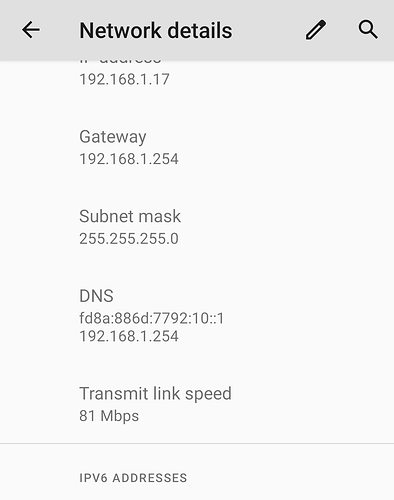
... indeed, you were right. I get IPv6 DNS on Android 11 (LineageOS in fact). Now I need to find out why Samsung doesn't get it...
... probably I will root it and check if it works with. DHCPv6 client app from Play Market. I'll report later.
Sure about that? IIRC I have never seen that an LLA is picked/used as the resolver address. It was always ULA or GUA on my Linux devices. That the gateway address could be LLA, yes, but the resolver? Technically possible yes but maybe the implementation prefers ULA or GUA?
I have a couple of OpenWrt VMs connected in cascade, and this is the downstream VM:
> cat /tmp/resolv.conf.d/resolv.conf.auto
# Interface wan
nameserver 192.168.1.1
search lan
# Interface wan6
nameserver fe80::5054:ff:feb8:487f%eth0
nameserver fd37:a698:ee4e::1
The LLA matches the upstream VM, but it appears in the list irregularly.
Other times there's only the ULA, so it might be a race condition.
I already did that in post #7. My pc running windows accepts the dns server without any configuration changes. So, this problem is reduced to android not taking the ra which also includes the dns server ipv6. Anyway, thank you for stating that android is not able to take dhcpv6. That helps to points in the right direction.
Some updates from me: I figured out, that it is an issue of the vpn interface. My android connects to it via wifi-vpn called "Bergwerk". If I run tcpdump on it like this
tcpdump -i br-vpn -v -n 'ip6' -w /tmp/dumpall-vpn.cap
and scroll through the file with wireshark... I can see only a few packets all of the type "Router Solicitation", "Neighbor Solicitation", "Router Advertisement", "Multicast Listener"..... I mean, all are ICMPv6, none is normal traffic. The android device seems to prefer IPv4 in this case although IPv6 is working - i can browse to ipv6.google.com for example.
Now I connected the android to another WiFi which is bridged to the lan interface. Boom. The android gets the ipv6 dns server ip regardless which type (GUA, ULA) I do configure. If I run tcpdump the same way like above it shows a lot of traffic different from ICMPv6.
So I compared the router advertisement packets of both interfaces. The only remarkable difference is, that on lan it includes a "route information" which is missing on vpn. This might lead android use IPv4 in favour of IPv6 and also to ignore the server IP. This is just my working hypothesis which is supported by the different packets captured.
So now the question is: How can I set the route information for vpn? I have manuelly set a IPv6 route, because i use pbr for ipv4, which doesnt work for ipv6. This is the reasons why wireguard cannot set a route by default ( option route_allowed_ips '0' ):
config device 'vpn_dev'
option type 'bridge'
option name 'br-vpn'
config interface 'vpn'
option proto 'static'
option device 'br-vpn'
option ipaddr '192.168.200.1'
option netmask '255.255.255.0'
option ip6assign '64'
option peerdns '0'
list dns ''\''192.168.224.1'\'''
list dns ''\''fdaa:0:0:aab0::1'\'''
list ip6class 'wg'
config interface 'wg'
option proto 'wireguard'
option private_key ''
option dns ''\''192.168.224.1'\'' '\''fdaa:0:0:aab0::1'\'''
option ip6prefix 'fdaa:0:0:aab9::/64'
list addresses '192.168.228.1/24'
list addresses 'fdaa:0:0:aab8::1/64'
config wireguard_wg 'wgserver'
option public_key ''
option preshared_key ''
option endpoint_host 'MY.WIREGUARD.SERVER.IP'
option endpoint_port 'A-PORT-NUMBER'
option route_allowed_ips '0'
option persistent_keepalive '25'
list allowed_ips '0.0.0.0/0'
list allowed_ips '::/0'
config route6
option interface 'wg'
option target '::/0'
Just in case I do miss something, here is the vpn snippet of /etc/config/firewall:
config zone 'vpn'
option name 'vpn'
option network 'vpn'
option input 'REJECT'
option output 'ACCEPT'
option forward 'REJECT'
config forwarding 'vpn_wan'
option src 'vpn'
option dest 'wan'
config rule 'vpn_dhcp'
option name 'Allow-DHCP-VPN'
option src 'vpn'
option dest_port '67'
option proto 'udp'
option family 'ipv4'
option target 'ACCEPT'
config rule 'vpn_dhcp6'
option name 'Allow-DHCPv6-VPN'
option src 'vpn'
option dest_port '547'
option proto 'udp'
option family 'ipv6'
option target 'ACCEPT'
There's a workaround to make apps prefer IPv6 over IPv4 when assigned only ULA:
https://openwrt.org/docs/guide-user/network/ipv6/ipv6_extras#using_ipv6_by_default
That was it. After changing the default routes with no success I played a little. I disabled router advertisement in dnsmasq and installed uradvd to test some conditions. As soon as I (fake) annouced a public prefix instead of a ULA, the android would accept both the dnsv6 ip and ipv6 as default. So I reverted everything back and now I use ddaa:0:0:aaf8::/63 for the wireguard tunnel. It works great! ![]() . Plus I am satisfied not to worry about the ISP and wireguard uplink conditions, the config is much more robust now. Thanks.
. Plus I am satisfied not to worry about the ISP and wireguard uplink conditions, the config is much more robust now. Thanks.
If you need a prefix which looks GUA but is not: then use 2001:db8::/32 which is the IPv6 network for documentation purpose but can be used in local (test) networks as well and even it should not leave a local network it will be seen as bogus if it ever will hit an router on the Internet.
Keep in mind that a documented and well-known non-routable prefix may suffer the same fate as ULA by being deprioritized or discarded by specific IPv6 implementations.
I use it regularly on test beds and never encountered any issues. AFAIK the Linux Kernel treats the documentation networks (v4+v6) not in any special way. Normally they are only filtered on filter/route maps. But the kernel treats them just as other "global" prefixes.
This topic was automatically closed 10 days after the last reply. New replies are no longer allowed.