wan'
option dest 'lan'
option proto 'esp'
option target 'ACCEPT'
config rule
option name 'Allow-ISAKMP'
option src 'wan'
option dest 'lan'
option dest_port '500'
option proto 'udp'
option target 'ACCEPT'
config include
option path '/etc/firewall.user'
config rule
option src 'lan'
option name 'block iot wan'
option src_ip '192.168.1.128/25'
option dest 'wan'
option target 'DROP'
config rule
option src 'lan'
option name 'block default ipcam'
option src_ip '192.168.1.10'
option dest 'wan'
option target 'DROP'
config redirect
option dest_port '443'
option src 'wan'
option name 'guideriis'
option src_dport '443'
option target 'DNAT'
option dest 'lan'
option proto 'tcp udp'
option dest_ip '192.168.1.111'
config zone
option name 'fw_Guests'
option network 'if_Guests'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'REJECT'
config forwarding
option dest 'wan'
option src 'fw_Guests'
# This file is interpreted as shell script.
# Put your custom iptables rules here, they will
# be executed with each firewall (re-)start.
# Internal uci firewall chains are flushed and recreated on reload, so
# put custom rules into the root chains e.g. INPUT or FORWARD or into the
# special user chains, e.g. input_wan_rule or postrouting_lan_rule.
# Generated by iptables-save v1.8.3 on Tue Nov 10 18:48:55 2020
*nat
:PREROUTING ACCEPT [20507:1824898]
:INPUT ACCEPT [5463:394292]
:OUTPUT ACCEPT [2485:177218]
:POSTROUTING ACCEPT [1441:89712]
:postrouting_fw_Guests_rule - [0:0]
:postrouting_lan_rule - [0:0]
:postrouting_rule - [0:0]
:postrouting_wan_rule - [0:0]
:prerouting_fw_Guests_rule - [0:0]
:prerouting_lan_rule - [0:0]
:prerouting_rule - [0:0]
:prerouting_wan_rule - [0:0]
:zone_fw_Guests_postrouting - [0:0]
:zone_fw_Guests_prerouting - [0:0]
:zone_lan_postrouting - [0:0]
:zone_lan_prerouting - [0:0]
:zone_wan_postrouting - [0:0]
:zone_wan_prerouting - [0:0]
[20507:1824898] -A PREROUTING -m comment --comment "!fw3: Custom prerouting rule chain" -j prerouting_rule
[1197:125499] -A PREROUTING -i br-if_Trusted -m comment --comment "!fw3" -j zone_lan_prerouting
[16431:1492383] -A PREROUTING -i br-lan -m comment --comment "!fw3" -j zone_lan_prerouting
[29:1680] -A PREROUTING -i eth1.2 -m comment --comment "!fw3" -j zone_wan_prerouting
[2850:205336] -A PREROUTING -i br-if_Guests -m comment --comment "!fw3" -j zone_fw_Guests_prerouting
[5149:338053] -A POSTROUTING -m comment --comment "!fw3: Custom postrouting rule chain" -j postrouting_rule
[13:2024] -A POSTROUTING -o br-if_Trusted -m comment --comment "!fw3" -j zone_lan_postrouting
[1065:60624] -A POSTROUTING -o br-lan -m comment --comment "!fw3" -j zone_lan_postrouting
[3708:248341] -A POSTROUTING -o eth1.2 -m comment --comment "!fw3" -j zone_wan_postrouting
[8:1504] -A POSTROUTING -o br-if_Guests -m comment --comment "!fw3" -j zone_fw_Guests_postrouting
[8:1504] -A zone_fw_Guests_postrouting -m comment --comment "!fw3: Custom fw_Guests postrouting rule chain" -j postrouting_fw_Guests_rule
[2850:205336] -A zone_fw_Guests_prerouting -m comment --comment "!fw3: Custom fw_Guests prerouting rule chain" -j prerouting_fw_Guests_rule
[1078:62648] -A zone_lan_postrouting -m comment --comment "!fw3: Custom lan postrouting rule chain" -j postrouting_lan_rule
[0:0] -A zone_lan_postrouting -s 10.0.0.0/14 -d 192.168.1.111/32 -p tcp -m tcp --dport 443 -m comment --comment "!fw3: guideriis (reflection)" -j SNAT --to-source 10.0.0.1
[0:0] -A zone_lan_postrouting -s 10.0.0.0/14 -d 192.168.1.111/32 -p udp -m udp --dport 443 -m comment --comment "!fw3: guideriis (reflection)" -j SNAT --to-source 10.0.0.1
[0:0] -A zone_lan_postrouting -s 10.4.0.0/16 -d 192.168.1.111/32 -p tcp -m tcp --dport 443 -m comment --comment "!fw3: guideriis (reflection)" -j SNAT --to-source 10.4.0.1
[0:0] -A zone_lan_postrouting -s 10.4.0.0/16 -d 192.168.1.111/32 -p udp -m udp --dport 443 -m comment --comment "!fw3: guideriis (reflection)" -j SNAT --to-source 10.4.0.1
[0:0] -A zone_lan_postrouting -s 192.168.1.0/24 -d 192.168.1.111/32 -p tcp -m tcp --dport 443 -m comment --comment "!fw3: guideriis (reflection)" -j SNAT --to-source 192.168.1.1
[0:0] -A zone_lan_postrouting -s 192.168.1.0/24 -d 192.168.1.111/32 -p udp -m udp --dport 443 -m comment --comment "!fw3: guideriis (reflection)" -j SNAT --to-source 192.168.1.1
[17628:1617882] -A zone_lan_prerouting -m comment --comment "!fw3: Custom lan prerouting rule chain" -j prerouting_lan_rule
[0:0] -A zone_lan_prerouting -s 10.0.0.0/14 -d 192.168.178.20/32 -p tcp -m tcp --dport 443 -m comment --comment "!fw3: guideriis (reflection)" -j DNAT --to-destination 192.168.1.111:443
[0:0] -A zone_lan_prerouting -s 10.0.0.0/14 -d 192.168.178.20/32 -p udp -m udp --dport 443 -m comment --comment "!fw3: guideriis (reflection)" -j DNAT --to-destination 192.168.1.111:443
[0:0] -A zone_lan_prerouting -s 10.4.0.0/16 -d 192.168.178.20/32 -p tcp -m tcp --dport 443 -m comment --comment "!fw3: guideriis (reflection)" -j DNAT --to-destination 192.168.1.111:443
[0:0] -A zone_lan_prerouting -s 10.4.0.0/16 -d 192.168.178.20/32 -p udp -m udp --dport 443 -m comment --comment "!fw3: guideriis (reflection)" -j DNAT --to-destination 192.168.1.111:443
[0:0] -A zone_lan_prerouting -s 192.168.1.0/24 -d 192.168.178.20/32 -p tcp -m tcp --dport 443 -m comment --comment "!fw3: guideriis (reflection)" -j DNAT --to-destination 192.168.1.111:443
[0:0] -A zone_lan_prerouting -s 192.168.1.0/24 -d 192.168.178.20/32 -p udp -m udp --dport 443 -m comment --comment "!fw3: guideriis (reflection)" -j DNAT --to-destination 192.168.1.111:443
[3708:248341] -A zone_wan_postrouting -m comment --comment "!fw3: Custom wan postrouting rule chain" -j postrouting_wan_rule
[3708:248341] -A zone_wan_postrouting -m comment --comment "!fw3" -j MASQUERADE
[29:1680] -A zone_wan_prerouting -m comment --comment "!fw3: Custom wan prerouting rule chain" -j prerouting_wan_rule
[0:0] -A zone_wan_prerouting -p tcp -m tcp --dport 443 -m comment --comment "!fw3: guideriis" -j DNAT --to-destination 192.168.1.111:443
[0:0] -A zone_wan_prerouting -p udp -m udp --dport 443 -m comment --comment "!fw3: guideriis" -j DNAT --to-destination 192.168.1.111:443
COMMIT
# Completed on Tue Nov 10 18:48:55 2020
# Generated by iptables-save v1.8.3 on Tue Nov 10 18:48:55 2020
*mangle
:PREROUTING ACCEPT [161992:68733603]
:INPUT ACCEPT [36023:4138303]
:FORWARD ACCEPT [125184:64452489]
:OUTPUT ACCEPT [40717:12570813]
:POSTROUTING ACCEPT [153906:75865022]
[4302:254980] -A FORWARD -o eth1.2 -p tcp -m tcp --tcp-flags SYN,RST SYN -m comment --comment "!fw3: Zone wan MTU fixing" -j TCPMSS --clamp-mss-to-pmtu
[868:48348] -A FORWARD -i eth1.2 -p tcp -m tcp --tcp-flags SYN,RST SYN -m comment --comment "!fw3: Zone wan MTU fixing" -j TCPMSS --clamp-mss-to-pmtu
COMMIT
# Completed on Tue Nov 10 18:48:55 2020
# Generated by iptables-save v1.8.3 on Tue Nov 10 18:48:55 2020
*filter
:INPUT ACCEPT [0:0]
:FORWARD ACCEPT [555:33300]
:OUTPUT ACCEPT [0:0]
:forwarding_fw_Guests_rule - [0:0]
:forwarding_lan_rule - [0:0]
:forwarding_rule - [0:0]
:forwarding_wan_rule - [0:0]
:input_fw_Guests_rule - [0:0]
:input_lan_rule - [0:0]
:input_rule - [0:0]
:input_wan_rule - [0:0]
:output_fw_Guests_rule - [0:0]
:output_lan_rule - [0:0]
:output_rule - [0:0]
:output_wan_rule - [0:0]
:reject - [0:0]
:syn_flood - [0:0]
:zone_fw_Guests_dest_ACCEPT - [0:0]
:zone_fw_Guests_dest_REJECT - [0:0]
:zone_fw_Guests_forward - [0:0]
:zone_fw_Guests_input - [0:0]
:zone_fw_Guests_output - [0:0]
:zone_fw_Guests_src_ACCEPT - [0:0]
:zone_lan_dest_ACCEPT - [0:0]
:zone_lan_forward - [0:0]
:zone_lan_input - [0:0]
:zone_lan_output - [0:0]
:zone_lan_src_ACCEPT - [0:0]
:zone_wan_dest_ACCEPT - [0:0]
:zone_wan_dest_DROP - [0:0]
:zone_wan_dest_REJECT - [0:0]
:zone_wan_forward - [0:0]
:zone_wan_input - [0:0]
:zone_wan_output - [0:0]
:zone_wan_src_REJECT - [0:0]
[17414:1412512] -A INPUT -i lo -m comment --comment "!fw3" -j ACCEPT
[18609:2725791] -A INPUT -m comment --comment "!fw3: Custom input rule chain" -j input_rule
[10024:1529143] -A INPUT -m conntrack --ctstate RELATED,ESTABLISHED -m comment --comment "!fw3" -j ACCEPT
[91:5460] -A INPUT -p tcp -m tcp --tcp-flags FIN,SYN,RST,ACK SYN -m comment --comment "!fw3" -j syn_flood
[577:49449] -A INPUT -i br-if_Trusted -m comment --comment "!fw3" -j zone_lan_input
[4723:933276] -A INPUT -i br-lan -m comment --comment "!fw3" -j zone_lan_input
[95:4322] -A INPUT -i eth1.2 -m comment --comment "!fw3" -j zone_wan_input
[3190:209601] -A INPUT -i br-if_Guests -m comment --comment "!fw3" -j zone_fw_Guests_input
[125184:64452489] -A FORWARD -m comment --comment "!fw3: Custom forwarding rule chain" -j forwarding_rule
[109461:63081148] -A FORWARD -m conntrack --ctstate RELATED,ESTABLISHED -m comment --comment "!fw3" -j ACCEPT
[1001:64791] -A FORWARD -i br-if_Trusted -m comment --comment "!fw3" -j zone_lan_forward
[13770:1249382] -A FORWARD -i br-lan -m comment --comment "!fw3" -j zone_lan_forward
[0:0] -A FORWARD -i eth1.2 -m comment --comment "!fw3" -j zone_wan_forward
[952:57168] -A FORWARD -i br-if_Guests -m comment --comment "!fw3" -j zone_fw_Guests_forward
[17414:1412512] -A OUTPUT -o lo -m comment --comment "!fw3" -j ACCEPT
[22910:11127385] -A OUTPUT -m comment --comment "!fw3: Custom output rule chain" -j output_rule
[20297:10939723] -A OUTPUT -m conntrack --ctstate RELATED,ESTABLISHED -m comment --comment "!fw3" -j ACCEPT
[21:4648] -A OUTPUT -o br-if_Trusted -m comment --comment "!fw3" -j zone_lan_output
[0:0] -A OUTPUT -o br-lan -m comment --comment "!fw3" -j zone_lan_output
[2579:179870] -A OUTPUT -o eth1.2 -m comment --comment "!fw3" -j zone_wan_output
[13:3144] -A OUTPUT -o br-if_Guests -m comment --comment "!fw3" -j zone_fw_Guests_output
[33:2090] -A reject -p tcp -m comment --comment "!fw3" -j REJECT --reject-with tcp-reset
[0:0] -A reject -m comment --comment "!fw3" -j REJECT --reject-with icmp-port-unreachable
[91:5460] -A syn_flood -p tcp -m tcp --tcp-flags FIN,SYN,RST,ACK SYN -m limit --limit 25/sec --limit-burst 50 -m comment --comment "!fw3" -j RETURN
[0:0] -A syn_flood -m comment --comment "!fw3" -j DROP
[13:3144] -A zone_fw_Guests_dest_ACCEPT -o br-if_Guests -m comment --comment "!fw3" -j ACCEPT
[0:0] -A zone_fw_Guests_dest_REJECT -o br-if_Guests -m comment --comment "!fw3" -j reject
[952:57168] -A zone_fw_Guests_forward -m comment --comment "!fw3: Custom fw_Guests forwarding rule chain" -j forwarding_fw_Guests_rule
[952:57168] -A zone_fw_Guests_forward -m comment --comment "!fw3: Zone fw_Guests to wan forwarding policy" -j zone_wan_dest_ACCEPT
[0:0] -A zone_fw_Guests_forward -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port forwards" -j ACCEPT
[555:33300] -A zone_fw_Guests_forward -m comment --comment "!fw3" -j zone_fw_Guests_dest_REJECT
[3190:209601] -A zone_fw_Guests_input -m comment --comment "!fw3: Custom fw_Guests input rule chain" -j input_fw_Guests_rule
[0:0] -A zone_fw_Guests_input -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port redirections" -j ACCEPT
[3190:209601] -A zone_fw_Guests_input -m comment --comment "!fw3" -j zone_fw_Guests_src_ACCEPT
[13:3144] -A zone_fw_Guests_output -m comment --comment "!fw3: Custom fw_Guests output rule chain" -j output_fw_Guests_rule
[13:3144] -A zone_fw_Guests_output -m comment --comment "!fw3" -j zone_fw_Guests_dest_ACCEPT
[3190:209601] -A zone_fw_Guests_src_ACCEPT -i br-if_Guests -m conntrack --ctstate NEW,UNTRACKED -m comment --comment "!fw3" -j ACCEPT
[21:4648] -A zone_lan_dest_ACCEPT -o br-if_Trusted -m comment --comment "!fw3" -j ACCEPT
[1404:73968] -A zone_lan_dest_ACCEPT -o br-lan -m comment --comment "!fw3" -j ACCEPT
[14771:1314173] -A zone_lan_forward -m comment --comment "!fw3: Custom lan forwarding rule chain" -j forwarding_lan_rule
[3203:192180] -A zone_lan_forward -s 192.168.1.128/25 -p tcp -m comment --comment "!fw3: block iot wan" -j zone_wan_dest_DROP
[8392:934260] -A zone_lan_forward -s 192.168.1.128/25 -p udp -m comment --comment "!fw3: block iot wan" -j zone_wan_dest_DROP
[0:0] -A zone_lan_forward -s 192.168.1.10/32 -p tcp -m comment --comment "!fw3: block default ipcam" -j zone_wan_dest_DROP
[0:0] -A zone_lan_forward -s 192.168.1.10/32 -p udp -m comment --comment "!fw3: block default ipcam" -j zone_wan_dest_DROP
[3176:187733] -A zone_lan_forward -m comment --comment "!fw3: Zone lan to wan forwarding policy" -j zone_wan_dest_ACCEPT
[0:0] -A zone_lan_forward -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port forwards" -j ACCEPT
[1404:73968] -A zone_lan_forward -m comment --comment "!fw3" -j zone_lan_dest_ACCEPT
[5300:982725] -A zone_lan_input -m comment --comment "!fw3: Custom lan input rule chain" -j input_lan_rule
[0:0] -A zone_lan_input -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port redirections" -j ACCEPT
[5300:982725] -A zone_lan_input -m comment --comment "!fw3" -j zone_lan_src_ACCEPT
[21:4648] -A zone_lan_output -m comment --comment "!fw3: Custom lan output rule chain" -j output_lan_rule
[21:4648] -A zone_lan_output -m comment --comment "!fw3" -j zone_lan_dest_ACCEPT
[577:49449] -A zone_lan_src_ACCEPT -i br-if_Trusted -m conntrack --ctstate NEW,UNTRACKED -m comment --comment "!fw3" -j ACCEPT
[4723:933276] -A zone_lan_src_ACCEPT -i br-lan -m conntrack --ctstate NEW,UNTRACKED -m comment --comment "!fw3" -j ACCEPT
[4:160] -A zone_wan_dest_ACCEPT -o eth1.2 -m conntrack --ctstate INVALID -m comment --comment "!fw3: Prevent NAT leakage" -j DROP
[4744:317343] -A zone_wan_dest_ACCEPT -o eth1.2 -m comment --comment "!fw3" -j ACCEPT
[11595:1126440] -A zone_wan_dest_DROP -o eth1.2 -m comment --comment "!fw3" -j DROP
[0:0] -A zone_wan_dest_REJECT -o eth1.2 -m comment --comment "!fw3" -j reject
[0:0] -A zone_wan_forward -m comment --comment "!fw3: Custom wan forwarding rule chain" -j forwarding_wan_rule
[0:0] -A zone_wan_forward -p esp -m comment --comment "!fw3: Allow-IPSec-ESP" -j zone_lan_dest_ACCEPT
[0:0] -A zone_wan_forward -p udp -m udp --dport 500 -m comment --comment "!fw3: Allow-ISAKMP" -j zone_lan_dest_ACCEPT
[0:0] -A zone_wan_forward -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port forwards" -j ACCEPT
[0:0] -A zone_wan_forward -m comment --comment "!fw3" -j zone_wan_dest_REJECT
[95:4322] -A zone_wan_input -m comment --comment "!fw3: Custom wan input rule chain" -j input_wan_rule
[0:0] -A zone_wan_input -p udp -m udp --dport 68 -m comment --comment "!fw3: Allow-DHCP-Renew" -j ACCEPT
[0:0] -A zone_wan_input -p icmp -m icmp --icmp-type 8 -m comment --comment "!fw3: Allow-Ping" -j ACCEPT
[62:2232] -A zone_wan_input -p igmp -m comment --comment "!fw3: Allow-IGMP" -j ACCEPT
[0:0] -A zone_wan_input -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port redirections" -j ACCEPT
[33:2090] -A zone_wan_input -m comment --comment "!fw3" -j zone_wan_src_REJECT
[2579:179870] -A zone_wan_output -m comment --comment "!fw3: Custom wan output rule chain" -j output_wan_rule
[2579:179870] -A zone_wan_output -m comment --comment "!fw3" -j zone_wan_dest_ACCEPT
[33:2090] -A zone_wan_src_REJECT -i eth1.2 -m comment --comment "!fw3" -j reject
COMMIT
# Completed on Tue Nov 10 18:48:55 2020
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
8: br-if_Guests: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP group default qlen 1000
inet 10.5.0.1/16 brd 10.5.255.255 scope global br-if_Guests
valid_lft forever preferred_lft forever
10: br-if_Trusted: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP group default qlen 1000
inet 10.4.0.1/16 brd 10.4.255.255 scope global br-if_Trusted
valid_lft forever preferred_lft forever
12: br-lan: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP group default qlen 1000
inet 10.0.0.1/14 brd 10.3.255.255 scope global br-lan
valid_lft forever preferred_lft forever
14: eth1.2@eth1: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP group default qlen 1000
inet 192.168.178.20/24 brd 192.168.178.255 scope global eth1.2
valid_lft forever preferred_lft forever
default via 192.168.178.1 dev eth1.2 proto static src 192.168.178.20
10.0.0.0/14 dev br-lan proto kernel scope link src 10.0.0.1
10.4.0.0/16 dev br-if_Trusted proto kernel scope link src 10.4.0.1
10.5.0.0/16 dev br-if_Guests proto kernel scope link src 10.5.0.1
192.168.178.0/24 dev eth1.2 proto kernel scope link src 192.168.178.20
broadcast 10.0.0.0 dev br-lan table local proto kernel scope link src 10.0.0.1
local 10.0.0.1 dev br-lan table local proto kernel scope host src 10.0.0.1
broadcast 10.3.255.255 dev br-lan table local proto kernel scope link src 10.0.0.1
broadcast 10.4.0.0 dev br-if_Trusted table local proto kernel scope link src 10.4.0.1
local 10.4.0.1 dev br-if_Trusted table local proto kernel scope host src 10.4.0.1
broadcast 10.4.255.255 dev br-if_Trusted table local proto kernel scope link src 10.4.0.1
broadcast 10.5.0.0 dev br-if_Guests table local proto kernel scope link src 10.5.0.1
local 10.5.0.1 dev br-if_Guests table local proto kernel scope host src 10.5.0.1
broadcast 10.5.255.255 dev br-if_Guests table local proto kernel scope link src 10.5.0.1
broadcast 127.0.0.0 dev lo table local proto kernel scope link src 127.0.0.1
local 127.0.0.0/8 dev lo table local proto kernel scope host src 127.0.0.1
local 127.0.0.1 dev lo table local proto kernel scope host src 127.0.0.1
broadcast 127.255.255.255 dev lo table local proto kernel scope link src 127.0.0.1
broadcast 192.168.178.0 dev eth1.2 table local proto kernel scope link src 192.168.178.20
local 192.168.178.20 dev eth1.2 table local proto kernel scope host src 192.168.178.20
broadcast 192.168.178.255 dev eth1.2 table local proto kernel scope link src 192.168.178.20
0: from all lookup local
32766: from all lookup main
32767: from all lookup default
ls: /tmp/resolv.*/*: No such file or directory
lrwxrwxrwx 1 root root 16 Sep 6 18:19 /etc/resolv.conf -> /tmp/resolv.conf
-rw-r--r-- 1 root root 32 Nov 10 16:09 /tmp/resolv.conf
-rw-r--r-- 1 root root 176 Nov 10 16:15 /tmp/resolv.conf.auto
==> /etc/resolv.conf <==
search lan
nameserver 127.0.0.1
==> /tmp/resolv.conf <==
search lan
nameserver 127.0.0.1
==> /tmp/resolv.conf.auto <==
# Interface if_Guests
nameserver 8.8.8.8
# Interface if_Trusted
nameserver 8.8.8.8
# Interface lan
nameserver 8.8.8.8
# Interface wan
nameserver 192.168.178.1
search fritz.box
head: /tmp/resolv.*/*: No such file or directory